mirror of
https://github.com/HackTricks-wiki/hacktricks.git
synced 2025-10-10 18:36:50 +00:00
1021 B
1021 B
USB Keystrokes
{{#include ../../../banners/hacktricks-training.md}}
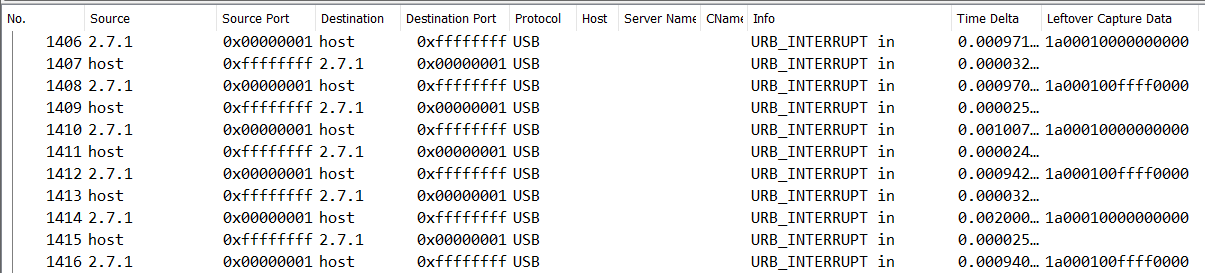
If you have a pcap containing the communication via USB of a keyboard like the following one:
You can use the tool ctf-usb-keyboard-parser to get what was written in the communication:
tshark -r ./usb.pcap -Y 'usb.capdata && usb.data_len == 8' -T fields -e usb.capdata | sed 's/../:&/g2' > keystrokes.txt
python3 usbkeyboard.py ./keystrokes.txt
You can read more information and find some scripts about how to analyse this in:
- https://medium.com/@ali.bawazeeer/kaizen-ctf-2018-reverse-engineer-usb-keystrok-from-pcap-file-2412351679f4
- https://github.com/tanc7/HacktheBox_Deadly_Arthropod_Writeup
{{#include ../../../banners/hacktricks-training.md}}