mirror of
https://github.com/HackTricks-wiki/hacktricks.git
synced 2025-10-10 18:36:50 +00:00
1.9 KiB
1.9 KiB
43 - Pentesting WHOIS
{{#include ../banners/hacktricks-training.md}}
基本信息
WHOIS 协议作为一种标准方法,通过特定数据库 查询各种互联网资源的注册人或持有者。这些资源包括域名、IP地址块和自治系统等。除此之外,该协议还用于访问更广泛的信息。
默认端口: 43
PORT STATE SERVICE
43/tcp open whois?
枚举
获取 whois 服务关于一个域名的所有信息:
whois -h <HOST> -p <PORT> "domain.tld"
echo "domain.ltd" | nc -vn <HOST> <PORT>
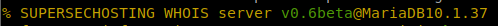
注意,有时在请求WHOIS服务的一些信息时,使用的数据库会出现在响应中:
此外,WHOIS服务始终需要使用数据库来存储和提取信息。因此,当查询用户提供的一些信息时,可能会存在SQL注入。例如,执行:whois -h 10.10.10.155 -p 43 "a') or 1=1#",您可能能够提取所有存储在数据库中的信息。
Shodan
port:43 whois
HackTricks 自动命令
Protocol_Name: WHOIS #Protocol Abbreviation if there is one.
Port_Number: 43 #Comma separated if there is more than one.
Protocol_Description: WHOIS #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for WHOIS
Note: |
The WHOIS protocol serves as a standard method for inquiring about the registrants or holders of various Internet resources through specific databases. These resources encompass domain names, blocks of IP addresses, and autonomous systems, among others. Beyond these, the protocol finds application in accessing a broader spectrum of information.
https://book.hacktricks.xyz/pentesting/pentesting-smtp
Entry_2:
Name: Banner Grab
Description: Grab WHOIS Banner
Command: whois -h {IP} -p 43 {Domain_Name} && echo {Domain_Name} | nc -vn {IP} 43
{{#include ../banners/hacktricks-training.md}}